WO2011007686A1 - 移動通信システム、移動局及び無線基地局 - Google Patents
移動通信システム、移動局及び無線基地局 Download PDFInfo
- Publication number
- WO2011007686A1 WO2011007686A1 PCT/JP2010/061352 JP2010061352W WO2011007686A1 WO 2011007686 A1 WO2011007686 A1 WO 2011007686A1 JP 2010061352 W JP2010061352 W JP 2010061352W WO 2011007686 A1 WO2011007686 A1 WO 2011007686A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- radio base
- base station
- frequency carriers
- mobile
- frequency
- Prior art date
Links
- 238000010295 mobile communication Methods 0.000 title claims abstract description 28
- 239000000969 carrier Substances 0.000 claims abstract description 47
- 238000004891 communication Methods 0.000 claims abstract description 44
- 230000006870 function Effects 0.000 description 29
- 230000002776 aggregation Effects 0.000 description 12
- 238000004220 aggregation Methods 0.000 description 12
- 238000010586 diagram Methods 0.000 description 6
- 238000000034 method Methods 0.000 description 5
- 230000005540 biological transmission Effects 0.000 description 3
- 239000002131 composite material Substances 0.000 description 3
- 230000002265 prevention Effects 0.000 description 3
- 238000009795 derivation Methods 0.000 description 1
- 230000007774 longterm Effects 0.000 description 1
- 239000000203 mixture Substances 0.000 description 1
- 230000011218 segmentation Effects 0.000 description 1
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/04—Key management, e.g. using generic bootstrapping architecture [GBA]
- H04W12/041—Key generation or derivation
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/04—Key management, e.g. using generic bootstrapping architecture [GBA]
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/002—Countermeasures against attacks on cryptographic mechanisms
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/04—Key management, e.g. using generic bootstrapping architecture [GBA]
- H04W12/043—Key management, e.g. using generic bootstrapping architecture [GBA] using a trusted network node as an anchor
- H04W12/0431—Key distribution or pre-distribution; Key agreement
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W88/00—Devices specially adapted for wireless communication networks, e.g. terminals, base stations or access point devices
- H04W88/08—Access point devices
Definitions
- the present invention relates to a mobile communication system, a mobile station, and a radio base station.
- a mobile station UE communicates with a radio base station eNB using a plurality of frequency carriers simultaneously.
- a technique called “Carrier Aggregation” is available.
- the frequency carrier constituting the “Carrier Aggregation” is called “Component Carrier”.
- Each “Component Carrier” may function as an independent LTE cell. That is, it is possible to perform “Carrier Aggregation” by setting an LTE cell using a different frequency carrier as “Component Carrier”.
- the key KeNB used for wireless security processing is the “PCI (Physical Cell Identity) and physical cell ID” and “E-ARFCN (E-UTRA Absolute Radio Frequency Number, frequency code) of the cell in communication. Depends on both.
- KDF Key Derivation Function
- such a key KeNB is generated from a different parent key KASME for each mobile station UE. Accordingly, in the LTE scheme, the key KeNB is cell specific and UE specific (UE specific).
- the LTE-Advanced mobile communication system has a problem that wireless security processing in “Carrier Aggregation” is not defined.
- an object of the present invention is to provide a mobile communication system, a mobile station, and a radio base station that can appropriately implement radio security processing in “Carrier Aggregation”.
- a first feature of the present invention is a mobile communication system, in which a mobile station is configured to communicate with a radio base station using a plurality of frequency carriers simultaneously.
- the mobile station is configured to perform communication by applying the same key to each of the plurality of frequency carriers.
- a second feature of the present invention is a mobile station comprising a communication unit configured to perform communication with a radio base station using a plurality of frequency carriers simultaneously, and the communication unit includes:
- the gist of the invention is that the same key is applied to each of the plurality of frequency carriers to perform communication security processing.
- a third feature of the present invention is a radio base station, comprising a communication unit configured to perform communication with a mobile station using a plurality of frequency carriers simultaneously, and the communication unit includes
- the gist of the invention is that the same key is applied to each of the plurality of frequency carriers to perform communication security processing.
- FIG. 1 is an overall configuration diagram of a mobile communication system according to a first embodiment of the present invention.
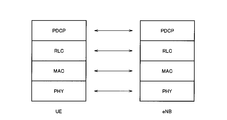
- FIG. 2 is a protocol stack diagram of the mobile communication system according to the first embodiment of the present invention.
