CN102812431A - 用于识别与保护一组源数据的完整性的方法 - Google Patents
用于识别与保护一组源数据的完整性的方法 Download PDFInfo
- Publication number
- CN102812431A CN102812431A CN2010800655963A CN201080065596A CN102812431A CN 102812431 A CN102812431 A CN 102812431A CN 2010800655963 A CN2010800655963 A CN 2010800655963A CN 201080065596 A CN201080065596 A CN 201080065596A CN 102812431 A CN102812431 A CN 102812431A
- Authority
- CN
- China
- Prior art keywords
- group
- conversion
- surplus
- source data
- data
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Pending
Links
Images
Classifications
-
- H—ELECTRICITY
- H03—ELECTRONIC CIRCUITRY
- H03M—CODING; DECODING; CODE CONVERSION IN GENERAL
- H03M13/00—Coding, decoding or code conversion, for error detection or error correction; Coding theory basic assumptions; Coding bounds; Error probability evaluation methods; Channel models; Simulation or testing of codes
- H03M13/29—Coding, decoding or code conversion, for error detection or error correction; Coding theory basic assumptions; Coding bounds; Error probability evaluation methods; Channel models; Simulation or testing of codes combining two or more codes or code structures, e.g. product codes, generalised product codes, concatenated codes, inner and outer codes
- H03M13/2906—Coding, decoding or code conversion, for error detection or error correction; Coding theory basic assumptions; Coding bounds; Error probability evaluation methods; Channel models; Simulation or testing of codes combining two or more codes or code structures, e.g. product codes, generalised product codes, concatenated codes, inner and outer codes using block codes
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/57—Certifying or maintaining trusted computer platforms, e.g. secure boots or power-downs, version controls, system software checks, secure updates or assessing vulnerabilities
- G06F21/572—Secure firmware programming, e.g. of basic input output system [BIOS]
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/64—Protecting data integrity, e.g. using checksums, certificates or signatures
-
- H—ELECTRICITY
- H03—ELECTRONIC CIRCUITRY
- H03M—CODING; DECODING; CODE CONVERSION IN GENERAL
- H03M13/00—Coding, decoding or code conversion, for error detection or error correction; Coding theory basic assumptions; Coding bounds; Error probability evaluation methods; Channel models; Simulation or testing of codes
- H03M13/63—Joint error correction and other techniques
Abstract
识别与保护一组源数据的完整性的方法,该方法产生并结合识别签名与检测和纠正余部,且扩充某些数据保证方法的现有能力。
Description
技术领域
本发明涉及一种用于识别与保护一组源数据的完整性的方法,特别涉及一种用于扩展检错纠错的方法的能力以包括改进的识别与保护的方法。
背景技术
W·W·彼得森(W.W.Peterson)在1962年在《科学美国人(Scientific American)》中所说的“无误表现是每套良好的通信系统的实现目标”仍然是老生常谈。可是,在全球的商业模式中,出现根本上不同、恶意的攻击,要在任务关键和安全关键系统中:a)变更设计;b)篡改硬件;以及c)包含欺骗性软件。过去,尤其是在保护嵌入式系统内的启动固件时,传统的检错纠错(error detection and correction,EDAC)技术大致已经足够满足数据传送中指定概率的未被检出的(随机)误差阈值。然而,在现今市场内,需要对这些算法有更多的防御以处理外包的系统开发和数据传递的识别、完整性和安全性问题。检测、纠正、追踪或阻遏由网际攻击所导致的蓄意的系统和数据损毁的问题特别受到关注。彼得森在当时提及的是免受“噪声”影响的保护,但现今我们务必包括在关键的环境中免受智能攻击的保护。这些关键的环境必须被设防御以幸免于物理安全性的损失。已有冗长的技术来用于不同层面的需要。普遍而言,加密用于保护大多数关键的数据,但通过不使用加密的系统编码来进行数据保护(或篡改侦测)也有其适用需求。某些双冗余系统具有严谨的实时启动和响应要求。用于对付恶意的攻击的任何EDAC数据处理的扩展或额外的保密(security)算法仍必须达到时间上的要求。
为响应启动固件潜在的保密性缺口,某些计算装置提供保密措施以确保该启动固件来自可信任的来源。这些保密措施依赖于唯一标识相关联的启动固件的来源的数字签名。所述计算装置可对数字签字进行译码以识别所述固件,并基于所述数字签字与已知值的比较而接受或拒绝所述启动。这个方法的困难在于所述设计受到恶意的攻击时,所述已知值可以容易地被修改以与计算值匹配。其他的缺陷会是计算装置在安装后只校验固件一次或只在启动时校验固件。启动后,便假设固件不受动态地更改。这些威胁并未通过被动性保密措施得到防止。
差错控制编码的进步已允许这些进展在数字信息存储和传送上的使用无所不在。所述数字信息的例子包括电话、因特网、DVD、电子商务交易、磁盘驱动器、ISBN(国际标准图书编号)、UPC(通用产品代码)和RFID(无线射频识别)标签。
现有技术提供了差错控制编码的部分的广义抽象概念。在图1a所示现有技术的基本例子中,源数据进入EDAC编码器,并且在编码后通过信道传输或传送。在数据接收器(sink)端、在信道之后,编码数据通过EDAC译码器检查错误。其中一类系统,是使用此设计的,其在检测到错误的情况下以重试请求进行响应。在另一类系统中,错误会由译码器纠正。两类系统对可被检出的、可纠正的、不可被检出的和不可纠正的错误的数目与类别均有其限制。这些类别的EDAC系统普遍并非这样设计以提供免受网际攻击的保护,而是设计成处理随机或猝发错误,或者随机或猝发错误的某些组合。
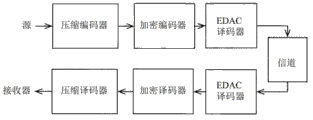
图1b所示的现有技术通过加入加密编码和加密译码来添加数据保密。通过在所述加密之前加上压缩阶段,某些表现与数大小限制得到改善,这是所述技术领域公知的。通常这些步骤远比仅有所述EDAC阶段时间集中,使它们在某些实时嵌入式系统中因涉及的风险而并不可行。
所述技术领域有更多的例子展示前述那个基本例子和那个较复杂的例子的变化,或展示连接、交叉、冗余和反馈之间的组合。这些变化的使用给磁盘驱动器在纠错后带来的未被检出的错误的概率处于数量级10-18级别。
某些应用要求有很低的未被检出的错误的概率。就最关键的航空电子设备的应用而言,未被检出的错误的概率的要求为10-9,另要求没有单点失效,以及没有针对硬件系统的共同原因。对于相似的关键软件系统,要求要满足所谓“A级”目标而非10-9,其他的要求则依然要达到。
有人曾指出在关键航空电子软件系统的端到端生命周期中,免受网际攻击的防护等级存在潜在缺口。保护这些缺口的解决方案一直是在开发时间EDAC编码器余部的可靠性,所述余部附属于启动代码映像902,可参图7的904。
当假定在不同物理层和装置内提供强大保护,将产生在数据生命周期内数据免受较高级别而日益明显的威胁的足够的端到端保护时,额外的缓解程序便是必需的。可行的部分的解决方案同样也是在所述源处附上对数据的足够的保护、并使其在预期使用期限内保持附上,且在过程中检查该部分。如前提及,考虑到新的威胁,对关键系统而言仅依赖EDAC的保护不再足够,但一如既往,任何解决方案必需是简单的、便宜的、适当的和快捷的。
在1974年1月15日发行的美国专利3,786,439中,麦克唐纳(McDonald)介绍新颖的想法“如应用于不同的错误码一样,通过使用与数据字段内的非线性变化结合的多个独立错误码,检错得以增强”。然后指出使用非线性置换,其通过“对多个独立代码之间的跟踪错误代码关系进行加扰”。非线性的定义没有明确地说明,但后来在该讨论中它看起来是指不进行循环置换。它指示将数据集分开成若干子集,以一个ECC-3端到端覆盖所有数据,见于以下陈述:“……产生第二个非线性相关之数据字段”及“由于所述两个代码之间的非线性差异,因此提供了高度的可靠性,其中错误状况与该两个代码属相同数学子段的概率变成非常之低”。后来,讨论中指出每一多项式均具有1+x的项。在所述权利要求中,跟随所述方法会显示“少于第一和第二组错误的第三组错误,该第三组包括均不在所述第一和第二组内的错误……”。
继麦克唐纳后,在1995年2月21日发行的美国专利5,392,299中,雷内斯(Rhines)等人介绍三维正交交错误差校正系统的想法。该系统用于为正使用的信道而设的随机与突发的增强保护。所述加扰是固定的并且所述方法要求三部分的正交交织。正交的定义为进行增强免受突发错误影响的保护的「左右移动」。后来,讨论中指出在编码之前或之后使用交织过程去提供对付包含的错误的额外保护,这属于所述技术领域公知。所述交织定义为在其中连续字节互相分开的过程,以免受猝发错误影响作出保护。
在1997年9月30日发行的美国专利5,673,316中,奥尔巴赫(Auerbach)等人讨论为信息部分的聚合的加密封装的创建与分配,其中要受保护的部分中的每个部分都经加密。
在《使用移动(TWINKLE)装置对大数字进行因子分解(Factoring LargeNumbers with the TWINKLE Device)》的摘要中,阿迪沙米尔(Adi Shamir)指出“RSA公钥密码体制的保密性根据对本身为两个大小相等的素数p和q的乘积的大数字n进行因子分解的难度而定”。他也指出“对大的RSA密钥进行因子分解的当前纪录是对465位数字的因子分解……‘移动’技术可增加可分解因子的数字的大小100至200位……”及“……可令512位RSA密钥(其保护95%现今因特网上的电子商务)十分易受攻击”。
在布罗(Berrou)于1996年发表的论文中,文中指出“2)非一致性交织:明显地,例如如图5所代表的,给予最短距离的形式可通过合宜的非一致性交织‘分开’,从而将可分开的FC[有限码字——由0开始的有限距离]形式转换成不可分开的FC或非FC。”“非一致性交织必须满足两个主要条件:如一般交织中最大的数据分散、以及在交织数据序列中最大的混乱。可能与前者有矛盾的后者是要使源自所述两个编码器产生的冗余代尽可能多种多样的。”
发明内容
本发明是识别与保护一组源数据的完整性的方法。所述源数据可以以软件或传输数据的形式存在。步骤(a)和步骤(b)可以是可编程的。所述源数据也可以完全地或部分地嵌入硬件。
本发明的一个实施例可以包括以下步骤:
(a)将所述源数据通过变换以产生经变换的一组源日期;
(b)利用畸变函数使得所述经变换的一组源数据畸变以产生中间的一组源数据;以及
(c)将所述中间的一组源数据通过EDAC(检错纠错)算法以产生余部,并将该余部附加到所述一组源数据以产生经编码的一组源数据。
在一个可替换实施例中,所述方法还可以包括以下步骤,就是将所述的一组源日期通过某第二EDAC算法以产生第二余部,并将该余部附加到所述经编码的一组源数据。
就嵌入式系统的情况,举例来说通过生成计算机,可以在将所述一组源数据嵌入前先计算所述余部中的一个或两个。
EDAC算法通常将所述源数据编码并产生余部,该余部用来警惕使用者在所述源数据中存在故意的或意外的变更。已知很多EDAC算法均适用于本发明的实施。所述EDAC算法和可能用上的第二EDAC算法可以是相同或不同的。所述EDAC算法通常通过多项式除数操作。所述EDAC算法可以使用不同的多项式。从现有技术得知的EDAC算法的例子包括CRC算法、里德-所罗门(Reed-Solomon)编码、维特比(Viterbi)编码、Turbo编码、MD5算法和SHA-1散列算法。
一类简单的变换是交织器。很多种类的交织器是所述技术公知的。交织器改变所述源数据的部分的相对位置。如美国专利5,393,299所示,可选择交织以致使结果与原本的正交。此外,交织器可以简单如位2的对的交换(“2-位交替”)。根据所选的多项式而定,2-位交替可被视作仿射变换。交织器也可以在较大的数据块上以较复杂的方式操作。一种现有技术中的交织器是称为福尼(Forney)交织器的交织器。交织器可完全地或部分地在硬件内执行。举例来说,交织器可包括串行至并行数据转换器,该数据转换器的输出与纵横交错布线矩阵交织。所述交织器也可以被实施为下述串行至并行数据转换器,所指数据转换器的输出与N乘N闪存(N-by-N FLASH memory)或N乘NRAM存储器(N-by-N RAM memory)交织。所述变换也可以在软件中执行,举例来说,可通过进行使得所述源数据发生非正交变换的仿射变换来执行。其他与此同类的变换可以包括没有反函数的变换、没有保护刚体(rigid)运动的变换、或LangGanong变换或源自非公理(non-axiomatic)变换的变换。
所述畸变函数的一个例子可包括在所述经变换的一组源数据与二进模式之间的异或(exclusive OR)运算。所述二进模式可从N乘NRAM存储器抽出。
一类非公理变换可以包括所述畸变函数为所述变换的一部分。一个例子是由m个元素映射n个元素,其中m<n或m>n。在某些实施例中,所述方法也可以包括以下步骤:通过重新计算所述两个余部中的一个或两个来校验源日期的完整性,将所述余部的重新计算值与所述余部的原始值比较,将所述余部的重新计算值与所述余部的原始值比较,以及在余部的集合之间的比较显示出不同的条件下提供指示符。可周期性地或非周期性地校验所述余部。所述余部的值可以提供给显示装置、通过在串行总线上放置提供、通过在并行总线上放置提供或提供给控制逻辑。所述余部的值可以响应于请求而提供。
附图说明
图1a为展示现有技术中数字通信系统的基本组件的图。
图1b为展示现有技术中数字通信系统较全面的组件的图。
图1c为展示本发明的IDAC编码器与IDAC译码器组件的组成的图。
图1d为展示EDAC1编码器、EDAC2编码器、以及所述IDAC编码器的其他部件的图。
图2为展示某IDAC编码器的实施例中的EDAC编码器的“T”副本的图。
图3为展示EDAC1译码器、EDAC2译码器、以及所述IDAC译码器的其他部件的图。
图4为展示具有挑战性的部件的两个IDAC译码器的双冗余实施例的图。
图5a为展示IDAC编码器或IDAC译码器的公开或秘密变换部件的分解图。
图5b为展示使用福尼交织器的IDAC的变换函数部件实施例的图。
图5c为展示在“有线”交织器周围使用串行至并行转换器和并行至串行转换器的IDAC的变换函数部件的另一实施例的图。
图5d为展示使用“线”交织器的IDAC的变换函数部件的另一实施例的图。
图5e为展示使用1位堆栈的IDAC的变换函数部件的另一实施例的图。
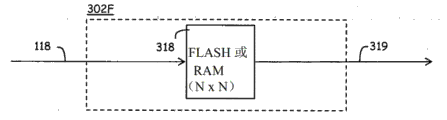
图5f为展示使用NxN FLASH或RAM的IDAC的变换函数部件的另一实施例的图。
图5g为展示使用LangGanong变换的将IDAC的变换函数部件与畸变函数部件结合的图。
图5h为展示所述IDAC的某实施例中的非公理变换的图。
图6a为展示使用NxN FLASH或RAM的IDAC的畸变函数部件的实施例的图。
图6b为展示使用LxL FLASH或RAM、为不可逆的、非一对一的、并且非映射的(onto)IDAC的畸变函数部件的另一实施例的图。
图6c为展示使用NxN FLASH或RAM、为可更新的的IDAC的一个组合的变换函数部件与畸变函数部件的实施例的图。
图6d为展示使用NxN FLASH或RAM、为可更新的的IDAC的一个组合的变换函数部件与畸变函数部件的另一实施例的图。
图7为展示受EDAC编码器和EDAC译码器保护的双冗余嵌入式固件的端到端生命周期内的组件的图。
具体实施方式
在以下的描述与讨论中,术语“码字”包括原本的一组源数据加上相对地唯一的标签(也称数字签名或散列),该标签为多个可能的编码之一的结果,正如所属技术领域所公知,所述编码例子是例如但不限于:a)循环冗余码校验(CRC)、b)里德-所罗门、c)维特比、d)Turbo、e)低密度奇偶校验(LDPC)、f)信息-摘要算法5(MD5)及g)安全散列算法(SHA-1)。该组源数据也可以在此称为消息、数据消息或源数据。源自检错纠错算法的余部也可以在此称为残数。
本发明在使用检错纠错代码时依赖反直觉的想法。该想法是在所述数据中加 入错误,实际上加入这样多的错误使为了要超过EDAC的能力。经过对经变换的一份数据消息进行编码时加入错误,在接收端电子欺骗会被显露(或者显露先前不可被检出的或不可纠正的错误)。所述技术改善了检测电子欺骗的能力,并可在创建所述数据消息时加到该消息以作为加强的数字签名,此签名比单靠所述第一EDAC产生的难被篡改。所以所述的基本想法是如在现有技术中一样使用一个EDAC,并且然后使用第二EDAC作为标识符或数字签名,其中第二EDAC使用与第一EDAC相同的编码器(或者在硬件内或软件内的复制出的编码器)。此外,由于所述变换步骤与畸变步骤已被分开且为并行进行的,所以它们是可编程的。如前提及,所述步骤的细节可以为公开的或私人的等等。另一优点是,由于所述步骤为并行的,故此所述步骤是可升级的。以32位CRC(称为REM1)为例,通过使得所述数据消息进行变换与畸变,可得到第二个32位CRC(或REM2),而无须采用独立的多项式。通过使得所述数据进行第三次的变换与畸变,可进一步得到另一个32位CRC(称作REM3),到现时为止总共96位。对于很小的512字节的消息,畸变的可能性为24096–1,这是很大的数字。通过加入非公理变换,譬如由4096映射8192,可能性会大得多。另有许多其他潜在的优点。以下是某些实施例的细节。
如图1c所示,在一个实施例中,源数据进入识别、检测和纠正(IDAC)编码器100,并被路由到两个分离的EDAC编码器,EDAC1编码器200和EDAC2编码器300。所述EDAC1编码器可以是所属技术领域所公知的多种编码器中的任何编码器。所述数据被编码而残数被传递到所述信道,再次如所属技术领域所公知的。所述EDAC2编码器同样可以包括任何编码器,但就本实施例而言,我们会使用与EDAC1相同类型的编码。复制出的一份源数据被编码并交给部件300,而所述残数如之前一样被传递到所述信道。部件200和部件300的细节将在后面描述。同样地,后面描述的IDAC译码器500包括容后描述的EDAC1译码器600和EDAC2译码器700。
若在EDAC2300内设定存有仿射变换,那么它的EDAC功能便与美国专利3,786,439相似,但没包含使用独立代码,且经EDAC2变换的数据并非传输或传送至所述信道的数据。EDAC2并非如美国专利3,786,439一样将所述数据变换得更能抵抗突发错误,因此EDAC2系统地发送所述原本未被改变的数据。EDAC2的目的是要使其本身更能抵抗怀恶意的攻击。此外,美国专利3,786,439并不包括畸变步骤。另外还有其他几个不同之处。
