WO2012105352A1 - ブロック暗号化装置、復号装置、暗号化方法、復号方法およびプログラム - Google Patents
ブロック暗号化装置、復号装置、暗号化方法、復号方法およびプログラム Download PDFInfo
- Publication number
- WO2012105352A1 WO2012105352A1 PCT/JP2012/051326 JP2012051326W WO2012105352A1 WO 2012105352 A1 WO2012105352 A1 WO 2012105352A1 JP 2012051326 W JP2012051326 W JP 2012051326W WO 2012105352 A1 WO2012105352 A1 WO 2012105352A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- bit
- intermediate variable
- adjustment value
- block
- encryption
- Prior art date
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/06—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols the encryption apparatus using shift registers or memories for block-wise or stream coding, e.g. DES systems or RC4; Hash functions; Pseudorandom sequence generators
- H04L9/0618—Block ciphers, i.e. encrypting groups of characters of a plain text message using fixed encryption transformation
- H04L9/0625—Block ciphers, i.e. encrypting groups of characters of a plain text message using fixed encryption transformation with splitting of the data block into left and right halves, e.g. Feistel based algorithms, DES, FEAL, IDEA or KASUMI
Definitions
- the present invention relates to a block cipher operation mode, and more particularly, to a bit block cipher technology of n to less than 2n, which has general and high security by n-bit block cipher.
- the block cipher is a set of substitutions uniquely determined by the key, and the input to the substitution corresponds to plaintext and the output corresponds to the ciphertext.
- the length of plaintext and ciphertext is called block size.
- a block cipher having a block size of n bits (n is an integer of 1 or more) is generally called an n-bit block cipher.
- DES Data Encryption Standard
- DES Data Encryption Standard
- the round function processing is relatively simple and the randomness of the output of the round function itself is low (it can be easily distinguished from random numbers), so the Feistel-type substitution iteration count is sufficiently large. It is necessary to improve the randomness of the entire 64-bit. In the case of DES, it is repeated 16 times.
- the block size of block ciphers is fixed at 64,128, etc., and is not variable. Therefore, in order to construct block ciphers with other block sizes, an approach that uses existing encryption processing including block ciphers as a component is common. It is.
- the advantage of this approach is that some sort of safety proof is possible based on the computational safety of the parts. For example, in a typical block cipher construction method called Feistel substitution, if the output of the round function that is a part has a high randomness so that it cannot be efficiently distinguished from a true random number, this Feistel type substitution is performed three to four times. It is proved by Luby and Rackoff that it becomes a 2n-bit block cipher in which the computational security is guaranteed as a whole by repeating this process once.
- Such a block cipher is called “double block length block cipher” in the sense that a 2n bit block size is realized by using an existing n bit block size block cipher as a component.
- the block size to be achieved is (n + m) bits (where m is 1 or more and less than n), and a block cipher with this block size is called a “partial block length block cipher”.
- FIG. 11 and FIG. 12 are diagrams illustrating an example of a method by repeating the Feistel type replacement four times.
- Figure 11 shows a procedure for generating a ciphertext y L, y R plaintext x L, x R
- FIG. 12 shows a procedure of returning ciphertext y L, the y R plaintext x L, the x R.
- the security guarantee is limited to the case where the number of encryptions q processed with one key is sufficiently smaller than 2 n / 2 (this is expressed as q ⁇ 2 n / 2 ). ing. 2 n / 2 is called a birthday limit, and an attack using the result of encryption about the number of birthday limits is generally called a birthday attack. Such an attack becomes a real threat when using a 64-bit block cipher, and it is considered a future risk even when a 128-bit block cipher is used.
- Non-Patent Document 2 XLS disclosed in Non-Patent Document 2 by Risenpart and Rogaway is known. This is to realize (n + m) bit block cipher by using n bit block cipher three times, but the security is still sufficiently higher than the number of encryptions q processed with one key is 2 n / 2. It is limited to small cases, and only guarantees safety up to the birthday limit of n.
- Non-Patent Document 4 discloses the method described in Non-Patent Document 4, etc., and converting the block cipher into a function that does not have an inverse function, and then using it as a component.
- Non-Patent Document 1 when the limit of q is improved to 2 (n + m) / 2 with a partial block length block cipher of (n + m) bits, (n + m) round function calls may be required.
- Non-Patent Document 5 claims that safety exceeding the birthday limit is obtained with relatively few repetitions of Feistel substitution (six times), but the problem is that proof is asymptotic and quantitative safety evaluation is difficult. There is.
- Patarin Security of Random Feistel Schemes with 5 or More Rounds, Advances in Cryptology-CRYPTO 2004, 24th Annual International Cryptology Conference, Santa Barbara, California, Sec 2004, USA, August 2004, USA, August 14 Springer 2004, pp. 106-122.
- the above-mentioned partial block length block cipher configuration method using block ciphers is a method that guarantees safety up to the birthday limit but does not have any more safety, or has safety exceeding the birthday limit. There is a problem that there is only one of the inefficient methods.
- One of the objects of the present invention is to provide a block encryption device, a decryption device, an encryption method, a decryption method, and a program for causing a computer to execute the program, which have safety exceeding the birthday limit and have high calculation efficiency. It is.
- the block encryption device includes a plaintext input unit for inputting (n + m) -bit plaintext to be encrypted when n is an integer of 1 or more and m is an integer of 1 to less than n;
- a stirring means for applying a universal hash function-based substitution to (n + m) -bit plaintext to generate an n-bit first intermediate variable and an m-bit second intermediate variable, and an n-bit block with an m-bit adjustment value
- the first intermediate variable is encrypted using the second intermediate variable as an adjustment value, and an m-bit third intermediate variable and an (n ⁇ m) -bit fourth intermediate variable are generated.
