EP3688949B1 - Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil - Google Patents
Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil Download PDFInfo
- Publication number
- EP3688949B1 EP3688949B1 EP18720674.3A EP18720674A EP3688949B1 EP 3688949 B1 EP3688949 B1 EP 3688949B1 EP 18720674 A EP18720674 A EP 18720674A EP 3688949 B1 EP3688949 B1 EP 3688949B1
- Authority
- EP
- European Patent Office
- Prior art keywords
- base station
- network
- handover
- rat
- type
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
- 238000004891 communication Methods 0.000 title claims description 161
- 238000009795 derivation Methods 0.000 title claims description 79
- 230000006870 function Effects 0.000 claims description 86
- 238000000034 method Methods 0.000 claims description 84
- 230000015654 memory Effects 0.000 claims description 61
- 238000005516 engineering process Methods 0.000 claims description 54
- 238000004590 computer program Methods 0.000 claims description 29
- 230000007774 longterm Effects 0.000 claims description 16
- 230000011664 signaling Effects 0.000 claims description 14
- 230000002730 additional effect Effects 0.000 claims description 2
- 230000001419 dependent effect Effects 0.000 claims 5
- 238000012545 processing Methods 0.000 description 119
- 210000004027 cell Anatomy 0.000 description 60
- 238000010586 diagram Methods 0.000 description 40
- 238000003860 storage Methods 0.000 description 32
- 238000013146 percutaneous coronary intervention Methods 0.000 description 20
- 230000008901 benefit Effects 0.000 description 19
- 230000005540 biological transmission Effects 0.000 description 18
- 230000003287 optical effect Effects 0.000 description 12
- 238000002360 preparation method Methods 0.000 description 12
- 238000007726 management method Methods 0.000 description 11
- 238000005259 measurement Methods 0.000 description 10
- 238000003491 array Methods 0.000 description 6
- 230000008859 change Effects 0.000 description 6
- 230000007246 mechanism Effects 0.000 description 6
- 230000001413 cellular effect Effects 0.000 description 5
- 230000003993 interaction Effects 0.000 description 5
- 238000012544 monitoring process Methods 0.000 description 4
- 230000006855 networking Effects 0.000 description 4
- 230000008569 process Effects 0.000 description 4
- 230000004044 response Effects 0.000 description 4
- 238000012546 transfer Methods 0.000 description 4
- 230000005611 electricity Effects 0.000 description 3
- 230000002085 persistent effect Effects 0.000 description 3
- 230000009471 action Effects 0.000 description 2
- 230000006399 behavior Effects 0.000 description 2
- 210000004271 bone marrow stromal cell Anatomy 0.000 description 2
- 238000004422 calculation algorithm Methods 0.000 description 2
- 230000023402 cell communication Effects 0.000 description 2
- 230000000295 complement effect Effects 0.000 description 2
- 238000012423 maintenance Methods 0.000 description 2
- 238000010295 mobile communication Methods 0.000 description 2
- 230000004048 modification Effects 0.000 description 2
- 238000012986 modification Methods 0.000 description 2
- 238000012360 testing method Methods 0.000 description 2
- 235000008694 Humulus lupulus Nutrition 0.000 description 1
- 241001481798 Stochomys longicaudatus Species 0.000 description 1
- 230000001133 acceleration Effects 0.000 description 1
- 230000004913 activation Effects 0.000 description 1
- 239000000654 additive Substances 0.000 description 1
- 230000000996 additive effect Effects 0.000 description 1
- 230000002776 aggregation Effects 0.000 description 1
- 238000004220 aggregation Methods 0.000 description 1
- 238000004458 analytical method Methods 0.000 description 1
- 230000009286 beneficial effect Effects 0.000 description 1
- 238000004364 calculation method Methods 0.000 description 1
- 230000010267 cellular communication Effects 0.000 description 1
- 238000007596 consolidation process Methods 0.000 description 1
- 239000013256 coordination polymer Substances 0.000 description 1
- 125000004122 cyclic group Chemical group 0.000 description 1
- 238000013500 data storage Methods 0.000 description 1
- 230000000694 effects Effects 0.000 description 1
- 210000004247 hand Anatomy 0.000 description 1
- RGNPBRKPHBKNKX-UHFFFAOYSA-N hexaflumuron Chemical compound C1=C(Cl)C(OC(F)(F)C(F)F)=C(Cl)C=C1NC(=O)NC(=O)C1=C(F)C=CC=C1F RGNPBRKPHBKNKX-UHFFFAOYSA-N 0.000 description 1
- 230000006872 improvement Effects 0.000 description 1
- 230000010354 integration Effects 0.000 description 1
- 238000004519 manufacturing process Methods 0.000 description 1
- 238000013507 mapping Methods 0.000 description 1
- 239000011159 matrix material Substances 0.000 description 1
- 239000002184 metal Substances 0.000 description 1
- 238000005457 optimization Methods 0.000 description 1
- 238000011176 pooling Methods 0.000 description 1
- 230000008439 repair process Effects 0.000 description 1
- 230000008672 reprogramming Effects 0.000 description 1
- 238000012827 research and development Methods 0.000 description 1
- 230000000717 retained effect Effects 0.000 description 1
- 239000000779 smoke Substances 0.000 description 1
- 239000007787 solid Substances 0.000 description 1
- 230000001360 synchronised effect Effects 0.000 description 1
- 210000003813 thumb Anatomy 0.000 description 1
- 230000007704 transition Effects 0.000 description 1
- 230000001960 triggered effect Effects 0.000 description 1
- CSRZQMIRAZTJOY-UHFFFAOYSA-N trimethylsilyl iodide Substances C[Si](C)(C)I CSRZQMIRAZTJOY-UHFFFAOYSA-N 0.000 description 1
- 230000000007 visual effect Effects 0.000 description 1
- 230000003245 working effect Effects 0.000 description 1
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/04—Key management, e.g. using generic bootstrapping architecture [GBA]
- H04W12/041—Key generation or derivation
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/04—Key management, e.g. using generic bootstrapping architecture [GBA]
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/06—Network architectures or network communication protocols for network security for supporting key management in a packet data network
- H04L63/061—Network architectures or network communication protocols for network security for supporting key management in a packet data network for key exchange, e.g. in peer-to-peer networks
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0861—Generation of secret information including derivation or calculation of cryptographic keys or passwords
- H04L9/0866—Generation of secret information including derivation or calculation of cryptographic keys or passwords involving user or device identifiers, e.g. serial number, physical or biometrical information, DNA, hand-signature or measurable physical characteristics
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W36/00—Hand-off or reselection arrangements
- H04W36/0005—Control or signalling for completing the hand-off
- H04W36/0011—Control or signalling for completing the hand-off for data sessions of end-to-end connection
- H04W36/0033—Control or signalling for completing the hand-off for data sessions of end-to-end connection with transfer of context information
- H04W36/0038—Control or signalling for completing the hand-off for data sessions of end-to-end connection with transfer of context information of security context information
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W36/00—Hand-off or reselection arrangements
- H04W36/14—Reselecting a network or an air interface
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W8/00—Network data management
- H04W8/02—Processing of mobility data, e.g. registration information at HLR [Home Location Register] or VLR [Visitor Location Register]; Transfer of mobility data, e.g. between HLR, VLR or external networks
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L2209/00—Additional information or applications relating to cryptographic mechanisms or cryptographic arrangements for secret or secure communication H04L9/00
- H04L2209/80—Wireless
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/06—Network architectures or network communication protocols for network security for supporting key management in a packet data network
- H04L63/062—Network architectures or network communication protocols for network security for supporting key management in a packet data network for key distribution, e.g. centrally by trusted party
Definitions
- the proposed technology generally relates to wireless communication technology, and more specifically to managing security contexts and performing key derivation at handover in a wireless communication system.
- LTE Long Term Evolution
- NR New Radio
- the 3GPP TS 23.501 describes the 5G network architecture.
- a stripped down simplified version of 5G network is shown in FIG. 1 .
- the UE User Equipment
- the radio access network (RAN) function or base station denoted as RAN node is responsible for providing wireless radio communication to the UE and connecting the UE to the core network.
- the core network function called AMF (Access and Mobility Management Function) is responsible for handling the mobility of the UE, among other responsibilities.
- AMF Access and Mobility Management Function
- UPF User Plane Function
- UPF User Plane Function
- the UE interacts with the RAN node over-the-air using radio interface.
- the RAN node in turn interacts with the AMF using the interface called N2.
- the RAN node interacts with the UPF using the interface called N3.
- the RAN nodes themselves interact with each other using the Xn interface.
- the 5G system defined by 3GPP includes both a new radio access network (NG-RAN) and new core network (5G-CN).
- NG-RAN new radio access network
- 5G-CN new core network
- the NG-RAN uses a flat architecture and includes base stations, called gNBs (Next Generation Node Bs), which are inter-connected via the Xn-interface and towards the core network by the N2/N3-interface.
- gNBs Next Generation Node Bs
- a smallest coverage area in which the gNB serves the UEs is called a cell.
- the gNB supports one or more cells which provides the radio access to the UE.
- the radio access technology (called next radio, NR) is OFDM (Orthogonal Frequency Division Multiplexing) based like in LTE and offers high data transfer speeds and low latency.
- NR will be rolled out gradually on top of the legacy LTE network starting in areas where high data traffic is expected. This means that NR coverage will be limited in the beginning and users must move between NR and LTE as they go in out of coverage.
- LTE base stations called eNBs (E-UTRAN Node Bs or Evolved Node Bs) will also connect to the 5G-CN and support the Xn interface.
- An eNB connected to 5GC is called a next generation eNB (ng-eNB) and is considered part of the NG-RAN (see FIG. 2 ).
- ng-eNB next generation eNB
- NAS non-access stratum
- access stratum access stratum
- NAS security and AS security security of communication
- K AMF base security key on which the NAS security is based. From this K AMF , further key derivations result in other keys that are used to provide confidentiality and integrity protection of NAS messages (mostly control plane).
- the K AMF is also used to derive another base key (AS-base key) on which the AS security is based on, denoted as K gNB , irrespective of whether the RAN node is a gNB or an ng-eNB. From this K gNB , further key derivations result in other keys that are used to provide confidentiality and integrity protection of AS messages (both control plane and user plane).
- the 3GPP specifications TS 38.300, TS 23.502, TS 38.413, and TS 38.423 describe various aspects of the handover procedures in the 5G system. Mind that the 5G specification is work in progress and whenever the specification is missing some information, it will be assumed to work with similarity to the LTE system.
- the source cell When the UE move from one cell to another cell while having active radio connection, i.e., while in RRC_CONNECTED mode, the source cell prepares and hands over the information related to the UE to the target cell so that the target cell can start serving the UE.
- This handing over mechanism is intuitively called a handover procedure.
- the handover procedure provides mobility support for UEs that are moving from one cell to another cell.
- there are 3 types of handover as follow illustrated in FIG. 3 ):
- a handover in 5G is likely to include three phases: handover preparation, handover execution, and handover completion.
- the Xn-handover is the default procedure and is used when there is an Xn interface between the source and target node. If there is no Xn interface or if the handover preparation fails, then N2-handover is initiated.
- the UE behavior is likely to be unified regardless if a handover is of type intra-cell, Xn, or N2. In other words, the UE should have to neither identify the type of handover nor behave differently for different type of handover. That means, on the UE side, the handling of the target node is expected to be similar regardless of the type of handover.
- 5G (and similar future generations) is a very special generation of mobile networks because it is the first time when a core network of one mobile generation supports radio access technologies belonging to multiple mobile generations.
- the 5G-CN supports NG-RAN and NG-RAN includes both gNB (NR type belonging to 5G) and ng-eNB (E-UTRA/LTE type belonging to 4G).
- the handovers in 5G can therefore be between two gNBs, between two ng-eNBs, and between gNB and ng-eNB. Therefore, it is challenging to have a simple and preferably harmonized way of key derivations in handovers while still maintaining desired security properties.
- handovers when the UE remains within the same core network are known as intra system handovers. This term is used regardless if the handover involves a change of RAT or not.
- Another object is to provide a wireless device comprising such a device.
- Yet another object is to provide a network node comprising such a device.
- Still another object is to provide a network device comprising such a device.
- Another object is to provide an apparatus for determining a security context for communication between a wireless device and a target network node at handover.
- a method for determining a security context for communication between a wireless device and a target network node at handover comprises:
- a device configured to determine a security context for communication between a wireless device and a target network node at handover.
- the device is configured to obtain information representative of the type of Radio Access Technology, also referred to as RAT type, of the target network node.
- the device is further configured to derive and/or determine the security context at least partly based on the information representative of the RAT type.
- a wireless communication device comprising a device according to the second aspect.
- a network node comprising a device according to the second aspect.
- a network device comprising a device according to the second aspect.
- a computer program for determining, when executed, a security context for communication between a wireless device and a target network node at handover.
- the computer program comprises instructions, which when executed by at least one processor, cause the at least one processor to:
- a computer-program product comprising a computer-readable medium having stored thereon such a computer program.
- an apparatus for determining a security context for communication between a wireless device and a target network node at handover comprises:
- a wireless device for secure communication between a wireless device and a target network node at handover, wherein the method comprises:
- a device configured for secure communication between a wireless device and a target network node at handover
- Another object is to provide a method performed by a wireless device for determining a security context for communication between the wireless device and a target network node at handover from a source network node to the target network node.
- Yet another object is to provide a method performed by a network node for determining a security context for communication between a wireless device and a target network node at handover from a source network node to the target network node.
- Still another object is to provide a wireless device and/or user equipment.
- It is also an object is to provide a network node such as a base station.
- Another object is to provide different embodiments of a communication system including a host computer, as well as corresponding methods implemented in such a communication system.
- wireless communication device may refer to a mobile phone, a cellular phone, a Personal Digital Assistant (PDA), equipped with radio communication capabilities, a smart phone, a laptop or Personal Computer (PC), equipped with an internal or external mobile broadband modem, a tablet with radio communication capabilities, a target device, a device to device UE, a machine type UE or UE capable of machine to machine communication, Customer Premises Equipment (CPE), Laptop Embedded Equipment (LEE), Laptop Mounted Equipment (LME), USB dongle, a portable electronic radio communication device, a sensor device equipped with radio communication capabilities or the like.
- PDA Personal Digital Assistant
- PC Personal Computer
- CPE Customer Premises Equipment
- LEE Laptop Embedded Equipment
- LME Laptop Mounted Equipment
- USB dongle a portable electronic radio communication device, a sensor device equipped with radio communication capabilities or the like.
- wireless communication device should be interpreted as non-limiting terms comprising any type of wireless device communicating with a network node in a wireless communication system and/or possibly communicating directly with another wireless communication device.
- a wireless communication device may be any device equipped with circuitry for wireless communication according to any relevant standard for communication.
- network node may refer to base stations, access points, network control nodes such as network controllers, radio network controllers, base station controllers, access controllers, and the like.
- base station may encompass different types of radio base stations including standardized base station functions such as Node Bs, or evolved Node Bs (eNBs), gNBs and/or ng-eNBs, and also macro/micro/pico radio base stations, home base stations, also known as femto base stations, relay nodes, repeaters, radio access points, Base Transceiver Stations (BTSs), and even radio control nodes controlling one or more Remote Radio Units (RRUs), or the like.
- eNBs evolved Node Bs
- gNBs evolved Node Bs
- ng-eNBs gNode Bs
- macro/micro/pico radio base stations home base stations, also known as femto base stations, relay nodes, repeaters, radio access points, Base Transceiver Stations (BTSs), and even radio control nodes
- network device may refer to any device located in connection with a communication network, including but not limited to devices in access networks, core networks and similar network structures.