如图1d所示,所述源数据在102处进入IDAC编码器100的说明性实施例。所述数据在未被改变的情况下进入消息缓冲器/fifo 104,该过程受控制与定时部件128控制或发生在由该控制与定时部件128提供的位置、同时地或顺序地通过118经EDAC2300的公开或秘密变换部件314处理、以及同时受128指引(EDAC2的部件细节以双点划线标示)。部件314使得所述数据产生本地已知变化(或本地暂时性产生,又或者通过126由128远程接收与提供),然后将所述经改变的数据传送至EDAC2300的余部产生器2部件316,作为检查/标识符。更详细的描述由下面提出的题名为数据变换的部分提供。在此时(或此序列步骤)或者使用由128提供的相同位置,EDAC1200的余部产生器1部件212累积为所属技术领域公知的检查数据(EDAC1的部件细节以点划线标示)。所有所述源数据经部件314、316、212和214处理后,通过122部件212将其检查数据发送至EDAC1200的REM1部件206,并且通过124部件316将其检查数据发送至EDAC2300的REM2部件308。源自102的未被改变的信息源数据,在所述源数据之前、所述源数据之后、某些组合或单独地在部件128的控制下通过部件104到110。所述REM1检查/标识符数据和所述REM2检查/标识符数据在部件128控制下在110与该源数据合并。刚描述的过程可在仅硬件电路和/或硬件和软件的组合(固件)中实现。若有需要,当与验证设计或检测和计数器设计合而为一时,有供安全或保密的可选择的超驰(override)去禁用所述检查130。依赖性与保密性之间的平衡可通过部件130针对每项应用而设定,即只是安全性的、只是保密性的或某些组合。
如图2所示,由于EDAC1200和EDAC2300的编码操作以并行方式进行,因此所述IDAC可以设定存有EDAC2类编码器的T副本。(EDAC T 400的部件细节以点划线标示。)也可以被设定存有译码操作的T副本。
如图3所示,再一次,所述源数据在102进入所述IDAC译码器的实施例。在这种情况下所述源数据已具有将所述检测符号与所述消息在102进行合并,产生将要通过图3的实施例重新计算、并使用本地已知的或通过128远程提供的对象进行校验的码字。第一检查符号在REM1 SRC块552移除,并且第二检查符号则在REM2SRC块554移除。所述码字的消息部分通过部件104处理。图1d与图3之间的不同之处在于,在图3中,新的一组检查符号针对部件206和308而被计算,并在部件128的控制下通过部件560比较,通过/未通过的指示或所述REM会通过558交给部件128。部件128的控制与定时过程给部件564信号以通知可纠正的完整性上的错误,以通过162对所述消息作出反馈或抵抗行动。
图4的实施例为图1d和图3的提升,其使用所述IDAC仪器及方法的两个副本800-A和800-B,并加入挑战性的部件。每个副本均能实现,作为仅双冗余硬件仪器与方法之间的交叉检验,以及作为硬件/软件组合,或者作为别的成双或更多的之变化。在这情况下,单例的、周期性或非周期性挑战以本地产生、本地接收、或者本地已知或伪随机的消息变更(仿射的、非公理的或公认的)的形式出现,在挑战出现时间之始确定。这些变更交给所述系统的另一侧832、138(或834、139),且真实的第二检查符号必须在所述出现时间终止前交给第一侧150、846、144(或166、848、140)。(若消息变换仅包含线性变换,以前冲突的欺骗可维持冲突,如早前在例子1中所见。)由于该多项式恢复问题的不可行性,在所述出现时间内所述消息受怀恶意的源欺骗的可能性不高。挑战出现时间的最短长度不为本专利之作者所知,但研究显示它可能是NP-难解(NP-完全)的计算。本专利的申请人不知道任何已知解决方案。根据论文[“作为难题的加密和解码里德-所罗门代码(Cryptography and Decoding Reed-Solomon Codes as a Hard Problem),”AggelosKiayias and Moti Yung,2005,IEEE,0-7803-9491-7],选择变得比(n*(k-1))的平方根大的位的数目,所述多项式恢复问题依然是不可解的。所以选择变得仅低于此值的位的数目看起来是指来自怀恶意的源的任何额外的位变化会导致超越所述阈值,亦因而不能被所述怀恶意的源所解决(即不能受欺骗)。换句话说,所述EDAC算法的纠正能力已远被超越。另一可能是将所述变更供作在所属技术领域上公知为不可解决的一次性密钥(pad)。
如图5所示,所述公开或秘密变换块314包括两个部件,让数据通过118进入与通过319离开的变换函数302,以及让数据通过319进入与通过115离开的畸变函数304。
图5b为所述变换函数302的一个实施例,其包括为所属技术领域公知的福尼交织器302B。
图5c为所述变换函数302的一个实施例302C,其包括为首的串行至并行转换器、接着的线交织器、再接着的并行至串行转换器,所有部件都为所属技术领域公知的。
图5d为所述变换函数302的一个实施例302D,其包括并行输入数据118、有线交织器,经变换的并行数据在319离开。
图5e为所述变换函数302的一个实施例302E,其包括每两位交替的1位堆栈314。串行输入数据在118进入,而306控制所述堆栈。307选择并控制在所述变换后来自2到1多路复用器Mux 316的数据,交给输出319。
图5f为所述变换函数302的一个实施例,其包括NxN FLASH或RAM 318。有输入118映射到输出319的一对一映射。供所述变换的FLASH项目被预先输入。所述FLASH按需要可以是可移除的。在118处的数据模式用作查寻318内的项目的地址,然后该地址的输入值在319处输出。根据所述FLASH的预设项目,这项变换可以是非公理变换的例子。就具有N=64K字节的数据消息而言,所述FLASH会是32吉字节。
图5g为所述变换函数302的实施例,其包括早前所述的LangGanong变换302G。
图5h为所述变换函数302的实施例,其包括早前所述的非公理变换302H。
图6a为所述畸变函数302的实施例352A,其包括NxN FLASH或RAM 354。有输入118映射到输出319的一对一映射。供所述畸变的FLASH项目被预先输入。所述FLASH按需要可以是可移除的。在319处的数据模式用作查寻354内的项目的地址,然后该地址的输入值在115处输出。根据所述FLASH的预设项目,这项畸变可以是非公理变换的例子的部分。就具有N=64K字节的数据消息而言,所述FLASH会是32G字节。
图6b为所述畸变函数302的一个实施例352B,其包括LxL FLASH或RAM 356。使用非公理变换时,不需要有输入118映射到输出319的一对一或映成映射。供所述畸变的FLASH项目被预先输入。所述FLASH按需要可以是可移除的。在319处的数据模式用作查寻356内的项目的地址,然后该地址的输入值在115处输出。根据所述FLASH的预设项目,这项畸变可以是非公理变换的例子的部分。就具有N=64千字节的数据消息而言,所述FLASH会是32G字节。319的某些输入线与所述FLASH未必连接(NC),某些输入线则可短接(short)在一起。115的某些输出线在358处可绑定到逻辑“1”,某些则在360处可绑定到逻辑“0”,以建立随非公理变换之后的那项畸变。
图6c为所述畸变函数302的实施例352C,其包括NxN FLASH或RAM 354。有输入118映射到输出319的一对一映射。供所述畸变的FLASH项目被预先输入。所述FLASH按需要可以是可移除的。在319处的数据模式用作查寻354内的项目的地址,然后该地址的输入值在115处输出。根据所述FLASH的预设项目,这项畸变可以是非公理变换的例子的部分。就具有N=64K字节的数据消息而言,所述FLASH会是32G字节。挑战性的数据模式通过由Mux 362选择的126进入并存储在FLASH354中。
图6d为所述畸变函数302的某实施例352D,其包括N位寄存器366及在后的N位XOR 364。319处的数据模式是与所述N位寄存器的内容异或运算的变换函数的输出。所述N位寄存器可通过126更新。若如此设定,则挑战性的数据模式通过126进入。
图7展示在嵌入式固件的生命周期中IDAC编码器和IDAC译码器的使用。在所述编译计算机902内的实施例是在存储在设定管理档案918之前附加所述编码器904的REM1和REM2数字签名(识别与EDAC)的软件实施。就不同的活动而言,例如安装、校验、测试、质量保证、存储库的存储、托管存储、输出活动、证明、重新使用、维护、开发,所述数据信息从所述档案找回并通过所述IDAC译码器906识别与校验。就双冗余安装而言,两个副本通过908安装,并同样地通过所述IDAC译码器/编码器912识别与校验。若使用可加载字段的装置、在外部端口进入、或者进行证明或检验活动,则所述数据在914识别与校验。最后,另一IDAC译码器/编码器916在将所述数据载入目标920之前识别与校验所述数据。在所述双冗余系统中,922是第一路径和装置的复制品。
本发明的操作
对数字数据的未经授权的或非故意的修改可以通过检错纠错方法检测得到,如所属技术领域所公知。与现有技术相比,本发明所实施的新的改良是增加了检测以前未被检出的变更的能力。所述设备和方法通过在接收器和发送器两者所已知和所提供的位置将所述原始消息改变,然后计算这个现为第二消息上的第二检查符号,来实现所述改良。所述第二消息无须存储以成为所述码字的部分,只有所述第二检查能被传输或传送。
数据变换(公开的或秘密的变换)
所述变换包含仿射或非公理变换。仿射变换包括线性变换和平移(translation)。较早前已定义的非公理变换包括既非一对一、也非映成的非线性变换,以及平移。仿射变换的一个例子是排列和偏移(该仿射变换的实现可能是通过移位和XOR;就并行输入数据而言,仅数据位之硬连线纵横交错和半加器;或者就串行数据而言,交换了的触发器输出),其中的结果为原本的组中的项。非公理变换的例子可以产生在原本的组以外的结果(该非公理变换可以通过插入或改变所述消息数据位之前、之中或之后的位来实现。此外,它可以通过删除或忽略所述消息的某些位,或者通过一起简略(点或(dot-OR))消息的位来实现)。硬件和/或软件又或二者可通过并行方式执行以提升性能,并且可配合不同的变换多次重复以增加强度和坚固度及减少未被检出的变更。
两个例子将用于展示所述方法的较弱和较强的应用。首先,不能检测源于电子欺骗的数字数据变化,却仍提供独特签字的所述方法较弱的应用概要如下。
例子1
为使解释与计算简明,现采用3个字节的消息来发送(使用16位CRC算法)。该信息经电子欺骗,以致它具有的残数与原本具有的相同,例如:
类别 消息 残数(CRC)
原版 0x2A301C 0xDAC2
经电子欺骗成为 0xC06454 0xDAC2(匹配)
然后切换接收端的第一位(这是所述畸变步骤,但实施时不存仿射变换)。(在数学上,所指的执行如下:
接收的原版便是 0xAA301C 0xD62E
接收的电子欺骗成为 0x406454 0xD62E(再次匹配,电子欺骗未被检出)
将切换之间的距离变成>16位又如何?切换首位和末位(相隔23位)(再一次,限于仅畸变步骤):
接收的原版便是 0xAA301D 0xC7A7
接收的电子欺骗成为 0x406455 0xC7A7(仍未被检出)
然后,在所述畸变之前加入仿射变换,在这情况下,切换每两位。
例子2
类别 消息 残数(CRC)
原版 0x2A301C 0xDAC2
经电子欺骗成为 0xC06454 0xDAC2(匹配)
接着于接收端每两位交替(仿射变换直接的选择):
接收的原版便是 0x15302C 0x2728
接收的电子欺骗成为 0xC098A8 0x3289(不匹配,电子欺骗可被检出)
下一个情况是在接收端每两位交替及切换第一位:
接收的原版便是 0x95302C 0x2BC4
接收的电子欺骗成为 0x4098A8 0x3E65(不匹配,不同检测)
仿射变换的非直接选择要求就所述系统对已知多项式的已知关系作出严密的分析,当中需要概率计算。
那么在例子1中发生什么?可通过谈论距离进行解释,但距离在不同的情况下具有不同的意思。在数轴上,两点之间的距离,譬如7和4之间,正是它们之差的绝对值(|7–4|=3)。在欧氏二维空间,两点之间的距离,譬如a=(x0,y0)和c=(x1,y1),人通常会想及就顶点为(x0,y0)、(x1,y0)、(x1,y1)的三角形使用毕氏定理。不失普遍性,是直角三角形之斜边。所以,
距离
距离的其他可能的定义是:
(*)距离
此定义(*)有点奇特的,它指所述距离定义为仅是较长一边的长度。
(**)距离
此距离的定义(**)指它仅是那两边的和,忽略平方根。
(***)距离
此定义(***)较奇特,两不同的点之间的距离总是1。
使用有限集的数字时,所述奇特情况持续。让我们选具有素元alpha(α)的域F16,α2:=α+1。
0=0000
1=0001
α=0010
α2=0100
α3=1000
α4=0011
α5=0110
α6=1100
α7=1011
α8=0101
α9=1010
α10=0111
α11=1110
α12=1111
α13=1101
α14=1001
或,
0=0*α3+0*α2+0*α1+0*α0
1=0*α3+0*α2+0*α1+1*α0
α=0*α3+0*α2+1*α1+0*α0
α2=0*α3+1*α2+0*α1+0*α0
α3=1*α3+0*α2+0*α1+0*α0
α4:=(α+1)根据定义=0*α3+0*α2+1*α1+1*α0
α5=(α4*α1)=((α+1)*α)=α2+α=0*α3+1*α2+1*α1+0*α0
α6=(α4*α2)=((α+1)*α2)=α3+α2=1*α3+1*α2+0*α1+0*α0
α7=(α4*α3)=((α+1)*α3)=α4+α3=1*α3+0*α2+1*α1+1*α0等等……
α4与α之间的“距离”是1,原因是α4=α+1,暗示了α4-α=(α+1)-α=1。或者使用所述系数位:
同样地,α8与α4之间的距离是(a2+1)-(α+1)=α2+α。
或者使用所述位:
若我们根据所述4位二进制数的数顺序重新排列上表,我们看出不同的次序和距离的情况:
0-0000
1-0001
α-0010
α4-0011
α2-0100
α8-0101
α5-0110
α10-0111
α3-1000
α14-1001
α9-1010
α7-1011
α6-1100
α13-1101
α11-1110
α12-1111
还有另一方法去看例子1的电子欺骗的检测失败。假设我们有两个消息m1和m2,两者具有相同的CRC,称作r。那么,
r1=m1(模n),就某个n,及
r1=m2(模n)。
这意味着:
所以称作r2=(m2+d)(mod n)的余部对于所述两个经修改的消息中的每个也相同。
一般来说,正交变换暗示在欧氏空间中所述变换保存共线性、距离和垂直。三维空间的旋转和平移是例子。仿射变换暗示它保存共线性,但非保存距离和垂直,然而它提供存在性和独特性。仿射变换保存线的次序。切变是非正交的仿射变换的例子。前向纠错(FEC)EDAC可与仿射变换一起使用,原因是它是无损的。仿射变换(或仿射形式(morphism))的较正式的定义是:映射T:Em→Em被称为仿射变换,条件是有可逆的m乘m矩阵A与向量从而对于所有的
Tx=Ax+b。
不可逆的变换暗示它不能是仿射的,原因是存在性标准为仿射变换的必要条件。我们如此定义非公理变换,以暗示它不保存共线性、距离或垂直;且它并不暗示存在性或独特性。非公理变换是供与自动重复请求(ARQ)EDAC一起使用、加强数字签名的用途使用或与其他信息保证方法一起使用。非公理变换提供映射S:
S:Eu→Ev。
我们定义LangGanong变换为与P线性系统矩阵的系数矩阵相乘,所指P线性系统矩阵由在特定的Zariski表面上使用LangGanong定理产生。建议具有大亏格的所述表面为首选的。就选择LangGanong变换的直接的例子而言:
假设,
z2=xy5+y(作为我们的Zariski表面),
及f=x,所以p=2,
及g(x,y)=xy5+y。
而t的程度的界限为4。我们找出ag的公式是
或者找出ag是根据LangGanong定理,
那么,
及C2=[000010000000000]。
所述变换如所属技术领域公知般进行。
交织
如距离一样,“交织”在不同情况下具有不同意思。在某些现有技术中,交织在猝发错误为普遍的那些情况下使用,以分散周围的顺序数据,致使导致不可被检出的或不可纠正的错误的猝发的可能性低。在所述磁带机EDAC专利的案子中,磁带边缘较易受影响而发生错误,因此磁带边缘的物理磁道编号从逻辑上重新排列(‘交织’),来将错误的概率分布至其他磁道。所述三维正交专利将一排一排和/或一栏一栏的数据‘交织’,同样地是为要减低猝发错误的影响。所述Turbo专利陈述了若干目的,总结如下:1)很高的纠正能力、2)高效能、3)高可靠性的译码、4)很高的位速率、5)相对地容易的编码器和译码器的制造、6)要求仅一个时钟、7)高的总编码效率、8)高性能译码器、9)在硅表面上植入所述译码方法、10)制造许多种类的译码器、11)可获利、12)简单、以及13)用于多种不同的应用。这些Turbo编码显然很好。再一次,在所述涵盖交织的Turbo专利中,其多数实施例的使用都是重新排列顺序数据,以改善译码器的纠正能力,正如人对EDAC方法所预期的一样。
我们的交织的一个目标是仅去改变数据的次序,致使所述编码导致独特的残数。就非普通大小的数据消息而言,通过不去将所述交织限定为正交的、线性的或可能可逆的,交织方式的数目得以大大提升。在非公理变换的实施例中,结果可能源自以下这样的映射(形式或关系):
S:Eu→Ev,
唯一的规则会是就某特定输入而言所述映射为可重复的。
工业应用
所述设备及方法扩充某特定EDAC系统的能力,以及提供嵌入式系统在其生命周期内免受网际攻击的经改良的防护。所述设备及方法也应用于其他数字数据的保密的递送。
一般来说,本发明通过在系统开发时与简单、扩展的签名联系去识别与确保计算机系统内启动固件可靠的执行而被改良,从而容许在系统验证和认证期间所述签名的记录与文件编制,以及容许监控与校验所述固件的生命周期的各方面,例如配置管理归档、字段加载验证、运行时间验证、通过运行健全维护系统对挑战作出响应、登录资料档案库的端口的验证、认证授权的验证与可追踪性、研发人员进行的历史跟踪、在代管档案内、以及在下一代系统中的重新使用中。可以有大量若干不同的签名通过不同的变换或畸变与输入的数字数据联系。所述处理启动固件的实施例仅供说明之用,并不暗示会限制它在启动固件的数字数据上的使用。
参考
美国专利参考:
美国专利号3,786,439 1974年1月15日 McDonald等人。
美国专利号5,392,299 1995年2月21日 Rhines等人。
美国专利号5,446,747 1995年8月29日 Berrou。
美国专利号5,673,316 1997年9月30日 Auerbach等人。
美国专利号4,821,268 1989年4月11日 Berlekamp等人。
美国专利号4,633,470 1986年12月30日 Welch等人。
美国专利号7,672,453 2010年3月2日 Matolak。
其他参考:
[1]Cryptography and Decoding Reed-Solomon Codes as a Hard Problem(作为难题的加密和解码里德-所罗门代码),A.Kiayias,M.Yung,IEEE,2005,0-7803-9491-7/05。
[2]Keying Hash Functions for MessageAuthentication(键入哈希函数以用于消息认证),M.Bellare等,Advances in Cryptography–Crypto 96Proceedings(密码学进展-加密96进展),1996年6月。
[3]Near Optimum Error Correcting Coding And Decoding:Turbo-Codes(临近最优纠错编码和解码:turbo-代码),C.Berrou,IEEE,1996,0090-6778/96。
[4]Factoring Large Numbers with the TWINKLE Device(Extended Abstract)(使用移动装置对大数字进行因子分解(扩展的摘要)),A.Shamir,魏茨曼科学研究所。
[5]A New Program for Computing the P-Linear System Cardinality that Determinesthe Group of Weil Divisors of a Zariski Surface(用于计算确定Zariski表面的一组韦伊除子的p-线性系统的基数的新程序),C.Rogers,堪萨斯大学,1995。
[6]Scientific American(科学美国人),206卷#2,1962年2月,96-108页。
[7]Choosing a CRC&Specifying Its Requirements for Field-Loadable Software(为场可加载软件选择CRC和规定其需求),C.Rogers,IEEE,2008,978-1-4224-2208-1/08.