- N-bit concatenated intermediate variables A unit block encryption unit with a second adjustment value that generates an n-bit fifth intermediate variable by encrypting the intermediate variable, and a result of concatenating the third intermediate variable and the fifth intermediate variable
- a reverse agitation means for generating (n + m) -bit ciphertext by applying universal hash function-based reverse replacement, and a ciphertext output means for outputting (n + m) -bit ciphertext.
- a decryption apparatus comprising: a ciphertext input means for inputting (n + m) -bit ciphertext to be decrypted when n is an integer of 1 or more and m is an integer of 1 to n.
- N-bit intermediate variable concatenated A unit block decoding means with a first adjustment value for generating an n-bit fifth intermediate variable, and a universal hash function base for the result of concatenating the fifth intermediate variable and the fourth intermediate variable
- the reverse permutation means that generates (n + m) -bit plaintext and the plaintext output means that outputs (n + m) -bit plaintext.
- An encryption method is an encryption method for generating ciphertext from (n + m) -bit plaintext when n is an integer of 1 or more and m is an integer of 1 to less than n.
- a universal hash function based permutation is applied to the (n + m) -bit plaintext to generate a first intermediate variable of n bits and a second intermediate variable of m bits, and an n-bit block with an m-bit adjustment value
- the first intermediate variable is encrypted using the second intermediate variable as an adjustment value, and an m-bit third intermediate variable and an (n ⁇ m) -bit fourth intermediate variable are generated.
- an n-bit intermediate variable obtained by concatenating the second intermediate variable and the fourth intermediate variable is encrypted using the third intermediate variable as an adjustment value.
- the n-bit fifth intermediate variable And applying a universal hash function based inverse permutation to the result of concatenating the third intermediate variable and the fifth intermediate variable to generate (n + m) -bit ciphertext, and (n + m) -bit ciphertext to Output.
- a decryption method is a decryption method for generating plaintext from (n + m) -bit ciphertext when n is an integer of 1 or more and m is an integer of 1 to less than n. , Applying universal hash function based substitution to (n + m) -bit ciphertext to generate a first intermediate variable of m bits and a second intermediate variable of n bits, and an n-bit block cipher with an m-bit adjustment value The second intermediate variable is decoded using the first intermediate variable as an adjustment value, and a (n ⁇ m) -bit third intermediate variable and an m-bit fourth intermediate variable are generated.
- a program according to one aspect of the present invention is a program for causing a computer to execute the encryption method of the present invention. Furthermore, a program according to one aspect of the present invention is a program for causing a computer to execute the decoding method of the present invention.
- FIG. 1 is a block diagram showing a configuration example of a partial block length block encryption apparatus according to the first embodiment.
- FIG. 2 is a block diagram showing an example of the configuration of an information processing apparatus that implements the partial block length block encryption apparatus shown in FIG.
- FIG. 3 is a diagram showing a flow of information processing in the partial block length block encryption apparatus according to the first embodiment.
- FIG. 4 is a diagram illustrating a configuration example of the first stirring unit and the second back stirring unit illustrated in FIG. 1 when different from the configuration illustrated in FIG. 3.
- FIG. 5 is a diagram for explaining the encryption function of the block cipher with adjustment value used in the partial block length block encryption apparatus of the first embodiment.
- FIG. 6 is a flowchart showing an operation procedure of the partial block length block encryption apparatus according to the first embodiment.
- FIG. 7 is a block diagram illustrating a configuration example of the partial block length block decoding apparatus according to the second embodiment.
- FIG. 8 is a diagram showing a flow of information processing in the partial block length block decoding apparatus according to the second embodiment.
- FIG. 9 is a diagram for explaining the decryption function of the block cipher with adjustment value used in the partial block length block decryption apparatus of the second embodiment.
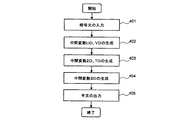
- FIG. 10 is a flowchart showing an operation procedure of the partial block length block decoding apparatus according to the second embodiment.
- FIG. 11 is a diagram illustrating a configuration example of an encryption apparatus related to the double block length block cipher.
- FIG. 12 is a diagram illustrating a configuration example of a related decryption apparatus for double block length block cipher.
- the block encryption device and the decryption device of the present embodiment make it possible to efficiently construct a partial block length block cipher having security exceeding the birthday limit for n using an actual block cipher.
- the block encryption device and the decryption device of the present embodiment are devices related to the partial block length block cipher.
- the block encryption device of the present embodiment is referred to as a “partial block length block encryption device”
- the decryption device of the present embodiment is referred to as a “partial block length block decryption device”.
- FIG. 1 is a block diagram showing a configuration example of a partial block length block encryption apparatus according to this embodiment.
- the partial block length block encryption device 10 of the present exemplary embodiment includes a plaintext input unit 100, a first agitation unit 101, a unit block encryption unit 102 with a first adjustment value, 2 unit block encryption means 103 with adjustment value, second inverse agitation means 104, and ciphertext output means 105.
- the partial block length block encryption apparatus 10 shown in FIG. 1 can be realized by the information processing apparatus 150 shown in FIG. As illustrated in FIG. 2, the information processing apparatus 150 is a type of computer that includes an input unit 151, a control unit 152, and an output unit 153.
- the control unit 152 includes a memory 51 that stores a program, and a CPU (Central Processing Unit) 52 that executes processing according to the program.
- CPU Central Processing Unit
- the reverse stirring means 104 is virtually configured in the information processing apparatus 150.
- the input unit 151 corresponds to the plaintext input unit 100
- the output unit 153 corresponds to the ciphertext output unit 105.