- the term network device may also encompass cloud-based network devices.
- FIG. 4 shows a simplified message flow during an Xn-handover.
- An N2-handover also arguably works in a similar way with the change that the source and target RAN node communicate indirectly via the AMF instead.
- the Xn-handover we will keep our explanation to the Xn-handover.
- the control plane (called RRC for Radio Resource Control) and the user plane traffic is integrity and confidentiality protected between UE and gNB/ng-eNB based on a shared key, the AS-base key, denoted the K gNB .
- RRC Radio Resource Control
- K gNB the AS-base key
- 5G will likely allow the AS-base key to be retained at certain handovers when the security termination point of the source RAN node/cell and target RAN node/cell do not change. For our purpose, we ignore that situation because it is not being super relevant. Changing AS-base key is important for security as it prevents the same key to be used more than once and provides compartmentalization between RAN nodes (i.e., a compromise of one RAN node should not affect the security of another RAN node).
- FIG. 5 shows the key handling in handover in LTE as described in the Clause 7.2.8.1.1 of the 3GPP TS 33.401. It is likely that 5G will also adopt the similar mechanism.
- the K ASME is analogous to the K AMF , i.e., it is the NAS-base key and the K eNB is analogous to the K gNB , i.e., it is the AS-base key.
- the NH and K eNB* are intermediary keys which will be described later.
- K eNB* will be analogous to K gNB* .
- Each K eNB is associated with a NCC value, which will also be described later.
- the derivation of the K eNB * from the K eNB is called horizontal key derivation, which is used during X2-handovers (analogous to Xn-handovers) as a part of handover preparation phase.
- the horizontally derived K eNB * is taken into use for the ongoing handover.
- the derivation of the K eNB * from the NH is called vertical key derivation, which is used during both X2-handover (analogous to Xn-handover) and S1-handover (analogous to N2-handover).
- the vertically derived K eNB * is taken into use for the ongoing handover.
- the vertically derived K eNB * is not taken into use for the ongoing handover, instead it is used for the next handover.
- K gNB* the new AS-base key
- K gNB * the new AS-base key
- NH Next Hop
- the latter is a security key computed by the AMF (and locally by the UE) from the K AMF security key and is provided to the RAN node during handover completion as a part of user plane path switch.
- the vertical key derivation can only be used if the source RAN node has acted as target RAN node in an earlier Xn-handover and hence has received a fresh NH from the AMF. Otherwise, if no NH is available or if the NH has already been used, the horizontal key derivation is used to derive the new AS-base key, i.e., K gNB* .
- the AMF provides the target RAN node with a fresh NH in the handover preparation phase and the target RAN node computes the K gNB* using vertical key derivation.
- the handover behavior looks identical regardless if it is of type Xn or N2.
- the UE looks at the NH Chaining Counter (NCC) which the target RAN node includes in the RRC handover command.
- NCC NH Chaining Counter
- the NCC counts the number of vertical key derivations that has been performed and directly corresponds to a NH key. If the UE receives a NCC value which is unchanged, K gNB* is derived using horizontal key derivation from the current K gNB . Otherwise, if the NCC is incremented, the UE computes the corresponding NH key and derives K gNB* using vertical key derivation.
- the benefit of using vertical key derivation is that it provides forward security (i.e., a source RAN node is unable to decrypt or modify traffic in subsequent RAN nodes).
- forward security i.e., a source RAN node is unable to decrypt or modify traffic in subsequent RAN nodes.
- ⁇ NCC NH ⁇ pair is provided by the AMF to the target node as a part of user plane path switch
- forward security is achieved only after another handover from the target node (i.e. after two hops).
- the N2 handover forward security is achieved already after one hop since the AMF provides the NH in the handover preparation phase.
- K eNB* key derivation In LTE, both during horizontal and vertical key derivation, besides the current AS-base key or NH key, the following inputs are used in K eNB* key derivation:
- K eNB* is analogous to the K gNB* .
- the advantage of using the PCI and DL-EARFCN as input to the K eNB* key derivation is that different K eNB* keys are generated for different target cells, which also means different K eNB* keys are generated for different RAN nodes, enabling the preparation of multiple RAN nodes, e.g., at handover where each target RAN nodes get their own set of K eNB* keys. This enables the source RAN cell to at the last moment select which candidate target cell or RAN node to use for handover.
- the PCI and DL-EARFCN are also parameters the UE knows about when entering the target cell.
- K gNB ./ K gNB* is used to denote the AS base key in both a gNB and an ng-eNB. It would have been more accurate to use separate terms (e.g. K gNB ./ K gNB* and K ng-eNB ./ K ng-eNB* ), but for the sake of simplicity and brevity only a single term is used. It should be understood that the AS base security key may be given different names in the future, even generic names such as K AN *, where AN stands for Access Network.
- RRC_INACTIVE the UE context from the previous RRC connection is stored in the RAN and is re-used at the next RRC connection setup.
- the UE context could include information on the UE security configuration, configured data radio bearer etc.
- RRC_INACTIVE With RRC_INACTIVE the RRC connection can be suspended in one cell and later on resumed in another cell.
- RRC_INACTIVE When an RRC connection is resumed the UE transitions from RRC_INACTIVE to RRC_CONNECTED and the UE context is transferred from the source RAN node to the target RAN node.
- a new AS-base key is also derived for the target cell by the source node and transferred to the target node together with the UE context. It is also possible for the source RAN node to prepare multiple target RAN nodes/cells in advance to speed up the connection resumption when the UE becomes active.
- the transfer of the UE context and key handling for RRC_INACTIVE is in many ways similar to an Xn-handover.
- 5G (and similar future generations) is a very special generation of mobile networks because it is the first time when a core network of one mobile generation supports radio access technologies belonging to multiple mobile generations.
- the 5G core network supports NG-RAN and NG-RAN includes both gNB (NR type belonging to 5G) and ng-eNB (E-UTRA/LTE type belonging to 4G).
- the handovers in 5G can therefore be between two gNBs, between two ng-eNBs, and between gNB and ng-eNB. Therefore, it is challenging to have a simple and preferably harmonized way of key derivations in handovers while still maintaining desired security properties.
- a method for determining a security context for communication between a wireless device and a target network node at handover as schematically illustrated in FIG. 6A .
- the method comprises:
- the security context may for example be used for and/or include the optional step S3 of protecting communication between the wireless device and the target network node based on the security context, e.g. see FIG. 6B .
- Examples include providing integrity and/or confidentiality protection for transmission and/or reception of user data and/or control data between the wireless device and the target network node.
- the RRC Handover Complete message (in the handover execution phase) between the wireless device and the target network node may be protected using a security key of the derived security context.
- the communication may be protected by providing integrity and/or confidentiality protection for transmission and/or reception of user data and/or control data between the wireless device and the target network node.
- the invention may be applied at intra-RAT and/or inter-RAT handovers.
- the proposed technology may be particularly useful at so called intra-system handovers, i.e. intra-RAT or inter-RAT handovers within the same core network (without a change of core network).
- the security context may be derived by taking the determined RAT type into account in the key derivation, as schematically illustrated in FIG. 7 .
- the security context may comprise at least a security key.
- the security key may be an Access Stratum (AS) base security key such as an AS base security key for protecting integrity and/or confidentiality of the communication between the wireless device and the target network node.
- AS Access Stratum
- the base security key may be K gNB* or K ng-eNB* .
- the information representative of the RAT type may for example be obtained by receiving the information and/or by determining the information.
- the information representative of the RAT type may be used together with information representative of a security key valid before handover to derive a new security key.
- the information representative of a security key valid before handover could be information about an actual base security key used before handover, or an intermediary key such as a NH key valid before the handover.
- the key derivation may possibly use other optional input(s).
- the RAT type in addition to information representing other properties of the target cell (like PCI and ARFCN) in the key derivation.
- the information representative of the RAT type of the target network node may be used together with information representing additional properties of the target cell in the key derivation.
- the information representing properties of the target cell may include Physical Cell ID, PCI, and/or Absolute Radio Frequency Channel Number, ARFCN.
- FIG. 8 is a schematic diagram illustrating an example of security context/key derivation based on RAT type, where an input parameter representative of the RAT type is used as input to a new or existing key derivation function.
- the step of deriving the security context at least partly based on the information representative of the RAT type is based on using an input parameter representative of the RAT type into a new or existing key derivation function (KDF).
- KDF key derivation function
- the RAT type may thus be included as an additional input to the key derivation ensuring the input parameter to the key derivation will be different for Long Term Evolution, LTE, and New radio, NR.
- FIG. 9 is a schematic diagram illustrating an example of security context/key derivation based on RAT type, where different key derivation functions are used for different RAT types.
- the step of deriving the security context at least partly based on the information representative of the RAT type is based on using different key derivation functions KDF(1), KDF(2), ...for different RAT types.
- the RAT type is encoded into the key derivation function, KDF, by defining two separate KDFs, one for Long Term Evolution, LTE and one for New Radio, NR.
- KDF key derivation function
- the step of deriving and/or determining the security context is based on selecting key derivation function depending on the RAT type.
- the method may be applied at intra-RAT and/or inter-RAT handovers within the same core network.
- the method may be performed by the wireless device such as a UE.
- the information representative of the RAT type may be obtained based on received information provided in the RRC handover command or based on received information broadcasted in the target cell.
- the method may be performed by a network node.
- the handover is from a source network node to a target network node.
- the method may be performed by the source network node, e.g. at Xn handover or intra-gNB handover.
- the source network node may be a source radio access network (RAN) node.
- RAN radio access network
- the handover is an Xn handover and the information representative of the RAT type is obtained based on Xn signaling or pre-configuration.
- the method may be performed by the target network node, e.g. at N2 handover.
- the target network node may be a target radio access network (RAN) node.
- RAN radio access network
- the handover is a N2 handover and the information representative of the RAT type is obtained based on N2 signaling or pre-configuration.
- the method may be performed by a network device.
- the network device may be a network device in the core network.
- the network device in the core network may implement an Access and Mobility management Function (AMF).
- AMF Access and Mobility management Function
- the network device may be an AMF network device in the core network.
- the information representative of the RAT type may be obtained based on N2 signaling or pre-configuration.
- the network device may be a computer-implemented network device such as a cloud-based network device.
- the proposed technology provides a simple and secure mechanism of key derivations in handovers in 5G.
- the simplicity comes from at least one of:
- the key derivation scheme also enables the usage of multi-cell preparation for handover and RRC_INACTIVE which could improve the cellular network and end user performance, for example:
- the radio access network, NG-RAN will include RAN nodes which could be either of type NR, i.e., gNB, or of type E-UTRA/LTE, i.e., ng-eNB. Consequently the handovers could involve two gNBs, two ng-eNBs, or a gNB and an ng-eNB. So there is a challenge of how to perform key derivations at handovers, similar to the horizontal and vertical key derivations in LTE.
- a potential solution could be to adopt a new mechanism for handovers in 5G.
- using some form of counter or more generally, a nonce for the key derivation instead of PCI and DL-EARFCN.
- the counter is chosen and maintained by the source RAN node.
- K gNB* will be decided solely by the source RAN node. This implies that the source RAN node can prepare multiple target RAN nodes with the same K gNB* .
- the UE is forced to comply with what source RAN node does.
- Another potential solution could be to adopt the LTE mechanism as is.
- the target RAN node as were used in LTE, i.e, the PCI and the DL-EARFCN of the target RAN node/cell for the derivation of the K gNB* .
- the problem is in NG-RAN and not in E-UTRAN because NG-RAN contains both NR and LTE cells whereas E-UTRAN only contains LTE cells.
- K gNB* the AS-base key
- K gNB* the AS-base key
- RAT radio access technology
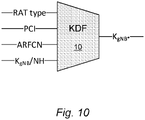
- FIG. 10 is a schematic diagram illustrating a particular example of key derivation according to an embodiment.
- FIG. 10 illustrates an example key derivation function (KDF) which is used to derive the new AS-base key, called K gNB* here, at handover in 5G.
- KDF key derivation function
- the KDF may take four inputs: - RAT type - Radio Access Technology, either NR or E-UTRA/LTE; - PCI - PCI of NR or E-UTRA/LTE cell; - DL-ARFCN - DL-NRARFCN for NR cells and DL-EARFCN for E-UTRA/LTE cells; and - K gNB /NH - current K gNB or Next Hop, NH, key
- the new additional input called the RAT type may be encoded in different ways, e.g. a single bit (1 for NR and 0 for LTE), or string ("nr" for NR and "Ite” for LTE).
- the KDF could be the extension of the existing LTE KDF specified in Clause A.5 in 3GPP TS 33.401.
- the same Function Code (FC) value i.e. 0x13, would be reused, P0/L0 (PCI, and length of PCI) would be reused, P1/L1 (DL-ARFCN and length of DL-ARFCN) would be reused and P2/L2 (RAT type and length of RAT type) would be additional input.
- FC Function Code
- the RAT type can be included in other ways as well.
- the source RAN node would then use the new NR KDF at handover to an NR cell (belonging to gNB) and the existing/legacy LTE KDF at handover to an LTE cell (belonging to ng-eNB).
- An advantage with using different KDFs for NR and LTE is that then it would be possible to reuse the existing LTE KDF and existing input parameters for UEs on LTE side while still ensuring that different keys are generated on the NR side (i.e. that the RAT type is considered as input to the key generation, in this case selecting which KDF to be used). It also possible to define new KDFs both for NR and for LTE. In this case the existing/legacy LTE KDF would not be used but only the new KDFs.
- Different KDFs can e.g. be created from the generic KDF defined in 3GPP TS 33.220 by using different values for the FC parameter.
- the generic KDF takes a key and bit string S as input and produces a 256 bit key as output, where S is formed by concatenating the fixed length FC and all the input parameters (except the key). Since FC occurs first in S, the input is guaranteed to be different even if the bit string formed from the other input parameters are identical.
- the NR and LTE target RAN nodes/cells receive distinct keys during handover preparation phase even if the PCI and ARFCN of two cells happen to be the same or if the parameters used in NR related to the target cell or RAN node has the identical value as a PCI and ARFCN in LTE.
- KDFs key derivation functions
- Our invention maintains the security properties, present in LTE, i.e., the security of new AS-base key is not decided by source RAN node alone because UE can independently acquire target RAN node's PCI and ARFCN.
- the source RAN node in case of Xn-handover or target RAN node (in case of N2 handover) can determine the RAT type of the target cell/target node required for the key derivation based on e.g., Xn or N2 signaling or pre-configuration. If the derivation is performed by a core network node, e.g., AMF, then the RAT type can be determined based on e.g., N2 signaling or pre-configuration. On the UE side the RAT type can be determined based on e.g., information provided in the RRC handover command or based on information broadcasted in the target cell (e.g. synchronization signals or system information).
- a core network node e.g., AMF
- the RAT type can be determined based on e.g., information provided in the RRC handover command or based on information broadcasted in the target cell (e.g. synchronization signals or system information).
- embodiments may be implemented in hardware, or in software for execution by suitable processing circuitry, or a combination thereof.
- At least some of the steps, functions, procedures, modules and/or blocks described herein may be implemented in software such as a computer program for execution by suitable processing circuitry such as one or more processors or processing units.
- processing circuitry includes, but is not limited to, one or more microprocessors, one or more Digital Signal Processors (DSPs), one or more Central Processing Units (CPUs), video acceleration hardware, and/or any suitable programmable logic circuitry such as one or more Field Programmable Gate Arrays (FPGAs), or one or more Programmable Logic Controllers (PLCs).
