CN106295353B - Engine vulnerability detection method and detection device - Google Patents
Engine vulnerability detection method and detection device Download PDFInfo
- Publication number
- CN106295353B CN106295353B CN201610643329.9A CN201610643329A CN106295353B CN 106295353 B CN106295353 B CN 106295353B CN 201610643329 A CN201610643329 A CN 201610643329A CN 106295353 B CN106295353 B CN 106295353B
- Authority
- CN
- China
- Prior art keywords
- application
- programming interface
- api
- application programming
- detected
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/57—Certifying or maintaining trusted computer platforms, e.g. secure boots or power-downs, version controls, system software checks, secure updates or assessing vulnerabilities
- G06F21/577—Assessing vulnerabilities and evaluating computer system security
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F2221/00—Indexing scheme relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/03—Indexing scheme relating to G06F21/50, monitoring users, programs or devices to maintain the integrity of platforms
- G06F2221/033—Test or assess software
Landscapes
- Engineering & Computer Science (AREA)
- Computer Hardware Design (AREA)
- Computer Security & Cryptography (AREA)
- General Engineering & Computer Science (AREA)
- Software Systems (AREA)
- Theoretical Computer Science (AREA)
- Computing Systems (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Debugging And Monitoring (AREA)
- Stored Programmes (AREA)
Abstract
The embodiment of the invention discloses a method for detecting engine loopholes, which comprises the following steps: acquiring an application program to be detected; acquiring an Application Programming Interface (API) experience library of a first application development engine, wherein the first application development engine is used for developing the application program to be detected, and the API experience library comprises at least one item of API information with security vulnerabilities; extracting the API of the application program to be detected; and judging whether the API of the application program to be detected has a security vulnerability or not according to the API experience library, and if so, determining a target API with the security vulnerability from the API of the application program to be detected. The embodiment of the invention also provides a detection device. According to the embodiment of the invention, the test case does not need to be written for each application development engine, the API experience library of the application development engine is established according to the API information of the security loophole, and the API loophole existing in the application program to be detected is scanned through the API experience library, so that the detection cost of the API loophole is reduced.
Description
Technical Field
The invention relates to the technical field of computers and information security, in particular to a method and a device for detecting engine bugs.
Background
Nowadays, with the continuous development of information technology, application programs are increasingly popularized. In order to enrich daily lives of people, developers develop various application programs, such as social applications, game applications, e-commerce applications, search applications, forum applications, and the like. However, in the process of developing an Application, a vulnerability may occur in an Application Programming Interface (API), which may cause a downtime of the Application during the operation of the Application.
In order to reduce the frequency of downtime of an application program in the running process, whether the API has a bug or not can be detected by adopting a means at present.
Specifically, as shown in fig. 1, fig. 1 is a schematic flow chart illustrating a process for detecting an api bug in the prior art. In step 101, a developer needs to first familiarize with the core functions and architecture of an application program and then design a scenario with a potential performance problem. In step 102, a developer may write an interface test case for each API in the development engine, so that in step 103, each interface test case may be used to perform an interface test on each corresponding API. Since the risk of modifying the development engine underlying APIs is high and it is not beneficial to update and maintain the engine code, it is generally necessary to call the upper level logic code of the interface through step 104. Finally, in step 105, the high-risk API code line obtained by positioning in step 104 is output, and a developer can repair the high-risk API code line in time according to the output high-risk API code line.
However, since there are many APIs for development engines, and there are many development engine versions, and there are certain differences between the APIs of each version, a large number of test cases need to be written for each development version, which consumes a huge API vulnerability detection cost.
Disclosure of Invention
The embodiment of the invention provides an engine vulnerability detection method and device, which can establish an API experience library according to API information with security vulnerabilities in application development engines without compiling test cases for each application development engine, and scan out the API vulnerabilities in application programs to be detected through the API experience library, thereby reducing the detection cost of the API vulnerabilities.
In view of the above, a first aspect of the present invention provides a method for detecting an engine vulnerability, including:
acquiring an application program to be detected;
acquiring an API experience library of a first application development engine, wherein the first application development engine is used for developing the application program to be detected, and the API experience library comprises at least one item of API information with security vulnerabilities;
extracting an Application Programming Interface (API) of the application program to be detected;
and judging whether the API of the application program to be detected has a security vulnerability or not according to the API experience library, and if so, determining a target API with the security vulnerability from the API of the application program to be detected.
In a second aspect, an embodiment of the present invention further provides a detection apparatus, including:
the first acquisition module is used for acquiring the application program to be detected;
the second acquisition module is used for acquiring an API experience library of a first application development engine, the first application development engine is used for developing the application program to be detected acquired by the first acquisition module, and the API experience library comprises at least one item of API information with security vulnerabilities;
the extraction module is used for extracting the application programming interface API of the application program to be detected, which is acquired by the first acquisition module;
and the determining module is used for judging whether the API of the application program to be detected extracted by the extracting module has a security vulnerability according to the API experience library acquired by the second acquiring module, and if so, determining a target API with the security vulnerability from the API of the application program to be detected.