- the memory 51 corresponds to a main storage unit such as a nonvolatile memory and a RAM (Random Access Memory), but a sub storage unit (not shown) having a large-capacity storage area such as a hard disk device is an information processing device. 150 may be provided. If the capacity of the program is too large to fit in the memory 51, the program is stored in the secondary storage unit, and the part in which the contents of the process to be executed next is described according to the progress of the process by the CPU 52. By sequentially reading the program from the storage unit into the memory 51, it is possible to execute even large-capacity program processing.
- FIG. 3 is a diagram showing the flow of information processing in the partial block length block encryption apparatus of the present embodiment.
- the target block size is (n + m) bits (m is 1 or more and less than n), the block size of the block cipher with adjustment value used internally is n bits, and the length of the adjustment value is m bits I will explain it.
- the block cipher with adjustment value refers to block cipher that performs encryption using a parameter called adjustment value (tweak) in addition to the secret key. If the adjustment value and the key are determined, it is a condition that plaintext and ciphertext correspond one-to-one. That is, when there is an encryption function TWENC of a tweakable block cipher and a corresponding decryption function TWDEC, the plaintext M, ciphertext C, key K, and adjustment value T are always expressed by equation (1) Meet.
- Non-Patent Document 6 refers to “M. Liskov, R. Rivest, D. Wagner, Tweakable Block Ciphers, Advances in Cryptology-CRYPTO 2002, 22nd Annual International Cryptology Conference, Santa Barbara, California, USA, August 18-22, 2002. , Proceedings. Lecture Notes in Computer Science 2442 Springer 2002, pp. 31-46.
- the plaintext input means 100 is means for inputting (n + m) bits of plaintext to be encrypted.
- the plaintext input means 100 is a character input device such as a keyboard, for example.
- the plaintext input unit 100 may be an interface device for receiving data from another connected device, or a reading device that reads data from a magnetic recording medium or an optical disk.
- the first stirring means 101 applies a simple keyed substitution mix1 to the input (n + m) bits of plaintext.
- x L and x ′ L are n bits
- x R and x ′ R are m bits.
- SE and SE ′ are n bits
- TE and TE ′ are m bits. In this case, it is necessary to satisfy the following condition (equation (2)) for sufficiently small e for any plaintext pair.
- the probability is defined by the randomness of the key of mix1.
- mix1 uses a method using unbalanced Feistel substitution. This can be done using equations (3) and (4) using a keyed function H with n-bit input and m-bit output.
- + represents a bitwise exclusive OR (XOR) operation.
- H When H satisfies this condition, H is called e-almost XOR universal. This is a kind of universal hash function and can be realized by multiplying an input on a finite field by a key.
- Non-Patent Document 7 refers to “S. Halevi and H. Krawczyk, MMH: Software Message Authentication in the Gbit / second rates, Fast Software Encryption, 4th Internatioanl Workshop, FSE '97, Lecture Notes in Computer.Vol. Feb. 1997 ".
- FIG. 4 shows a configuration when the first stirring means 101 is realized by using the method disclosed herein.
- FIG. 4 shows a case where the stirring means and the back stirring means are realized by Feistel type replacement.
- the unit block encryption unit 102 with the first adjustment value performs an encryption process using the output of the first agitation unit 101.
- the first unit block encryption means 102 with an adjustment value is a block with an adjustment value.
- Equation (6) is obtained.
- TWENC1 (K1, (TE, SE) indicates a process of encrypting an n-bit plaintext SE using the key K1 and m-bit tweak TE.
- represents the concatenation of bits
- the output of Equation (6) is a total of n bits of m bits of UE and (nm) bits of ZE.
- the n-bit SE corresponds to the first intermediate variable
- the m-bit TE corresponds to the second intermediate variable.
- the m-bit UE corresponds to the third intermediate variable
- the (n ⁇ m) -bit ZE corresponds to the fourth intermediate variable.
- the block cipher with adjustment value used in the first unit block encryption means 102 with adjustment value has an m-bit adjustment value and an n-bit block size as shown in the equation (6).
- Non-Patent Document 8 refers to “D. Goldenberg, S. Hohenberger, M. Liskov, E. C. Schwartz, H. Seyalioglu, On Tweaking Luby-Rackoff Blockciphers, Advances in Cryptology-The AIACRYPT2007, TheIACRYPT and Application of Cryptology and Information Security, Kuching, Malaysia, December 2-6, 2007, Proceedings. Lecture Notes in Computer Science 4833 Springer 2007, pp. 342-356.
- n-bit block cipher by using block cipher key renewal that depends on the adjustment value, it is possible to configure without modifying the existing (normal, non-adjustment value) n-bit block cipher algorithm. For example, if there is an encryption function E of a normal block cipher having an n-bit block, L (L is a positive integer greater than or equal to n; for example, 2n) bit key, and an encryption function G of an L-bit block, TWENC1 is Equation (7) can be used.
- E (V, M) is encryption of n-bit plaintext M using L-bit V as a key
- pad (T) is padding m-bit T into L-bit (for example, adding all zeros)
- G (K1, pad (T)) is encryption of L-bit pad (T) with the key K1.
- the TWENC at this time is shown in FIG.
- the encryption function TWENC has an encryption function E of an n-bit block, an L-bit key block cipher, and an encryption function G of an L-bit block for any positive integer L greater than or equal to n.
- the n-bit plaintext is encrypted using the encryption function E as a key.
- TWENC shown in FIG. 5 in the case of the unit block encryption means 102 with the first adjustment value, TWENC shown in FIG. 5 is represented as TWENC1, and the key K shown in FIG. 5 is represented as K1.
- TWENC shown in FIG. 5 is represented as TWENC2
- the key K shown in FIG. 5 is represented as K2.