- DSPs Digital Signal Processors
- CPUs Central Processing Units
- FPGAs Field Programmable Gate Arrays
- PLCs Programmable Logic Controllers
- a device configured to determine a security context for communication between a wireless device and a target network node at handover.
- the device is configured to obtain information representative of the type of Radio Access Technology, also referred to as RAT type, of the target network node.
- the device is further configured to derive and/or determine the security context at least partly based on the information representative of the RAT type.
- the device may be configured to derive the security context by taking the determined RAT type into account in the key derivation.
- the security context may comprise at least a security key.
- the device may be configured to derive and/or determine at least a security key as part of the security context.
- the security key may be an Access Stratum (AS) base security key such as an AS base security key for protecting integrity and/or confidentiality.
- AS Access Stratum
- the base security key is K gNB* or K ng-eNB* .
- the device may be configured to receive and/or determine the information representative of the RAT type.
- the device may be configured to derive a new security key to be used after handover by using the information representative of the RAT type together with information representative of a security key valid before handover.
- the device may be configured to derive the security context at least partly based on the information representative of the RAT type by using an input parameter representative of the RAT type into a new or existing key derivation function.
- the device may be configured to derive the security context at least partly based on the information representative of the RAT type by using different key derivation functions for different RAT types.
- the device comprises a processor and a memory, the memory comprising instructions executable by the processor, whereby the processor is operative to derive and/or determine the security context, as will be discussed later on.
- a wireless device comprising a device according to the second aspect.
- a network node comprising a device according to the second aspect.
- the network node may be a source network node.
- the source network node may be a source radio access network (RAN) node.
- RAN radio access network
- the network node is a target network node.
- the target network node may be a target radio access network (RAN) node.
- RAN radio access network
- a network device comprising a device according to the second aspect.
- the network device may be a network device in the core network.
- the network device in the core network may implement an Access and Mobility management Function (AMF).
- AMF Access and Mobility management Function
- the network device may be an AMF network device in the core network.
- the network device may be a computer-implemented network device such as a cloud-based network device.
- FIG. 11 is a schematic diagram illustrating an example of a device configured to determine a security context according to an embodiment.
- the device 100 comprises a processor 110 and a memory 120, the memory 120 comprising instructions executable by the processor 110, whereby the processor is operative to perform at least some of the steps, actions and/or functions described herein.
- the device 100 may also include a communication circuit 130.
- the communication circuit 130; 230 may include functions for wired and/or wireless communication with other devices and/or network nodes in the network.
- the communication circuit 130 may be based on radio circuitry for communication with one or more other nodes, including transmitting and/or receiving information.
- the communication circuit 130 may be interconnected to the processor 110 and/or memory 120.
- the communication circuit 130 may include any of the following: a receiver, a transmitter, a transceiver, input/output (I/O) circuitry, input port(s) and/or output port(s).
- FIG. 12 is a schematic diagram illustrating an example of a wireless device, network node or network device according to an embodiment.
- the wireless device, network node or network device 200 comprises a processor 210 and a memory 220, the memory 220 comprising instructions executable by the processor 210, whereby the processor is operative to perform at least some of the steps, actions and/or functions described herein.
- the wireless device, network node or network device 200 may also include a communication circuit 230.
- the communication circuit 230 may include functions for wired and/or wireless communication with other devices and/or network nodes in the network.
- the communication circuit 230 may be based on radio circuitry for communication with one or more other nodes, including transmitting and/or receiving information.
- the communication circuit 230 may be interconnected to the processor 210 and/or memory 220.
- the communication circuit 230 may include any of the following: a receiver, a transmitter, a transceiver, input/output (I/O) circuitry, input port(s) and/or output port(s).
- FIG. 13 is a schematic diagram illustrating an example of a computer-implementation according to an embodiment.
- a computer program 325; 335 which is loaded into the memory 320 for execution by processing circuitry including one or more processors 310.
- the processor(s) 310 and memory 320 are interconnected to each other to enable normal software execution.
- An optional input/output device 340 may also be interconnected to the processor(s) 310 and/or the memory 320 to enable input and/or output of relevant data such as input parameter(s) and/or resulting output parameter(s).
- processor' should be interpreted in a general sense as any system or device capable of executing program code or computer program instructions to perform a particular processing, determining or computing task.
- the processing circuitry including one or more processors 310 is thus configured to perform, when executing the computer program 325, well-defined processing tasks such as those described herein.
- the processing circuitry does not have to be dedicated to only execute the above-described steps, functions, procedure and/or blocks, but may also execute other tasks.
- the computer program comprises instructions, which when executed by at least one processor, cause the at least one processor to:
- a computer-program product comprising a computer-readable medium 320; 330 having stored thereon such a computer program 325; 335.
- the proposed technology also provides a carrier comprising the computer program, wherein the carrier is one of an electronic signal, an optical signal, an electromagnetic signal, a magnetic signal, an electric signal, a radio signal, a microwave signal, or a computer-readable storage medium.
- the software or computer program 325; 335 may be realized as a computer program product, which is normally carried or stored on a computer-readable medium 320; 330, in particular a non-volatile medium.
- the computer-readable medium may include one or more removable or non-removable memory devices including, but not limited to a Read-Only Memory (ROM), a Random Access Memory (RAM), a Compact Disc (CD), a Digital Versatile Disc (DVD), a Blu-ray disc, a Universal Serial Bus (USB) memory, a Hard Disk Drive (HDD) storage device, a flash memory, a magnetic tape, or any other conventional memory device.
- the computer program may thus be loaded into the operating memory of a computer or equivalent processing device for execution by the processing circuitry thereof.
- a network device comprising a device configured for determining a security context as described herein.
- the network device may be any suitable network device in the wireless communication system, or a network device in connection with the wireless communication system.
- the network device may be a suitable network node such a base station or an access point.
- the network device may alternatively be a cloud-implemented network device.
- the flow diagram or diagrams presented herein may be regarded as a computer flow diagram or diagrams, when performed by one or more processors.
- a corresponding apparatus may be defined as a group of function modules, where each step performed by the processor corresponds to a function module.
- the function modules are implemented as a computer program running on the processor.
- the computer program residing in memory may thus be organized as appropriate function modules configured to perform, when executed by the processor, at least part of the steps and/or tasks described herein.
- any appropriate steps, methods, features, functions, or benefits disclosed herein may be performed through one or more functional units or modules of one or more virtual apparatuses.
- Each virtual apparatus may comprise a number of these functional units.
- These functional units may be implemented via processing circuitry, which may include one or more microprocessor or microcontrollers, as well as other digital hardware, which may include digital signal processors (DSPs), special-purpose digital logic, and the like.
- the processing circuitry may be configured to execute program code stored in memory, which may include one or several types of memory such as read-only memory (ROM), random-access memory (RAM), cache memory, flash memory devices, optical storage devices, etc.
- Program code stored in memory includes program instructions for executing one or more telecommunications and/or data communications protocols as well as instructions for carrying out one or more of the techniques described herein.
- the processing circuitry may be used to cause the respective functional unit to perform corresponding functions according one or more embodiments of the present disclosure.
- FIG. 14 is a schematic diagram illustrating an example of an apparatus for determining a security context for communication between a wireless device and a target network node at handover.
- the apparatus 400 comprises:
- module(s) in FIG. 14 it is possible to realize the module(s) in FIG. 14 predominantly by hardware modules, or alternatively by hardware, with suitable interconnections between relevant modules.
- Particular examples include one or more suitably configured digital signal processors and other known electronic circuits, e.g. discrete logic gates interconnected to perform a specialized function, and/or Application Specific Integrated Circuits (ASICs) as previously mentioned.
- Other examples of usable hardware include input/output (I/O) circuitry and/or circuitry for receiving and/or sending signals.
- I/O input/output
- the "virtual" apparatus may be implemented in a wireless device or network node (e.g., wireless device QQ110 or network node QQ160 shown in FIG. 15 ).
- the apparatus is operable to carry out the example method described herein, e.g. with reference to FIG. 6A and/or FIG. 6B and possibly any other processes or methods disclosed herein. It is also to be understood that the method of FIG. 6A and/or FIG. 6B is not necessarily carried out solely by the apparatus in FIG. 14 . At least some operations of the method can be performed by one or more other entities.
- the virtual apparatus may comprise processing circuitry, which may include one or more microprocessor or microcontrollers, as well as other digital hardware, which may include digital signal processors (DSPs), special-purpose digital logic, and the like.
- the processing circuitry may be configured to execute program code stored in memory, which may include one or several types of memory such as read-only memory (ROM), random-access memory, cache memory, flash memory devices, optical storage devices, etc.
- Program code stored in memory includes program instructions for executing one or more telecommunications and/or data communications protocols as well as instructions for carrying out one or more of the techniques described herein, in several embodiments.
- module or unit may have conventional meaning in the field of electronics, electrical devices and/or electronic devices and may include, for example, electrical and/or electronic circuitry, devices, modules, processors, memories, logic solid state and/or discrete devices, computer programs or instructions for carrying out respective tasks, procedures, computations, outputs, and/or displaying functions, and so on, as such as those that are described herein.
- computing services can be distributed or re-located to one or more separate physical nodes or servers.
- the functionality may be re-located or distributed to one or more jointly acting physical and/or virtual machines that can be positioned in separate physical node(s), i.e. in the so-called cloud.
- cloud computing is a model for enabling ubiquitous on-demand network access to a pool of configurable computing resources such as networks, servers, storage, applications and general or customized services.
- a Network Device may generally be seen as an electronic device being communicatively connected to other electronic devices in the network.
- the network device may be implemented in hardware, software or a combination thereof.
- the network device may be a special-purpose network device or a general purpose network device, or a hybrid thereof.
- a special-purpose network device may use custom processing circuits and a proprietary operating system (OS), for execution of software to provide one or more of the features or functions disclosed herein.
- OS operating system
- a general purpose network device may use common off-the-shelf (COTS) processors and a standard OS, for execution of software configured to provide one or more of the features or functions disclosed herein.
- COTS off-the-shelf
- a special-purpose network device may include hardware comprising processing or computing resource(s), which typically include a set of one or more processors, and physical network interfaces (NIs), which sometimes are called physical ports, as well as non-transitory machine readable storage media having stored thereon software.
- a physical NI may be seen as hardware in a network device through which a network connection is made, e.g. wirelessly through a wireless network interface controller (WNIC) or through plugging in a cable to a physical port connected to a network interface controller (NIC).
- WNIC wireless network interface controller
- NIC network interface controller
- the software may be executed by the hardware to instantiate a set of one or more software instance(s).
- Each of the software instance(s), and that part of the hardware that executes that software instance may form a separate virtual network element.
- a general purpose network device may for example include hardware comprising a set of one or more processor(s), often COTS processors, and network interface controller(s) (NICs), as well as non-transitory machine readable storage media having stored thereon software.
- the processor(s) executes the software to instantiate one or more sets of one or more applications.
- one embodiment does not implement virtualization, alternative embodiments may use different forms of virtualization - for example represented by a virtualization layer and software containers.
- one such alternative embodiment implements operating system-level virtualization, in which case the virtualization layer represents the kernel of an operating system (or a shim executing on a base operating system) that allows for the creation of multiple software containers that may each be used to execute one of a sets of applications.
- each of the software containers also called virtualization engines, virtual private servers, or jails
- a user space instance typically a virtual memory space.
- the virtualization layer represents a hypervisor (sometimes referred to as a Virtual Machine Monitor (VMM)) or the hypervisor is executed on top of a host operating system; and 2) the software containers each represent a tightly isolated form of software container called a virtual machine that is executed by the hypervisor and may include a guest operating system.
- VMM Virtual Machine Monitor
- a hypervisor is the software/hardware that is responsible for creating and managing the various virtualized instances and in some cases the actual physical hardware.
- the hypervisor manages the underlying resources and presents them as virtualized instances. What the hypervisor virtualizes to appear as a single processor may actually comprise multiple separate processors. From the perspective of the operating system, the virtualized instances appear to be actual hardware components.
- a virtual machine is a software implementation of a physical machine that runs programs as if they were executing on a physical, non-virtualized machine; and applications generally do not know they are running on a virtual machine as opposed to running on a "bare metal" host electronic device, though some systems provide para-virtualization which allows an operating system or application to be aware of the presence of virtualization for optimization purposes.
- the instantiation of the one or more sets of one or more applications as well as the virtualization layer and software containers if implemented, are collectively referred to as software instance(s).
- Each set of applications, corresponding software container if implemented, and that part of the hardware that executes them (be it hardware dedicated to that execution and/or time slices of hardware temporally shared by software containers), forms a separate virtual network element(s).
- the virtual network element(s) may perform similar functionality compared to Virtual Network Element(s) (VNEs). This virtualization of the hardware is sometimes referred to as Network Function Virtualization (NFV)).
- NFV Network Function Virtualization
- NFV may be used to consolidate many network equipment types onto industry standard high volume server hardware, physical switches, and physical storage, which could be located in data centers, NDs, and Customer Premise Equipment (CPE).
- CPE Customer Premise Equipment
- different embodiments may implement one or more of the software container(s) differently.
- a hybrid network device which includes both custom processing circuitry/proprietary OS and COTS processors/standard OS in a network device, e.g. in a card or circuit board within a network device ND.
- a platform Virtual Machine such as a VM that implements functionality of a special-purpose network device, could provide for para-virtualization to the hardware present in the hybrid network device.
- the proposed technology is generally applicable to management of security contexts in wireless communications.
- the proposed technology may be applied to many specific applications and communication scenarios including secure communication within wireless networks, securely providing various services within such networks, including so-called Over-the-Top (OTT) services.
- OTT Over-the-Top
- the proposed technology may provide the underlying security context(s) for secure communication, and enables and/or includes transfer and/or transmission and/or reception of relevant user data and/or control data in wireless communications.
- the method comprises:
- the step of protecting the communication includes providing integrity and/or confidentiality protection for transmission and/or reception of user data and/or control data between the wireless device and the target network node.
- the method may further comprise:
- the method may further comprise:
- a corresponding device configured for secure communication between a wireless device and a target network node at handover
- FIG. 15 is a schematic diagram illustrating an example of a wireless network in accordance with some embodiments.
- a wireless network such as the example wireless network illustrated in FIG. 15 .
- the wireless network of FIG. 15 only depicts network QQ106, network nodes QQ160 and QQ160b, and WDs QQ110, QQ110b, and QQ110c.
- a wireless network may further include any additional elements suitable to support communication between wireless devices or between a wireless device and another communication device, such as a landline telephone, a service provider, or any other network node or end device.
- network node QQ160 and wireless device (WD) QQ110 are depicted with additional detail.
- the wireless network may provide communication and other types of services to one or more wireless devices to facilitate the wireless devices' access to and/or use of the services provided by, or via, the wireless network.
- the wireless network may comprise and/or interface with any type of communication, telecommunication, data, cellular, and/or radio network or other similar type of system.
- the wireless network may be configured to operate according to specific standards or other types of predefined rules or procedures.
- particular embodiments of the wireless network may implement communication standards, such as Global System for Mobile Communications (GSM), Universal Mobile Telecommunications System (UMTS), Long Term Evolution (LTE), and/or other suitable 2G, 3G, 4G, or 5G standards; wireless local area network (WLAN) standards, such as the IEEE 802.11 standards; and/or any other appropriate wireless communication standard, such as the Worldwide Interoperability for Microwave Access (WiMax), Bluetooth, Z-Wave and/or ZigBee standards.