[8]Proposing Improvements to Avoid the CRC Compromise and the SilentSpecification(为避免CRC折中和无声规范而提议的改进),C.Rogers,IEEE,2009,978-1-4244-4078-8/09。
Claims (25)
1.一种用于识别与保护一组源数据的完整性的方法,其包括以下步骤:
(a)将所述源数据通过变换以产生经变换的一组源日期;
(b)利用畸变函数使得所述经变换的一组源数据畸变以产生中间的一组源数据;以及
(c)将所述中间的一组源数据通过EDAC算法以产生余部,并将该余部附加到所述一组源数据以产生经编码的一组源数据。
2.根据权利要求1的方法,进一步包括以下步骤:将所述经编码的一组源数据通过第二EDAC算法以产生某第二余部,并将该余部附加到所述经编码的一组源数据。
3.根据权利要求1的方法,其中所述变换包括包含2-位交替的交织器。
4.根据权利要求1的方法,其中步骤(b)的畸变函数包括在所述经变换的一组源数据与二进制模式之间的异或运算。
5.根据权利要求1的方法,其中所述一组源数据是嵌入式的一组源数据。
6.根据权利要求5的方法,其中所述余部在嵌入所述一组源数据之前计算。
7.根据权利要求1的方法,其中所述变换包括包含福尼交织器的交织器。
8.根据权利要求1的方法,其中所述变换包括交织器,该交织器包含串行至并行数据转换器,该数据转换器的输出与纵横交错布线矩阵交织。
9.根据权利要求1的方法,其中所述变换包括交织器,该交织器包含串行至并行数据转换器,该数据转换器的输出与N乘N闪存交织。
10.根据权利要求1的方法,其中所述变换包括交织器,该交织器包含串行至并行数据转换器,该数据转换器的输出与N乘N RAM存储器交织。
11.根据权利要求4的方法,其中所述二进制模式是从N乘N RAM存储器抽出的。
12.根据权利要求1的方法,其中所述变换包括仿射变换。
13.根据权利要求1的方法,其中所述变换包括非公理变换。
14.根据权利要求1的方法,其中所述变换从群组中选择,该群组包含没有反函数的变换、没有保护刚体运动的变换、以及LangGanong变换矩阵。
15.根据权利要求2的方法,其中所述EDAC算法与所述第二EDAC算法相同。
16.根据权利要求2的方法,其中所述EDAC算法与所述第二EDAC算法不同。
17.根据权利要求16的方法,其中所述第一EDAC算法包括第一多项式,并且所述第二EDAC算法包括与所述第一多项式不同的某第二多项式。
18.根据权利要求1的方法,其中所述EDAC算法是从群组中选择的,该群组包含CRC算法、里德-所罗门编码、维特比编码、Turbo编码、MD5算法和SHA-1哈希算法。
19.根据权利要求5的方法,其中所述步骤(a)和(b)为可编程的。
20.根据权利要求17的方法,其中所述余部周期性地被校验。
21.根据权利要求17的方法,其中所述余部非周期性地被校验。
22.根据权利要求1的方法,进一步包括校验所述源日期的完整性的步骤,所述步骤包含重新计算所述余部、将所述余部的重新计算的值与在步骤(c)中计算出的所述余部的值比较、以及在所述比较显示所述余部与所述余部的所述重新计算的值不同时提供指示符。
23.根据权利要求22的方法,进一步包括将所述余部供给接收器的步骤。
24.根据权利要求23的方法,其中所述接收器是从群组中选择的,该群组包含显示装置、在串行总线上的布置、在并行总线上的布置和控制逻辑。
25.根据权利要求22的方法,进一步包括响应于请求而提供所述余部的步骤。
Applications Claiming Priority (3)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US28271310P | 2010-03-22 | 2010-03-22 | |
| US61/282,713 | 2010-03-22 | ||
| PCT/US2010/002682 WO2011119137A1 (en) | 2010-03-22 | 2010-10-05 | A method of identifying and protecting the integrity of a set of source data |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| CN102812431A true CN102812431A (zh) | 2012-12-05 |
Family
ID=44673481
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN2010800655963A Pending CN102812431A (zh) | 2010-03-22 | 2010-10-05 | 用于识别与保护一组源数据的完整性的方法 |
Country Status (5)
| Country | Link |
|---|---|
| US (1) | US8769373B2 (zh) |
| EP (1) | EP2438511B1 (zh) |
| JP (1) | JP2013523043A (zh) |
| CN (1) | CN102812431A (zh) |
| WO (1) | WO2011119137A1 (zh) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103280242A (zh) * | 2013-05-08 | 2013-09-04 | 中国人民解放军国防科学技术大学 | 适用于片上存储edac的可配置后台刷新方法 |
Families Citing this family (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US8874477B2 (en) | 2005-10-04 | 2014-10-28 | Steven Mark Hoffberg | Multifactorial optimization system and method |
| US8510841B2 (en) * | 2011-12-06 | 2013-08-13 | Raytheon Company | Detecting malware using patterns |
| US8966074B1 (en) | 2013-09-13 | 2015-02-24 | Network Kinetix, LLC | System and method for real-time analysis of network traffic |
| KR102287627B1 (ko) * | 2015-02-16 | 2021-08-10 | 한국전자통신연구원 | 길이가 64800이며, 부호율이 4/15인 ldpc 부호어 및 4096-심볼 맵핑을 위한 비트 인터리버 및 이를 이용한 비트 인터리빙 방법 |
| US10282224B2 (en) | 2015-09-22 | 2019-05-07 | Qualcomm Incorporated | Dynamic register virtualization |
| EP3378005B1 (en) * | 2015-11-19 | 2020-01-08 | Nagravision S.A. | Method to verify the execution integrity of an application in a target device |
| RU2666645C1 (ru) * | 2017-08-10 | 2018-09-11 | Акционерное общество "Лаборатория Касперского" | Система и способ обеспечения безопасного изменения конфигурации систем |
| DE102018220711A1 (de) * | 2018-11-30 | 2020-06-04 | Robert Bosch Gmbh | Messung der Anfälligkeit von KI-Modulen gegen Täuschungsversuche |
| US10951544B2 (en) * | 2019-01-30 | 2021-03-16 | The Boeing Company | Apparatus and method of crosschecking data copies using one or more voter elements |
| US11265019B1 (en) * | 2020-12-01 | 2022-03-01 | Huawei Technologies Co., Ltd. | Parallel polar code with shared data and cooperative decoding |
Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US3508194A (en) * | 1964-04-06 | 1970-04-21 | Ibm | Error detection and correction system |
| US3786439A (en) * | 1972-12-26 | 1974-01-15 | Ibm | Error detection systems |
| US6618395B1 (en) * | 1999-05-27 | 2003-09-09 | 3Com Corporation | Physical coding sub-layer for transmission of data over multi-channel media |
Family Cites Families (598)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| NL82289C (zh) | 1949-03-11 | |||
| NL79872C (zh) | 1950-01-11 | |||
| US2956124A (en) | 1958-05-01 | 1960-10-11 | Bell Telephone Labor Inc | Continuous digital error correcting system |
| BE623802A (zh) | 1961-10-19 | |||
| US3144635A (en) | 1961-12-14 | 1964-08-11 | Ibm | Error correcting system for binary erasure channel transmission |
| US3551886A (en) | 1968-07-16 | 1970-12-29 | Teletype Corp | Automatic error detection and correction system |
| US3629824A (en) | 1970-02-12 | 1971-12-21 | Ibm | Apparatus for multiple-error correcting codes |
| US3652998A (en) | 1970-03-01 | 1972-03-28 | Codex Corp | Interleavers |
| US3639900A (en) | 1970-05-27 | 1972-02-01 | Ibm | Enhanced error detection and correction for data systems |
| US3931504A (en) | 1972-02-07 | 1976-01-06 | Basic Computing Arts, Inc. | Electronic data processing security system and method |
| US4030067A (en) | 1975-12-29 | 1977-06-14 | Honeywell Information Systems, Inc. | Table lookup direct decoder for double-error correcting (DEC) BCH codes using a pair of syndromes |
| US4087856A (en) | 1976-06-30 | 1978-05-02 | International Business Machines Corporation | Location dependence for assuring the security of system-control operations |
| US4181969A (en) | 1978-01-18 | 1980-01-01 | Westinghouse Electric Corp. | System for detecting and isolating static bit faults in a network of arithmetic units |
| US4213188A (en) | 1978-08-30 | 1980-07-15 | Akushsky Izrail Y | Apparatus for detecting and correcting errors in arithmetic processing of data represented in the numerical system of residual classes |
| US4442486A (en) | 1981-11-25 | 1984-04-10 | U.S. Philips Corporation | Protected programmable apparatus |
| US4777595A (en) | 1982-05-07 | 1988-10-11 | Digital Equipment Corporation | Apparatus for transferring blocks of information from one node to a second node in a computer network |
| US4723284A (en) | 1983-02-14 | 1988-02-02 | Prime Computer, Inc. | Authentication system |
| US4567594A (en) | 1983-06-07 | 1986-01-28 | Burroughs Corporation | Reed-Solomon error detecting and correcting system employing pipelined processors |
| US4592019A (en) | 1983-08-31 | 1986-05-27 | At&T Bell Laboratories | Bus oriented LIFO/FIFO memory |
| US4633470A (en) | 1983-09-27 | 1986-12-30 | Cyclotomics, Inc. | Error correction for algebraic block codes |
| WO1986001026A1 (en) | 1984-07-21 | 1986-02-13 | Sony Corporation | Apparatus for recording and/or reproducing optical cards |
| CA1238427A (en) | 1984-12-18 | 1988-06-21 | Jonathan Oseas | Code protection using cryptography |
| US4870607A (en) | 1986-07-03 | 1989-09-26 | Nec Corporation | Error detection carried out by the use of unused modulo-m code |
| US4752904A (en) | 1986-07-28 | 1988-06-21 | International Business Machines Corporation | Efficient structure for computing mixed-radix projections from residue number systems |
| US4809274A (en) | 1986-09-19 | 1989-02-28 | M/A-Com Government Systems, Inc. | Digital audio companding and error conditioning |
| US5224160A (en) | 1987-02-23 | 1993-06-29 | Siemens Nixdorf Informationssysteme Ag | Process for securing and for checking the integrity of the secured programs |
| JPS63240625A (ja) | 1987-03-27 | 1988-10-06 | Nec Corp | 障害検出方式 |
| US4833678A (en) | 1987-07-22 | 1989-05-23 | Cyclotomics, Inc. | Hard-wired serial Galois field decoder |
| US4908861A (en) | 1987-08-28 | 1990-03-13 | International Business Machines Corporation | Data authentication using modification detection codes based on a public one way encryption function |
| US4821268A (en) | 1987-10-26 | 1989-04-11 | Cyclotomics, Inc. | Soft decision Reed-Solomon decoder |
| US4918653A (en) | 1988-01-28 | 1990-04-17 | International Business Machines Corporation | Trusted path mechanism for an operating system |
| USRE34088E (en) | 1988-03-09 | 1992-10-06 | Seagate Technology, Inc. | On-the-fly error correction |
| US4905281A (en) | 1988-05-04 | 1990-02-27 | Halliburton Company | Security apparatus and method for computers connected to telephone circuits |
| US4926374A (en) | 1988-11-23 | 1990-05-15 | International Business Machines Corporation | Residue checking apparatus for detecting errors in add, subtract, multiply, divide and square root operations |
| US5069547A (en) | 1988-11-23 | 1991-12-03 | The Boeing Company | Multitrack multilevel sensing system with error detecting |
| US5081629A (en) | 1989-05-08 | 1992-01-14 | Unisys Corporation | Fault isolation for multiphase clock signals supplied to dual modules which are checked by comparison using residue code generators |
| GB9003322D0 (en) | 1990-02-14 | 1990-04-11 | Inmos Ltd | Decoder |
| US5249294A (en) | 1990-03-20 | 1993-09-28 | General Instrument Corporation | Determination of time of execution of predetermined data processing routing in relation to occurrence of prior externally observable event |
| US5051745A (en) | 1990-08-21 | 1991-09-24 | Pkware, Inc. | String searcher, and compressor using same |
| FR2675971B1 (fr) | 1991-04-23 | 1993-08-06 | France Telecom | Procede de codage correcteur d'erreurs a au moins deux codages convolutifs systematiques en parallele, procede de decodage iteratif, module de decodage et decodeur correspondants. |
| FR2675968B1 (fr) | 1991-04-23 | 1994-02-04 | France Telecom | Procede de decodage d'un code convolutif a maximum de vraisemblance et ponderation des decisions, et decodeur correspondant. |
| US5359721A (en) | 1991-12-18 | 1994-10-25 | Sun Microsystems, Inc. | Non-supervisor mode cross address space dynamic linking |
| US5392299A (en) | 1992-01-15 | 1995-02-21 | E-Systems, Inc. | Triple orthogonally interleaed error correction system |
| US5361359A (en) | 1992-08-31 | 1994-11-01 | Trusted Information Systems, Inc. | System and method for controlling the use of a computer |
| US7089212B2 (en) | 1992-12-15 | 2006-08-08 | Sl Patent Holdings Llc | System and method for controlling access to protected information |
| US6614914B1 (en) | 1995-05-08 | 2003-09-02 | Digimarc Corporation | Watermark embedder and reader |
| FR2712760B1 (fr) | 1993-11-19 | 1996-01-26 | France Telecom | Procédé pour transmettre des bits d'information en appliquant des codes en blocs concaténés. |
| US5420640A (en) | 1993-12-03 | 1995-05-30 | Scientific-Atlanta, Inc. | Memory efficient method and apparatus for sync detection |
| US5559884A (en) | 1994-06-30 | 1996-09-24 | Microsoft Corporation | Method and system for generating and auditing a signature for a computer program |
| US5864683A (en) | 1994-10-12 | 1999-01-26 | Secure Computing Corporartion | System for providing secure internetwork by connecting type enforcing secure computers to external network for limiting access to data based on user and process access rights |
| WO1996016401A1 (fr) | 1994-11-17 | 1996-05-30 | Matsushita Electric Industrial Co., Ltd. | Appareil generateur de marquage, procede de formation d'un marquage au laser sur disque optique, appareil de reproduction, disque optique et procede de production de disque optique |
| USRE39653E1 (en) | 1994-11-17 | 2007-05-22 | Matsushita Electric Industrial Co., Ltd. | Mark forming apparatus, method of forming laser mark on optical disk, reproducing apparatus, optical disk and method of producing optical disk |
| FR2730370B1 (fr) | 1995-02-07 | 1997-04-25 | France Telecom | Dispositif de reception de signaux numeriques a structure iterative, module et procede correspondants |
| DE69638018D1 (de) | 1995-02-13 | 2009-10-15 | Intertrust Tech Corp | Systeme und Verfahren zur Verwaltung von gesicherten Transaktionen und zum Schutz von elektronischen Rechten |
| US5901127A (en) * | 1995-06-30 | 1999-05-04 | Sony Corporation | Data recording method and apparatus, data record medium and data reproducing method and apparatus |
| US6006328A (en) | 1995-07-14 | 1999-12-21 | Christopher N. Drake | Computer software authentication, protection, and security system |
| DE69618509T2 (de) | 1995-07-14 | 2002-08-29 | Sony Corp | Übertragung, Aufzeichnung und Wiedergabe von Daten |
| US5757915A (en) | 1995-08-25 | 1998-05-26 | Intel Corporation | Parameterized hash functions for access control |
| US5633929A (en) | 1995-09-15 | 1997-05-27 | Rsa Data Security, Inc | Cryptographic key escrow system having reduced vulnerability to harvesting attacks |
| US5608801A (en) | 1995-11-16 | 1997-03-04 | Bell Communications Research, Inc. | Efficient cryptographic hash functions and methods for amplifying the security of hash functions and pseudo-random functions |
| US6067622A (en) | 1996-01-02 | 2000-05-23 | Moore; Steven Jerome | Software security system using remove function to restrict unauthorized duplicating and installation of an application program |
| US5673316A (en) | 1996-03-29 | 1997-09-30 | International Business Machines Corporation | Creation and distribution of cryptographic envelope |
| FR2747255B1 (fr) | 1996-04-03 | 1998-07-10 | France Telecom | Procede et dispositif de codage convolutif de blocs de donnees, et procede et dispositif de decodage correspondants |
| US6023783A (en) | 1996-05-15 | 2000-02-08 | California Institute Of Technology | Hybrid concatenated codes and iterative decoding |
| US5892899A (en) | 1996-06-13 | 1999-04-06 | Intel Corporation | Tamper resistant methods and apparatus |
| US6118870A (en) | 1996-10-09 | 2000-09-12 | Lsi Logic Corp. | Microprocessor having instruction set extensions for decryption and multimedia applications |
| US6587563B1 (en) | 1997-02-15 | 2003-07-01 | Apple Computer, Inc. | Cryptographic system using chaotic dynamics |
| US6044468A (en) | 1997-08-25 | 2000-03-28 | Emc Corporation | Secure transmission using an ordinarily insecure network communication protocol such as SNMP |
| US6411715B1 (en) | 1997-11-10 | 2002-06-25 | Rsa Security, Inc. | Methods and apparatus for verifying the cryptographic security of a selected private and public key pair without knowing the private key |
| US6714931B1 (en) | 1998-04-29 | 2004-03-30 | Ncr Corporation | Method and apparatus for forming user sessions and presenting internet data according to the user sessions |
| US6941463B1 (en) | 1998-05-14 | 2005-09-06 | Purdue Research Foundation | Secure computational outsourcing techniques |
| US6957341B2 (en) | 1998-05-14 | 2005-10-18 | Purdue Research Foundation | Method and system for secure computational outsourcing and disguise |
| US6684199B1 (en) | 1998-05-20 | 2004-01-27 | Recording Industry Association Of America | Method for minimizing pirating and/or unauthorized copying and/or unauthorized access of/to data on/from data media including compact discs and digital versatile discs, and system and data media for same |