- E may be a 2-key Triple DES encryption function and G will be an AES encryption function (however, the output will be shortened from 128 bits to 112 bits as appropriate). Is possible.
- G is an AES encryption function
- this TWENC1 the processing of equation (6) becomes equation (8).
- the second unit block encryption means 103 with adjustment value is the m-bit UE output according to the equation (6) and the (n ⁇ m) -bit ZE, And encryption processing using n-bit TE.
- the second unit block encryption means 103 with adjustment value uses the encryption function TWENC2 (m-bit adjustment value, n-bit block) of a certain block encryption with adjustment value to obtain equation (9). .
- n-bit VE corresponds to the fifth intermediate variable.
- the second inverse agitation means 104 performs a process of applying a simple keyed replacement invmix2 to the (n + m) -bit output of the second unit block encryption means 103 with adjustment value. If the input of the second back agitation means 104 is (UE, VE), the output is invmix2 (UE, VE).
- y L and y ′ L are m bits
- y R and y ′ R are n bits.
- mix2 may be a mix of left and right processing of mix1, and invmix2 is uniquely determined by defining mix2.
- invmix2 may be Feistel substitution like mix1.
- the input of invmix2 is (UE, VE) and the output is (y L , y R ), the equation (11) can be obtained.
- the key of the keyed function H used here may be the same as the key of H used by the first stirring means 101 or may be independent.
- FIG. 4 shows a configuration in the case where the second back stirring means 104 is realized using Feistel substitution.
- the ciphertext output means 105 is means for outputting the (n + m) -bit ciphertext (y L , y R ) input from the second back agitation means 104. It can be realized with a display device or a printer.
- FIG. 6 is a flowchart showing the operation procedure of the partial block length block encryption apparatus of this embodiment.
- the first stirring means 101 uses the keyed substitution to stir the plain text (x L , x R ) Variables (SE, TE) are obtained (step 302).
- the unit block encryption means 102 with the first adjustment value encrypts the intermediate variable SE according to the equation (6) using a certain m-bit part of the intermediate variable TE as the adjustment value, and obtains the intermediate variables UE and ZE ( Step 303).
- the second unit block encryption means 103 with an adjustment value encrypts the result of concatenating the intermediate variable ZE and the intermediate variable TE with an m-bit part of the intermediate variable UE as the adjustment value, and sets the intermediate variable VE to Obtain (step 304).
- the second inverse agitation means 104 reversely agitates the intermediate variable (UE, VE) using keyed inverse substitution to generate a ciphertext (y L , y R ), and the ciphertext (y L , y R) ) Is output from the ciphertext output means 105 (step 305).
- FIG. 7 is a block diagram showing an example of the configuration of the partial block length block decoding apparatus of the present embodiment.
- the partial block length block decrypting apparatus 20 of the present embodiment includes a ciphertext input unit 200, a second stirring unit 201, a second unit block decrypting unit 202 with an adjustment value, and a first unit block decrypting with an adjustment value.
- Means 203, first back agitation means 204, and plaintext output means 205 are provided.
- partial block length block decoding device 10 shown in FIG. 7 can be realized by the information processing device 150 shown in FIG. 2, and detailed description thereof will be omitted here.
- FIG. 8 is a diagram showing a flow of information processing in the partial block length block decoding apparatus of the present embodiment.
- the target block size is (n + m) bits (m is 1 or more and less than n), the block size of the block cipher with adjustment value used internally is n bits, and the length of the adjustment value is m bits I will explain it.
- the ciphertext input means 200 is means for inputting (n + m) -bit ciphertext to be decrypted.
- the ciphertext input means 200 is a character input device such as a keyboard, for example.
- the ciphertext input unit 200 may be an interface device or a reading device.
- the second agitation means 201 applies keyed substitution mix2 to the input (n + m) -bit ciphertext.
- the keyed replacement mix2 may be an inverse function of invmix2 in the first embodiment.
- the unit block decoding unit 202 with the second adjustment value is a decoding process using the output of the second stirring unit 201.
- the output of the second stirring means 201 is (UD, VD) (UD is m bits, VD is n bits)
- the second unit block decoding means 202 with adjusted values Using the decryption function TWDEC2 corresponding to the encryption function TWENC2 of the block cipher with adjustment value used by the second unit block encryption means 103 with adjustment value in the embodiment, from (UD, VD), the following equation (12) nm) ZD and m-bit TD are obtained, and (ZD, UD, TD) is output.
- the key K2 of TWDEC2 is the same value as K2 in equation (9).
- the m-bit UD corresponds to the first intermediate variable
- the n-bit VD corresponds to the second intermediate variable
- the (n ⁇ m) -bit ZD corresponds to the third intermediate variable
- the m-bit TD Corresponds to the fourth intermediate variable.
- a decryption function D corresponding to the encryption function E TWDEC2 is defined as equation (13).
- FIG. 9 shows the TWDEC at this time.
- the decryption function TWDEC uses a decryption function D of an n-bit block, an L-bit key block cipher, and an encryption function G of an L-bit block for any positive integer L that is greater than or equal to n.
- the n-bit ciphertext is decrypted using the result obtained by encrypting the m-bit adjustment value with the encryption function G as the key of the decryption function D.
- the TWDEC shown in FIG. 9 is represented as TWDEC1, and the key K shown in FIG. 9 is represented as K1. Further, in the case of the unit block decryption means 202 with the second adjustment value, the TWDEC shown in FIG. 9 is represented as TWDEC2, and the key K shown in FIG. 9 is represented as K2.
- the first unit block decoding unit with adjustment value 203 is a decoding process using the output of the second unit block decoding unit with adjustment value 202.