- GSM Global System for Mobile Communications
- UMTS Universal Mobile Telecommunications System
- LTE Long Term Evolution
- WLAN wireless local area network
- WiMax Worldwide Interoperability for Microwave Access
- Bluetooth Z-Wave and/or ZigBee standards.
- Network QQ106 may comprise one or more backhaul networks, core networks, IP networks, public switched telephone networks (PSTNs), packet data networks, optical networks, wide-area networks (WANs), local area networks (LANs), wireless local area networks (WLANs), wired networks, wireless networks, metropolitan area networks, and other networks to enable communication between devices.
- PSTNs public switched telephone networks
- WANs wide-area networks
- LANs local area networks
- WLANs wireless local area networks
- wired networks wireless networks, metropolitan area networks, and other networks to enable communication between devices.
- Network node QQ160 and WD QQ110 comprise various components described in more detail below. These components work together in order to provide network node and/or wireless device functionality, such as providing wireless connections in a wireless network.
- the wireless network may comprise any number of wired or wireless networks, network nodes, base stations, controllers, wireless devices, relay stations, and/or any other components or systems that may facilitate or participate in the communication of data and/or signals whether via wired or wireless connections.
- network node refers to equipment capable, configured, arranged and/or operable to communicate directly or indirectly with a wireless device and/or with other network nodes or equipment in the wireless network to enable and/or provide wireless access to the wireless device and/or to perform other functions (e.g., administration) in the wireless network.
- network nodes include, but are not limited to, access points (APs) (e.g., radio access points), base stations (BSs) (e.g., radio base stations, Node Bs, evolved Node Bs (eNBs) and NR NodeBs (gNBs)).
- APs access points
- BSs base stations
- eNBs evolved Node Bs
- gNBs NR NodeBs
- Base stations may be categorized based on the amount of coverage they provide (or, stated differently, their transmit power level) and may then also be referred to as femto base stations, pico base stations, micro base stations, or macro base stations.
- a base station may be a relay node or a relay donor node controlling a relay.
- a network node may also include one or more (or all) parts of a distributed radio base station such as centralized digital units and/or remote radio units (RRUs), sometimes referred to as Remote Radio Heads (RRHs). Such remote radio units may or may not be integrated with an antenna as an antenna integrated radio.
- RRUs remote radio units
- RRHs Remote Radio Heads
- Such remote radio units may or may not be integrated with an antenna as an antenna integrated radio.
- Parts of a distributed radio base station may also be referred to as nodes in a distributed antenna system (DAS).
- DAS distributed antenna system
- network nodes include multi-standard radio (MSR) equipment such as MSR BSs, network controllers such as radio network controllers (RNCs) or base station controllers (BSCs), base transceiver stations (BTSs), transmission points, transmission nodes, multi-cell/multicast coordination entities (MCEs), core network nodes (e.g., MSCs, MMEs), O&M nodes, OSS nodes, SON nodes, positioning nodes (e.g., E-SMLCs), and/or MDTs.
- MSR multi-standard radio
- RNCs radio network controllers
- BSCs base station controllers
- BTSs base transceiver stations
- transmission points transmission nodes
- MCEs multi-cell/multicast coordination entities
- core network nodes e.g., MSCs, MMEs
- O&M nodes e.g., OSS nodes, SON nodes, positioning nodes (e.g., E-SMLCs), and/or MDTs.
- network nodes may represent any suitable device (or group of devices) capable, configured, arranged, and/or operable to enable and/or provide a wireless device with access to the wireless network or to provide some service to a wireless device that has accessed the wireless network.
- network node QQ160 includes processing circuitry QQ170, device readable medium QQ180, interface QQ190, auxiliary equipment QQ184, power source QQ186, power circuitry QQ187, and antenna QQ162.
- network node QQ160 illustrated in the example wireless network of FIG. 15 may represent a device that includes the illustrated combination of hardware components, other embodiments may comprise network nodes with different combinations of components. It is to be understood that a network node comprises any suitable combination of hardware and/or software needed to perform the tasks, features, functions and methods disclosed herein.
- network node QQ160 may comprise multiple different physical components that make up a single illustrated component (e.g., device readable medium QQ180 may comprise multiple separate hard drives as well as multiple RAM modules).
- network node QQ160 may be composed of multiple physically separate components (e.g., a NodeB component and a RNC component, or a BTS component and a BSC component, etc.), which may each have their own respective components.
- network node QQ160 comprises multiple separate components (e.g., BTS and BSC components)
- one or more of the separate components may be shared among several network nodes.
- a single RNC may control multiple NodeB's.
- each unique NodeB and RNC pair may in some instances be considered a single separate network node.
- network node QQ160 may be configured to support multiple radio access technologies (RATs).
- RATs radio access technologies
- Network node QQ160 may also include multiple sets of the various illustrated components for different wireless technologies integrated into network node QQ160, such as, for example, GSM, WCDMA, LTE, NR, WiFi, or Bluetooth wireless technologies. These wireless technologies may be integrated into the same or different chip or set of chips and other components within network node QQ160.
- Processing circuitry QQ170 is configured to perform any determining, calculating, or similar operations (e.g., certain obtaining operations) described herein as being provided by a network node. These operations performed by processing circuitry QQ170 may include processing information obtained by processing circuitry QQ170 by, for example, converting the obtained information into other information, comparing the obtained information or converted information to information stored in the network node, and/or performing one or more operations based on the obtained information or converted information, and as a result of said processing making a determination.
- processing information obtained by processing circuitry QQ170 by, for example, converting the obtained information into other information, comparing the obtained information or converted information to information stored in the network node, and/or performing one or more operations based on the obtained information or converted information, and as a result of said processing making a determination.
- Processing circuitry QQ170 may comprise a combination of one or more of a microprocessor, controller, microcontroller, central processing unit, digital signal processor, application-specific integrated circuit, field programmable gate array, or any other suitable computing device, resource, or combination of hardware, software and/or encoded logic operable to provide, either alone or in conjunction with other network node QQ160 components, such as device readable medium QQ180, network node QQ160 functionality.
- processing circuitry QQ170 may execute instructions stored in device readable medium QQ180 or in memory within processing circuitry QQ170. Such functionality may include providing any of the various wireless features, functions, or benefits discussed herein.
- processing circuitry QQ170 may include a system on a chip (SOC).
- SOC system on a chip
- processing circuitry QQ170 may include one or more of radio frequency (RF) transceiver circuitry QQ172 and baseband processing circuitry QQ174.
- radio frequency (RF) transceiver circuitry QQ172 and baseband processing circuitry QQ174 may be on separate chips (or sets of chips), boards, or units, such as radio units and digital units.
- part or all of RF transceiver circuitry QQ172 and baseband processing circuitry QQ174 may be on the same chip or set of chips, boards, or units
- processing circuitry QQ170 executing instructions stored on device readable medium QQ180 or memory within processing circuitry QQ170.
- some or all of the functionality may be provided by processing circuitry QQ170 without executing instructions stored on a separate or discrete device readable medium, such as in a hard-wired manner.
- processing circuitry QQ170 can be configured to perform the described functionality. The benefits provided by such functionality are not limited to processing circuitry QQ170 alone or to other components of network node QQ160, but are enjoyed by network node QQ160 as a whole, and/or by end users and the wireless network generally.
- Device readable medium QQ180 may comprise any form of volatile or non-volatile computer readable memory including, without limitation, persistent storage, solid-state memory, remotely mounted memory, magnetic media, optical media, random access memory (RAM), read-only memory (ROM), mass storage media (for example, a hard disk), removable storage media (for example, a flash drive, a Compact Disk (CD) or a Digital Video Disk (DVD)), and/or any other volatile or non-volatile, non-transitory device readable and/or computer-executable memory devices that store information, data, and/or instructions that may be used by processing circuitry QQ170.
- volatile or non-volatile computer readable memory including, without limitation, persistent storage, solid-state memory, remotely mounted memory, magnetic media, optical media, random access memory (RAM), read-only memory (ROM), mass storage media (for example, a hard disk), removable storage media (for example, a flash drive, a Compact Disk (CD) or a Digital Video Disk (DVD)), and/or any
- Device readable medium QQ180 may store any suitable instructions, data or information, including a computer program, software, an application including one or more of logic, rules, code, tables, etc. and/or other instructions capable of being executed by processing circuitry QQ170 and, utilized by network node QQ160.
- Device readable medium QQ180 may be used to store any calculations made by processing circuitry QQ170 and/or any data received via interface QQ190.
- processing circuitry QQ170 and device readable medium QQ180 may be considered to be integrated.
- Interface QQ190 is used in the wired or wireless communication of signalling and/or data between network node QQ160, network QQ106, and/or WDs QQ110. As illustrated, interface QQ190 comprises port(s)/terminal(s) QQ194 to send and receive data, for example to and from network QQ106 over a wired connection. Interface QQ190 also includes radio front end circuitry QQ192 that may be coupled to, or in certain embodiments a part of, antenna QQ162. Radio front end circuitry QQ192 comprises filters QQ198 and amplifiers QQ196. Radio front end circuitry QQ192 may be connected to antenna QQ162 and processing circuitry QQ170.
- Radio front end circuitry may be configured to condition signals communicated between antenna QQ162 and processing circuitry QQ170.
- Radio front end circuitry QQ192 may receive digital data that is to be sent out to other network nodes or WDs via a wireless connection.
- Radio front end circuitry QQ192 may convert the digital data into a radio signal having the appropriate channel and bandwidth parameters using a combination of filters QQ198 and/or amplifiers QQ196. The radio signal may then be transmitted via antenna QQ162.
- antenna QQ162 may collect radio signals which are then converted into digital data by radio front end circuitry QQ192.
- the digital data may be passed to processing circuitry QQ170.
- the interface may comprise different components and/or different combinations of components.
- network node QQ160 may not include separate radio front end circuitry QQ192, instead, processing circuitry QQ170 may comprise radio front end circuitry and may be connected to antenna QQ162 without separate radio front end circuitry QQ192.
- processing circuitry QQ170 may comprise radio front end circuitry and may be connected to antenna QQ162 without separate radio front end circuitry QQ192.
- all or some of RF transceiver circuitry QQ172 may be considered a part of interface QQ190.
- interface QQ190 may include one or more ports or terminals QQ194, radio front end circuitry QQ192, and RF transceiver circuitry QQ172, as part of a radio unit (not shown), and interface QQ190 may communicate with baseband processing circuitry QQ174, which is part of a digital unit (not shown).
- Antenna QQ162 may include one or more antennas, or antenna arrays, configured to send and/or receive wireless signals. Antenna QQ162 may be coupled to radio front end circuitry QQ190 and may be any type of antenna capable of transmitting and receiving data and/or signals wirelessly. In some embodiments, antenna QQ162 may comprise one or more omni-directional, sector or panel antennas operable to transmit/receive radio signals between, for example, 2 GHz and 66 GHz.
- An omni-directional antenna may be used to transmit/receive radio signals in any direction
- a sector antenna may be used to transmit/receive radio signals from devices within a particular area
- a panel antenna may be a line of sight antenna used to transmit/receive radio signals in a relatively straight line.
- the use of more than one antenna may be referred to as MIMO.
- antenna QQ162 may be separate from network node QQ160 and may be connectable to network node QQ160 through an interface or port.
- Antenna QQ162, interface QQ190, and/or processing circuitry QQ170 may be configured to perform any receiving operations and/or certain obtaining operations described herein as being performed by a network node. Any information, data and/or signals may be received from a wireless device, another network node and/or any other network equipment. Similarly, antenna QQ162, interface QQ190, and/or processing circuitry QQ170 may be configured to perform any transmitting operations described herein as being performed by a network node. Any information, data and/or signals may be transmitted to a wireless device, another network node and/or any other network equipment.
- Power circuitry QQ187 may comprise, or be coupled to, power management circuitry and is configured to supply the components of network node QQ160 with power for performing the functionality described herein. Power circuitry QQ187 may receive power from power source QQ186. Power source QQ186 and/or power circuitry QQ187 may be configured to provide power to the various components of network node QQ160 in a form suitable for the respective components (e.g., at a voltage and current level needed for each respective component). Power source QQ186 may either be included in, or external to, power circuitry QQ187 and/or network node QQ160.
- network node QQ160 may be connectable to an external power source (e.g., an electricity outlet) via an input circuitry or interface such as an electrical cable, whereby the external power source supplies power to power circuitry QQ187.
- power source QQ186 may comprise a source of power in the form of a battery or battery pack which is connected to, or integrated in, power circuitry QQ187. The battery may provide backup power should the external power source fail.
- Other types of power sources such as photovoltaic devices, may also be used.
- Alternative embodiments of network node QQ160 may include additional components beyond those shown in FIG.
- network node QQ160 may include user interface equipment to allow input of information into network node QQ160 and to allow output of information from network node QQ160. This may allow a user to perform diagnostic, maintenance, repair, and other administrative functions for network node QQ160.
- wireless device refers to a device capable, configured, arranged and/or operable to communicate wirelessly with network nodes and/or other wireless devices.
- the term WD may be used interchangeably herein with user equipment (UE).
- Communicating wirelessly may involve transmitting and/or receiving wireless signals using electromagnetic waves, radio waves, infrared waves, and/or other types of signals suitable for conveying information through air.
- a WD may be configured to transmit and/or receive information without direct human interaction.
- a WD may be designed to transmit information to a network on a predetermined schedule, when triggered by an internal or external event, or in response to requests from the network.
- Examples of a WD include, but are not limited to, a smart phone, a mobile phone, a cell phone, a voice over IP (VoIP) phone, a wireless local loop phone, a desktop computer, a personal digital assistant (PDA), a wireless cameras, a gaming console or device, a music storage device, a playback appliance, a wearable terminal device, a wireless endpoint, a mobile station, a tablet, a laptop, a laptop-embedded equipment (LEE), a laptop-mounted equipment (LME), a smart device, a wireless customer-premise equipment (CPE).
- a WD may support device-to-device (D2D) communication, for example by implementing a 3GPP standard for sidelink communication, vehicle-to-vehicle (V2V), vehicle-to-infrastructure (V2I), vehicle-to-everything (V2X) and may in this case be referred to as a D2D communication device.
- D2D device-to-device
- V2V vehicle-to-vehicle
- V2I vehicle-to-infrastructure
- V2X vehicle-to-everything
- a WD may represent a machine or other device that performs monitoring and/or measurements, and transmits the results of such monitoring and/or measurements to another WD and/or a network node.
- the WD may in this case be a machine-to-machine (M2M) device, which may in a 3GPP context be referred to as an MTC device.
- M2M machine-to-machine
- the WD may be a UE implementing the 3GPP narrow band internet of things (NB-IoT) standard.
- NB-IoT narrow band internet of things
- machines or devices are sensors, metering devices such as power meters, industrial machinery, or home or personal appliances (e.g. refrigerators, televisions, etc.) personal wearables (e.g., watches, fitness trackers, etc.).
- a WD may represent a vehicle or other equipment that is capable of monitoring and/or reporting on its operational status or other functions associated with its operation.
- a WD as described above may represent the endpoint of a wireless connection, in which case the device may be referred to as a wireless terminal. Furthermore, a WD as described above may be mobile, in which case it may also be referred to as a mobile device or a mobile terminal.
- wireless device QQ110 includes antenna QQ111, interface QQ114, processing circuitry QQ120, device readable medium QQ130, user interface equipment QQ132, auxiliary equipment QQ134, power source QQ136 and power circuitry QQ137.