| DE69936683T2 (de) | 1998-06-01 | 2008-04-30 | Her Majesty The Queen In Right Of Canada As Represented By The Minister Of Industry, Ottawa | Verschachtelung unter Verwendung von Inkrementen basierend auf dem Goldenen Schnitt |
| WO2000022621A1 (fr) | 1998-10-14 | 2000-04-20 | Sony Corporation | Dispositif et procede de transmission de donnees, et support d'enregistrement de donnees |
| US6321338B1 (en) | 1998-11-09 | 2001-11-20 | Sri International | Network surveillance |
| DE19851690A1 (de) | 1998-11-10 | 2000-05-11 | Ibm | Residuum-Prüfung von Datenumwandlungen |
| US6763370B1 (en) | 1998-11-16 | 2004-07-13 | Softricity, Inc. | Method and apparatus for content protection in a secure content delivery system |
| US7017188B1 (en) | 1998-11-16 | 2006-03-21 | Softricity, Inc. | Method and apparatus for secure content delivery over broadband access networks |
| US7685425B1 (en) | 1999-03-31 | 2010-03-23 | British Telecommunications Public Limited Company | Server computer for guaranteeing files integrity |
| JP3976932B2 (ja) | 1999-03-31 | 2007-09-19 | キヤノン株式会社 | データ処理方法及び装置並びに記憶媒体 |
| FR2792141B1 (fr) | 1999-04-09 | 2001-06-15 | Bull Cp8 | Procede de securisation d'un ou plusieurs ensembles electroniques mettant en oeuvre un meme algorithme cryptographique avec cle secrete, une utilisation du procede et l'ensemble electronique |
| US6804778B1 (en) | 1999-04-15 | 2004-10-12 | Gilian Technologies, Ltd. | Data quality assurance |
| US7644439B2 (en) | 1999-05-03 | 2010-01-05 | Cisco Technology, Inc. | Timing attacks against user logon and network I/O |
| US6681331B1 (en) | 1999-05-11 | 2004-01-20 | Cylant, Inc. | Dynamic software system intrusion detection |
| US7096499B2 (en) | 1999-05-11 | 2006-08-22 | Cylant, Inc. | Method and system for simplifying the structure of dynamic execution profiles |
| US7185367B2 (en) | 1999-05-11 | 2007-02-27 | Cylant, Inc. | Method and system for establishing normal software system behavior and departures from normal behavior |
| US6351832B1 (en) | 1999-05-28 | 2002-02-26 | Lucent Technologies Inc. | Turbo code symbol interleaver |
| US6473878B1 (en) | 1999-05-28 | 2002-10-29 | Lucent Technologies Inc. | Serial-concatenated turbo codes |
| US6594761B1 (en) | 1999-06-09 | 2003-07-15 | Cloakware Corporation | Tamper resistant software encoding |
| US6957344B1 (en) | 1999-07-09 | 2005-10-18 | Digital Video Express, L.P. | Manufacturing trusted devices |
| US7461402B1 (en) | 1999-07-14 | 2008-12-02 | Symantec Corporation | System and method for preventing detection of a selected process running on a computer |
| FR2796780B1 (fr) | 1999-07-21 | 2003-09-19 | Groupe Ecoles Telecomm | Procede et dispositif de codage a au moins deux codages en parallele et permutation amelioree, et procede et dispositif de decodage correspondants |
| US6915426B1 (en) | 1999-07-23 | 2005-07-05 | Networks Associates Technology, Inc. | System and method for enabling authentication at different authentication strength-performance levels |
| US7243236B1 (en) | 1999-07-29 | 2007-07-10 | Intertrust Technologies Corp. | Systems and methods for using cryptography to protect secure and insecure computing environments |
| US7430670B1 (en) | 1999-07-29 | 2008-09-30 | Intertrust Technologies Corp. | Software self-defense systems and methods |
| US7389466B1 (en) | 1999-08-12 | 2008-06-17 | Texas Instruments Incorporated | ECC in computer system with associated mass storage device, and method for operating same |
| JP2001057022A (ja) | 1999-08-18 | 2001-02-27 | Sony Corp | データ記録媒体、データ記録装置、データ記録方法、データ再生装置およびデータ再生方法 |
| WO2001015380A1 (fr) | 1999-08-20 | 2001-03-01 | Sony Corporation | Systeme et procede d'emission d'informations, lecteur et procede d'acces, support d'enregistrement d'informations, et dispositif et procede de production de supports d'enregistrement |
| US7757097B2 (en) | 1999-09-03 | 2010-07-13 | Purdue Research Foundation | Method and system for tamperproofing software |
| JP2001093226A (ja) | 1999-09-21 | 2001-04-06 | Sony Corp | 情報通信システムおよび方法、ならびに、情報通信装置および方法 |
| US6795947B1 (en) | 1999-10-07 | 2004-09-21 | The Regents Of The University Of California | Parity check outer code and runlength constrained outer code usable with parity bits |
| US7213154B1 (en) | 1999-11-02 | 2007-05-01 | Cisco Technology, Inc. | Query data packet processing and network scanning method and apparatus |
| JP2001142764A (ja) | 1999-11-12 | 2001-05-25 | Japan Science & Technology Corp | ログ・ファイル保護システム |
| US7475428B2 (en) | 2002-06-20 | 2009-01-06 | Angel Secure Networks, Inc. | Secure detection network system |
| US6990591B1 (en) | 1999-11-18 | 2006-01-24 | Secureworks, Inc. | Method and system for remotely configuring and monitoring a communication device |
| WO2001039140A1 (fr) | 1999-11-25 | 2001-05-31 | Fujitsu Limited | Dispositif de securite et programme de securite de stockage sur support lisible par ordinateur |
| US6832316B1 (en) | 1999-12-22 | 2004-12-14 | Intertrust Technologies, Corp. | Systems and methods for protecting data secrecy and integrity |
| US6957348B1 (en) | 2000-01-10 | 2005-10-18 | Ncircle Network Security, Inc. | Interoperability of vulnerability and intrusion detection systems |
| US7124439B1 (en) | 2000-03-15 | 2006-10-17 | Nokia Mobile Phones, Ltd. | Secure user action request indicator |
| US6842861B1 (en) | 2000-03-24 | 2005-01-11 | Networks Associates Technology, Inc. | Method and system for detecting viruses on handheld computers |
| US7120934B2 (en) | 2000-03-30 | 2006-10-10 | Ishikawa Mark M | System, method and apparatus for detecting, identifying and responding to fraudulent requests on a network |
| US6829671B1 (en) | 2000-04-04 | 2004-12-07 | Promos Technologies Inc. | Method and system for improved audio data retrieval from an optical media |
| JP2001290707A (ja) * | 2000-04-05 | 2001-10-19 | Kazumi Mochizuki | データ処理方法、データ処理プログラムを格納したコンピュータ読取可能な記憶媒体、およびデータ処理装置 |
| US7574740B1 (en) | 2000-04-28 | 2009-08-11 | International Business Machines Corporation | Method and system for intrusion detection in a computer network |
| US7565692B1 (en) | 2000-05-30 | 2009-07-21 | At&T Wireless Services, Inc. | Floating intrusion detection platforms |
| US7162649B1 (en) | 2000-06-30 | 2007-01-09 | Internet Security Systems, Inc. | Method and apparatus for network assessment and authentication |
| US7356696B1 (en) | 2000-08-01 | 2008-04-08 | Lucent Technologies Inc. | Proofs of work and bread pudding protocols |
| US7155015B2 (en) | 2000-08-08 | 2006-12-26 | Hitachi, Ltd. | Optical disk apparatus and data randomizing method using for optical disk apparatus |
| US7672453B1 (en) | 2000-08-21 | 2010-03-02 | Lockheed Martin Corporation | Data encryption by nonlinear transfer function |
| US7181769B1 (en) | 2000-08-25 | 2007-02-20 | Ncircle Network Security, Inc. | Network security system having a device profiler communicatively coupled to a traffic monitor |
| US7642566B2 (en) | 2006-06-12 | 2010-01-05 | Dsm Solutions, Inc. | Scalable process and structure of JFET for small and decreasing line widths |
| US7165173B1 (en) | 2000-09-01 | 2007-01-16 | Samsung Electronics Co., Ltd. | System and method for secure over-the-air administration of a wireless mobile station |
| US7475405B2 (en) | 2000-09-06 | 2009-01-06 | International Business Machines Corporation | Method and system for detecting unusual events and application thereof in computer intrusion detection |
| FI114749B (fi) | 2000-09-11 | 2004-12-15 | Nokia Corp | Poikkeamien ilmaisujärjestelmä ja menetelmä sen opettamiseksi |
| US6768942B1 (en) | 2000-09-18 | 2004-07-27 | Navigation Technologies Corp. | Navigation system with decryption functions and secure geographic database |
| US7237123B2 (en) | 2000-09-22 | 2007-06-26 | Ecd Systems, Inc. | Systems and methods for preventing unauthorized use of digital content |
| JP3419391B2 (ja) | 2000-10-05 | 2003-06-23 | 日本電気株式会社 | 認証拒否端末に対し特定条件でアクセスを許容するlan |
| US7313825B2 (en) | 2000-11-13 | 2007-12-25 | Digital Doors, Inc. | Data security system and method for portable device |
| US6718276B2 (en) | 2000-11-28 | 2004-04-06 | Agilent Technologies, Inc. | Method and apparatus for characterizing frequency response on an error performance analyzer |
| JP4300705B2 (ja) | 2000-12-05 | 2009-07-22 | ソニー株式会社 | データ転送システム、データ転送装置、データ転送方法、記録媒体 |
| JP2002261748A (ja) | 2000-12-28 | 2002-09-13 | Sony Corp | データ送信装置及び方法並びにデータ記録装置及び方法 |
| US7627897B2 (en) | 2001-01-03 | 2009-12-01 | Portauthority Technologies Inc. | Method and apparatus for a reactive defense against illegal distribution of multimedia content in file sharing networks |
| US7631349B2 (en) | 2001-01-11 | 2009-12-08 | Digi International Inc. | Method and apparatus for firewall traversal |
| US20020147803A1 (en) | 2001-01-31 | 2002-10-10 | Dodd Timothy David | Method and system for calculating risk in association with a security audit of a computer network |
| JP4190742B2 (ja) | 2001-02-09 | 2008-12-03 | ソニー株式会社 | 信号処理装置及び方法 |
| US7647402B2 (en) | 2001-03-08 | 2010-01-12 | International Business Machines Corporation | Protecting contents of computer data files from suspected intruders by renaming and hiding data files subjected to intrusion |
| US7089592B2 (en) | 2001-03-15 | 2006-08-08 | Brighterion, Inc. | Systems and methods for dynamic detection and prevention of electronic fraud |
| US7721110B2 (en) | 2001-04-06 | 2010-05-18 | Mcafee, Inc. | System and method for secure and verified sharing of resources in a peer-to-peer network environment |
| US7603709B2 (en) | 2001-05-03 | 2009-10-13 | Computer Associates Think, Inc. | Method and apparatus for predicting and preventing attacks in communications networks |
| GB0111063D0 (en) | 2001-05-04 | 2001-06-27 | Abathorn Ltd | Method and apparatus for the creation of a self authenticating |
| JP4009437B2 (ja) | 2001-05-09 | 2007-11-14 | 株式会社ルネサステクノロジ | 情報処理装置 |
| WO2002097587A2 (en) | 2001-05-31 | 2002-12-05 | Internet Security Systems, Inc. | Method and system for implementing security devices in a network |
| US7237264B1 (en) | 2001-06-04 | 2007-06-26 | Internet Security Systems, Inc. | System and method for preventing network misuse |
| US7458094B2 (en) | 2001-06-06 | 2008-11-25 | Science Applications International Corporation | Intrusion prevention system |
| US7747853B2 (en) | 2001-06-06 | 2010-06-29 | Sony Corporation | IP delivery of secure digital content |
| JP4221286B2 (ja) | 2001-06-06 | 2009-02-12 | ヤフー! インコーポレイテッド | デジタル・コンテンツおよびストリーミングデータへのアクセスを管理するシステム及び方法 |
| DE10128305A1 (de) | 2001-06-12 | 2002-12-19 | Giesecke & Devrient Gmbh | Steuereinheit |
| AU2002322109A1 (en) | 2001-06-13 | 2002-12-23 | Intruvert Networks, Inc. | Method and apparatus for distributed network security |
| US7594267B2 (en) | 2001-06-14 | 2009-09-22 | Cisco Technology, Inc. | Stateful distributed event processing and adaptive security |
| ATE406026T1 (de) | 2001-06-14 | 2008-09-15 | Ibm | Eindringsdetektion in datenverarbeitungssystemen |
| US7673342B2 (en) | 2001-07-26 | 2010-03-02 | Mcafee, Inc. | Detecting e-mail propagated malware |
| NZ531131A (en) | 2001-08-13 | 2005-12-23 | Qualcomm Inc | Using permissions to allocate device resources to an application |
| US7571480B2 (en) | 2001-08-16 | 2009-08-04 | International Business Machines Corporation | Presentation of correlated events as situation classes |
| US7484105B2 (en) | 2001-08-16 | 2009-01-27 | Lenovo (Singapore) Ptd. Ltd. | Flash update using a trusted platform module |
| US7657935B2 (en) | 2001-08-16 | 2010-02-02 | The Trustees Of Columbia University In The City Of New York | System and methods for detecting malicious email transmission |
| US7464410B1 (en) | 2001-08-30 | 2008-12-09 | At&T Corp. | Protection against flooding of a server |
| US7308714B2 (en) | 2001-09-27 | 2007-12-11 | International Business Machines Corporation | Limiting the output of alerts generated by an intrusion detection sensor during a denial of service attack |
| GB0123417D0 (en) * | 2001-09-28 | 2001-11-21 | Memquest Ltd | Improved data processing |
| US7743404B1 (en) | 2001-10-03 | 2010-06-22 | Trepp, LLC | Method and system for single signon for multiple remote sites of a computer network |
| AU2002362419A1 (en) | 2001-10-03 | 2003-04-14 | The Trustees Of Columbia University In The City Of New York | Method and apparatus for watermarking and authenticating data |
| US7444679B2 (en) | 2001-10-31 | 2008-10-28 | Hewlett-Packard Development Company, L.P. | Network, method and computer readable medium for distributing security updates to select nodes on a network |
| JP3688628B2 (ja) | 2001-11-09 | 2005-08-31 | 株式会社東芝 | 信号処理方法及び装置、信号再生方法及び装置、記録媒体 |
| US7577998B1 (en) | 2001-11-16 | 2009-08-18 | Hewlett-Packard Development Company, L.P. | Method of detecting critical file changes |
| EP1315065B1 (en) | 2001-11-23 | 2007-10-10 | Protegrity Research & Development | Method for intrusion detection in a database system |
| US6952479B2 (en) | 2001-11-27 | 2005-10-04 | Macrovision Europe Limited | Dynamic copy protection of optical media |
| US7730303B2 (en) | 2001-11-27 | 2010-06-01 | Koninklijke Philips Electronics N.V. | Enhanced content resolution method |
| US7437762B2 (en) | 2001-11-29 | 2008-10-14 | International Business Machines Corporation | Method, computer program element and a system for processing alarms triggered by a monitoring system |
| US7475426B2 (en) | 2001-11-30 | 2009-01-06 | Lancope, Inc. | Flow-based detection of network intrusions |
| US7644151B2 (en) | 2002-01-31 | 2010-01-05 | Lancope, Inc. | Network service zone locking |
| US7512980B2 (en) | 2001-11-30 | 2009-03-31 | Lancope, Inc. | Packet sampling flow-based detection of network intrusions |
| US7586993B2 (en) | 2001-12-06 | 2009-09-08 | Texas Instruments Incorporated | Interleaver memory selectably receiving PN or counter chain read address |
| US7480799B2 (en) | 2001-12-11 | 2009-01-20 | Actional Corporation | Traffic manager for distributed computing environments |
| US7681034B1 (en) | 2001-12-12 | 2010-03-16 | Chang-Ping Lee | Method and apparatus for securing electronic data |
| JP3829724B2 (ja) | 2001-12-21 | 2006-10-04 | ソニー株式会社 | 記録媒体、記録方法および装置、再生装置および方法、ならびに、データ判別方法 |
| AU2003202876A1 (en) | 2002-01-04 | 2003-07-24 | Internet Security Systems, Inc. | System and method for the managed security control of processes on a computer system |
| US7739498B2 (en) | 2002-01-15 | 2010-06-15 | GlobalFoundries, Inc. | Method and apparatus for multi-table accessing of input/output devices using target security |
| US7743415B2 (en) | 2002-01-31 | 2010-06-22 | Riverbed Technology, Inc. | Denial of service attacks characterization |
| US7716485B2 (en) | 2002-02-01 | 2010-05-11 | Sca Ipla Holdings Inc. | Systems and methods for media authentication |
| JP4088082B2 (ja) | 2002-02-15 | 2008-05-21 | 株式会社東芝 | 未知コンピュータウイルスの感染を防止する装置およびプログラム |
| US7529242B1 (en) | 2002-02-15 | 2009-05-05 | Symantec Corporation | Routing network packets for multi-processor network flow analysis |