- the first unit block decryption unit with adjustment value 203 uses the encryption function TWENC1 (m of the block cipher with adjustment value used by the unit block encryption unit with first adjustment value 102 in the first embodiment.
- TWENC1 m of the block cipher with adjustment value used by the unit block encryption unit with first adjustment value 102 in the first embodiment.
- TWDEC1 corresponding to (bit adjustment value, n-bit block)
- SD, TD is output from (UD, ZD, TD) as equation (15).
- TWDEC1 uses block decryption function D having an n-bit block and an L-bit key and encryption function G of an L-bit block as in TWDEC2, and equation (16). It becomes.
- the n-bit SD corresponds to the fifth intermediate variable.
- the first inverse agitation means 204 applies keyed replacement invmix1 to the output of the unit block decryption means 203 with the first adjustment value.
- invmix1 is a reverse substitution of the substitution mix1 used by the first stirring means 101 in the first embodiment.
- the plaintext output means 205 is a means for outputting plaintext (x L , x R ) given from the first back agitation means 204. It can be realized with a display device or a printer.
- FIG. 10 is a flowchart showing an operation procedure of the partial block length block decoding apparatus of the present embodiment.
- the second agitation means 201 agitates the ciphertext (y L , y R ) using keyed replacement. Then, intermediate variables (UD, VD) are obtained (step 402).
- the second unit block decoding means 202 with adjustment value decodes the intermediate variable VD according to the equation (12) using a certain m-bit part of the intermediate variable UD as an adjustment value, and obtains intermediate variables ZD and TD (step) 403).
- the first unit block decoding unit 203 with an adjustment value decodes the result of concatenating the intermediate variable UD and the intermediate variable ZD using an m-bit part of the intermediate variable TD as an adjustment value, and obtains the intermediate variable SD.
- the first intermediate variable inverse mixing means 204 by using the inverse permutation keyed (SD, TD) reverse stirring to plaintext (x L, x R) to generate a plaintext (x L, x R) is Output from the plaintext output means 205 (step 405).
- the block cipher with adjustment value (m bit adjustment value, n bit block) used as a component is theoretically safe, and the number of plaintext / ciphertext pairs used by the attacker is Since it has theoretical safety when it is sufficiently smaller than 2 (n + m) / 2 , it has theoretical resistance against birthday attacks. Therefore, it is possible to efficiently realize a partial block length block cipher that guarantees security exceeding the birthday limit.
- the strength of resistance increases in direct proportion to m.
- the security that exceeds the birthday limit of n is also required for the block cipher with adjustment value itself, but depending on the length of the adjustment value (determined by the required level of security), it can be realized with a normal block cipher.
- a block cipher algorithm with an adjustment value designed from scratch such as Hasty Pudding Cipher described in Non-Patent Document 9, and, as described in Non-Patent Document 8, an intermediate in an ordinary block cipher algorithm.
- An approach to create a block cipher with an adjustment value by adding an adjustment value to a variable has also been proposed, and an algorithm based on these results realizes a block cipher with an adjustment value that has security exceeding the birthday limit of n It is also possible to do.
- Non-patent document 9 is “R. Schroeppel, Specification for the Hasty Pudding Cipher, http://www.cs.arizona.edu/ ⁇ rcs/hpc/hpc-spec.”.
- processing called agitation is necessary at the beginning and at the end, but this can be realized by a universal hash function, which is significantly more than block cipher by optimizing according to the implementation environment. It is possible to operate at high speed.
- the (n + m) bit block cipher which is an example of the present invention described in the above-described embodiment, specifically, can be used as an encryption mode when used for encryption in communication or data storage. That is, information such as a packet to be encrypted is divided into (n + m) bits, and a CBC (Cipher Block Chaining) mode can be applied for communication.
- the encryption of data storage such as a hard disk can be applied by applying the method described in Non-Patent Document 6. Further, it is possible to efficiently encrypt a message having a specific length different from that of a normal block cipher.
- Non-Patent Document 2 using a 64-bit block cipher can guarantee only 32-bit security (that is, security with 2 32 times encryption).
- it is possible to guarantee 48-bit security by combining the 64-bit block cipher and the 128-bit block cipher described above.
- the present invention is not limited to the program of the present invention, and may be a computer-readable recording medium on which the program of the present invention is recorded.
- the program of the present invention can be installed in another information processing apparatus via a recording medium, not limited to the case of transmitting the program of the present invention to another information processing apparatus via a communication line.