- WD QQ110 may include multiple sets of one or more of the illustrated components for different wireless technologies supported by WD QQ110, such as, for example, GSM, WCDMA, LTE, NR, WiFi, WiMAX, or Bluetooth wireless technologies, just to mention a few. These wireless technologies may be integrated into the same or different chips or set of chips as other components within WD QQ110.
- Antenna QQ111 may include one or more antennas or antenna arrays, configured to send and/or receive wireless signals, and is connected to interface QQ114.
- antenna QQ111 may be separate from WD QQ110 and be connectable to WD QQ110 through an interface or port.
- Antenna QQ111, interface QQ114, and/or processing circuitry QQ120 may be configured to perform any receiving or transmitting operations described herein as being performed by a WD. Any information, data and/or signals may be received from a network node and/or another WD.
- radio front end circuitry and/or antenna QQ111 may be considered an interface.
- interface QQ114 comprises radio front end circuitry QQ112 and antenna QQ111.
- Radio front end circuitry QQ112 comprise one or more filters QQ118 and amplifiers QQ116.
- Radio front end circuitry QQ114 is connected to antenna QQ111 and processing circuitry QQ120, and is configured to condition signals communicated between antenna QQ111 and processing circuitry QQ120.
- Radio front end circuitry QQ112 may be coupled to or a part of antenna QQ111.
- WD QQ110 may not include separate radio front end circuitry QQ112; rather, processing circuitry QQ120 may comprise radio front end circuitry and may be connected to antenna QQ111.
- Radio front end circuitry QQ112 may receive digital data that is to be sent out to other network nodes or WDs via a wireless connection. Radio front end circuitry QQ112 may convert the digital data into a radio signal having the appropriate channel and bandwidth parameters using a combination of filters QQ118 and/or amplifiers QQ116. The radio signal may then be transmitted via antenna QQ111. Similarly, when receiving data, antenna QQ111 may collect radio signals which are then converted into digital data by radio front end circuitry QQ112. The digital data may be passed to processing circuitry QQ120.
- the interface may comprise different components and/or different combinations of components.
- Processing circuitry QQ120 may comprise a combination of one or more of a microprocessor, controller, microcontroller, central processing unit, digital signal processor, application-specific integrated circuit, field programmable gate array, or any other suitable computing device, resource, or combination of hardware, software, and/or encoded logic operable to provide, either alone or in conjunction with other WD QQ110 components, such as device readable medium QQ130, WD QQ110 functionality. Such functionality may include providing any of the various wireless features or benefits discussed herein.
- processing circuitry QQ120 may execute instructions stored in device readable medium QQ130 or in memory within processing circuitry QQ120 to provide the functionality disclosed herein.
- processing circuitry QQ120 includes one or more of RF transceiver circuitry QQ122, baseband processing circuitry QQ124, and application processing circuitry QQ126.
- the processing circuitry may comprise different components and/or different combinations of components.
- processing circuitry QQ120 of WD QQ110 may comprise a SOC.
- RF transceiver circuitry QQ122, baseband processing circuitry QQ124, and application processing circuitry QQ126 may be on separate chips or sets of chips.
- part or all of baseband processing circuitry QQ124 and application processing circuitry QQ126 may be combined into one chip or set of chips, and RF transceiver circuitry QQ122 may be on a separate chip or set of chips.
- part or all of RF transceiver circuitry QQ122 and baseband processing circuitry QQ124 may be on the same chip or set of chips, and application processing circuitry QQ126 may be on a separate chip or set of chips.
- part or all of RF transceiver circuitry QQ122, baseband processing circuitry QQ124, and application processing circuitry QQ126 may be combined in the same chip or set of chips.
- RF transceiver circuitry QQ122 may be a part of interface QQ114.
- RF transceiver circuitry QQ122 may condition RF signals for processing circuitry QQ120.
- processing circuitry QQ120 executing instructions stored on device readable medium QQ130, which in certain embodiments may be a computer-readable storage medium.
- some or all of the functionality may be provided by processing circuitry QQ120 without executing instructions stored on a separate or discrete device readable storage medium, such as in a hard-wired manner.
- processing circuitry QQ120 can be configured to perform the described functionality.
- the benefits provided by such functionality are not limited to processing circuitry QQ120 alone or to other components of WD QQ110, but are enjoyed by WD QQ110 as a whole, and/or by end users and the wireless network generally.
- Processing circuitry QQ120 may be configured to perform any determining, calculating, or similar operations (e.g., certain obtaining operations) described herein as being performed by a WD. These operations, as performed by processing circuitry QQ120, may include processing information obtained by processing circuitry QQ120 by, for example, converting the obtained information into other information, comparing the obtained information or converted information to information stored by WD QQ110, and/or performing one or more operations based on the obtained information or converted information, and as a result of said processing making a determination.
- processing information obtained by processing circuitry QQ120 by, for example, converting the obtained information into other information, comparing the obtained information or converted information to information stored by WD QQ110, and/or performing one or more operations based on the obtained information or converted information, and as a result of said processing making a determination.
- Device readable medium QQ130 may be operable to store a computer program, software, an application including one or more of logic, rules, code, tables, etc. and/or other instructions capable of being executed by processing circuitry QQ120.
- Device readable medium QQ130 may include computer memory (e.g., Random Access Memory (RAM) or Read Only Memory (ROM)), mass storage media (e.g., a hard disk), removable storage media (e.g., a Compact Disk (CD) or a Digital Video Disk (DVD)), and/or any other volatile or non-volatile, non-transitory device readable and/or computer executable memory devices that store information, data, and/or instructions that may be used by processing circuitry QQ120.
- processing circuitry QQ120 and device readable medium QQ130 may be considered to be integrated.
- User interface equipment QQ132 may provide components that allow for a human user to interact with WD QQ110. Such interaction may be of many forms, such as visual, audial, tactile, etc. User interface equipment QQ132 may be operable to produce output to the user and to allow the user to provide input to WD QQ110. The type of interaction may vary depending on the type of user interface equipment QQ132 installed in WD QQ110. For example, if WD QQ110 is a smart phone, the interaction may be via a touch screen; if WD QQ110 is a smart meter, the interaction may be through a screen that provides usage (e.g., the number of gallons used) or a speaker that provides an audible alert (e.g., if smoke is detected).
- usage e.g., the number of gallons used
- a speaker that provides an audible alert
- User interface equipment QQ132 may include input interfaces, devices and circuits, and output interfaces, devices and circuits. User interface equipment QQ132 is configured to allow input of information into WD QQ110, and is connected to processing circuitry QQ120 to allow processing circuitry QQ120 to process the input information. User interface equipment QQ132 may include, for example, a microphone, a proximity or other sensor, keys/buttons, a touch display, one or more cameras, a USB port, or other input circuitry. User interface equipment QQ132 is also configured to allow output of information from WD QQ110, and to allow processing circuitry QQ120 to output information from WD QQ110.
- User interface equipment QQ132 may include, for example, a speaker, a display, vibrating circuitry, a USB port, a headphone interface, or other output circuitry. Using one or more input and output interfaces, devices, and circuits, of user interface equipment QQ132, WD QQ110 may communicate with end users and/or the wireless network, and allow them to benefit from the functionality described herein.
- Auxiliary equipment QQ134 is operable to provide more specific functionality which may not be generally performed by WDs. This may comprise specialized sensors for doing measurements for various purposes, interfaces for additional types of communication such as wired communications etc. The inclusion and type of components of auxiliary equipment QQ134 may vary depending on the embodiment and/or scenario.
- Power source QQ136 may, in some embodiments, be in the form of a battery or battery pack. Other types of power sources, such as an external power source (e.g., an electricity outlet), photovoltaic devices or power cells, may also be used.
- WD QQ110 may further comprise power circuitry QQ137 for delivering power from power source QQ136 to the various parts of WD QQ110 which need power from power source QQ136 to carry out any functionality described or indicated herein.
- Power circuitry QQ137 may in certain embodiments comprise power management circuitry.
- Power circuitry QQ137 may additionally or alternatively be operable to receive power from an external power source; in which case WD QQ110 may be connectable to the external power source (such as an electricity outlet) via input circuitry or an interface such as an electrical power cable.
- Power circuitry QQ137 may also in certain embodiments be operable to deliver power from an external power source to power source QQ136. This may be, for example, for the charging of power source QQ136. Power circuitry QQ137 may perform any formatting, converting, or other modification to the power from power source QQ136 to make the power suitable for the respective components of WD QQ110 to which power is supplied.
- FIG. 16 is a schematic diagram illustrating an example of an embodiment of a UE in accordance with various aspects described herein.
- a user equipment or UE may not necessarily have a user in the sense of a human user who owns and/or operates the relevant device.
- a UE may represent a device that is intended for sale to, or operation by, a human user but which may not, or which may not initially, be associated with a specific human user (e.g., a smart sprinkler controller).
- a UE may represent a device that is not intended for sale to, or operation by, an end user but which may be associated with or operated for the benefit of a user (e.g., a smart power meter).
- UE QQ2200 may be any UE identified by the 3 rd Generation Partnership Project (3GPP), including a NB-IoT UE, a machine type communication (MTC) UE, and/or an enhanced MTC (eMTC) UE.
- UE QQ200 is one example of a WD configured for communication in accordance with one or more communication standards promulgated by the 3 rd Generation Partnership Project (3GPP), such as 3GPP's GSM, UMTS, LTE, and/or 5G standards.
- 3GPP 3 rd Generation Partnership Project
- the term WD and UE may be used interchangeable. Accordingly, although FIG. 16 is a UE, the components discussed herein are equally applicable to a WD, and vice-versa.
- UE QQ200 includes processing circuitry QQ201 that is operatively coupled to input/output interface QQ205, radio frequency (RF) interface QQ209, network connection interface QQ211, memory QQ215 including random access memory (RAM) QQ217, read-only memory (ROM) QQ219, and storage medium QQ221 or the like, communication subsystem QQ231, power source QQ233, and/or any other component, or any combination thereof.
- Storage medium QQ221 includes operating system QQ223, application program QQ225, and data QQ227. In other embodiments, storage medium QQ221 may include other similar types of information. Certain UEs may utilize all of the components shown in FIG. 16 , or only a subset of the components. The level of integration between the components may vary from one UE to another UE. Further, certain UEs may contain multiple instances of a component, such as multiple processors, memories, transceivers, transmitters, receivers, etc.
- processing circuitry QQ201 may be configured to process computer instructions and data.
- Processing circuitry QQ201 may be configured to implement any sequential state machine operative to execute machine instructions stored as machine-readable computer programs in the memory, such as one or more hardware-implemented state machines (e.g., in discrete logic, FPGA, ASIC, etc.); programmable logic together with appropriate firmware; one or more stored program, general-purpose processors, such as a microprocessor or Digital Signal Processor (DSP), together with appropriate software; or any combination of the above.
- the processing circuitry QQ201 may include two central processing units (CPUs). Data may be information in a form suitable for use by a computer.
- input/output interface QQ205 may be configured to provide a communication interface to an input device, output device, or input and output device.
- UE QQ200 may be configured to use an output device via input/output interface QQ205.
- An output device may use the same type of interface port as an input device.
- a USB port may be used to provide input to and output from UE QQ200.
- the output device may be a speaker, a sound card, a video card, a display, a monitor, a printer, an actuator, an emitter, a smartcard, another output device, or any combination thereof.
- UE QQ200 may be configured to use an input device via input/output interface QQ205 to allow a user to capture information into UE QQ200.
- the input device may include a touch-sensitive or presence-sensitive display, a camera (e.g., a digital camera, a digital video camera, a web camera, etc.), a microphone, a sensor, a mouse, a trackball, a directional pad, a trackpad, a scroll wheel, a smartcard, and the like.
- the presence-sensitive display may include a capacitive or resistive touch sensor to sense input from a user.
- a sensor may be, for instance, an accelerometer, a gyroscope, a tilt sensor, a force sensor, a magnetometer, an optical sensor, a proximity sensor, another like sensor, or any combination thereof.
- the input device may be an accelerometer, a magnetometer, a digital camera, a microphone, and an optical sensor.
- RF interface QQ209 may be configured to provide a communication interface to RF components such as a transmitter, a receiver, and an antenna.
- Network connection interface QQ211 may be configured to provide a communication interface to network QQ243a.
- Network QQ243a may encompass wired and/or wireless networks such as a local-area network (LAN), a wide-area network (WAN), a computer network, a wireless network, a telecommunications network, another like network or any combination thereof.
- network QQ243a may comprise a Wi-Fi network.
- Network connection interface QQ211 may be configured to include a receiver and a transmitter interface used to communicate with one or more other devices over a communication network according to one or more communication protocols, such as Ethernet, TCP/IP, SONET, ATM, or the like.
- Network connection interface QQ211 may implement receiver and transmitter functionality appropriate to the communication network links (e.g., optical, electrical, and the like).
- the transmitter and receiver functions may share circuit components, software or firmware, or alternatively may be implemented separately.
- RAM QQ217 may be configured to interface via bus QQ202 to processing circuitry QQ201 to provide storage or caching of data or computer instructions during the execution of software programs such as the operating system, application programs, and device drivers.
- ROM QQ219 may be configured to provide computer instructions or data to processing circuitry QQ201.
- ROM QQ219 may be configured to store invariant low-level system code or data for basic system functions such as basic input and output (I/O), startup, or reception of keystrokes from a keyboard that are stored in a non-volatile memory.
- Storage medium QQ221 may be configured to include memory such as RAM, ROM, programmable read-only memory (PROM), erasable programmable read-only memory (EPROM), electrically erasable programmable read-only memory (EEPROM), magnetic disks, optical disks, floppy disks, hard disks, removable cartridges, or flash drives.
- storage medium QQ221 may be configured to include operating system QQ223, application program QQ225 such as a web browser application, a widget or gadget engine or another application, and data file QQ227.
- Storage medium QQ221 may store, for use by UE QQ200, any of a variety of various operating systems or combinations of operating systems.
- Storage medium QQ221 may be configured to include a number of physical drive units, such as redundant array of independent disks (RAID), floppy disk drive, flash memory, USB flash drive, external hard disk drive, thumb drive, pen drive, key drive, high-density digital versatile disc (HD-DVD) optical disc drive, internal hard disk drive, Blu-Ray optical disc drive, holographic digital data storage (HDDS) optical disc drive, external mini-dual in-line memory module (DIMM), synchronous dynamic random access memory (SDRAM), external micro-DIMM SDRAM, smartcard memory such as a subscriber identity module or a removable user identity (SIM/RUIM) module, other memory, or any combination thereof.
- RAID redundant array of independent disks
- HD-DVD high-density digital versatile disc
- HDDS holographic digital data storage
- DIMM external mini-dual in-line memory module
- SDRAM synchronous dynamic random access memory
- SDRAM synchronous dynamic random access memory
- smartcard memory such as a subscriber identity module or a
- Storage medium QQ221 may allow UE QQ200 to access computer-executable instructions, application programs or the like, stored on transitory or non-transitory memory media, to off-load data, or to upload data.
- An article of manufacture, such as one utilizing a communication system may be tangibly embodied in storage medium QQ221, which may comprise a device readable medium.
- processing circuitry QQ201 may be configured to communicate with network QQ243b using communication subsystem QQ231.
- Network QQ243a and network QQ243b may be the same network or networks or different network or networks.
- Communication subsystem QQ231 may be configured to include one or more transceivers used to communicate with network QQ243b.
- communication subsystem QQ231 may be configured to include one or more transceivers used to communicate with one or more remote transceivers of another device capable of wireless communication such as another WD, UE, or base station of a radio access network (RAN) according to one or more communication protocols, such as IEEE 802.QQ2, CDMA, WCDMA, GSM, LTE, UTRAN, WiMax, or the like.