| US7458098B2 (en) | 2002-03-08 | 2008-11-25 | Secure Computing Corporation | Systems and methods for enhancing electronic communication security |
| US7228426B2 (en) | 2002-04-03 | 2007-06-05 | Microsoft Corporation | Integrity ordainment and ascertainment of computer-executable instructions with consideration for execution context |
| US7290282B1 (en) | 2002-04-08 | 2007-10-30 | Symantec Corporation | Reducing false positive computer virus detections |
| US7543333B2 (en) | 2002-04-08 | 2009-06-02 | Microsoft Corporation | Enhanced computer intrusion detection methods and systems |
| GB0208616D0 (en) | 2002-04-15 | 2002-05-22 | Neural Technologies Ltd | A system for identifying extreme behaviour in elements of a network |
| US7748045B2 (en) | 2004-03-30 | 2010-06-29 | Michael Frederick Kenrich | Method and system for providing cryptographic document retention with off-line access |
| FR2838892A1 (fr) * | 2002-04-23 | 2003-10-24 | Scm Microsystems Gmbh | Procede et dispositif de chiffrement de donnees numeriques |
| ATE405056T1 (de) | 2002-05-03 | 2008-08-15 | Nokia Siemens Networks Oy | Verfahren und system in einem kommunikationsnetz zur zuteilung und änderung von adressen auf streckenebene |
| IL149583A0 (en) | 2002-05-09 | 2003-07-06 | Kavado Israel Ltd | Method for automatic setting and updating of a security policy |
| US7058796B2 (en) | 2002-05-20 | 2006-06-06 | Airdefense, Inc. | Method and system for actively defending a wireless LAN against attacks |
| US7532895B2 (en) | 2002-05-20 | 2009-05-12 | Air Defense, Inc. | Systems and methods for adaptive location tracking |
| US7509675B2 (en) | 2002-05-29 | 2009-03-24 | At&T Intellectual Property I, L.P. | Non-invasive monitoring of the effectiveness of electronic security services |
| US7412057B2 (en) | 2002-05-31 | 2008-08-12 | Intel Corporation | Fast-software-implemented pseudo-random code generator |
| FR2840748B1 (fr) | 2002-06-05 | 2004-08-27 | France Telecom | Procede et systeme de verification de signatures electroniques et carte a microcircuit pour la mise en oeuvre du procede |
| US7181617B2 (en) | 2002-06-10 | 2007-02-20 | Kelley Wise | Remote virtual medical diagnostic imaging viewer |
| US7512977B2 (en) | 2003-06-11 | 2009-03-31 | Symantec Corporation | Intrustion protection system utilizing layers |
| US7549164B2 (en) | 2003-06-11 | 2009-06-16 | Symantec Corporation | Intrustion protection system utilizing layers and triggers |
| US7743257B2 (en) | 2002-06-27 | 2010-06-22 | Nxp B.V. | Security processor with bus configuration |
| US7373666B2 (en) | 2002-07-01 | 2008-05-13 | Microsoft Corporation | Distributed threat management |
| JP2004040307A (ja) | 2002-07-01 | 2004-02-05 | Canon Inc | 画像生成装置 |
| JP4115759B2 (ja) | 2002-07-01 | 2008-07-09 | 株式会社東芝 | 耐タンパプロセッサにおける共有ライブラリの使用方法およびそのプログラム |
| US7752665B1 (en) | 2002-07-12 | 2010-07-06 | TCS Commercial, Inc. | Detecting probes and scans over high-bandwidth, long-term, incomplete network traffic information using limited memory |
| US7162740B2 (en) | 2002-07-22 | 2007-01-09 | General Instrument Corporation | Denial of service defense by proxy |
| US7526809B2 (en) | 2002-08-08 | 2009-04-28 | Trend Micro Incorporated | System and method for computer protection against malicious electronic mails by analyzing, profiling and trapping the same |
| US7587762B2 (en) | 2002-08-09 | 2009-09-08 | Netscout Systems, Inc. | Intrusion detection system and network flow director method |
| US6917215B2 (en) | 2002-08-30 | 2005-07-12 | Matsushita Electric Industrial Co., Ltd. | Semiconductor integrated circuit and memory test method |
| US7467408B1 (en) | 2002-09-09 | 2008-12-16 | Cisco Technology, Inc. | Method and apparatus for capturing and filtering datagrams for network security monitoring |
| US6823383B2 (en) | 2002-09-10 | 2004-11-23 | Capital One Financial Corporation | Stealth network |
| US7730325B2 (en) | 2002-09-13 | 2010-06-01 | Bally Gaming, Inc. | Verification system and method |
| DE10242917A1 (de) | 2002-09-16 | 2004-03-25 | Siemens Ag | System zur Erfassung und Anzeige eines Sicherstatus von Geräten |
| JP4290401B2 (ja) | 2002-09-18 | 2009-07-08 | 三菱電機株式会社 | 量子鍵配送方法および通信装置 |
| US7472421B2 (en) | 2002-09-30 | 2008-12-30 | Electronic Data Systems Corporation | Computer model of security risks |
| US7469418B1 (en) | 2002-10-01 | 2008-12-23 | Mirage Networks, Inc. | Deterring network incursion |
| US8260961B1 (en) | 2002-10-01 | 2012-09-04 | Trustwave Holdings, Inc. | Logical / physical address state lifecycle management |
| US7337471B2 (en) | 2002-10-07 | 2008-02-26 | Symantec Corporation | Selective detection of malicious computer code |
| US7657838B2 (en) | 2002-10-08 | 2010-02-02 | At&T Intellectual Property I, L.P. | Preventing execution of programs that are embedded in email messages |
| US7437760B2 (en) | 2002-10-10 | 2008-10-14 | International Business Machines Corporation | Antiviral network system |
| US7412053B1 (en) | 2002-10-10 | 2008-08-12 | Silicon Image, Inc. | Cryptographic device with stored key data and method for using stored key data to perform an authentication exchange or self test |
| JP2004134044A (ja) | 2002-10-15 | 2004-04-30 | Sony Corp | データ記録媒体、データ記録方法および情報端末装置、ならびに、情報サービス方法および情報サービス装置 |
| US20040078747A1 (en) * | 2002-10-21 | 2004-04-22 | Miller David H. | Generalized forney algorithm circuit |
| US7540028B2 (en) | 2002-10-25 | 2009-05-26 | Intel Corporation | Dynamic network security apparatus and methods or network processors |
| WO2004040774A1 (en) | 2002-10-29 | 2004-05-13 | Samsung Electronics Co., Ltd. | Method and apparatus for deinterleaving interleaved data stream in a communication system |
| US7461404B2 (en) | 2002-11-04 | 2008-12-02 | Mazu Networks, Inc. | Detection of unauthorized access in a network |
| US7724907B2 (en) | 2002-11-05 | 2010-05-25 | Sony Corporation | Mechanism for protecting the transfer of digital content |
| US7149801B2 (en) | 2002-11-08 | 2006-12-12 | Microsoft Corporation | Memory bound functions for spam deterrence and the like |
| JP3960959B2 (ja) | 2002-11-08 | 2007-08-15 | 三洋電機株式会社 | 電子透かし埋め込み装置と方法ならびに電子透かし抽出装置と方法 |
| KR100481130B1 (ko) | 2002-11-08 | 2005-04-07 | 주식회사 웨어밸리 | 데이터베이스 시스템에 접속하지 않고 데이터베이스시스템을 모니터링하는 방법 |
| JP4099039B2 (ja) | 2002-11-15 | 2008-06-11 | 松下電器産業株式会社 | プログラム更新方法 |
| WO2004046844A2 (en) | 2002-11-18 | 2004-06-03 | Nokia Corporation | Faster authentication with parallel message processing |
| US7694343B2 (en) | 2002-11-27 | 2010-04-06 | Symantec Corporation | Client compliancy in a NAT environment |
| US7650638B1 (en) | 2002-12-02 | 2010-01-19 | Arcsight, Inc. | Network security monitoring system employing bi-directional communication |
| US7607169B1 (en) | 2002-12-02 | 2009-10-20 | Arcsight, Inc. | User interface for network security console |
| US7500266B1 (en) | 2002-12-03 | 2009-03-03 | Bbn Technologies Corp. | Systems and methods for detecting network intrusions |
| US7549166B2 (en) | 2002-12-05 | 2009-06-16 | International Business Machines Corporation | Defense mechanism for server farm |
| US7587763B2 (en) | 2002-12-12 | 2009-09-08 | Finite State Machine Labs, Inc. | Systems and methods for detecting a security breach in a computer system |
| US6938167B2 (en) | 2002-12-18 | 2005-08-30 | America Online, Inc. | Using trusted communication channel to combat user name/password theft |
| US7603704B2 (en) | 2002-12-19 | 2009-10-13 | Massachusetts Institute Of Technology | Secure execution of a computer program using a code cache |
| US7305564B2 (en) | 2002-12-19 | 2007-12-04 | International Business Machines Corporation | System and method to proactively detect software tampering |
| JP4146434B2 (ja) | 2002-12-20 | 2008-09-10 | 研一 澤田 | ウェブアプリケーションサーバ用支援プログラム及びサーバ |
| FR2849230B1 (fr) | 2002-12-24 | 2005-04-22 | Francois Bangui | Procede et dispositif de verification de l'integrite d'une application logicielle sans cle de chiffrement/dechiffrement |
| US7412723B2 (en) | 2002-12-31 | 2008-08-12 | International Business Machines Corporation | Method and system for morphing honeypot with computer security incident correlation |
| US7657937B1 (en) | 2003-01-02 | 2010-02-02 | Vmware, Inc. | Method for customizing processing and response for intrusion prevention |
| US7318163B2 (en) | 2003-01-07 | 2008-01-08 | International Business Machines Corporation | System and method for real-time detection of computer system files intrusion |
| US7483972B2 (en) | 2003-01-08 | 2009-01-27 | Cisco Technology, Inc. | Network security monitoring system |
| JP4331947B2 (ja) | 2003-01-17 | 2009-09-16 | 誠 加藤 | データ送信システム及びデータ送信方法並びに装置 |
| US7523503B2 (en) | 2003-01-21 | 2009-04-21 | Hewlett-Packard Development Company, L.P. | Method for protecting security of network intrusion detection sensors |
| US7519834B1 (en) | 2003-01-24 | 2009-04-14 | Nortel Networks Limited | Scalable method and apparatus for transforming packets to enable secure communication between two stations |
| JP4004521B2 (ja) | 2003-02-03 | 2007-11-07 | シャープ株式会社 | 符号化装置及び方法、復号装置及び方法、プログラム、並びに記録媒体 |
| US7467400B1 (en) | 2003-02-14 | 2008-12-16 | S2 Security Corporation | Integrated security system having network enabled access control and interface devices |
| CN1329911C (zh) | 2003-02-19 | 2007-08-01 | 威盛电子股份有限公司 | 扰频方法、写入数据产生方法及重复数据写入方法 |
| US7469049B1 (en) | 2003-03-04 | 2008-12-23 | Marvell International Ltd. | Data dependent scrambler with reduced overhead |
| EP1457858A1 (fr) | 2003-03-14 | 2004-09-15 | SCHLUMBERGER Systèmes | Procédé de sécurisation d'un ensemble électronique à cryptoprocesseur |
| JP4354201B2 (ja) | 2003-03-18 | 2009-10-28 | 富士通株式会社 | 不正アクセス対処システム、及び不正アクセス対処処理プログラム |
| JP4520703B2 (ja) | 2003-03-31 | 2010-08-11 | 富士通株式会社 | 不正アクセス対処システム、及び不正アクセス対処処理プログラム |
| US7562214B2 (en) | 2003-03-31 | 2009-07-14 | International Business Machines Corporation | Data processing systems |
| US7603710B2 (en) | 2003-04-03 | 2009-10-13 | Network Security Technologies, Inc. | Method and system for detecting characteristics of a wireless network |
| WO2004090675A2 (en) | 2003-04-03 | 2004-10-21 | Commvault Systems, Inc. | System and method for performing storage operations through a firewall |
| US7373519B1 (en) | 2003-04-09 | 2008-05-13 | Symantec Corporation | Distinguishing legitimate modifications from malicious modifications during executable computer file modification analysis |
| US7549167B1 (en) | 2003-04-10 | 2009-06-16 | George Mason Intellectual Properties, Inc. | Self-cleansing system |
| US6950039B2 (en) | 2003-04-10 | 2005-09-27 | Matsushita Electric Industrial Co., Ltd. | Information encoding apparatus, information encoding method, information re-encoding apparatus and information re-encoding method |
| US7590870B2 (en) | 2003-04-10 | 2009-09-15 | Lenovo (Singapore) Pte. Ltd. | Physical presence determination in a trusted platform |
| US7607010B2 (en) | 2003-04-12 | 2009-10-20 | Deep Nines, Inc. | System and method for network edge data protection |
| US7540029B1 (en) | 2003-04-16 | 2009-05-26 | Bbn Technologies Corp. | Methods and systems for reducing the spread of files on a network |
| US7716736B2 (en) | 2003-04-17 | 2010-05-11 | Cybersoft, Inc. | Apparatus, methods and articles of manufacture for computer virus testing |
| US7522908B2 (en) | 2003-04-21 | 2009-04-21 | Airdefense, Inc. | Systems and methods for wireless network site survey |
| US7640590B1 (en) | 2004-12-21 | 2009-12-29 | Symantec Corporation | Presentation of network source and executable characteristics |
| US7730175B1 (en) | 2003-05-12 | 2010-06-01 | Sourcefire, Inc. | Systems and methods for identifying the services of a network |
| US7603614B2 (en) | 2003-05-13 | 2009-10-13 | Aladdin Knowledge Systems Ltd. | Method and system for indicating an executable as trojan horse |
| US7441275B2 (en) | 2003-05-14 | 2008-10-21 | Northrop Grumman Corporation | Real-time recovery of compromised information |
| US7681235B2 (en) | 2003-05-19 | 2010-03-16 | Radware Ltd. | Dynamic network protection |
| US7464398B2 (en) | 2003-05-19 | 2008-12-09 | Alcatel Lucent | Queuing methods for mitigation of packet spoofing |
| US7617526B2 (en) | 2003-05-20 | 2009-11-10 | International Business Machines Corporation | Blocking of spam e-mail at a firewall |
| US7308716B2 (en) | 2003-05-20 | 2007-12-11 | International Business Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US7464404B2 (en) | 2003-05-20 | 2008-12-09 | International Business Machines Corporation | Method of responding to a truncated secure session attack |
| US7516487B1 (en) | 2003-05-21 | 2009-04-07 | Foundry Networks, Inc. | System and method for source IP anti-spoofing security |
| US7562390B1 (en) | 2003-05-21 | 2009-07-14 | Foundry Networks, Inc. | System and method for ARP anti-spoofing security |
| US7293063B1 (en) | 2003-06-04 | 2007-11-06 | Symantec Corporation | System utilizing updated spam signatures for performing secondary signature-based analysis of a held e-mail to improve spam email detection |
| GB2402804B (en) | 2003-06-13 | 2006-10-11 | Macrovision Europ Ltd | Copying copy protected optical discs |
| US7467417B2 (en) | 2003-06-18 | 2008-12-16 | Architecture Technology Corporation | Active verification of boot firmware |
| US7712133B2 (en) | 2003-06-20 | 2010-05-04 | Hewlett-Packard Development Company, L.P. | Integrated intrusion detection system and method |
| US7748030B1 (en) | 2003-06-27 | 2010-06-29 | Realnetworks, Inc. | Licensing digital content use |
| US7568229B1 (en) | 2003-07-01 | 2009-07-28 | Symantec Corporation | Real-time training for a computer code intrusion detection system |
| US7596807B2 (en) | 2003-07-03 | 2009-09-29 | Arbor Networks, Inc. | Method and system for reducing scope of self-propagating attack code in network |
| JP2007527044A (ja) | 2003-07-04 | 2007-09-20 | バイエリッシェ モートーレン ウエルケ アクチエンゲゼルシャフト | 特に自動車の制御装置内にロード可能なソフトウェアコンポーネントを認証するための方法 |
| US7523501B2 (en) | 2003-07-21 | 2009-04-21 | Trend Micro, Inc. | Adaptive computer worm filter and methods of use thereof |
| US7620988B1 (en) | 2003-07-25 | 2009-11-17 | Symantec Corporation | Protocol identification by heuristic content analysis |
| US7463590B2 (en) | 2003-07-25 | 2008-12-09 | Reflex Security, Inc. | System and method for threat detection and response |
| US7356587B2 (en) | 2003-07-29 | 2008-04-08 | International Business Machines Corporation | Automatically detecting malicious computer network reconnaissance by updating state codes in a histogram |
| US7739737B2 (en) | 2003-07-29 | 2010-06-15 | Wisconsin Alumni Research Foundation | Method and apparatus to detect malicious software |
| US7712140B2 (en) | 2003-08-04 | 2010-05-04 | Lsi Corporation | 3-prong security/reliability/real-time distributed architecture of information handling system |
| US7519996B2 (en) | 2003-08-25 | 2009-04-14 | Hewlett-Packard Development Company, L.P. | Security intrusion mitigation system and method |
| JP4174392B2 (ja) | 2003-08-28 | 2008-10-29 | 日本電気株式会社 | ネットワークへの不正接続防止システム、及びネットワークへの不正接続防止装置 |
| US7669239B2 (en) | 2003-09-15 | 2010-02-23 | Jpmorgan Chase Bank, N.A. | Secure network system and associated method of use |