- the present invention can be applied to uses such as authentication and encryption in wireless or wired data communication, and uses such as encryption of data on a storage and prevention of tampering.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Storage Device Security (AREA)
Abstract
Description
本実施形態の部分ブロック長ブロック暗号化装置の構成を説明する。図1は本実施形態の部分ブロック長ブロック暗号化装置の一構成例を示すブロック図である。
本実施形態の部分ブロック長ブロック復号装置の構成を説明する。図7は本実施形態の部分ブロック長ブロック復号装置の一構成例を示すブロック図である。
20 部分ブロック長ブロック復号装置
100 平文入力手段
101 第1の撹拌手段
102 第1の調整値付き単位ブロック暗号化手段
103 第2の調整値付き単位ブロック暗号化手段
104 第2の逆撹拌手段
105 暗号文出力手段
200 暗号文入力手段
201 第2の撹拌手段
202 第2の調整値付き単位ブロック復号手段
203 第1の調整値付き単位ブロック復号手段
204 第1の逆撹拌手段
205 平文出力手段
Claims (10)
- nを1以上の整数とし、mを1以上n未満の整数とするとき、暗号化対象の(n+m)ビット平文が入力される平文入力手段と、
前記(n+m)ビット平文に対してユニバーサルハッシュ関数ベースの置換を適用し、nビットの第1の中間変数とmビットの第2の中間変数を生成する攪拌手段と、
mビット調整値付きnビットブロック暗号の暗号化関数を用いて、前記第2の中間変数を調整値として前記第1の中間変数を暗号化し、mビットの第3の中間変数と(n-m)ビットの第4の中間変数を生成する第1の調整値付き単位ブロック暗号化手段と、
前記mビット調整値付きnビットブロック暗号の暗号化関数を用いて、前記第3の中間変数を調整値として、前記第2の中間変数と前記第4の中間変数を連結したnビットの中間変数を暗号化することで、nビットの第5の中間変数を生成する第2の調整値付き単位ブロック暗号化手段と、
前記第3の中間変数と前記第5の中間変数を連結した結果に対してユニバーサルハッシュ関数ベースの逆置換を適用し、(n+m)ビット暗号文を生成する逆攪拌手段と、
前記(n+m)ビット暗号文を出力する暗号文出力手段と、
を有するブロック暗号化装置。 - 請求項1に記載のブロック暗号化装置において、
前記ユニバーサルハッシュ関数ベースの置換および前記ユニバーサルハッシュ関数ベースの逆置換が、nビット入力mビット出力のユニバーサルハッシュ関数をラウンド関数としたFeistel型置換で構成される、ブロック暗号化装置。 - 請求項1または2に記載のブロック暗号化装置において、
前記mビット調整値付きnビットブロック暗号の暗号化関数は、
n以上で任意の正の整数Lについて、nビットブロック、Lビット鍵のブロック暗号の暗号化関数Eと、Lビットブロックの暗号化関数Gを用いて、調整値を該暗号化関数Gで暗号化した結果をさらに該暗号化関数Eの鍵として用いてnビット平文を暗号化するものである、ブロック暗号化装置。 - nを1以上の整数とし、mを1以上n未満の整数とするとき、復号対象の(n+m)ビット暗号文が入力される暗号文入力手段と、
前記(n+m)ビット暗号文に対してユニバーサルハッシュ関数ベースの置換を適用し、mビットの第1の中間変数とnビットの第2の中間変数を生成する攪拌手段と、
mビット調整値付きnビットブロック暗号の復号関数を用いて、前記第1の中間変数を調整値として前記第2の中間変数を復号し、(n-m)ビットの第3の中間変数とmビットの第4の中間変数を生成する第2の調整値付き単位ブロック復号手段と、
前記mビット調整値付きnビットブロック暗号の復号関数を用いて、前記第4の中間変数を調整値として前記第1の中間変数と前記第3の中間変数を連結したnビットの中間変数を復号することで、nビットの第5の中間変数を生成する第1の調整値付き単位ブロック復号手段と、
前記第5の中間変数と前記第4の中間変数を連結した結果に対してユニバーサルハッシュ関数ベースの逆置換を適用し、(n+m)ビット平文を生成する逆攪拌手段と、
前記(n+m)ビット平文を出力する平文出力手段と、
を有する復号装置。 - 請求項4に記載の復号装置において、
前記ユニバーサルハッシュ関数ベースの置換および前記ユニバーサルハッシュ関数ベースの逆置換が、
nビット入力mビット出力のユニバーサルハッシュ関数をラウンド関数としたFeistel型置換で構成される、復号装置。 - 請求項4または5に記載の復号装置において、
前記mビット調整値付きnビットブロック暗号の復号関数は、
n以上で任意の正の整数Lについて、nビットブロック、Lビット鍵のブロック暗号の復号関数Dと、Lビットブロックの暗号化関数Gを用いて、調整値を該暗号化関数Gで暗号化した結果をさらに該復号関数Dの鍵として用いてnビット暗号文を復号するものである、復号装置。 - nを1以上の整数とし、mを1以上n未満の整数とするとき、(n+m)ビット平文から暗号文を生成するための暗号化方法であって、
前記(n+m)ビット平文に対してユニバーサルハッシュ関数ベースの置換を適用し、nビットの第1の中間変数とmビットの第2の中間変数を生成し、
mビット調整値付きnビットブロック暗号の暗号化関数を用いて、前記第2の中間変数を調整値として前記第1の中間変数を暗号化し、mビットの第3の中間変数と(n-m)ビットの第4の中間変数を生成し、
前記mビット調整値付きnビットブロック暗号の暗号化関数を用いて、前記第3の中間変数を調整値として、前記第2の中間変数と前記第4の中間変数を連結したnビットの中間変数を暗号化することで、nビットの第5の中間変数を生成し、
前記第3の中間変数と前記第5の中間変数を連結した結果に対してユニバーサルハッシュ関数ベースの逆置換を適用し、(n+m)ビット暗号文を生成し、
前記(n+m)ビット暗号文を出力する、暗号化方法。 - nを1以上の整数とし、mを1以上n未満の整数とするとき、(n+m)ビット暗号文から平文を生成するための復号方法であって、
前記(n+m)ビット暗号文に対してユニバーサルハッシュ関数ベースの置換を適用し、mビットの第1の中間変数とnビットの第2の中間変数を生成し、
mビット調整値付きnビットブロック暗号の復号関数を用いて、前記第1の中間変数を調整値として前記第2の中間変数を復号し、(n-m)ビットの第3の中間変数とmビットの第4の中間変数を生成し、
前記mビット調整値付きnビットブロック暗号の復号関数を用いて、前記第4の中間変数を調整値として前記第1の中間変数と前記第3の中間変数を連結したnビットの中間変数を復号することで、nビットの第5の中間変数を生成し、
前記第5の中間変数と前記第4の中間変数を連結した結果に対してユニバーサルハッシュ関数ベースの逆置換を適用し、(n+m)ビット平文を生成し、
前記(n+m)ビット平文を出力する、復号方法。 - nを1以上の整数とし、mを1以上n未満の整数とするとき、(n+m)ビット平文から暗号文をコンピュータに生成させるためのプログラムを記録したコンピュータ読み取り可能な記録媒体であって、
前記(n+m)ビット平文に対してユニバーサルハッシュ関数ベースの置換を適用し、nビットの第1の中間変数とmビットの第2の中間変数を生成し、
mビット調整値付きnビットブロック暗号の暗号化関数を用いて、前記第2の中間変数を調整値として前記第1の中間変数を暗号化し、mビットの第3の中間変数と(n-m)ビットの第4の中間変数を生成し、
前記mビット調整値付きnビットブロック暗号の暗号化関数を用いて、前記第3の中間変数を調整値として、前記第2の中間変数と前記第4の中間変数を連結したnビットの中間変数を暗号化することで、nビットの第5の中間変数を生成し、
前記第3の中間変数と前記第5の中間変数を連結した結果に対してユニバーサルハッシュ関数ベースの逆置換を適用し、(n+m)ビット暗号文を生成し、