- FIG. 3 is a diagram for explaining an example in which three PDCP-SDUs are transmitted in the mobile communication system according to the first embodiment of the present invention.
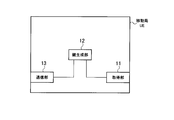
- FIG. 4 is a functional block diagram of the mobile station according to the first embodiment of the present invention.
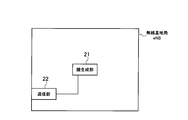
- FIG. 5 is a functional block diagram of the radio base station according to the first embodiment of the present invention.
- FIG. 6 is a sequence diagram showing operations of the mobile communication system according to the first embodiment of the present invention.
- the mobile communication system according to the present embodiment is an LTE-Advanced mobile communication system, in which the mobile station UE uses a plurality of frequency carriers simultaneously with the radio base station eNB. Communication can be performed, that is, “Carrier Aggregation” can be used.
- PCI Physical Cell ID
- the cells # 1 to # 3 are all cells under the radio base station eNB.
- the cells # 1 to # 3 may be independent LTE cells.
- the mobile station UE and the radio base station eNB include a physical (PHY) layer function, a MAC (Media Access Control) layer function, and an RLC (Radio Link Control). ) Layer function and PDCP (Packet Data Convergence Protocol) layer function.
- PHY physical
- MAC Media Access Control
- RLC Radio Link Control
- PDCP Packet Data Convergence Protocol
- the PDCP layer function is configured to perform radio security processing in communication between the mobile station UE and the radio base station eNB.
- the RLC layer function is configured to perform retransmission control in the RLC layer
- the MAC layer function is configured to perform HARQ retransmission control.
- FIG. 3 shows an example in which three PDCP-SDUs # 1 to # 3 are transmitted.
- the PDCP layer function performs a ciphering process on the PDCP-SDUs # 1 to # 3 of U-plane, and performs PDCP-PDUs # 1 to # 3. Generate and pass to RLC layer function.
- the PDCP layer function provides MAC-I for integrity protection processing in addition to performing ciphering processing for PDCP-SDUs # 1 to # 3 of C-plane.
- PDCP-PDUs # 1 to # 3 are generated and passed to the RLC layer function.
- the RLC layer function performs segment processing (segmentation) or concatenation processing (concatenation) so as to generate RLC-PDUs # 1 to # 4 of TBS (Transmission Block Size) specified by the scheduler, and RLC. Add a header.
- the RLC layer function performs retransmission control in the RLC layer when activated in the AM mode.
- the RLC layer function passes the generated RLC-PDUs # 1 to # 4 to the MAC layer function.
- the MAC layer function adds MAC headers to RLC-PDUs # 1 to # 4 to generate MAC-PDUs # 1 to # 4, and uses the HARQ retransmission control to implement the physical layer function. Send to.
- the mobile station UE includes an acquisition unit 11, a key generation unit 12, and a communication unit 13.
- the acquiring unit 11 From the radio base station eNB, the acquiring unit 11 performs “PCI” for identifying each cell under the radio base station eNB and “E-ARFCN (E ⁇ ) for identifying the frequency carrier used in each cell. UTRA Absolute Radio Frequency Channel Number) ”.
- the key generation unit 12 is configured to generate a key KeNB based on “PCI” and “E-ARFCN” acquired by the acquisition unit 11.
- the key generation unit 12 may be configured to generate a key KeNB by a key generation function KDF (PCI, E-ARFCN).
- KDF key generation function
- the key KeNB is a key for generating keys (KUPenc, KRRCenc, KRRCint) used in radio security processing in the PDCP layer function.
- KUPenc is a key for U-plane concealment processing
- KRRCenc is a key for C-plane concealment processing
- KRRCint is a key for C-plane falsification protection processing
- the key generation unit 12 is configured to generate one key KeNB to be applied to all of a plurality of frequency carriers.
- the key generation unit 12 applies a key (KUPenc, KRRCenc, KRRCint) used in wireless security processing in the PDCP layer function to all of a plurality of frequency carriers. It is configured to generate a set of keys (KUPenc, KRRCenc, KRRCint).
- the key generation unit 12 is based on “PCI” and “E-ARFCN” of any one of a plurality of frequency carriers, specifically, “Anchor Carrier”.
- the key KeNB is generated based on “PCI” and “E-ARFCN”.