| US7757291B2 (en) | 2003-09-15 | 2010-07-13 | Trigence Corp. | Malware containment by application encapsulation |
| US7594268B1 (en) | 2003-09-19 | 2009-09-22 | Symantec Corporation | Preventing network discovery of a system services configuration |
| US7711948B2 (en) | 2003-09-30 | 2010-05-04 | Cisco Technology, Inc. | Method and apparatus of communicating security/encryption information to a physical layer transceiver |
| US7503071B1 (en) | 2003-10-01 | 2009-03-10 | Symantec Corporation | Network traffic identification by waveform analysis |
| US7536452B1 (en) | 2003-10-08 | 2009-05-19 | Cisco Technology, Inc. | System and method for implementing traffic management based on network resources |
| US7464158B2 (en) | 2003-10-15 | 2008-12-09 | International Business Machines Corporation | Secure initialization of intrusion detection system |
| US7496961B2 (en) | 2003-10-15 | 2009-02-24 | Intel Corporation | Methods and apparatus to provide network traffic support and physical security support |
| US7657938B2 (en) | 2003-10-28 | 2010-02-02 | International Business Machines Corporation | Method and system for protecting computer networks by altering unwanted network data traffic |
| US7444678B2 (en) | 2003-10-28 | 2008-10-28 | Aol Llc | Securing resources from untrusted scripts behind firewalls |
| US7725936B2 (en) | 2003-10-31 | 2010-05-25 | International Business Machines Corporation | Host-based network intrusion detection systems |
| US7526806B2 (en) | 2003-11-05 | 2009-04-28 | Cisco Technology, Inc. | Method and system for addressing intrusion attacks on a computer system |
| JP2005141601A (ja) | 2003-11-10 | 2005-06-02 | Nec Corp | モデル選択計算装置,動的モデル選択装置,動的モデル選択方法およびプログラム |
| CN1545242A (zh) | 2003-11-13 | 2004-11-10 | ����ͨѶ�ɷ�����˾ | 一种基于辫群共轭问题的数字签名方法 |
| US7581249B2 (en) | 2003-11-14 | 2009-08-25 | Enterasys Networks, Inc. | Distributed intrusion response system |
| US7313691B2 (en) | 2003-11-18 | 2007-12-25 | International Business Machines Corporation | Internet site authentication service |
| US7681246B1 (en) | 2003-11-20 | 2010-03-16 | Microsoft Corporation | System and method for server side data signing |
| US7512969B2 (en) | 2003-11-21 | 2009-03-31 | Time Warner Cable, A Division Of Time Warner Entertainment Company, L.P. | System and method for detecting and reporting cable network devices with duplicate media access control addresses |
| US7516331B2 (en) | 2003-11-26 | 2009-04-07 | International Business Machines Corporation | Tamper-resistant trusted java virtual machine and method of using the same |
| US7613179B2 (en) | 2003-11-26 | 2009-11-03 | Nortel Networks Limited | Technique for tracing source addresses of packets |
| US7109861B2 (en) | 2003-11-26 | 2006-09-19 | International Business Machines Corporation | System and method for alarm generation based on the detection of the presence of a person |
| US7526807B2 (en) | 2003-11-26 | 2009-04-28 | Alcatel-Lucent Usa Inc. | Distributed architecture for statistical overload control against distributed denial of service attacks |
| US7533413B2 (en) | 2003-12-05 | 2009-05-12 | Microsoft Corporation | Method and system for processing events |
| US7565696B1 (en) | 2003-12-10 | 2009-07-21 | Arcsight, Inc. | Synchronizing network security devices within a network security system |
| JP4580871B2 (ja) | 2003-12-11 | 2010-11-17 | パナソニック株式会社 | パケット送信装置 |
| US7398399B2 (en) | 2003-12-12 | 2008-07-08 | International Business Machines Corporation | Apparatus, methods and computer programs for controlling performance of operations within a data processing system or network |
| FR2864392A1 (fr) | 2003-12-17 | 2005-06-24 | France Telecom | Procede de classification automatique d'un ensemble d'alertes issues de sondes de detection d'intrusions d'un systeme de securite d'information |
| US7587765B2 (en) | 2003-12-23 | 2009-09-08 | International Business Machines Corporation | Automatic virus fix |
| US7716495B2 (en) | 2003-12-31 | 2010-05-11 | Microsoft Corporation | Protection against runtime function attacks |
| US8031865B2 (en) * | 2004-01-08 | 2011-10-04 | Encryption Solutions, Inc. | Multiple level security system and method for encrypting data within documents |
| JP4608931B2 (ja) | 2004-01-09 | 2011-01-12 | ソニー株式会社 | 情報処理装置および方法、プログラム、並びに記録媒体 |
| US7472416B2 (en) | 2004-01-09 | 2008-12-30 | Cisco Technology, Inc. | Preventing network reset denial of service attacks using embedded authentication information |
| US7610624B1 (en) | 2004-01-12 | 2009-10-27 | Novell, Inc. | System and method for detecting and preventing attacks to a target computer system |
| US7555777B2 (en) | 2004-01-13 | 2009-06-30 | International Business Machines Corporation | Preventing attacks in a data processing system |
| US7487542B2 (en) | 2004-01-14 | 2009-02-03 | International Business Machines Corporation | Intrusion detection using a network processor and a parallel pattern detection engine |
| US7426749B2 (en) | 2004-01-20 | 2008-09-16 | International Business Machines Corporation | Distributed computation in untrusted computing environments using distractive computational units |
| US7624449B1 (en) | 2004-01-22 | 2009-11-24 | Symantec Corporation | Countering polymorphic malicious computer code through code optimization |
| US7707634B2 (en) | 2004-01-30 | 2010-04-27 | Microsoft Corporation | System and method for detecting malware in executable scripts according to its functionality |
| US7526804B2 (en) | 2004-02-02 | 2009-04-28 | Microsoft Corporation | Hardware assist for pattern matches |
| US7594263B2 (en) | 2004-02-05 | 2009-09-22 | International Business Machines Corporation | Operating a communication network through use of blocking measures for responding to communication traffic anomalies |
| US7523494B2 (en) | 2004-02-05 | 2009-04-21 | International Business Machines Corporation | Determining blocking measures for processing communication traffic anomalies |
| US7725937B1 (en) | 2004-02-09 | 2010-05-25 | Symantec Corporation | Capturing a security breach |
| US7440434B2 (en) | 2004-02-11 | 2008-10-21 | Airtight Networks, Inc. | Method and system for detecting wireless access devices operably coupled to computer local area networks and related methods |
| US7339914B2 (en) | 2004-02-11 | 2008-03-04 | Airtight Networks, Inc. | Automated sniffer apparatus and method for monitoring computer systems for unauthorized access |
| US7634655B2 (en) | 2004-02-13 | 2009-12-15 | Microsoft Corporation | Efficient hash table protection for data transport protocols |
| US7603716B2 (en) | 2004-02-13 | 2009-10-13 | Microsoft Corporation | Distributed network security service |
| JP3954583B2 (ja) | 2004-02-16 | 2007-08-08 | メモリーテック株式会社 | 光ディスク、光ディスク製造装置及び光ディスク製造方法 |
| US7437759B1 (en) | 2004-02-17 | 2008-10-14 | Symantec Corporation | Kernel mode overflow attack prevention system and method |
| US7620989B1 (en) | 2004-02-19 | 2009-11-17 | Spirent Communications Inc. | Network testing methods and systems |
| JP4909498B2 (ja) | 2004-02-27 | 2012-04-04 | 日本電気株式会社 | インターリーブパラメータ演算方法/プログラム/プログラム記録媒体/装置、携帯電話機 |
| US7712077B2 (en) | 2004-02-27 | 2010-05-04 | International Business Machines Corporation | Method and system for instantiating components conforming to the “COM” specification in custom contexts |
| US7702968B2 (en) | 2004-02-27 | 2010-04-20 | Qualcomm Incorporated | Efficient multi-symbol deinterleaver |
| US7761923B2 (en) | 2004-03-01 | 2010-07-20 | Invensys Systems, Inc. | Process control methods and apparatus for intrusion detection, protection and network hardening |
| KR100601667B1 (ko) | 2004-03-02 | 2006-07-14 | 삼성전자주식회사 | 디지털 권한 관리의 상태 보고 장치 및 방법 |
| US7379546B2 (en) | 2004-03-03 | 2008-05-27 | King Fahd University Of Petroleum And Minerals | Method for XZ-elliptic curve cryptography |
| US7444677B2 (en) | 2004-03-05 | 2008-10-28 | Microsoft Corporation | Intentional cascade failure |
| US7739516B2 (en) | 2004-03-05 | 2010-06-15 | Microsoft Corporation | Import address table verification |
| US7694335B1 (en) | 2004-03-09 | 2010-04-06 | Cisco Technology, Inc. | Server preventing attacks by generating a challenge having a computational request and a secure cookie for processing by a client |
| US7487149B2 (en) | 2004-03-10 | 2009-02-03 | Oracle International Corporation | Method and apparatus for providing query-level security in a database system |
| US7698730B2 (en) | 2004-03-16 | 2010-04-13 | Riverbed Technology, Inc. | Service detection |
| US7685327B1 (en) | 2004-03-19 | 2010-03-23 | Xilinx, Inc. | Identification of multi-device systems |
| US7669059B2 (en) | 2004-03-23 | 2010-02-23 | Network Equipment Technologies, Inc. | Method and apparatus for detection of hostile software |
| US7523499B2 (en) | 2004-03-25 | 2009-04-21 | Microsoft Corporation | Security attack detection and defense |
| JP4144880B2 (ja) | 2004-04-09 | 2008-09-03 | インターナショナル・ビジネス・マシーンズ・コーポレーション | プラットフォーム構成測定装置、プログラム及び方法、プラットフォーム構成認証装置、プログラム及び方法、プラットフォーム構成証明装置、プログラム及び方法、並びに、プラットフォーム構成開示装置、プログラム及び方法 |
| US7716473B1 (en) | 2004-04-09 | 2010-05-11 | Cisco Technology, Inc. | Methods and apparatus providing a reference monitor simulator |
| US7600255B1 (en) | 2004-04-14 | 2009-10-06 | Cisco Technology, Inc. | Preventing network denial of service attacks using an accumulated proof-of-work approach |
| US7673049B2 (en) | 2004-04-19 | 2010-03-02 | Brian Dinello | Network security system |
| US7533415B2 (en) | 2004-04-21 | 2009-05-12 | Trend Micro Incorporated | Method and apparatus for controlling traffic in a computer network |
| JPWO2005103909A1 (ja) | 2004-04-26 | 2008-03-13 | セイコーエプソン株式会社 | セキュリティ保全方法およびデータ蓄積装置、セキュリティ保全サーバ、及びそのプログラムを記録した記録媒体 |
| US7484091B2 (en) | 2004-04-29 | 2009-01-27 | International Business Machines Corporation | Method and system for providing a trusted platform module in a hypervisor environment |
| EP1745660B1 (en) | 2004-04-30 | 2012-01-11 | Research In Motion Limited | System and method for handling restoration operations on mobile devices |
| US7596808B1 (en) | 2004-04-30 | 2009-09-29 | Tw Acquisition, Inc. | Zero hop algorithm for network threat identification and mitigation |
| US7529187B1 (en) | 2004-05-04 | 2009-05-05 | Symantec Corporation | Detecting network evasion and misinformation |
| US7509677B2 (en) | 2004-05-04 | 2009-03-24 | Arcsight, Inc. | Pattern discovery in a network security system |
| US7664855B1 (en) | 2004-05-05 | 2010-02-16 | Juniper Networks, Inc. | Port scanning mitigation within a network through establishment of an a prior network connection |
| US7681237B1 (en) | 2004-05-13 | 2010-03-16 | Symantec Corporation | Semi-synchronous scanning of modified files in real time |
| DE102004026800B4 (de) | 2004-05-24 | 2006-05-24 | Infineon Technologies Ag | Verfahren zum Verändern einer Tiefe einer Interleaver-Vorrichtung oder Deinterleaver-Vorrichtung sowie entsprechende Interleaver-Vorrichtung, Deinterleaver-Vorrichtung und Kommunikationseinrichtung |
| JP4371905B2 (ja) | 2004-05-27 | 2009-11-25 | 富士通株式会社 | 不正アクセス検知装置、不正アクセス検知方法、不正アクセス検知プログラムおよび分散型サービス不能化攻撃検知装置 |
| US7757086B2 (en) | 2004-05-27 | 2010-07-13 | Silverbrook Research Pty Ltd | Key transportation |
| US7698552B2 (en) | 2004-06-03 | 2010-04-13 | Intel Corporation | Launching a secure kernel in a multiprocessor system |
| US7730482B2 (en) | 2004-06-08 | 2010-06-01 | Covia Labs, Inc. | Method and system for customized programmatic dynamic creation of interoperability content |
| US7523500B1 (en) | 2004-06-08 | 2009-04-21 | Symantec Corporation | Filtered antivirus scanning |
| US7568230B2 (en) | 2004-06-09 | 2009-07-28 | Lieberman Software Corporation | System for selective disablement and locking out of computer system objects |
| US7441272B2 (en) | 2004-06-09 | 2008-10-21 | Intel Corporation | Techniques for self-isolation of networked devices |
| US7490354B2 (en) | 2004-06-10 | 2009-02-10 | International Business Machines Corporation | Virus detection in a network |
| US7631360B2 (en) | 2004-06-12 | 2009-12-08 | Microsoft Corporation | Hardware protection |
| US7624445B2 (en) | 2004-06-15 | 2009-11-24 | International Business Machines Corporation | System for dynamic network reconfiguration and quarantine in response to threat conditions |
| US7694340B2 (en) | 2004-06-21 | 2010-04-06 | Microsoft Corporation | Anti virus for an item store |
| US7669050B2 (en) | 2004-06-24 | 2010-02-23 | International Business Machines Corporation | Method to enable user mode process to operate in a privileged execution mode |
| CN1998176B (zh) | 2004-07-01 | 2011-06-15 | 高通股份有限公司 | 高级mimo交织方法和系统 |
| JP4700301B2 (ja) | 2004-07-15 | 2011-06-15 | オークマ株式会社 | リアルタイムシステムのためのソフトウェアオブジェクト検証方法 |
| US7716494B2 (en) | 2004-07-15 | 2010-05-11 | Sony Corporation | Establishing a trusted platform in a digital processing system |
| US7490356B2 (en) | 2004-07-20 | 2009-02-10 | Reflectent Software, Inc. | End user risk management |
| US7325183B2 (en) | 2004-07-21 | 2008-01-29 | Hewlett-Packard Development Company, L.P. | Error correction code generation method and apparatus |
| US7627898B2 (en) | 2004-07-23 | 2009-12-01 | Microsoft Corporation | Method and system for detecting infection of an operating system |
| US7519998B2 (en) | 2004-07-28 | 2009-04-14 | Los Alamos National Security, Llc | Detection of malicious computer executables |
| US20060101047A1 (en) | 2004-07-29 | 2006-05-11 | Rice John R | Method and system for fortifying software |
| US7496962B2 (en) | 2004-07-29 | 2009-02-24 | Sourcefire, Inc. | Intrusion detection strategies for hypertext transport protocol |
| US7509676B2 (en) | 2004-07-30 | 2009-03-24 | Electronic Data Systems Corporation | System and method for restricting access to an enterprise network |
| US7523504B2 (en) | 2004-08-02 | 2009-04-21 | Netiq Corporation | Methods, systems and computer program products for evaluating security of a network environment |
| US7590813B1 (en) | 2004-08-09 | 2009-09-15 | Symantec Corporation | Cache scanning system and method |
| JP4643204B2 (ja) | 2004-08-25 | 2011-03-02 | 株式会社エヌ・ティ・ティ・ドコモ | サーバ装置 |
| US7500265B2 (en) | 2004-08-27 | 2009-03-03 | International Business Machines Corporation | Apparatus and method to identify SPAM emails |
| US7703137B2 (en) | 2004-09-03 | 2010-04-20 | Fortinet, Inc. | Centralized data transformation |
| US7487546B1 (en) | 2004-09-03 | 2009-02-03 | Symantec Corporation | Hosts file protection system and method |
| US7690034B1 (en) | 2004-09-10 | 2010-03-30 | Symantec Corporation | Using behavior blocking mobility tokens to facilitate distributed worm detection |
| US7590880B1 (en) | 2004-09-13 | 2009-09-15 | National Semiconductor Corporation | Circuitry and method for detecting and protecting against over-clocking attacks |
| US7490244B1 (en) | 2004-09-14 | 2009-02-10 | Symantec Corporation | Blocking e-mail propagation of suspected malicious computer code |
| US7685640B2 (en) | 2004-09-21 | 2010-03-23 | Agere Systems Inc. | Methods and apparatus for interface adapter integrated virus protection |