前記(n+m)ビット暗号文を出力する処理を前記コンピュータに実行させるためのプログラムを記録したコンピュータ読み取り可能な記録媒体。 - nを1以上の整数とし、mを1以上n未満の整数とするとき、(n+m)ビット暗号文から平文をコンピュータに生成させるためのプログラムを記録したコンピュータ読み取り可能な記録媒体であって、
前記(n+m)ビット暗号文に対してユニバーサルハッシュ関数ベースの置換を適用し、mビットの第1の中間変数とnビットの第2の中間変数を生成し、
mビット調整値付きnビットブロック暗号の復号関数を用いて、前記第1の中間変数を調整値として前記第2の中間変数を復号し、(n-m)ビットの第3の中間変数とmビットの第4の中間変数を生成し、
前記mビット調整値付きnビットブロック暗号の復号関数を用いて、前記第4の中間変数を調整値として前記第1の中間変数と前記第3の中間変数を連結したnビットの中間変数を復号することで、nビットの第5の中間変数を生成し、
前記第5の中間変数と前記第4の中間変数を連結した結果に対してユニバーサルハッシュ関数ベースの逆置換を適用し、(n+m)ビット平文を生成し、
前記(n+m)ビット平文を出力する処理を前記コンピュータに実行させるためのプログラムを記録したコンピュータ読み取り可能な記録媒体。
Priority Applications (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP2012555798A JP5365750B2 (ja) | 2011-01-31 | 2012-01-23 | ブロック暗号化装置、復号装置、暗号化方法、復号方法およびプログラム |
| US13/982,690 US8891761B2 (en) | 2011-01-31 | 2012-01-23 | Block encryption device, decryption device, encrypting method, decrypting method and program |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP2011-018359 | 2011-01-31 | ||
| JP2011018359 | 2011-01-31 |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2012105352A1 true WO2012105352A1 (ja) | 2012-08-09 |
Family
ID=46602571
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/JP2012/051326 WO2012105352A1 (ja) | 2011-01-31 | 2012-01-23 | ブロック暗号化装置、復号装置、暗号化方法、復号方法およびプログラム |
Country Status (3)
| Country | Link |
|---|---|
| US (1) | US8891761B2 (ja) |
| JP (1) | JP5365750B2 (ja) |
| WO (1) | WO2012105352A1 (ja) |
Families Citing this family (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9571270B2 (en) | 2013-11-29 | 2017-02-14 | Portland State University | Construction and uses of variable-input-length tweakable ciphers |
| KR101519777B1 (ko) * | 2014-01-29 | 2015-05-12 | 현대자동차주식회사 | 차량 네트워크 내의 제어기간의 데이터 송신 방법 및 수신 방법 |
| US9946662B2 (en) * | 2014-08-29 | 2018-04-17 | The Boeing Company | Double-mix Feistel network for key generation or encryption |
| US10346318B2 (en) * | 2016-09-13 | 2019-07-09 | Intel Corporation | Multi-stage memory integrity method and apparatus |
| WO2018154623A1 (ja) * | 2017-02-21 | 2018-08-30 | 三菱電機株式会社 | 暗号化装置及び復号装置 |
Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2007034212A (ja) * | 2005-07-29 | 2007-02-08 | Nippon Telegr & Teleph Corp <Ntt> | ブロック暗号装置、ブロック復号装置、それらの方法及びプログラム |
| WO2009020060A1 (ja) * | 2007-08-06 | 2009-02-12 | Nec Corporation | 共通鍵ブロック暗号化装置、共通鍵ブロック暗号化方法及びプログラム |
| WO2010024004A1 (ja) * | 2008-08-29 | 2010-03-04 | 日本電気株式会社 | 調整値付きブロック暗号化装置、調整値付きブロック暗号化方法及び調整値付きブロック暗号化プログラム並びに調整値付きブロック復号装置、調整値付きブロック復号方法及び調整値付きブロック復号プログラム |
| WO2010024003A1 (ja) * | 2008-08-29 | 2010-03-04 | 日本電気株式会社 | 倍ブロック長ブロック暗号化装置、復号装置、暗号化方法及び復号方法、及びそのプログラム |
Family Cites Families (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2002175008A (ja) | 2000-09-27 | 2002-06-21 | Nec Soft Ltd | 暗号化方法、暗号化器、暗号化及び復号化システム |
| JP2002108205A (ja) | 2000-09-28 | 2002-04-10 | Hitachi Software Eng Co Ltd | ブロック暗号方法及び復号方法 |
| US7200227B2 (en) * | 2001-07-30 | 2007-04-03 | Phillip Rogaway | Method and apparatus for facilitating efficient authenticated encryption |
| US7418100B2 (en) * | 2004-10-20 | 2008-08-26 | Cisco Technology, Inc. | Enciphering method |
| WO2008018303A1 (fr) | 2006-08-10 | 2008-02-14 | Nec Corporation | Dispositif de chiffrage de bloc équipé d'une fonction d'ajustement, procédé et programme |
| JP5141558B2 (ja) | 2006-10-30 | 2013-02-13 | 日本電気株式会社 | 共通鍵ブロック暗号化装置、その方法、そのプログラム、及び記録媒体 |
| US8107620B2 (en) | 2007-03-21 | 2012-01-31 | International Business Machines Corporation | Simple and efficient one-pass authenticated encryption scheme |
| JP5038866B2 (ja) | 2007-11-27 | 2012-10-03 | 日本電信電話株式会社 | 暗号通信方法、暗号化装置、復号装置、及びそれらのプログラム |