- one “Anchor Carrier” is determined from a plurality of frequency carriers constituting “Carrier Aggregation”.
- “Anchor Carrier” is used at “Connection Setup”, “Security Mode Command”, “Reconfiguration”, “Intra-RAT Handover”, “Inter-RAT Handover”, “Re- In the case of “establishment” or the like, the radio base station eNB sets the mobile station UE.
- Anchor Carrier may be defined as a frequency carrier in which the mobile station UE first establishes an RRC connection.
- the key generation unit 12 when “Anchor Carrier” is changed, the key generation unit 12 generates the above-described key KeNB again based on “PCI” and “E-ARFCN” of “Anchor Carrier” after the change. It may be configured.
- an intra-eNB handover may be activated from the radio base station eNB.
- Intra-eNB handover is instructed, the mobile station UE changes the “Anchor Carrier” and simultaneously updates the key KeNB, and performs reset processing for each layer of PHY, MAC, and RLC in the same manner as the LTE handover. You may go.
- the communication unit 13 includes the physical (PHY) layer function, the MAC layer function, the RLC layer function, and the PDCP layer function, and communicates with the radio base station eNB using a plurality of frequency carriers at the same time. Is configured to do.
- the secret processing and falsification protection processing algorithms used in the PDCP layer are also configured to be the same in each of the plurality of frequency carriers.
- the algorithm to be used is from the radio base station eNB at “Security Mode Command”, “Reconfiguration”, “Intra-RAT Handover”, “Inter-RAT Handover”, “Re-establishment”, etc. ,
- the radio base station eNB sets the mobile station UE.
- the radio base station eNB includes a key generation unit 21 and a communication unit 22.
- the key generation unit 21 has the same function as the key generation unit 12 shown in FIG. 4
- the communication unit 22 has the same function as the communication unit 13 shown in FIG.
- step S1001 the mobile station UE requests the radio base station eNB to establish communication (RRC (Radio Resource Control) connection) with the cell # 1 “RRC”. Send "Connection Request”.
- RRC Radio Resource Control
- step S1002 the radio base station eNB transmits “RRC Connection Setup” for the “RRC Connection Request” received in step S1001 to the mobile station UE.
- step S1003 the mobile station UE transmits “RRC Connection Setup Complete” to the radio base station eNB.
- step S1004 an RRC connection using the frequency carrier F1 is established between the mobile station UE and the radio base station eNB, and communication via the RRC connection is started.
- step S1005 the radio base station eNB transmits “RRC Connection Reconfiguration” related to the RRC connection established using the frequency carrier F1 to the mobile station UE.
- Such “RRC Connection Reconfiguration” is to set that the frequency carrier F2 is added as a radio resource used for communication.
- step S1006 the mobile station UE transmits “RRC Connection Reconfiguration Complete” to the radio base station eNB.
- step S1007 communication using the frequency carrier F1 and the frequency carrier F2 simultaneously is started between the mobile station UE and the radio base station eNB.
- the RLC-PDU may be retransmitted by “Composite Carrier” different from the initial transmission.
- the RLC-PDU includes one or more concealed PDCP-PDUs. Therefore, when the key KeNB that follows the LTE scheme and depends on each frequency carrier is used, the following points are concerned.
- the PDCP layer is once deprived of confidentiality, and a concealment process that matches the "Composite Carrier" used for retransmission is performed. It is assumed that it must be done again to regenerate the RLC-PDU.
- the receiving side when transmitting with a connection using a different "Composite Carrier" for each PDCP-PDU segment, the receiving side receives each segment of the received PDCP-PDU. It is assumed that the key used for the concealment process is different, and the PDCP-PDU decryption process becomes extremely difficult.
- the first feature of the present embodiment is a mobile communication system, in which the mobile station UE is configured to communicate with the radio base station eNB using a plurality of frequency carriers simultaneously.
- the gist of the present invention is that the mobile station UE is configured to perform communication security processing by applying the same key KeNB to all the frequency carriers.
- the mobile station UE sets “PCI (physical cell ID)” and “E-ARFCN (frequency code)” of “Anchor Carrier (one of a plurality of frequency carriers)”. Based on this, it may be configured to generate such a key KeNB.
- PCI physical cell ID
- E-ARFCN frequency code
- the same security processing confidential processing and tampering prevention processing
- the same security processing may be used for all the above-described frequency carriers.
- “Anchor Carrier (anchor carrier)” may be specified by the radio base station.