| US7451486B2 (en) | 2004-09-30 | 2008-11-11 | Avaya Inc. | Stateful and cross-protocol intrusion detection for voice over IP |
| US7685632B2 (en) | 2004-10-01 | 2010-03-23 | Microsoft Corporation | Access authorization having a centralized policy |
| US7478429B2 (en) | 2004-10-01 | 2009-01-13 | Prolexic Technologies, Inc. | Network overload detection and mitigation system and method |
| JP2006108961A (ja) | 2004-10-04 | 2006-04-20 | Sony Corp | 情報処理装置および方法、プログラム並びに記録媒体 |
| US7752671B2 (en) | 2004-10-04 | 2010-07-06 | Promisec Ltd. | Method and device for questioning a plurality of computerized devices |
| US7594272B1 (en) | 2004-10-05 | 2009-09-22 | Symantec Corporation | Detecting malicious software through file group behavior |
| US7600257B2 (en) | 2004-10-13 | 2009-10-06 | Sonicwall, Inc. | Method and an apparatus to perform multiple packet payloads analysis |
| US7571319B2 (en) | 2004-10-14 | 2009-08-04 | Microsoft Corporation | Validating inbound messages |
| CN100407089C (zh) | 2004-10-15 | 2008-07-30 | 国际商业机器公司 | 检测非法访问计算机网络的系统和方法 |
| US7650640B1 (en) | 2004-10-18 | 2010-01-19 | Symantec Corporation | Method and system for detecting IA32 targeted buffer overflow attacks |
| US7555778B2 (en) | 2004-10-19 | 2009-06-30 | George Mason Intellectual Properties, Inc. | Minimum-cost network hardening |
| KR100611741B1 (ko) | 2004-10-19 | 2006-08-11 | 한국전자통신연구원 | 네트워크 침입 탐지 및 방지 시스템 및 그 방법 |
| US7516480B2 (en) | 2004-10-22 | 2009-04-07 | Microsoft Corporation | Secure remote configuration of targeted devices using a standard message transport protocol |
| US7644438B1 (en) | 2004-10-27 | 2010-01-05 | Arcsight, Inc. | Security event aggregation at software agent |
| US7657940B2 (en) | 2004-10-28 | 2010-02-02 | Cisco Technology, Inc. | System for SSL re-encryption after load balance |
| KR100777752B1 (ko) | 2004-10-28 | 2007-11-19 | 니폰덴신뎅와 가부시키가이샤 | 서비스 불능 공격 검지 시스템 및 서비스 불능 공격 검지방법 |
| JP4501156B2 (ja) | 2004-10-28 | 2010-07-14 | 日本電気株式会社 | 機密モードに応じたアクセスフォルダ切り替え方法、プログラム、及びコンピュータシステム |
| US7594269B2 (en) | 2004-10-29 | 2009-09-22 | Intel Corporation | Platform-based identification of host software circumvention |
| US7565686B1 (en) | 2004-11-08 | 2009-07-21 | Symantec Corporation | Preventing unauthorized loading of late binding code into a process |
| US7546639B2 (en) | 2004-11-19 | 2009-06-09 | International Business Machines Corporation | Protection of information in computing devices |
| US7493654B2 (en) | 2004-11-20 | 2009-02-17 | International Business Machines Corporation | Virtualized protective communications system |
| US7546637B1 (en) | 2004-11-22 | 2009-06-09 | Symantec Corproation | Structures and methods for using geo-location in security detectors |
| US7784097B1 (en) | 2004-11-24 | 2010-08-24 | The Trustees Of Columbia University In The City Of New York | Systems and methods for correlating and distributing intrusion alert information among collaborating computer systems |
| DE102004057490B4 (de) | 2004-11-29 | 2007-02-22 | Infineon Technologies Ag | Vorrichtung und Verfahren zum Verarbeiten eines Programmcodes |
| US7716563B2 (en) | 2004-11-30 | 2010-05-11 | Ciena Corporation | Method and apparatus for the efficient implementation of a totally general convolutional interleaver in DMT-based xDSL systems |
| EP1667329A1 (en) | 2004-12-01 | 2006-06-07 | Istituto Superiore Mario Boella per le Technologie dell Informazione e delle Telecommunicazioni | Methods for the generation of S-random interleavers for turbo-decoders with a parallel structure |
| US7747017B2 (en) | 2004-12-01 | 2010-06-29 | Motorola, Inc. | Method and apparatus for end-to-end clear transport protocol |
| US7636856B2 (en) | 2004-12-06 | 2009-12-22 | Microsoft Corporation | Proactive computer malware protection through dynamic translation |
| US7549162B2 (en) | 2004-12-06 | 2009-06-16 | At&T Intellectual Property I, L.P. | Methods of providing security for data distributions in a data network and related devices, networks, and computer program products |
| KR100622670B1 (ko) | 2004-12-07 | 2006-09-19 | 한국전자통신연구원 | 알려지지 않은 네트워크 공격에 대한 실시간 공격 패턴 검출 시스템 및 그 방법 |
| US7673341B2 (en) | 2004-12-15 | 2010-03-02 | Microsoft Corporation | System and method of efficiently identifying and removing active malware from a computer |
| US7600164B2 (en) | 2004-12-17 | 2009-10-06 | Telefonaktiebolaget Lm Ericsson (Publ) | Interleaving/de-interleaving using compressed bit-mapping sequences |
| KR100628325B1 (ko) | 2004-12-20 | 2006-09-27 | 한국전자통신연구원 | 무선 네트워크에 대한 공격을 탐지하기 위한 침입 탐지센서 및 무선 네트워크 침입 탐지 시스템 및 방법 |
| US7607170B2 (en) | 2004-12-22 | 2009-10-20 | Radware Ltd. | Stateful attack protection |
| TWI252976B (en) | 2004-12-27 | 2006-04-11 | Ind Tech Res Inst | Detecting method and architecture thereof for malicious codes |
| US7752667B2 (en) | 2004-12-28 | 2010-07-06 | Lenovo (Singapore) Pte Ltd. | Rapid virus scan using file signature created during file write |
| US7551615B2 (en) | 2004-12-29 | 2009-06-23 | Intel Corporation | Method for packet encapsulation and redirection of data packets |
| US7703138B2 (en) | 2004-12-29 | 2010-04-20 | Intel Corporation | Use of application signature to identify trusted traffic |
| WO2006071985A2 (en) | 2004-12-29 | 2006-07-06 | Alert Logic, Inc. | Threat scoring system and method for intrusion detection security networks |
| US7716741B2 (en) | 2005-01-12 | 2010-05-11 | International Business Machines Corporation | Method and system for offloading real-time virus scanning during data transfer to storage peripherals |
| US7735138B2 (en) | 2005-01-14 | 2010-06-08 | Trend Micro Incorporated | Method and apparatus for performing antivirus tasks in a mobile wireless device |
| US7546471B2 (en) | 2005-01-14 | 2009-06-09 | Microsoft Corporation | Method and system for virus detection using pattern matching techniques |
| US7647430B2 (en) | 2005-01-19 | 2010-01-12 | Microsoft Corporation | Remote command framework for devices |
| US7685418B1 (en) | 2005-01-19 | 2010-03-23 | Altera Corporation | Mechanisms and techniques for protecting intellectual property |
| US7725938B2 (en) | 2005-01-20 | 2010-05-25 | Cisco Technology, Inc. | Inline intrusion detection |
| US7587645B2 (en) | 2005-01-24 | 2009-09-08 | Samsung Electronics Co., Ltd. | Input circuit of semiconductor memory device and test system having the same |
| US7624446B1 (en) | 2005-01-25 | 2009-11-24 | Symantec Corporation | Efficient signature packing for an intrusion detection system |
| US7665134B1 (en) | 2005-01-26 | 2010-02-16 | Symantec Corporation | Profiling users based on artificially constructed deceptive content |
| US7617533B1 (en) | 2005-01-31 | 2009-11-10 | Symantec Corporation | Self-quarantining network |
| US7676217B2 (en) | 2005-01-31 | 2010-03-09 | Theta Networks, Inc. | Method for malicious traffic recognition in IP networks with subscriber identification and notification |
| US7676841B2 (en) | 2005-02-01 | 2010-03-09 | Fmr Llc | Network intrusion mitigation |
| US7526707B2 (en) | 2005-02-01 | 2009-04-28 | Agere Systems Inc. | Method and apparatus for encoding and decoding data using a pseudo-random interleaver |
| US7739742B2 (en) | 2005-02-01 | 2010-06-15 | Lionel Poizner | Theft protection method and promotion system for audio media |
| JP2006221242A (ja) | 2005-02-08 | 2006-08-24 | Fujitsu Ltd | 認証情報詐取防止システム、プログラム及び方法 |
| US7552377B1 (en) | 2005-02-10 | 2009-06-23 | Xilinx, Inc. | Method of and circuit for interleaving data in a data coder |
| US7581250B2 (en) | 2005-02-17 | 2009-08-25 | Lenovo (Singapore) Pte Ltd | System, computer program product and method of selecting sectors of a hard disk on which to perform a virus scan |
| CN101120351B (zh) | 2005-02-18 | 2010-10-06 | Rsa安全公司 | 派生种子的分发方法 |
| US7516488B1 (en) | 2005-02-23 | 2009-04-07 | Symantec Corporation | Preventing data from being submitted to a remote system in response to a malicious e-mail |
| US7587764B2 (en) | 2005-02-28 | 2009-09-08 | Chadwick James Cox | Cryptic information and behavior generation for competitive environments |
| US7735141B1 (en) | 2005-03-10 | 2010-06-08 | Noel Steven E | Intrusion event correlator |
| US7657939B2 (en) | 2005-03-14 | 2010-02-02 | International Business Machines Corporation | Computer security intrusion detection system for remote, on-demand users |
| US7685149B2 (en) | 2005-03-28 | 2010-03-23 | Microsoft Corporation | Identifying and removing potentially unwanted software |
| US7725735B2 (en) | 2005-03-29 | 2010-05-25 | International Business Machines Corporation | Source code management method for malicious code detection |
| DE602005024514D1 (de) | 2005-03-31 | 2010-12-16 | Texas Instruments Inc | Verfahren und System zum Vereiteln und Neutralisieren von Pufferüberläufangriffen |
| US7650639B2 (en) | 2005-03-31 | 2010-01-19 | Microsoft Corporation | System and method for protecting a limited resource computer from malware |
| US7624373B2 (en) | 2005-03-31 | 2009-11-24 | Microsoft Corporation | Security mechanism for interpreting scripts in an interpretive environment |
| US7707629B2 (en) | 2005-03-31 | 2010-04-27 | Intel Corporation | Platform configuration register virtualization apparatus, systems, and methods |
| US7568233B1 (en) | 2005-04-01 | 2009-07-28 | Symantec Corporation | Detecting malicious software through process dump scanning |
| US7490352B2 (en) | 2005-04-07 | 2009-02-10 | Microsoft Corporation | Systems and methods for verifying trust of executable files |
| US7565695B2 (en) | 2005-04-12 | 2009-07-21 | Webroot Software, Inc. | System and method for directly accessing data from a data storage medium |
| US7636940B2 (en) | 2005-04-12 | 2009-12-22 | Seiko Epson Corporation | Private key protection for secure servers |
| US7668097B2 (en) | 2005-04-12 | 2010-02-23 | Motorola, Inc. | Method of dormant data session reactivation |
| US7591016B2 (en) | 2005-04-14 | 2009-09-15 | Webroot Software, Inc. | System and method for scanning memory for pestware offset signatures |
| US7730531B2 (en) | 2005-04-15 | 2010-06-01 | Microsoft Corporation | System and method for detection of artificially generated system load |
| US7562391B1 (en) | 2005-04-18 | 2009-07-14 | Symantec Corporation | Reducing false positive indications of buffer overflow attacks |
| US7509250B2 (en) | 2005-04-20 | 2009-03-24 | Honeywell International Inc. | Hardware key control of debug interface |
| US7574741B2 (en) | 2005-04-20 | 2009-08-11 | Cisco Technology, Inc. | Method and system for preventing operating system detection |
| US7748035B2 (en) | 2005-04-22 | 2010-06-29 | Cisco Technology, Inc. | Approach for securely deploying network devices |
| US7640591B1 (en) | 2005-04-22 | 2009-12-29 | Sun Microsystems, Inc. | Method and apparatus for limiting denial of service attack by limiting traffic for hosts |
| US7376823B2 (en) | 2005-04-28 | 2008-05-20 | International Business Machines Corporation | Method and system for automatic detection, inventory, and operating system deployment on network boot capable computers |
| US7748046B2 (en) | 2005-04-29 | 2010-06-29 | Microsoft Corporation | Security claim transformation with intermediate claims |
| US7748047B2 (en) | 2005-04-29 | 2010-06-29 | Verizon Business Global Llc | Preventing fraudulent internet account access |
| US7721094B2 (en) | 2005-05-06 | 2010-05-18 | Microsoft Corporation | Systems and methods for determining if applications executing on a computer system are trusted |
| US7577881B1 (en) | 2005-05-10 | 2009-08-18 | Ikanos Communications Inc. | Method and apparatus for an interleaver |
| US7599289B2 (en) | 2005-05-13 | 2009-10-06 | Lockheed Martin Corporation | Electronic communication control |
| US7730522B2 (en) | 2005-05-16 | 2010-06-01 | Microsoft Corporation | Self-registering objects for an IPC mechanism |
| US7558796B1 (en) | 2005-05-19 | 2009-07-07 | Symantec Corporation | Determining origins of queries for a database intrusion detection system |
| US7721331B1 (en) | 2005-05-19 | 2010-05-18 | Adobe Systems Inc. | Methods and apparatus for performing a pre-processing activity |
| US7757288B1 (en) | 2005-05-23 | 2010-07-13 | Symantec Corporation | Malicious e-mail attack inversion filter |
| US7454790B2 (en) | 2005-05-23 | 2008-11-18 | Ut-Battelle, Llc | Method for detecting sophisticated cyber attacks |
| US7694338B1 (en) | 2005-06-03 | 2010-04-06 | Sprint Communications Company L.P. | Shared tap DOS-attack protection |
| CN101496343B (zh) | 2005-06-03 | 2012-06-27 | 华纳兄弟娱乐公司 | 用于确保将所有的视听光盘类型的水印合理扫描的系统 |
| US7665135B1 (en) | 2005-06-03 | 2010-02-16 | Sprint Communications Company L.P. | Detecting and addressing network attacks |
| US7730536B2 (en) | 2005-06-08 | 2010-06-01 | Verizon Business Global Llc | Security perimeters |
| US7600259B2 (en) | 2005-06-08 | 2009-10-06 | Symantec Corporation | Critical period protection |
| US7587761B2 (en) | 2005-06-10 | 2009-09-08 | At&T Corp. | Adaptive defense against various network attacks |
| US7636943B2 (en) | 2005-06-13 | 2009-12-22 | Aladdin Knowledge Systems Ltd. | Method and system for detecting blocking and removing spyware |
| CA2510366C (en) | 2005-06-14 | 2013-02-26 | Certicom Corp. | System and method for remote device registration |
| US7734933B1 (en) | 2005-06-17 | 2010-06-08 | Rockwell Collins, Inc. | System for providing secure and trusted computing environments through a secure computing module |
| US7571482B2 (en) | 2005-06-28 | 2009-08-04 | Microsoft Corporation | Automated rootkit detector |
| US7747597B2 (en) | 2005-06-29 | 2010-06-29 | Microsoft Corporation | Security execution context for a database management system |
| US7603461B2 (en) | 2005-06-29 | 2009-10-13 | Intel Corporation | Methods, apparatus, and systems for distributed hypothesis testing in autonomic processing machines |
| US7702906B1 (en) | 2005-06-30 | 2010-04-20 | Symantec Operating Corporation | Securing kernel metadata communication in environments employing distributed software services |
| JP2007018401A (ja) | 2005-07-11 | 2007-01-25 | Hitachi Ltd | 記憶制御装置、記憶制御装置の上位インターフェース制御部及び記憶制御装置の情報保護方法 |
| US7690037B1 (en) | 2005-07-13 | 2010-03-30 | Symantec Corporation | Filtering training data for machine learning |
| US7587724B2 (en) | 2005-07-13 | 2009-09-08 | Symantec Corporation | Kernel validation layer |
| US7716739B1 (en) | 2005-07-20 | 2010-05-11 | Symantec Corporation | Subjective and statistical event tracking incident management system |
| CN1904862A (zh) | 2005-07-27 | 2007-01-31 | 鸿富锦精密工业(深圳)有限公司 | 基本输入/输出系统的密码保护系统及方法 |
| JP5124455B2 (ja) | 2005-07-28 | 2013-01-23 | エムフォメーション・テクノロジーズ・インコーポレイテッド | 装置の機能性を遠隔的に制御するためのシステムおよび方法 |
| US7486666B2 (en) | 2005-07-28 | 2009-02-03 | Symbol Technologies, Inc. | Rogue AP roaming prevention |
| US7584507B1 (en) | 2005-07-29 | 2009-09-01 | Narus, Inc. | Architecture, systems and methods to detect efficiently DoS and DDoS attacks for large scale internet |
| US7711953B2 (en) | 2005-08-10 | 2010-05-04 | Hewlett-Packard Development Company, L.P. | Methods and systems that selectively permit changes to a cryptographic hardware unit's state |