| US8526605B2 (en) * | 2009-10-09 | 2013-09-03 | Seagate Technology Llc | Data encryption to provide data security and memory cell bit wear leveling |
-
2012
- 2012-01-23 JP JP2012555798A patent/JP5365750B2/ja active Active
- 2012-01-23 WO PCT/JP2012/051326 patent/WO2012105352A1/ja active Application Filing
- 2012-01-23 US US13/982,690 patent/US8891761B2/en active Active
Patent Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2007034212A (ja) * | 2005-07-29 | 2007-02-08 | Nippon Telegr & Teleph Corp <Ntt> | ブロック暗号装置、ブロック復号装置、それらの方法及びプログラム |
| WO2009020060A1 (ja) * | 2007-08-06 | 2009-02-12 | Nec Corporation | 共通鍵ブロック暗号化装置、共通鍵ブロック暗号化方法及びプログラム |
| WO2010024004A1 (ja) * | 2008-08-29 | 2010-03-04 | 日本電気株式会社 | 調整値付きブロック暗号化装置、調整値付きブロック暗号化方法及び調整値付きブロック暗号化プログラム並びに調整値付きブロック復号装置、調整値付きブロック復号方法及び調整値付きブロック復号プログラム |
| WO2010024003A1 (ja) * | 2008-08-29 | 2010-03-04 | 日本電気株式会社 | 倍ブロック長ブロック暗号化装置、復号装置、暗号化方法及び復号方法、及びそのプログラム |
Also Published As
| Publication number | Publication date |
|---|---|
| JP5365750B2 (ja) | 2013-12-11 |
| US8891761B2 (en) | 2014-11-18 |
| JPWO2012105352A1 (ja) | 2014-07-03 |
| US20130308775A1 (en) | 2013-11-21 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| JP5402632B2 (ja) | 共通鍵ブロック暗号化装置、共通鍵ブロック暗号化方法及びプログラム | |
| WO2015015702A1 (ja) | 認証暗号装置、認証暗号方法および認証暗号用プログラム | |
| JP2010140026A (ja) | 連鎖暗号モードのための方法および装置 | |
| WO2012132623A1 (ja) | 暗号処理装置、および暗号処理方法、並びにプログラム | |
| JPH0863097A (ja) | データを暗号化するための対称暗号化方法およびシステム | |
| US9800406B2 (en) | Technologies for modifying a first cryptographic cipher with operations of a second cryptographic cipher | |
| WO2011105367A1 (ja) | ブロック暗号化装置、ブロック復号装置、ブロック暗号化方法、ブロック復号方法及びプログラム | |
| JP7031580B2 (ja) | 暗号化装置、暗号化方法、復号化装置、及び復号化方法 | |
| WO2010024003A1 (ja) | 倍ブロック長ブロック暗号化装置、復号装置、暗号化方法及び復号方法、及びそのプログラム | |
| JPWO2008053650A1 (ja) | 共通鍵ブロック暗号化装置、その方法、そのプログラム、及び記録媒体 | |
| JP5365750B2 (ja) | ブロック暗号化装置、復号装置、暗号化方法、復号方法およびプログラム | |
| US8526602B2 (en) | Adjustment-value-attached block cipher apparatus, cipher generation method and recording medium | |
| Reyad et al. | Key-based enhancement of data encryption standard for text security | |
| Dewangan et al. | Study of avalanche effect in AES using binary codes | |
| JP5333450B2 (ja) | 調整値付きブロック暗号化装置、方法及びプログラム並びに復号装置、方法及びプログラム | |
| CN109714154B (zh) | 一种代码体积困难白盒安全模型下的白盒密码算法的实现方法 | |
| Rawal | Advanced encryption standard (AES) and it’s working | |
| Sousi et al. | Aes encryption: Study & evaluation | |
| Singh et al. | An ordeal random data encryption scheme (ORDES) | |
| Nema et al. | Critical analysis of various symmetric key cryptographic algorithms | |
| Azzawi | Enhancing the encryption process of advanced encryption standard (AES) by using proposed algorithm to generate S-Box | |
| Salman | New method for encryption using mixing advanced encryption standard and blowfish algorithms | |
| JP5293612B2 (ja) | 暗号化装置、復号装置、暗号化方法、復号方法およびプログラム | |
| Mahmoud et al. | Improved Rijndael Algorithm by Encryption S-Box Using NTRU Algorithm | |
| Kangude et al. | Advanced Encryption Standard |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 12742145 Country of ref document: EP Kind code of ref document: A1 |
|
| ENP | Entry into the national phase |
Ref document number: 2012555798 Country of ref document: JP Kind code of ref document: A |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 13982690 Country of ref document: US |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| 122 | Ep: pct application non-entry in european phase |
Ref document number: 12742145 Country of ref document: EP Kind code of ref document: A1 |