- RAN radio access network
- Each transceiver may include transmitter QQ233 and/or receiver QQ235 to implement transmitter or receiver functionality, respectively, appropriate to the RAN links (e.g., frequency allocations and the like). Further, transmitter QQ233 and receiver QQ235 of each transceiver may share circuit components, software or firmware, or alternatively may be implemented separately.
- the communication functions of communication subsystem QQ231 may include data communication, voice communication, multimedia communication, short-range communications such as Bluetooth, near-field communication, location-based communication such as the use of the global positioning system (GPS) to determine a location, another like communication function, or any combination thereof.
- communication subsystem QQ231 may include cellular communication, Wi-Fi communication, Bluetooth communication, and GPS communication.
- Network QQ243b may encompass wired and/or wireless networks such as a local-area network (LAN), a wide-area network (WAN), a computer network, a wireless network, a telecommunications network, another like network or any combination thereof.
- network QQ243b may be a cellular network, a Wi-Fi network, and/or a near-field network.
- Power source QQ213 may be configured to provide alternating current (AC) or direct current (DC) power to components of UE QQ200.
- communication subsystem QQ231 may be configured to include any of the components described herein.
- processing circuitry QQ201 may be configured to communicate with any of such components over bus QQ202.
- any of such components may be represented by program instructions stored in memory that when executed by processing circuitry QQ201 perform the corresponding functions described herein.
- the functionality of any of such components may be partitioned between processing circuitry QQ201 and communication subsystem QQ231.
- the non-computationally intensive functions of any of such components may be implemented in software or firmware and the computationally intensive functions may be implemented in hardware.
- FIG. 17 is a schematic block diagram illustrating an example of a virtualization environment QQ300 in which functions implemented by some embodiments may be virtualized.
- virtualizing means creating virtual versions of apparatuses or devices which may include virtualizing hardware platforms, storage devices and networking resources.
- virtualization can be applied to a node (e.g., a virtualized base station or a virtualized radio access node) or to a device (e.g., a UE, a wireless device or any other type of communication device) or components thereof and relates to an implementation in which at least a portion of the functionality is implemented as one or more virtual components (e.g., via one or more applications, components, functions, virtual machines or containers executing on one or more physical processing nodes in one or more networks).
- a node e.g., a virtualized base station or a virtualized radio access node
- a device e.g., a UE, a wireless device or any other type of communication device
- some or all of the functions described herein may be implemented as virtual components executed by one or more virtual machines implemented in one or more virtual environments QQ300 hosted by one or more of hardware nodes QQ330. Further, in embodiments in which the virtual node is not a radio access node or does not require radio connectivity (e.g., a core network node), then the network node may be entirely virtualized.
- the functions may be implemented by one or more applications QQ320 (which may alternatively be called software instances, virtual appliances, network functions, virtual nodes, virtual network functions, etc.) operative to implement some of the features, functions, and/or benefits of some of the embodiments disclosed herein.
- Applications QQ320 are run in virtualization environment QQ300 which provides hardware QQ330 comprising processing circuitry QQ360 and memory QQ390.
- Memory QQ390 contains instructions QQ395 executable by processing circuitry QQ360 whereby application QQ320 is operative to provide one or more of the features, benefits, and/or functions disclosed herein.
- Virtualization environment QQ300 comprises general-purpose or special-purpose network hardware devices QQ330 comprising a set of one or more processors or processing circuitry QQ360, which may be commercial off-the-shelf (COTS) processors, dedicated Application Specific Integrated Circuits (ASICs), or any other type of processing circuitry including digital or analog hardware components or special purpose processors.
- Each hardware device may comprise memory QQ390-1 which may be non-persistent memory for temporarily storing instructions QQ395 or software executed by processing circuitry QQ360.
- Each hardware device may comprise one or more network interface controllers (NICs) QQ370, also known as network interface cards, which include physical network interface QQ380.
- NICs network interface controllers
- Each hardware device may also include non-transitory, persistent, machine-readable storage media QQ390-2 having stored therein software QQ395 and/or instructions executable by processing circuitry QQ360.
- Software QQ395 may include any type of software including software for instantiating one or more virtualization layers QQ350 (also referred to as hypervisors), software to execute virtual machines QQ340 as well as software allowing it to execute functions, features and/or benefits described in relation with some embodiments described herein.
- Virtual machines QQ340 comprise virtual processing, virtual memory, virtual networking or interface and virtual storage, and may be run by a corresponding virtualization layer QQ350 or hypervisor. Different embodiments of the instance of virtual appliance QQ320 may be implemented on one or more of virtual machines QQ340, and the implementations may be made in different ways.
- processing circuitry QQ360 executes software QQ395 to instantiate the hypervisor or virtualization layer QQ350, which may sometimes be referred to as a virtual machine monitor (VMM).
- Virtualization layer QQ350 may present a virtual operating platform that appears like networking hardware to virtual machine QQ340.
- hardware QQ330 may be a standalone network node with generic or specific components. Hardware QQ330 may comprise antenna QQ3225 and may implement some functions via virtualization. Alternatively, hardware QQ330 may be part of a larger cluster of hardware (e.g. such as in a data center or customer premise equipment (CPE)) where many hardware nodes work together and are managed via management and orchestration (MANO) QQ3100, which, among others, oversees lifecycle management of applications QQ320.
- CPE customer premise equipment
- NFV network function virtualization
- NFV may be used to consolidate many network equipment types onto industry standard high volume server hardware, physical switches, and physical storage, which can be located in data centers, and customer premise equipment.
- virtual machine QQ340 may be a software implementation of a physical machine that runs programs as if they were executing on a physical, non-virtualized machine.
- Each of virtual machines QQ340, and that part of hardware QQ330 that executes that virtual machine be it hardware dedicated to that virtual machine and/or hardware shared by that virtual machine with others of the virtual machines QQ340, forms a separate virtual network elements (VNE).
- VNE virtual network elements
- VNF Virtual Network Function
- one or more radio units QQ3200 that each include one or more transmitters QQ3220 and one or more receivers QQ3210 may be coupled to one or more antennas QQ3225.
- Radio units QQ3200 may communicate directly with hardware nodes QQ330 via one or more appropriate network interfaces and may be used in combination with the virtual components to provide a virtual node with radio capabilities, such as a radio access node or a base station.
- control system QQ3230 which may alternatively be used for communication between the hardware nodes QQ330 and radio units QQ3200.
- FIG. 18 is a schematic diagram illustrating an example of a telecommunication network connected via an intermediate network to a host computer in accordance with some embodiments.
- a communication system includes telecommunication network QQ410, such as a 3GPP-type cellular network, which comprises access network QQ411, such as a radio access network, and core network QQ414.
- Access network QQ411 comprises a plurality of base stations QQ412a, QQ412b, QQ412c, such as NBs, eNBs, gNBs or other types of wireless access points, each defining a corresponding coverage area QQ413a, QQ413b, QQ413c.
- Each base station QQ412a, QQ412b, QQ412c is connectable to core network QQ414 over a wired or wireless connection QQ415.
- a first UE QQ491 located in coverage area QQ413c is configured to wirelessly connect to, or be paged by, the corresponding base station QQ412c.
- a second UE QQ492 in coverage area QQ413a is wirelessly connectable to the corresponding base station QQ412a. While a plurality of UEs QQ491, QQ492 are illustrated in this example, the disclosed embodiments are equally applicable to a situation where a sole UE is in the coverage area or where a sole UE is connecting to the corresponding base station QQ412.
- Telecommunication network QQ410 is itself connected to host computer QQ430, which may be embodied in the hardware and/or software of a standalone server, a cloud-implemented server, a distributed server or as processing resources in a server farm.
- Host computer QQ430 may be under the ownership or control of a service provider, or may be operated by the service provider or on behalf of the service provider.
- Connections QQ421 and QQ422 between telecommunication network QQ410 and host computer QQ430 may extend directly from core network QQ414 to host computer QQ430 or may go via an optional intermediate network QQ420.
- Intermediate network QQ420 may be one of, or a combination of more than one of, a public, private or hosted network; intermediate network QQ420, if any, may be a backbone network or the Internet; in particular, intermediate network QQ420 may comprise two or more sub-networks (not shown).
- the communication system of FIG. 18 as a whole enables connectivity between the connected UEs QQ491, QQ492 and host computer QQ430.
- the connectivity may be described as an over-the-top (OTT) connection QQ450.
- Host computer QQ430 and the connected UEs QQ491, QQ492 are configured to communicate data and/or signaling via OTT connection QQ450, using access network QQ411, core network QQ414, any intermediate network QQ420 and possible further infrastructure (not shown) as intermediaries.
- OTT connection QQ450 may be transparent in the sense that the participating communication devices through which OTT connection QQ450 passes are unaware of routing of uplink and downlink communications.
- base station QQ412 may not or need not be informed about the past routing of an incoming downlink communication with data originating from host computer QQ430 to be forwarded (e.g., handed over) to a connected UE QQ491.
- base station QQ412 need not be aware of the future routing of an outgoing uplink communication originating from the UE QQ491 towards the host computer QQ430.
- FIG. 19 is a schematic diagram illustrating an example of a host computer communicating via a base station with a user equipment over a partially wireless connection in accordance with some embodiments
- host computer QQ510 comprises hardware QQ515 including communication interface QQ516 configured to set up and maintain a wired or wireless connection with an interface of a different communication device of communication system QQ500.
- Host computer QQ510 further comprises processing circuitry QQ518, which may have storage and/or processing capabilities.
- processing circuitry QQ518 may comprise one or more programmable processors, application-specific integrated circuits, field programmable gate arrays or combinations of these (not shown) adapted to execute instructions.
- Host computer QQ510 further comprises software QQ511, which is stored in or accessible by host computer QQ510 and executable by processing circuitry QQ518.
- Software QQ511 includes host application QQ512.
- Host application QQ512 may be operable to provide a service to a remote user, such as UE QQ530 connecting via OTT connection QQ550 terminating at UE QQ530 and host computer QQ510. In providing the service to the remote user, host application QQ512 may provide user data which is transmitted using OTT connection QQ550.
- Communication system QQ500 further includes base station QQ520 provided in a telecommunication system and comprising hardware QQ525 enabling it to communicate with host computer QQ510 and with UE QQ530.
- Hardware QQ525 may include communication interface QQ526 for setting up and maintaining a wired or wireless connection with an interface of a different communication device of communication system QQ500, as well as radio interface QQ527 for setting up and maintaining at least wireless connection QQ570 with UE QQ530 located in a coverage area (not shown in FIG. 19 ) served by base station QQ520.
- Communication interface QQ526 may be configured to facilitate connection QQ560 to host computer QQ510.
- Connection QQ560 may be direct or it may pass through a core network (not shown in FIG.
- hardware QQ525 of base station QQ520 further includes processing circuitry QQ528, which may comprise one or more programmable processors, application-specific integrated circuits, field programmable gate arrays or combinations of these (not shown) adapted to execute instructions.
- Base station QQ520 further has software QQ521 stored internally or accessible via an external connection.
- Communication system QQ500 further includes UE QQ530 already referred to.
- the hardware QQ535 may include radio interface QQ537 configured to set up and maintain wireless connection QQ570 with a base station serving a coverage area in which UE QQ530 is currently located.
- Hardware QQ535 of UE QQ530 further includes processing circuitry QQ538, which may comprise one or more programmable processors, application-specific integrated circuits, field programmable gate arrays or combinations of these (not shown) adapted to execute instructions.
- UE QQ530 further comprises software QQ531, which is stored in or accessible by UE QQ530 and executable by processing circuitry QQ538.
- Software QQ531 includes client application QQ532.
- Client application QQ532 may be operable to provide a service to a human or non-human user via UE QQ530, with the support of host computer QQ510.
- an executing host application QQ512 may communicate with the executing client application QQ532 via OTT connection QQ550 terminating at UE QQ530 and host computer QQ510.
- client application QQ532 may receive request data from host application QQ512 and provide user data in response to the request data.
- OTT connection QQ550 may transfer both the request data and the user data.
- Client application QQ532 may interact with the user to generate the user data that it provides.
- host computer QQ510, base station QQ520 and UE QQ530 illustrated in FIG. 19 may be similar or identical to host computer QQ430, one of base stations QQ412a, QQ412b, QQ412c and one of UEs QQ491, QQ492 of FIG. 18 , respectively.
- the inner workings of these entities may be as shown in FIG. 19 and independently, the surrounding network topology may be that of FIG. 18 .
- OTT connection QQ550 has been drawn abstractly to illustrate the communication between host computer QQ510 and UE QQ530 via base station QQ520, without explicit reference to any intermediary devices and the precise routing of messages via these devices.
- Network infrastructure may determine the routing, which it may be configured to hide from UE QQ530 or from the service provider operating host computer QQ510, or both. While OTT connection QQ550 is active, the network infrastructure may further take decisions by which it dynamically changes the routing (e.g., on the basis of load balancing consideration or reconfiguration of the network).
- Wireless connection QQ570 between UE QQ530 and base station QQ520 is in accordance with the teachings of the embodiments described throughout this disclosure.
- One or more of the various embodiments improve the performance of OTT services provided to UE QQ530 using OTT connection QQ550, in which wireless connection QQ570 forms the last segment.
- a measurement procedure may be provided for the purpose of monitoring data rate, latency and other factors on which the one or more embodiments improve.
- the measurement procedure and/or the network functionality for reconfiguring OTT connection QQ550 may be implemented in software QQ511 and hardware QQ515 of host computer QQ510 or in software QQ531 and hardware QQ535 of UE QQ530, or both.
- sensors may be deployed in or in association with communication devices through which OTT connection QQ550 passes; the sensors may participate in the measurement procedure by supplying values of the monitored quantities exemplified above, or supplying values of other physical quantities from which software QQ511, QQ531 may compute or estimate the monitored quantities.
- the reconfiguring of OTT connection QQ550 may include message format, retransmission settings, preferred routing etc.; the reconfiguring need not affect base station QQ520, and it may be unknown or imperceptible to base station QQ520. Such procedures and functionalities may be known and practiced in the art.
- measurements may involve proprietary UE signaling facilitating host computer QQ510's measurements of throughput, propagation times, latency and the like. The measurements may be implemented in that software QQ511 and QQ531 causes messages to be transmitted, in particular empty or 'dummy' messages, using OTT connection QQ550 while it monitors propagation times, errors etc.
- FIGs. 20A-B are schematic flow diagrams illustrating examples of methods implemented in a communication system including, e.g. a host computer, and optionally also a base station and a user equipment in accordance with some embodiments.
- FIG. 20A is a flowchart illustrating a method implemented in a communication system, in accordance with one embodiment.
- the communication system includes a host computer, a base station and a UE which may be those described with reference to FIG. 18 and FIG. 19 .
- the host computer provides user data.
- substep QQ611 (which may be optional) of step QQ610, the host computer provides the user data by executing a host application.
- step QQ620 the host computer initiates a transmission carrying the user data to the UE.
- step QQ630 the base station transmits to the UE the user data which was carried in the transmission that the host computer initiated, in accordance with the teachings of the embodiments described throughout this disclosure.
- step QQ640 the UE executes a client application associated with the host application executed by the host computer.
- FIG. 20B is a flowchart illustrating a method implemented in a communication system, in accordance with one embodiment.
- the communication system includes a host computer, a base station and a UE which may be those described with reference to FIG. 18 and FIG. 19 .
- the host computer provides user data.
- the host computer provides the user data by executing a host application.