- the mobile station UE when “Anchor Carrier” is changed by the radio base station eNB, the mobile station UE is based on “PCI” and “E-ARFCN” of “Anchor Carrier” after the change.
- the key KeNB described above may be generated.
- the second feature of the present embodiment is a mobile station UE, comprising a communication unit 13 configured to communicate with a radio base station eNB using a plurality of frequency carriers simultaneously,
- the gist of the communication unit 13 is that the same key KeNB is applied to all the frequency carriers to perform communication security processing.
- the key generation unit 12 configured to generate the key KeNB based on “PCI” and “E-ARFCN” of “Anchor Carrier” may be provided. .
- the communication unit 13 may be configured to use the same security processing (confidential processing and tampering prevention processing) algorithm for all the above-described frequency carriers.
- “Anchor Carrier” may be specified by the radio base station eNB.
- the key generation unit 12 sets “PCI” and “E-ARFCN” of “Anchor Carrier” after the change. Based on this, the above-described key KeNB may be generated.
- a third feature of the present embodiment is a radio base station eNB, which includes a communication unit 22 configured to perform communication with a mobile station UE using a plurality of frequency carriers simultaneously, The gist is that the communication unit 22 is configured to apply the same key KeNB to all the frequency carriers to perform communication security processing.
- a key generation unit 21 configured to generate the key KeNB based on “PCI” and “E-ARFCN” of “Anchor Carrier” may be provided. .
- the communication unit 22 may be configured to use the same security processing (confidential processing and tampering prevention processing) algorithm for all the above-described frequency carriers.
- the key generation unit 21 when “Anchor Carrier” is changed, the key generation unit 21 performs the above-described operation based on “PCI” and “E-ARFCN” of “Anchor Carrier” after the change.
- the key KeNB may be configured to be generated.
- radio base station eNB and the mobile station UE described above may be implemented by hardware, may be implemented by a software module executed by a processor, or may be implemented by a combination of both. .
- Software modules include RAM (Random Access Memory), flash memory, ROM (Read Only Memory), EPROM (Erasable Programmable ROM), EEPROM (Electronically Erasable and Programmable, Removable ROM, and Hard Disk). Alternatively, it may be provided in a storage medium of an arbitrary format such as a CD-ROM.
- Such a storage medium is connected to the processor so that the processor can read and write information from and to the storage medium. Further, such a storage medium may be integrated in the processor. Such a storage medium and processor may be provided in the ASIC. Such an ASIC may be provided in the radio base station eNB or the mobile station UE. Further, the storage medium and the processor may be provided as a discrete component in the radio base station eNB or the mobile station UE.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Mobile Radio Communication Systems (AREA)
Abstract
Description
図1乃至図3を参照して、本発明の第1の実施形態に係る移動通信システムについて説明する。
Claims (15)
- 移動局が、無線基地局との間で、複数の周波数キャリアを用いて通信を行うように構成されている移動通信システムであって、