| EP2568613A1 (en) * | 2005-08-12 | 2013-03-13 | Fujitsu Limited | Transmission device, encoding device and decoding device |
| US7725946B2 (en) | 2005-08-18 | 2010-05-25 | Fujitsu Limited | Program, system and method for authenticating permission to use a computer system and inhibiting access to an unauthorized user |
| US7647637B2 (en) | 2005-08-19 | 2010-01-12 | Sun Microsystems, Inc. | Computer security technique employing patch with detection and/or characterization mechanism for exploit of patched vulnerability |
| US7647636B2 (en) | 2005-08-24 | 2010-01-12 | Microsoft Corporation | Generic RootKit detector |
| US7617534B1 (en) | 2005-08-26 | 2009-11-10 | Symantec Corporation | Detection of SYSENTER/SYSCALL hijacking |
| US7480847B2 (en) | 2005-08-29 | 2009-01-20 | Sun Microsystems, Inc. | Error correction code transformation technique |
| US7661138B1 (en) | 2005-08-31 | 2010-02-09 | Jupiter Networks, Inc. | Finite state automaton compression |
| US7624447B1 (en) | 2005-09-08 | 2009-11-24 | Cisco Technology, Inc. | Using threshold lists for worm detection |
| JP4089719B2 (ja) | 2005-09-09 | 2008-05-28 | 沖電気工業株式会社 | 異常検出システム,異常管理装置,異常管理方法,プローブおよびそのプログラム |
| US7690045B2 (en) | 2005-09-15 | 2010-03-30 | Microsoft Corporation | On-the-fly contents-based access control system |
| US7739740B1 (en) | 2005-09-22 | 2010-06-15 | Symantec Corporation | Detecting polymorphic threats |
| US7748037B2 (en) | 2005-09-22 | 2010-06-29 | Intel Corporation | Validating a memory type modification attempt |
| US7739746B2 (en) | 2005-10-04 | 2010-06-15 | Adobe Systems Incorporated | Document control |
| US7716740B2 (en) | 2005-10-05 | 2010-05-11 | Alcatel Lucent | Rogue access point detection in wireless networks |
| US7712132B1 (en) | 2005-10-06 | 2010-05-04 | Ogilvie John W | Detecting surreptitious spyware |
| US7707635B1 (en) | 2005-10-06 | 2010-04-27 | Trend Micro Incorporated | Script-based pattern for detecting computer viruses |
| US7748034B2 (en) | 2005-10-12 | 2010-06-29 | Cisco Technology, Inc. | Strong anti-replay protection for IP traffic sent point to point or multi-cast to large groups |
| US7647623B2 (en) | 2005-10-17 | 2010-01-12 | Alcatel Lucent | Application layer ingress filtering |
| US7739100B1 (en) | 2005-10-18 | 2010-06-15 | Mcafee, Inc. | Emulation system, method and computer program product for malware detection by back-stepping in program code |
| US7636944B2 (en) | 2005-10-28 | 2009-12-22 | Hewlett-Packard Development Company, L.P. | Method and apparatus for detecting and responding to email based propagation of malicious software in a trusted network |
| US7607173B1 (en) | 2005-10-31 | 2009-10-20 | Symantec Corporation | Method and apparatus for preventing rootkit installation |
| US7743418B2 (en) | 2005-10-31 | 2010-06-22 | Microsoft Corporation | Identifying malware that employs stealth techniques |
| US7630406B2 (en) | 2005-11-04 | 2009-12-08 | Intel Corporation | Methods and apparatus for providing a delayed attack protection system for network traffic |
| US7644271B1 (en) | 2005-11-07 | 2010-01-05 | Cisco Technology, Inc. | Enforcement of security policies for kernel module loading |
| US7665136B1 (en) | 2005-11-09 | 2010-02-16 | Symantec Corporation | Method and apparatus for detecting hidden network communication channels of rootkit tools |
| US7853018B2 (en) | 2005-11-10 | 2010-12-14 | Atallah Mikhail J | Method and apparatus for hiding a private key |
| KR100833488B1 (ko) | 2005-11-25 | 2008-05-29 | 한국전자통신연구원 | 침해 규칙 저장 방법 및 장치 |
| US7389426B2 (en) | 2005-11-29 | 2008-06-17 | Research In Motion Limited | Mobile software terminal identifier |
| US7665123B1 (en) | 2005-12-01 | 2010-02-16 | Symantec Corporation | Method and apparatus for detecting hidden rootkits |
| US7698741B2 (en) | 2005-12-06 | 2010-04-13 | Microsoft Corporation | Controlling the isolation of an object |
| US7657754B2 (en) | 2005-12-08 | 2010-02-02 | Agere Systems Inc | Methods and apparatus for the secure handling of data in a microcontroller |
| KR100734864B1 (ko) | 2005-12-09 | 2007-07-03 | 한국전자통신연구원 | 패턴 매칭 정책 저장 방법 및 경보 제어 방법 |
| US7757289B2 (en) | 2005-12-12 | 2010-07-13 | Finjan, Inc. | System and method for inspecting dynamically generated executable code |
| US7685638B1 (en) | 2005-12-13 | 2010-03-23 | Symantec Corporation | Dynamic replacement of system call tables |
| US7703133B1 (en) | 2005-12-16 | 2010-04-20 | Sprint Communications Company L.P. | Secure authentication curtain system and method |
| US7665139B1 (en) | 2005-12-16 | 2010-02-16 | Symantec Corporation | Method and apparatus to detect and prevent malicious changes to tokens |
| US7752664B1 (en) | 2005-12-19 | 2010-07-06 | Symantec Corporation | Using domain name service resolution queries to combat spyware |
| US7734934B2 (en) | 2005-12-20 | 2010-06-08 | Intel Corporation | Seamless data migration |
| US7663479B1 (en) | 2005-12-21 | 2010-02-16 | At&T Corp. | Security infrastructure |
| US7590113B1 (en) | 2005-12-29 | 2009-09-15 | At&T Corp. | Method and apparatus for generating a reconnaissance index |
| US7712134B1 (en) | 2006-01-06 | 2010-05-04 | Narus, Inc. | Method and apparatus for worm detection and containment in the internet core |
| US7555684B1 (en) | 2006-01-17 | 2009-06-30 | Xilinx, Inc. | Circuit for and a method of generating an interleaver address |
| US7721333B2 (en) | 2006-01-18 | 2010-05-18 | Webroot Software, Inc. | Method and system for detecting a keylogger on a computer |
| US7743153B2 (en) | 2006-01-18 | 2010-06-22 | International Business Machines Corporation | Killing login-based sessions with a single action |
| US7450005B2 (en) | 2006-01-18 | 2008-11-11 | International Business Machines Corporation | System and method of dynamically weighted analysis for intrusion decision-making |
| US7757290B2 (en) | 2006-01-30 | 2010-07-13 | Microsoft Corporation | Bypassing software services to detect malware |
| US7606225B2 (en) | 2006-02-06 | 2009-10-20 | Fortinet, Inc. | Integrated security switch |
| US7590834B2 (en) | 2006-02-10 | 2009-09-15 | Lenovo Singapore Pte. Ltd. | Method and apparatus for tracking boot history |
| US7870399B2 (en) | 2006-02-10 | 2011-01-11 | Arxan Defense Systems | Software trusted platform module and application security wrapper |
| US7617435B2 (en) * | 2006-02-23 | 2009-11-10 | Yuwei Zhang | Hard-decision iteration decoding based on an error-correcting code with a low undetectable error probability |
| US7610519B1 (en) | 2006-03-03 | 2009-10-27 | Xilinx, Inc. | Vector generation for codes through symmetry |
| US7624448B2 (en) | 2006-03-04 | 2009-11-24 | 21St Century Technologies, Inc. | Intelligent intrusion detection system utilizing enhanced graph-matching of network activity with context data |
| US7721090B1 (en) | 2006-03-07 | 2010-05-18 | Xilinx, Inc. | Event-driven simulation of IP using third party event-driven simulators |
| US7739738B1 (en) | 2006-03-15 | 2010-06-15 | Symantec Corporation | Enabling clean file cache persistence using dual-boot detection |
| US7681092B2 (en) | 2006-04-11 | 2010-03-16 | Sharp Laboratories Of America, Inc. | Systems and methods for interleaving and deinterleaving data in an OFDMA-based communication system |
| US7739211B2 (en) | 2006-11-08 | 2010-06-15 | 21St Century Technologies, Inc. | Dynamic SNA-based anomaly detection using unsupervised learning |
| US7676673B2 (en) | 2006-04-28 | 2010-03-09 | Bae Systems Information And Electronic Systems Integration Inc. | Multi-level secure (MLS) information network |
| US7730538B2 (en) | 2006-06-02 | 2010-06-01 | Microsoft Corporation | Combining virus checking and replication filtration |
| US7757098B2 (en) | 2006-06-27 | 2010-07-13 | Intel Corporation | Method and apparatus for verifying authenticity of initial boot code |
| US7743239B2 (en) | 2006-06-30 | 2010-06-22 | Intel Corporation | Accelerating integrity checks of code and data stored in non-volatile memory |
| US7701945B2 (en) | 2006-08-10 | 2010-04-20 | Sourcefire, Inc. | Device, system and method for analysis of segments in a transmission control protocol (TCP) session |
| US7523502B1 (en) | 2006-09-21 | 2009-04-21 | Symantec Corporation | Distributed anti-malware |
| JP4408881B2 (ja) | 2006-09-27 | 2010-02-03 | Necエレクトロニクス株式会社 | 半導体集積回路 |
| US7743287B2 (en) | 2006-10-18 | 2010-06-22 | Trellisware Technologies, Inc. | Using SAM in error correcting code encoder and decoder implementations |
| US7647635B2 (en) | 2006-11-02 | 2010-01-12 | A10 Networks, Inc. | System and method to resolve an identity interactively |
| US7647308B2 (en) | 2006-11-08 | 2010-01-12 | Mcafee, Inc. | Method and system for the detection of file system filter driver based rootkits |
| US7551073B2 (en) | 2007-01-10 | 2009-06-23 | International Business Machines Corporation | Method, system and program product for alerting an information technology support organization of a security event |
| US7747688B2 (en) | 2007-02-07 | 2010-06-29 | International Business Machines Corporation | System and method for managing group interaction session states |
| US7747024B2 (en) | 2007-02-09 | 2010-06-29 | Lenovo (Singapore) Pte. Ltd. | System and method for generalized authentication |
| US7743424B2 (en) | 2007-02-22 | 2010-06-22 | Inventec Corporation | Method for protecting data in a hard disk |
| US7386885B1 (en) | 2007-07-03 | 2008-06-10 | Kaspersky Lab, Zao | Constraint-based and attribute-based security system for controlling software component interaction |
| US7742409B2 (en) | 2007-08-15 | 2010-06-22 | At&T Intellectual Property Ii, L.P. | Method and apparatus for compensating for performance degradation of an application session |
| US7614084B2 (en) | 2007-10-02 | 2009-11-03 | Kaspersky Lab Zao | System and method for detecting multi-component malware |
| US8120960B2 (en) * | 2007-11-07 | 2012-02-21 | Spansion Israel Ltd. | Method and apparatus for accessing a non-volatile memory array comprising unidirectional current flowing multiplexers |
| US7945825B2 (en) * | 2007-11-25 | 2011-05-17 | Spansion Isreal, Ltd | Recovery while programming non-volatile memory (NVM) |
| US7392544B1 (en) | 2007-12-18 | 2008-06-24 | Kaspersky Lab, Zao | Method and system for anti-malware scanning with variable scan settings |
| US7752666B2 (en) | 2007-12-21 | 2010-07-06 | At&T Labs, Inc. | Detection of routing loops based on time-to-live expiries |
| US7720764B2 (en) | 2008-02-01 | 2010-05-18 | Kenneth James Emerson | Method, device, and system for completing on-line financial transaction |
| US7519987B1 (en) | 2008-02-05 | 2009-04-14 | International Business Machines Corporation | Method, system, and apparatus to allow for credential vault usage in templated portal applications |
| US7472420B1 (en) | 2008-04-23 | 2008-12-30 | Kaspersky Lab, Zao | Method and system for detection of previously unknown malware components |
| US7530106B1 (en) | 2008-07-02 | 2009-05-05 | Kaspersky Lab, Zao | System and method for security rating of computer processes |
| US7540030B1 (en) | 2008-09-15 | 2009-05-26 | Kaspersky Lab, Zao | Method and system for automatic cure against malware |
| US7607174B1 (en) | 2008-12-31 | 2009-10-20 | Kaspersky Lab Zao | Adaptive security for portable information devices |
| US7743419B1 (en) | 2009-10-01 | 2010-06-22 | Kaspersky Lab, Zao | Method and system for detection and prediction of computer virus-related epidemics |
-
2010
- 2010-10-05 WO PCT/US2010/002682 patent/WO2011119137A1/en active Application Filing
- 2010-10-05 EP EP10848579.8A patent/EP2438511B1/en active Active
- 2010-10-05 US US13/514,178 patent/US8769373B2/en active Active
- 2010-10-05 JP JP2013501220A patent/JP2013523043A/ja active Pending
- 2010-10-05 CN CN2010800655963A patent/CN102812431A/zh active Pending
Patent Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US3508194A (en) * | 1964-04-06 | 1970-04-21 | Ibm | Error detection and correction system |
| US3786439A (en) * | 1972-12-26 | 1974-01-15 | Ibm | Error detection systems |
| US6618395B1 (en) * | 1999-05-27 | 2003-09-09 | 3Com Corporation | Physical coding sub-layer for transmission of data over multi-channel media |
Cited By (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103280242A (zh) * | 2013-05-08 | 2013-09-04 | 中国人民解放军国防科学技术大学 | 适用于片上存储edac的可配置后台刷新方法 |
| CN103280242B (zh) * | 2013-05-08 | 2016-02-17 | 中国人民解放军国防科学技术大学 | 适用于片上存储edac的可配置后台刷新方法 |
Also Published As
| Publication number | Publication date |
|---|---|
| EP2438511A4 (en) | 2013-01-09 |
| EP2438511B1 (en) | 2019-07-03 |
| US8769373B2 (en) | 2014-07-01 |
| WO2011119137A1 (en) | 2011-09-29 |
| JP2013523043A (ja) | 2013-06-13 |
| EP2438511A1 (en) | 2012-04-11 |
| US20130019140A1 (en) | 2013-01-17 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN102812431A (zh) | 用于识别与保护一组源数据的完整性的方法 | |
| US11853171B2 (en) | Systems and methods for quorum-based data processing | |
| US11182247B2 (en) | Encoding and storage node repairing method for minimum storage regenerating codes for distributed storage systems | |
| KR102412616B1 (ko) | 대수적 조작으로부터 데이터를 보호하는 방법 | |
| JP2021513141A (ja) | 2次元バーコードの生成及び識別 | |
| RU2680350C2 (ru) | Способ и система распределенного хранения восстанавливаемых данных с обеспечением целостности и конфиденциальности информации | |
| CA2771622A1 (en) | Methods and apparatus employing fec codes with permanent inactivation of symbols for encoding and decoding processes | |
| JP7065888B6 (ja) | 暗号装置及び方法 | |
| CN101779190A (zh) | 信息传输和综合保护的方法 | |
| CN102799495B (zh) | 用于生成校验和的装置 | |
| CN104769675A (zh) | 数据处理 | |
| CN104769881A (zh) | 具有错误校正的aes实现方式 | |
| Bartz et al. | Rank-metric codes and their applications | |
| Loureiro et al. | Function hiding based on error correcting codes | |
| Lee et al. | Punctured Reed–Muller code‐based McEliece cryptosystems | |
| CN101980471B (zh) | 数字签名方法、数字签名的验证方法、装置及系统 | |
| Huang et al. | Secure RAID schemes for distributed storage | |
| Wang et al. | New error detecting codes for the design of hardware resistant to strong fault injection attacks | |
| WO2015092585A1 (en) | Method and apparatus for cipher fault detection | |
| Freitas et al. | Data Validation System Using QR Code and Meaningless Reversible Degradation | |
| Tabatabaei et al. | AACI: The mechanism for approximate authentication and correction of images | |
| CN112614557A (zh) | 电子病历加密存档方法 | |
| US20140052987A1 (en) | Method and System Making it Possible to Test a Cryptographic Integrity of an Error Tolerant Data Item | |
| US11196447B2 (en) | Computer-implemented method for error-correction-encoding and encrypting of a file | |
| CN112613844A (zh) | 一种人事合同电子签名方法 |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| C06 | Publication | ||
| PB01 | Publication | ||
| C10 | Entry into substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| C02 | Deemed withdrawal of patent application after publication (patent law 2001) | ||
| WD01 | Invention patent application deemed withdrawn after publication |
Application publication date: 20121205 |