- the host computer initiates a transmission carrying the user data to the UE.
- the transmission may pass via the base station, in accordance with the teachings of the embodiments described throughout this disclosure.
- step QQ730 (which may be optional), the UE receives the user data carried in the transmission.
- FIGs. 21A-B are schematic diagrams illustrating examples of methods implemented in a communication system including a host computer, a base station and a user equipment in accordance with some embodiments.
- FIG. 21A is a flowchart illustrating a method implemented in a communication system, in accordance with one embodiment.
- the communication system includes a host computer, a base station and a UE which may be those described with reference to FIG. 18 and FIG. 19 .
- the UE receives input data provided by the host computer.
- the UE provides user data.
- substep QQ821 (which may be optional) of step QQ820, the UE provides the user data by executing a client application.
- substep QQ811 (which may be optional) of step QQ810, the UE executes a client application which provides the user data in reaction to the received input data provided by the host computer. In providing the user data, the executed client application may further consider user input received from the user. Regardless of the specific manner in which the user data was provided, the UE initiates, in substep QQ830 (which may be optional), transmission of the user data to the host computer. In step QQ840 of the method, the host computer receives the user data transmitted from the UE, in accordance with the teachings of the embodiments described throughout this disclosure.
- FIG. 21 B is a flowchart illustrating a method implemented in a communication system, in accordance with one embodiment.
- the communication system includes a host computer, a base station and a UE which may be those described with reference to FIG. 18 and FIG. 19 .
- the base station receives user data from the UE.
- the base station initiates transmission of the received user data to the host computer.
- the host computer receives the user data carried in the transmission initiated by the base station.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Computer Security & Cryptography (AREA)
- Databases & Information Systems (AREA)
- Computer Hardware Design (AREA)
- Computing Systems (AREA)
- General Engineering & Computer Science (AREA)
- Mobile Radio Communication Systems (AREA)
Claims (19)
- Procédé de détermination d'un contexte de sécurité dans une communication entre un dispositif sans fil et une station de base cible lors d'un transfert intercellulaire au sein du même réseau central, dans lequel le réseau central est un réseau central 5G qui prend en charge un réseau d'accès radio NG, NG-RAN et le NG-RAN comprend à la fois gNB, qui est une station de base de type nouvelle radio, NR, appartenant au 5G, et ng-eNB, qui est une station de base de type E-UTRA / LTE appartenant au 4G, et le procédé est appliquée lors de transferts intercellulaires intra-RAT et / ou des inter-RAT entre deux gNB, entre deux ng-eNB, ou entre une gNB et une ng-eNB au sein du même réseau central, de sorte que la station de base cible est soit une gNB, soit une ng-eNB, et le type de RAT est représentatif de nouvelle radio, NR, ou évolution à long terme, LTE, dans lequel le procédé est caractérisé par :- l'obtention (S1) d'informations représentatives du type de technologie d'accès radio, également appelé type de RAT, de la station de base cible ; et- la dérivation (S2) et / ou la détermination du contexte de sécurité au moins en partie sur la base des informations représentatives du type de RAT de la station de base cible, dans lequel le contexte de sécurité comprend au moins une clé de sécurité de base de strate d'accès, AS,
dans lequel l'étape (S2) de dérivation et / ou de détermination du contexte de sécurité comprend la dérivation de la clé de sécurité de base AS en utilisant une fonction de dérivation de clé (KDF) qui dépend du type de RAT de la station de base cible, le type de RAT étant codé en la fonction de dérivation de clé, KDF, en utilisant deux valeurs différentes d'un paramètre de code de fonction comme entrée dans une KDF générique, créant ainsi deux KDF différentes, une pour évolution à long terme, LTE, et une pour nouvelle radio, NR. - Procédé selon la revendication 1, dans lequel la clé de sécurité de base AS est KgNB* ou Kng-eNB*.
- Procédé selon l'une quelconque des revendications 1 à 2, dans lequel les informations représentatives du type de RAT sont obtenues en recevant les informations et / ou en déterminant les informations.
- Procédé selon l'une quelconque des revendications 1 à 3, dans lequel les informations représentatives du type de RAT sont utilisées conjointement avec des informations représentatives d'une clé de sécurité valide avant le transfert intercellulaire pour dériver une nouvelle clé de sécurité.
- Procédé selon la revendication 4, dans lequel les informations représentatives d'une clé de sécurité valide avant le transfert intercellulaire comprennent des informations sur une clé de sécurité de base utilisée avant le transfert intercellulaire, ou une clé intermédiaire valide avant le transfert intercellulaire.
- Procédé selon l'une quelconque des revendications 1 à 5, dans lequel les informations représentatives du type de RAT de la station de base cible sont utilisées conjointement avec des informations représentant des propriétés supplémentaires de la cellule cible dans la dérivation de clé (10).
- Procédé selon l'une quelconque des revendications 1 à 6, dans lequel le procédé est mis en œuvre par le dispositif sans fil.
- Procédé selon l'une quelconque des revendications 1 à 6, dans lequel le procédé est mis en œuvre par une station de base comprise dans ledit réseau d'accès radio NG, NG-RAN, pris en charge par ledit réseau central 5G.
- Procédé selon la revendication 8, dans lequel le transfert intercellulaire s'effectue à partir d'une station de base source vers la station de base cible, et le procédé est mis en œuvre par la station de base source.
- Procédé selon la revendication 9, dans lequel le transfert intercellulaire est un transfert intercellulaire Xn et les informations représentatives du type de RAT sont obtenues sur la base d'une signalisation Xn ou d'une pré-configuration.
- Procédé selon la revendication 8, dans lequel le procédé est mis en œuvre par la station de base cible.
- Procédé selon la revendication 11, dans lequel le transfert intercellulaire est un transfert intercellulaire N2 et les informations représentatives du type de RAT sont obtenues sur la base d'une signalisation N2 ou d'une pré-configuration.
- Procédé selon l'une quelconque des revendications 1 à 6, dans lequel le procédé est mis en œuvre par un dispositif de réseau de fonction de gestion d'accès et de mobilité, AMF, dans le réseau central.
- Dispositif sans fil (200) configuré pour déterminer un contexte de sécurité pour une communication entre le dispositif sans fil et une station de base cible lors d'un transfert intercellulaire au sein du même réseau central, dans lequel le réseau central est un réseau central 5G qui prend en charge un réseau d'accès radio NG, NG-RAN et le NG-RAN comprend à la fois gNB, qui est une station de base de type nouvelle radio, NR, appartenant au 5G, et ng-eNB, qui est une station de base de type E-UTRA / LTE appartenant au 4G, et dans lequel le dispositif sans fil est configuré pour déterminer le contexte de sécurité lors de transferts intercellulaires intra-RAT et / ou inter-RAT entre deux gNB, entre deux ng-eNB, ou entre une gNB et une ng-eNB au sein du même réseau central, de sorte que la station de base cible est soit une gNB, soit une ng-eNB, et le type de RAT est représentatif de nouvelle radio, NR, ou évolution à long terme, LTE, dans lequel le dispositif sans fil (200) est caractérisé en ce qu'il est configuré pour exécuter les étapes suivantes :- l'obtention d'informations représentatives du type de technologie d'accès radio, également appelé type de RAT, de la station de base cible ; et- la dérivation et / ou la détermination du contexte de sécurité au moins en partie sur la base des informations représentatives du type de RAT de la station de base cible, dans lequel le contexte de sécurité comprend au moins une clé de sécurité de base de strate d'accès, AS, et dans lequel la dérivation et / ou la détermination du contexte de sécurité comprend la dérivation de la clé de sécurité de base AS en utilisant une fonction de dérivation de clé (KDF) qui dépend du type de RAT de la station de base cible, le type de RAT étant codé en la fonction de dérivation de clé, KDF, en utilisant deux valeurs différentes d'un paramètre de code de fonction comme entrée dans une KDF générique, créant ainsi deux KDF différentes, une pour évolution à long terme, LTE, et une pour nouvelle radio, NR.
- Dispositif sans fil selon la revendication 14, dans lequel le dispositif sans fil (200) comprend un processeur et une mémoire, la mémoire comprenant des instructions exécutables par le processeur, moyennant quoi le processeur est opérationnel pour dériver et / ou déterminer le contexte de sécurité.
- Station de base (200) configurée pour déterminer un contexte de sécurité dans une communication entre un dispositif sans fil et une station de base cible lors d'un transfert intercellulaire au sein du même réseau central, dans lequel le réseau central est un réseau central 5G qui prend en charge un réseau d'accès radio NG, NG-RAN et le NG-RAN comprend à la fois gNB, qui est une station de base de type nouvelle radio, NR, appartenant au 5G, et ng-eNB, qui est une station de base de type E-UTRA / LTE appartenant au 4G, et dans lequel le dispositif sans fil est configuré pour déterminer le contexte de sécurité lors de transferts intercellulaires intra-RAT et / ou inter-RAT entre deux gNB, entre deux ng-eNB, ou entre une gNB et une ng-eNB au sein du même réseau central, de sorte que la station de base cible est soit une gNB, soit une ng-eNB, et le type de RAT est représentatif de nouvelle radio, NR, ou évolution à long terme, LTE, dans lequel la station de base (200) est caractérisée en ce qu'elle est configurée pour exécuter les étapes suivantes :- l'obtention d'informations représentatives du type de technologie d'accès radio, également appelé type de RAT, de la station de base cible ; et- la dérivation et / ou la détermination du contexte de sécurité au moins en partie sur la base des informations représentatives du type de RAT de la station de base cible, dans lequel le contexte de sécurité comprend au moins une clé de sécurité de base de strate d'accès, AS ; et dans lequel la dérivation et / ou la détermination du contexte de sécurité comprend la dérivation de la clé de sécurité de base AS en utilisant une fonction de dérivation de clé (KDF) qui dépend du type de RAT de la station de base cible, le type de RAT étant codé en la fonction de dérivation de clé, KDF, en utilisant deux valeurs différentes d'un paramètre de code de fonction comme entrée dans une KDF générique, créant ainsi deux KDF différentes, une pour évolution à long terme, LTE, et une pour nouvelle radio, NR.
- Dispositif de réseau de fonction de gestion d'accès et de mobilité, AMF, dans un réseau central, configuré pour déterminer un contexte de sécurité dans une communication entre un dispositif sans fil et une station de base cible lors d'un transfert intercellulaire au sein du même réseau central, dans lequel le réseau central est un réseau central 5G qui prend en charge un réseau d'accès radio NG, NG-RAN et le NG-RAN comprend à la fois gNB, qui est une station de base de type nouvelle radio, NR, appartenant au 5G, et ng-eNB, qui est une station de base de type E-UTRA / LTE appartenant au 4G, et dans lequel le dispositif de réseau AMF est configuré pour déterminer le contexte de sécurité lors de transferts intercellulaires intra-RAT et / ou inter-RAT entre deux gNB, entre deux ng-eNB, ou entre un gNB et un ng-eNB au sein du même réseau central, de sorte que la station de base cible est soit une gNB, soit une ng-eNB, et le type de RAT est représentatif de nouvelle radio, NR, ou évolution à long terme, LTE,
dans lequel le dispositif de réseau AMF (200) est caractérisé en ce que le dispositif de réseau AMF est configuré pour exécuter les étapes suivantes :- l'obtention d'informations représentatives du type de technologie d'accès radio, également appelé type de RAT, de la station de base cible ; et- la dérivation et / ou la détermination du contexte de sécurité au moins en partie sur la base des informations représentatives du type de RAT de la station de base cible, dans lequel le contexte de sécurité comprend au moins une clé de sécurité de base de strate d'accès, AS ; et dans lequel la dérivation et / ou la détermination du contexte de sécurité comprend la dérivation de la clé de sécurité de base AS en utilisant une fonction de dérivation de clé (KDF) qui dépend du type de RAT de la station de base cible, le type de RAT étant codé en la fonction de dérivation de clé, KDF, en utilisant deux valeurs différentes d'un paramètre de code de fonction comme entrée dans un KDF générique, créant ainsi deux KDF différents, l'un pour évolution à long terme, LTE, et un pour nouvelle radio, NR. - Programme informatique (325 ; 335) pour déterminer, lorsqu'il est exécuté, un contexte de sécurité pour une communication entre un dispositif sans fil et une station de base cible lors d'un transfert intercellulaire au sein du même réseau central, et le réseau central est un réseau central 5G qui prend en charge un réseau d'accès radio NG, NG-RAN et le NG-RAN comprend à la fois gNB, qui est une station de base de type nouvelle radio, NR, appartenant au 5G, et ng-eNB, qui est une station de base de type E-UTRA / LTE appartenant au 4G, de sorte que la station de base cible est soit une gNB, soit une ng-eNB, dans lequel le programme informatique est caractérisé en ce qu'il comprend des instructions qui, lorsqu'elles sont exécutées par au moins un processeur (310), amènent l'au moins un processeur (310) à :- obtenir des informations représentatives du type de technologie d'accès radio, également appelé type de RAT, de la station de base cible ;- - dériver et / ou déterminer, lors de transferts intercellulaires intra-RAT et / ou inter-RAT entre deux gNB, entre deux ng-eNB, ou entre un gNB et un ng-eNB au sein d'un même réseau central, le contexte de sécurité étant au moins en partie basé sur les informations représentatives du type de RAT de la station de base cible, dans lequel le contexte de sécurité comprend au moins une clé de sécurité de base de strate d'accès, AS, et le réseau central est un réseau central 5G, et le type de RAT est représentatif de nouvelle radio, NR, ou évolution à long terme, LTE, etdans lequel le programme informatique comprend des instructions qui, lorsqu'elles sont exécutées par au moins un processeur (310), amènent l'au moins un processeur (310) à dériver et / ou déterminer le contexte de sécurité, qui comprend la dérivation de la clé de sécurité de base AS en utilisant une fonction de dérivation de clé (KDF) qui dépend du type de RAT de la station de base cible, le type de RAT étant codé en la fonction de dérivation de clé, KDF, en utilisant deux valeurs différentes d'un paramètre de code de fonction comme entrée dans une KDF générique, créant ainsi deux KDF différentes, une pour évolution à long terme, LTE, et une pour nouvelle radio, NR.
- Produit de programme informatique (320 ; 330) comprenant un support lisible par ordinateur sur lequel est stocké un programme informatique (325 ; 335) selon la revendication 18.