前記移動局は、前記複数の周波数キャリアの全てに対して同じ鍵を適用して通信のセキュリティ処理を行うように構成されていることを特徴とする移動通信システム。 - 前記移動局は、前記複数の周波数キャリアのいずれか1つの物理セルID及び周波数コードに基づいて、前記鍵を生成するように構成されていることを特徴とする請求項1に記載の移動通信システム。
- 前記複数の周波数キャリアの全てに対して同じセキュリティ処理のアルゴリズムが適用されることを特徴とする請求項1に記載の移動通信システム。
- 前記複数の周波数キャリアのいずれか1つは、前記無線基地局によって指定されるアンカーキャリアであることを特徴とする請求項2に記載の移動通信システム。
- 前記アンカーキャリアが、前記無線基地局によって変更される場合、前記移動局は、変更後の前記アンカーキャリアの物理セルID及び周波数コードに基づいて、前記鍵を生成するように構成されていることを特徴とする請求項4に記載の移動通信システム。
- 無線基地局との間で、複数の周波数キャリアを同時に用いて通信を行うように構成されている通信部を具備し、
前記通信部は、前記複数の周波数キャリアの全てに対して同じ鍵を適用して通信のセキュリティ処理を行うように構成されていることを特徴とする移動局。 - 前記複数の周波数キャリアのいずれか1つの物理セルID及び周波数コードに基づいて、前記鍵を生成するように構成されている鍵生成部を具備することを特徴とする請求項6に記載の移動局。
- 前記通信部は、前記複数の周波数キャリアの全てに対して同じセキュリティ処理のアルゴリズムを用いるように構成されていることを特徴とする請求項6に記載の移動局。
- 前記複数の周波数キャリアのいずれか1つは、前記無線基地局によって指定されるアンカーキャリアであることを特徴とする請求項7に記載の移動局。
- 前記アンカーキャリアが、前記無線基地局によって変更される場合、前記鍵生成部は、変更後の前記アンカーキャリアの物理セルID及び周波数コードに基づいて、前記鍵を生成するように構成されていることを特徴とする請求項9に記載の移動局。
- 移動局との間で、複数の周波数キャリアを同時に用いて通信を行うように構成されている通信部を具備し、
前記通信部は、前記複数の周波数キャリアの全てに対して同じ鍵を適用して通信のセキュリティ処理を行うように構成されていることを特徴とする無線基地局。 - 前記複数の周波数キャリアのいずれか1つの物理セルID及び周波数コードに基づいて、前記鍵を生成するように構成されている鍵生成部を具備することを特徴とする請求項11に記載の無線基地局。
- 前記通信部は、前記複数の周波数キャリアの全てに対して同じセキュリティ処理のアルゴリズムを用いるように構成されていることを特徴とする請求項11に記載の無線基地局。
- 前記複数の周波数キャリアのいずれか1つは、前記無線基地局によって指定されるアンカーキャリアであることを特徴とする請求項12に記載の無線基地局。
- 前記アンカーキャリアが、変更される場合、前記鍵生成部は、変更後の前記アンカーキャリアの物理セルID及び周波数コードに基づいて、前記鍵を生成するように構成されていることを特徴とする請求項14に記載の無線基地局。
Priority Applications (8)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CA2767989A CA2767989C (en) | 2009-07-16 | 2010-07-02 | Mobile communication system, mobile station and radio base station using carrier aggregation security process |
| US13/383,731 US8676164B2 (en) | 2009-07-16 | 2010-07-02 | Mobile communication system, mobile station, and radio base station using a carrier aggregation security process |
| KR1020127002356A KR101302064B1 (ko) | 2009-07-16 | 2010-07-02 | 이동통신시스템, 이동국 및 무선기지국 |
| CN201080031950.0A CN102474717B (zh) | 2009-07-16 | 2010-07-02 | 移动通信系统、移动台以及无线基站 |
| EP10799745.4A EP2456244B1 (en) | 2009-07-16 | 2010-07-02 | Mobile communication system, mobile station and radio base station |
| AU2010271918A AU2010271918B2 (en) | 2009-07-16 | 2010-07-02 | Mobile communication system, mobile station and radio base station |
| RU2012103447/08A RU2493675C1 (ru) | 2009-07-16 | 2010-07-02 | Система мобильной связи, мобильная станция и базовая радиостанция |
| ES10799745.4T ES2449698T3 (es) | 2009-07-16 | 2010-07-02 | Sistema de comunicación móvil, estación móvil, y una estación de base radioeléctrica |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP2009168130A JP5038366B2 (ja) | 2009-07-16 | 2009-07-16 | 移動通信システム、移動局及び無線基地局 |
| JP2009-168130 | 2009-07-16 |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2011007686A1 true WO2011007686A1 (ja) | 2011-01-20 |
Family
ID=43449296
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/JP2010/061352 WO2011007686A1 (ja) | 2009-07-16 | 2010-07-02 | 移動通信システム、移動局及び無線基地局 |
Country Status (11)
| Country | Link |
|---|---|
| US (1) | US8676164B2 (ja) |
| EP (1) | EP2456244B1 (ja) |
| JP (1) | JP5038366B2 (ja) |
| KR (1) | KR101302064B1 (ja) |
| CN (1) | CN102474717B (ja) |
| AU (1) | AU2010271918B2 (ja) |
| CA (1) | CA2767989C (ja) |
| CL (1) | CL2012000128A1 (ja) |
| ES (1) | ES2449698T3 (ja) |
| RU (1) | RU2493675C1 (ja) |
| WO (1) | WO2011007686A1 (ja) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2022160616A (ja) * | 2013-01-17 | 2022-10-19 | 日本電気株式会社 | 基地局及び基地局により行われる方法 |