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| EP22168417.8A EP4047865A1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US201762563210P | 2017-09-26 | 2017-09-26 | |
| PCT/SE2018/050390 WO2019066692A1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
Related Child Applications (2)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| EP22168417.8A Division-Into EP4047865A1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
| EP22168417.8A Division EP4047865A1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| EP3688949A1 EP3688949A1 (fr) | 2020-08-05 |
| EP3688949B1 true EP3688949B1 (fr) | 2022-06-08 |
Family
ID=62063587
Family Applications (2)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| EP22168417.8A Pending EP4047865A1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
| EP18720674.3A Active EP3688949B1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
Family Applications Before (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| EP22168417.8A Pending EP4047865A1 (fr) | 2017-09-26 | 2018-04-18 | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil |
Country Status (6)
| Country | Link |
|---|---|
| US (1) | US11122427B2 (fr) |
| EP (2) | EP4047865A1 (fr) |
| JP (1) | JP7232250B2 (fr) |
| CN (2) | CN111133732B (fr) |
| PL (1) | PL3688949T3 (fr) |
| WO (1) | WO2019066692A1 (fr) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20220191759A1 (en) * | 2018-04-05 | 2022-06-16 | Telefonaktiebolaget Lm Ericsson (Publ) | INTRA-RAT Handovers with Core Network Change |
Families Citing this family (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN111133732B (zh) * | 2017-09-26 | 2022-10-04 | 瑞典爱立信有限公司 | 在无线通信系统中切换时管理安全上下文并执行密钥导出 |
| US11553381B2 (en) * | 2018-01-12 | 2023-01-10 | Qualcomm Incorporated | Method and apparatus for multiple registrations |
| WO2020070652A1 (fr) * | 2018-10-03 | 2020-04-09 | Telefonaktiebolaget Lm Ericsson (Publ) | Compression de données d'utilisateur transmises entre une unité centrale séparée de couche inférieure et une unité radio en utilisant des représentations en mode points |
| US11089524B2 (en) * | 2019-01-31 | 2021-08-10 | Corning Optical Communications LLC | Automatic cell discovery of a source radio access network (RAN) cell by a neighboring, target ran by initiating a fake handover of a user equipment (UE) from the source RAN cell to the target RAN |
| US11540182B2 (en) * | 2019-10-01 | 2022-12-27 | Qualcomm Incorporated | Absolute radio frequency channel number for security key generation |
| CN116601985A (zh) * | 2020-12-25 | 2023-08-15 | 华为技术有限公司 | 一种安全上下文生成方法、装置及计算机可读存储介质 |
Family Cites Families (37)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN101779516A (zh) * | 2007-08-10 | 2010-07-14 | 三菱电机株式会社 | 无线通信系统以及基站 |
| US8346257B2 (en) * | 2007-09-26 | 2013-01-01 | Telefonaktiebolaget Lm Ericsson (Publ) | Selecting a cell associated with a radio access technology |
| US8559387B2 (en) * | 2009-05-04 | 2013-10-15 | Blackberry Limited | Indicating radio access technology information to mobile stations system and method |
| UA102039C2 (ru) * | 2009-09-29 | 2013-05-27 | Нокиа Корпорэйшн | Способ и устройство для идентификации источника для обработки ключа после ошибки хендовера |
| US9775027B2 (en) | 2009-12-31 | 2017-09-26 | Alcatel Lucent | Method for interworking among wireless technologies |
| US9084110B2 (en) * | 2010-04-15 | 2015-07-14 | Qualcomm Incorporated | Apparatus and method for transitioning enhanced security context from a UTRAN/GERAN-based serving network to an E-UTRAN-based serving network |
| US10075420B2 (en) * | 2010-05-04 | 2018-09-11 | Qualcomm Incorporated | Shared circuit switched security context |
| CN103650626B (zh) * | 2011-07-12 | 2018-05-15 | 交互数字专利控股公司 | 用于多rat接入模式操作的方法和设备 |
| KR102013540B1 (ko) * | 2011-07-29 | 2019-08-22 | 인터디지탈 패튼 홀딩스, 인크 | 다중 무선 액세스 기술 무선 시스템에서 무선 자원 관리를 위한 방법 및 장치 |
| CN103167492B (zh) * | 2011-12-15 | 2016-03-30 | 华为技术有限公司 | 在通信系统中生成接入层密钥的方法及其设备 |
| US10433161B2 (en) * | 2012-01-30 | 2019-10-01 | Telefonaktiebolaget Lm Ericsson (Publ) | Call handover between cellular communication system nodes that support different security contexts |
| US9161281B2 (en) * | 2012-06-08 | 2015-10-13 | Blackberry Limited | Method and apparatus for multi-rat transmission |
| CN105230103B (zh) * | 2013-05-17 | 2019-07-12 | 寰发股份有限公司 | 上报bsr的方法以及用户设备 |
| WO2015013879A1 (fr) * | 2013-07-30 | 2015-02-05 | 华为技术有限公司 | Procédé, appareil, dispositif et système de commutation de réseau |
| KR102196213B1 (ko) * | 2013-09-11 | 2020-12-31 | 삼성전자 주식회사 | 기지국 상호간 전송을 위한 보안 통신을 가능하게 하는 방법 및 시스템 |
| KR102131233B1 (ko) * | 2014-02-19 | 2020-07-07 | 콘비다 와이어리스, 엘엘씨 | 시스템 간 이동성을 위한 서빙 게이트웨이 확장들 |
| EP3886397B1 (fr) * | 2014-03-21 | 2023-01-18 | Sun Patent Trust | Dérivation de clés de sécurité à connectivité double |
| EP3843500A1 (fr) * | 2014-07-14 | 2021-06-30 | Convida Wireless, LLC | Transfert et multi-connectabilité entre systèmes par l'intermédiaire d'une passerelle intégrée de petite cellule et wi-fi |
| CN107079509A (zh) * | 2014-11-07 | 2017-08-18 | 瑞典爱立信有限公司 | 用于暂停和恢复ran‑cn连接的方法、ran节点和移动性管理节点 |
| CN106134231B (zh) * | 2015-02-28 | 2019-10-01 | 华为技术有限公司 | 密钥生成方法、设备及系统 |
| US10028307B2 (en) * | 2016-01-13 | 2018-07-17 | Qualcomm Incorporated | Configurable access stratum security |
| WO2017171354A1 (fr) * | 2016-03-28 | 2017-10-05 | 엘지전자 주식회사 | Procédé et dispositif par lesquels un terminal réalise une mobilité |
| US10257078B2 (en) * | 2016-04-01 | 2019-04-09 | Qualcomm Incorporated | Interworking with legacy radio access technologies for connectivity to next generation core network |
| US10638388B2 (en) * | 2016-08-05 | 2020-04-28 | Qualcomm Incorporated | Techniques for fast transition of a connection between a wireless device and a local area network, from a source access node to a target access node |
| CN112672343B (zh) * | 2016-08-09 | 2022-04-26 | 三星电子株式会社 | 无线通信系统中管理用户平面操作的方法和装置 |
| WO2018029931A1 (fr) * | 2016-08-10 | 2018-02-15 | 日本電気株式会社 | Nœud de réseau d'accès sans fil, terminal sans fil, nœud de réseau central, et procédés associés |
| WO2018056957A1 (fr) * | 2016-09-20 | 2018-03-29 | Nokia Solutions And Networks Oy | Identificateur d'ensemble de clés de prochaine génération |
| WO2018079692A1 (fr) * | 2016-10-26 | 2018-05-03 | 日本電気株式会社 | Système de communication , station de base, procédé de commande, et support lisible par ordinateur |
| EP3550889A4 (fr) * | 2016-12-29 | 2019-10-09 | LG Electronics Inc. -1- | Procédé et appareil de prise en charge d'un faisceau dans un système de communication sans fil |
| KR102289879B1 (ko) * | 2017-03-20 | 2021-08-13 | 삼성전자 주식회사 | 셀룰러망에서 세션의 다양한 ssc 모드 지원을 위한 upf 변경 방안 |
| WO2018203300A1 (fr) * | 2017-05-05 | 2018-11-08 | Telefonaktiebolaget Lm Ericsson (Publ) | Porteuse radio à signalisation divisée dans un transfert intercellulaire |
| US10841302B2 (en) * | 2017-05-24 | 2020-11-17 | Lg Electronics Inc. | Method and apparatus for authenticating UE between heterogeneous networks in wireless communication system |
| US11616768B2 (en) * | 2017-06-23 | 2023-03-28 | Motorola Mobility Llc | Method and apparatus for handling security keys for individual bearers |
| US11071021B2 (en) * | 2017-07-28 | 2021-07-20 | Qualcomm Incorporated | Security key derivation for handover |
| CN109309920B (zh) * | 2017-07-28 | 2021-09-21 | 华为技术有限公司 | 安全实现方法、相关装置以及系统 |
| US10893568B2 (en) * | 2017-08-18 | 2021-01-12 | Huawei Technologies Co., Ltd. | Location and context management in a RAN INACTIVE mode |
| CN111133732B (zh) * | 2017-09-26 | 2022-10-04 | 瑞典爱立信有限公司 | 在无线通信系统中切换时管理安全上下文并执行密钥导出 |
-
2018
- 2018-04-18 CN CN201880062660.9A patent/CN111133732B/zh active Active
- 2018-04-18 EP EP22168417.8A patent/EP4047865A1/fr active Pending
- 2018-04-18 WO PCT/SE2018/050390 patent/WO2019066692A1/fr unknown
- 2018-04-18 CN CN202211127685.7A patent/CN115767525A/zh active Pending
- 2018-04-18 JP JP2020517529A patent/JP7232250B2/ja active Active
- 2018-04-18 US US16/067,256 patent/US11122427B2/en active Active
- 2018-04-18 EP EP18720674.3A patent/EP3688949B1/fr active Active
- 2018-04-18 PL PL18720674.3T patent/PL3688949T3/pl unknown
Cited By (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20220191759A1 (en) * | 2018-04-05 | 2022-06-16 | Telefonaktiebolaget Lm Ericsson (Publ) | INTRA-RAT Handovers with Core Network Change |
| US11638191B2 (en) * | 2018-04-05 | 2023-04-25 | Telefonaktiebolaget Lm Ericsson (Publ) | Intra-RAT handovers with core network change |
Also Published As
| Publication number | Publication date |
|---|---|
| PL3688949T3 (pl) | 2022-10-31 |
| US11122427B2 (en) | 2021-09-14 |
| EP3688949A1 (fr) | 2020-08-05 |
| CN115767525A (zh) | 2023-03-07 |
| JP7232250B2 (ja) | 2023-03-02 |
| US20200092718A1 (en) | 2020-03-19 |
| JP2020535732A (ja) | 2020-12-03 |
| CN111133732B (zh) | 2022-10-04 |
| EP4047865A1 (fr) | 2022-08-24 |
| CN111133732A (zh) | 2020-05-08 |
| WO2019066692A1 (fr) | 2019-04-04 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US11838810B2 (en) | Report NSA/SA NR indicator | |
| EP3711361B1 (fr) | Configuration rrc complète en en-dc | |
| EP3688949B1 (fr) | Gestion de contextes de sécurité et réalisation d'une dérivation de clé lors d'un transfert intercellulaire dans un système de communications sans fil | |
| CN111566994B (zh) | 管理标识符隐私 | |
| US20220394565A1 (en) | Determining Security Keys | |
| EP4037380A1 (fr) | Procédure de mobilité | |
| EP3791682B1 (fr) | Sélection d'id de cellule dans des scénarios à multiples id de cellule | |
| US11317308B2 (en) | Update of cell quality derivation parameters | |
| WO2019072904A1 (fr) | Notification d'informations sur un type de réseau central (cn) | |
| WO2020091662A1 (fr) | Procédure de mobilité | |
| US20220015038A1 (en) | Mobile Terminated Early Data Transmission Reachability for RAN Context | |
| US20210400630A1 (en) | Methods and Apparatus for Controlling a Mode of Operation of a Wireless Device | |
| US11595929B2 (en) | Methods providing release and re-direct message contents and UE behavior and related wireless devices |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: UNKNOWN |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: THE INTERNATIONAL PUBLICATION HAS BEEN MADE |
|
| PUAI | Public reference made under article 153(3) epc to a published international application that has entered the european phase |
Free format text: ORIGINAL CODE: 0009012 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: REQUEST FOR EXAMINATION WAS MADE |
|
| 17P | Request for examination filed |
Effective date: 20200407 |
|
| AK | Designated contracting states |
Kind code of ref document: A1 Designated state(s): AL AT BE BG CH CY CZ DE DK EE ES FI FR GB GR HR HU IE IS IT LI LT LU LV MC MK MT NL NO PL PT RO RS SE SI SK SM TR |
|
| AX | Request for extension of the european patent |
Extension state: BA ME |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: EXAMINATION IS IN PROGRESS |
|
| 17Q | First examination report despatched |
Effective date: 20201022 |
|
| DAV | Request for validation of the european patent (deleted) | ||
| DAX | Request for extension of the european patent (deleted) | ||
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R079 Ref document number: 602018036483 Country of ref document: DE Free format text: PREVIOUS MAIN CLASS: H04L0029060000 Ipc: H04L0009080000 |
|
| GRAP | Despatch of communication of intention to grant a patent |
Free format text: ORIGINAL CODE: EPIDOSNIGR1 |
|
| RIC1 | Information provided on ipc code assigned before grant |
Ipc: H04W 36/00 20090101ALI20220203BHEP Ipc: H04W 36/14 20090101ALI20220203BHEP Ipc: H04W 12/04 20090101ALI20220203BHEP Ipc: H04L 9/08 20060101AFI20220203BHEP |
|
| INTG | Intention to grant announced |
Effective date: 20220301 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: GRANT OF PATENT IS INTENDED |
|
| GRAS | Grant fee paid |
Free format text: ORIGINAL CODE: EPIDOSNIGR3 |
|
| GRAA | (expected) grant |
Free format text: ORIGINAL CODE: 0009210 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: THE PATENT HAS BEEN GRANTED |
|
| AK | Designated contracting states |
Kind code of ref document: B1 Designated state(s): AL AT BE BG CH CY CZ DE DK EE ES FI FR GB GR HR HU IE IS IT LI LT LU LV MC MK MT NL NO PL PT RO RS SE SI SK SM TR |
|
| REG | Reference to a national code |
Ref country code: AT Ref legal event code: REF Ref document number: 1497679 Country of ref document: AT Kind code of ref document: T Effective date: 20220615 Ref country code: CH Ref legal event code: EP |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R096 Ref document number: 602018036483 Country of ref document: DE |
|
| REG | Reference to a national code |
Ref country code: IE Ref legal event code: FG4D |
|
| REG | Reference to a national code |
Ref country code: NL Ref legal event code: FP |
|
| GRAP | Despatch of communication of intention to grant a patent |
Free format text: ORIGINAL CODE: EPIDOSNIGR1 |
|
| REG | Reference to a national code |
Ref country code: LT Ref legal event code: MG9D |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: SE Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: NO Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220908 Ref country code: LT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: HR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: GR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220909 Ref country code: FI Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: ES Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: BG Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220908 |
|
| REG | Reference to a national code |
Ref country code: AT Ref legal event code: MK05 Ref document number: 1497679 Country of ref document: AT Kind code of ref document: T Effective date: 20220608 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: RS Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: LV Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: SM Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: SK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: RO Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: PT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20221010 Ref country code: EE Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: CZ Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: AT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: IS Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20221008 |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R097 Ref document number: 602018036483 Country of ref document: DE |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: AL Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 |
|
| PLBE | No opposition filed within time limit |
Free format text: ORIGINAL CODE: 0009261 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: NO OPPOSITION FILED WITHIN TIME LIMIT |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: DK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 |
|
| 26N | No opposition filed |
Effective date: 20230310 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: SI Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 |
|
| P01 | Opt-out of the competence of the unified patent court (upc) registered |
Effective date: 20230517 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: IT Payment date: 20230419 Year of fee payment: 6 Ref country code: IE Payment date: 20230427 Year of fee payment: 6 Ref country code: FR Payment date: 20230425 Year of fee payment: 6 Ref country code: DE Payment date: 20230427 Year of fee payment: 6 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: TR Payment date: 20230404 Year of fee payment: 6 Ref country code: PL Payment date: 20230403 Year of fee payment: 6 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: GB Payment date: 20230427 Year of fee payment: 6 |
|
| REG | Reference to a national code |
Ref country code: CH Ref legal event code: PL |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: LU Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20230418 |
|
| REG | Reference to a national code |
Ref country code: BE Ref legal event code: MM Effective date: 20230430 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: MC Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: MC Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20220608 Ref country code: LI Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20230430 Ref country code: CH Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20230430 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: BE Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20230430 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: NL Payment date: 20240426 Year of fee payment: 7 |