Families Citing this family (16)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN102595399B (zh) * | 2008-06-23 | 2017-02-01 | 华为技术有限公司 | 密钥衍生方法、设备及系统 |
| EP2690901A4 (en) * | 2011-03-25 | 2015-05-06 | Fujitsu Ltd | BASIC STATION, COMMUNICATION SYSTEM AND COMMUNICATION PROCESS |
| JP5519566B2 (ja) * | 2011-04-05 | 2014-06-11 | 株式会社Nttドコモ | 移動通信方法、無線基地局、移動管理ノード及び移動局 |
| US9414223B2 (en) * | 2012-02-17 | 2016-08-09 | Nokia Technologies Oy | Security solution for integrating a WiFi radio interface in LTE access network |
| JP6077839B2 (ja) * | 2012-11-22 | 2017-02-08 | 株式会社Nttドコモ | 移動通信システム、無線基地局及び移動局 |
| CN110290523B (zh) * | 2012-12-28 | 2022-12-27 | 北京三星通信技术研究有限公司 | 配置和传输加密密匙的方法 |
| JP6309543B2 (ja) * | 2013-01-09 | 2018-04-11 | 株式会社Nttドコモ | 無線基地局間(inter−eNB)キャリアアグリゲーションによる保護された無線アクセス |
| WO2014109602A1 (en) | 2013-01-11 | 2014-07-17 | Lg Electronics Inc. | Method and apparatus for applying security information in wireless communication system |
| MX342101B (es) * | 2013-01-30 | 2016-09-13 | Ericsson Telefon Ab L M | Generación de clave de seguridad para conectividad dual. |
| JP6035227B2 (ja) * | 2013-10-31 | 2016-11-30 | 株式会社Nttドコモ | 移動通信方法 |
| JP2015095675A (ja) * | 2013-11-08 | 2015-05-18 | 株式会社Nttドコモ | 移動通信方法 |
| CN110809326B (zh) * | 2014-01-16 | 2023-05-02 | 三星电子株式会社 | 用户设备及其方法 |
| USD917802S1 (en) | 2018-08-16 | 2021-04-27 | Samsung Electronics Co., Ltd. | Clothing care machine |
| USD886471S1 (en) | 2018-08-17 | 2020-06-09 | Samsung Electronics Co., Ltd. | Trouser stretcher |
| CN110881203A (zh) | 2018-09-05 | 2020-03-13 | 电信科学技术研究院有限公司 | 一种定位资源协调方法、装置、网络节点、终端及基站 |
| US11363582B2 (en) * | 2019-12-20 | 2022-06-14 | Qualcomm Incorporated | Key provisioning for broadcast control channel protection in a wireless network |
Citations (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2005020076A (ja) * | 2003-06-23 | 2005-01-20 | Toshiba Corp | 通信方法、送信装置および受信装置 |
| JP2006352225A (ja) * | 2005-06-13 | 2006-12-28 | Hitachi Ltd | 認証システム、無線通信端末及び無線基地局 |
Family Cites Families (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US7224713B2 (en) * | 1998-04-09 | 2007-05-29 | Andrzej Partyka | Telemetry system with authentication |
| US7418043B2 (en) * | 2000-07-19 | 2008-08-26 | Lot 41 Acquisition Foundation, Llc | Software adaptable high performance multicarrier transmission protocol |
| US7352868B2 (en) * | 2001-10-09 | 2008-04-01 | Philip Hawkes | Method and apparatus for security in a data processing system |
| RU2402814C2 (ru) * | 2005-04-19 | 2010-10-27 | Майкрософт Корпорейшн | Сетевые коммерческие транзакции |
-
2009
- 2009-07-16 JP JP2009168130A patent/JP5038366B2/ja active Active
-
2010
- 2010-07-02 ES ES10799745.4T patent/ES2449698T3/es active Active
- 2010-07-02 KR KR1020127002356A patent/KR101302064B1/ko not_active IP Right Cessation
- 2010-07-02 WO PCT/JP2010/061352 patent/WO2011007686A1/ja active Application Filing
- 2010-07-02 US US13/383,731 patent/US8676164B2/en active Active
- 2010-07-02 EP EP10799745.4A patent/EP2456244B1/en active Active
- 2010-07-02 CA CA2767989A patent/CA2767989C/en not_active Expired - Fee Related
- 2010-07-02 AU AU2010271918A patent/AU2010271918B2/en not_active Ceased
- 2010-07-02 CN CN201080031950.0A patent/CN102474717B/zh active Active
- 2010-07-02 RU RU2012103447/08A patent/RU2493675C1/ru not_active IP Right Cessation
-
2012
- 2012-01-16 CL CL2012000128A patent/CL2012000128A1/es unknown
Patent Citations (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2005020076A (ja) * | 2003-06-23 | 2005-01-20 | Toshiba Corp | 通信方法、送信装置および受信装置 |
| JP2006352225A (ja) * | 2005-06-13 | 2006-12-28 | Hitachi Ltd | 認証システム、無線通信端末及び無線基地局 |
Cited By (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2022160616A (ja) * | 2013-01-17 | 2022-10-19 | 日本電気株式会社 | 基地局及び基地局により行われる方法 |
| JP7327603B2 (ja) | 2013-01-17 | 2023-08-16 | 日本電気株式会社 | 基地局及び基地局により行われる方法 |
Also Published As
| Publication number | Publication date |
|---|---|
| JP2011024037A (ja) | 2011-02-03 |
| KR101302064B1 (ko) | 2013-09-05 |
| AU2010271918B2 (en) | 2013-11-07 |
| CL2012000128A1 (es) | 2012-08-24 |
| EP2456244B1 (en) | 2013-12-18 |
| EP2456244A1 (en) | 2012-05-23 |
| CN102474717B (zh) | 2014-03-12 |
| AU2010271918A1 (en) | 2012-02-16 |
| CA2767989A1 (en) | 2011-01-20 |
| RU2493675C1 (ru) | 2013-09-20 |
| CA2767989C (en) | 2014-12-16 |
| US20120157053A1 (en) | 2012-06-21 |
| KR20120042872A (ko) | 2012-05-03 |
| EP2456244A4 (en) | 2013-01-09 |
| US8676164B2 (en) | 2014-03-18 |
| ES2449698T3 (es) | 2014-03-20 |
| CN102474717A (zh) | 2012-05-23 |
| JP5038366B2 (ja) | 2012-10-03 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| JP5038366B2 (ja) | 移動通信システム、移動局及び無線基地局 | |
| TWI332345B (en) | Security considerations for the lte of umts | |
| Forsberg et al. | LTE security | |
| CN103945376B (zh) | 用于高吞吐量无线通信的在减少分组丢失情况下进行密钥重置的无线设备和方法 | |
| KR101507482B1 (ko) | Lte 모바일 유닛에서의 비접속 계층(nas) 보안을 가능하게 하는 방법 및 장치 | |
| US8787572B1 (en) | Enhanced association for access points | |
| US8627092B2 (en) | Asymmetric cryptography for wireless systems | |
| US8392968B2 (en) | Stateless cryptographic protocol-based hardware acceleration | |
| US7890745B2 (en) | Apparatus and method for protection of management frames | |
| CN102804729B (zh) | 用于加密错误检测和恢复的系统、方法和装置 | |
| WO2014080837A1 (ja) | 移動通信システム、無線基地局及び移動局 | |
| JP2010028747A (ja) | 秘匿処理を行う送信装置及び受信装置 | |
| JP4550759B2 (ja) | 通信システム及び通信装置 | |
| Hall | Detection of rogue devices in wireless networks | |
| CN113455034B (zh) | 一种通信方法及装置 | |
| CN101883358A (zh) | 保障单收发机时间插槽式分布cr mac协议安全的方法 | |
| CN101835151B (zh) | 空中接口密钥的更新方法及无线接入系统 | |
| KR100968523B1 (ko) | 세션키 분배 방법, 단말 및 그 방법을 실행하는 프로그램이기록된 기록매체 | |
| Rajput | Wireless security protocols |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| WWE | Wipo information: entry into national phase |
Ref document number: 201080031950.0 Country of ref document: CN |
|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 10799745 Country of ref document: EP Kind code of ref document: A1 |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 2767989 Country of ref document: CA |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 2012000128 Country of ref document: CL |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 708/CHENP/2012 Country of ref document: IN |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 2010271918 Country of ref document: AU |
|
| ENP | Entry into the national phase |
Ref document number: 20127002356 Country of ref document: KR Kind code of ref document: A |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 2010799745 Country of ref document: EP |
|
| ENP | Entry into the national phase |
Ref document number: 2010271918 Country of ref document: AU Date of ref document: 20100702 Kind code of ref document: A |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 2012103447 Country of ref document: RU |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 13383731 Country of ref document: US |