According to the technical scheme, the embodiment of the invention has the following advantages:
the embodiment of the invention provides a method for detecting API loopholes in an application program.A detection device firstly obtains the application program to be detected and an API experience library of a first application development engine, wherein the first application development engine is used for developing the application program to be detected and comprises at least one item of API information with security loopholes, then the detection device extracts the API of the application program to be detected, finally, whether the API of the application program to be detected has the security loopholes or not is judged according to the API experience library, and if so, a target API with the security loopholes is determined from the API of the application program to be detected. By adopting the method, the test case does not need to be written for each application development engine, the API experience library of the application development engine is established according to the API information of the security vulnerability, and the API vulnerability existing in the application program to be detected is scanned through the API experience library, so that the detection cost of the API vulnerability is reduced.
Drawings
FIG. 1 is a schematic diagram illustrating a process for detecting an API bug in the prior art;
FIG. 2 is a diagram of an embodiment of a method for engine vulnerability detection according to the present invention;
FIG. 3 is a schematic flow chart illustrating detection of API bugs in an application according to an embodiment of the present invention;
FIG. 4 is a schematic flow chart illustrating the process of creating an API experience library according to an embodiment of the present invention;
FIG. 5 is a schematic flow chart illustrating implementation of detection items of an application development engine according to an embodiment of the present invention;
FIG. 6 is a diagram showing an interface before detection by the CocosCheck tool in an application scenario;
FIG. 7 is a display of an interface during detection of the CocosCheck tool in an application scenario;
FIG. 8 is a diagram showing an interface after detection by the CocosCheck tool in an application scenario;
FIG. 9 is a schematic diagram of an embodiment of a detection device in an embodiment of the invention;
FIG. 10 is a schematic diagram of another embodiment of a detecting device in an embodiment of the present invention;
FIG. 11 is a schematic diagram of another embodiment of the detecting device in the embodiment of the present invention;
FIG. 12 is a schematic view of another embodiment of the detecting device in the embodiment of the present invention;
FIG. 13 is a schematic diagram of another embodiment of a detecting device in an embodiment of the present invention;
FIG. 14 is a schematic diagram of another embodiment of a detecting device in an embodiment of the present invention;
FIG. 15 is a schematic diagram of another embodiment of a detecting device in an embodiment of the present invention;
FIG. 16 is a schematic structural diagram of a detecting device according to an embodiment of the present invention.
Detailed Description
The embodiment of the invention provides an engine vulnerability detection method and device, which do not need to compile test cases for each application development engine, but establish an API experience library according to API information with security vulnerabilities in the application development engines, and scan out the API vulnerabilities in an application program to be detected through the API experience library, thereby reducing the detection cost of the API vulnerabilities.
The terms "first," "second," "third," "fourth," and the like in the description and in the claims, as well as in the drawings, if any, are used for distinguishing between similar elements and not necessarily for describing a particular sequential or chronological order. It is to be understood that the data so used is interchangeable under appropriate circumstances such that the embodiments of the invention described herein are, for example, capable of operation in sequences other than those illustrated or otherwise described herein. Furthermore, the terms "comprises," "comprising," and "having," and any variations thereof, are intended to cover a non-exclusive inclusion, such that a process, method, system, article, or apparatus that comprises a list of steps or elements is not necessarily limited to those steps or elements expressly listed, but may include other steps or elements not expressly listed or inherent to such process, method, article, or apparatus.
It should be understood that the application development engine in the embodiment of the present invention is mainly an open source framework based on an open source software licensing agreement (abbreviated as MIT in english), and may be an open source framework of Cocos in particular. Cocos provides a complete set of engines and development tools, and covers a complete set of solutions from early design, resource production, development and debugging and packaging online. The Cocos is used for constructing games, application programs and other graphical interface interactive applications, can optimize the workflow in a key mode, standardizes the whole development process, reduces the communication cost and improves the development efficiency.
The open source framework of Cocos mainly has the function of flow control, and the flow control can very easily manage the flow control between different scenes. In addition to the function of flow control, there are also functions such as:
(1) actions (full English name: Sprites) function, combinable actions such as moving, rotating, zooming, etc.;
(2) special Effects (English full name: Effects) functions including waves, rotations, lenses and the like;
(3) the planar map (English full name: Tiled Maps) function supports the rectangular and hexagonal planar Maps;
(4) a conversion (English full name: Transitions) function, which moves from one scene to another scene with different style;
(5) menu (English full name: menu) function, creating internal menu;
(6) a Text Rendering (English full name: Text Rendering) function supporting a label and a HyperText Markup Language (English full name: Hypertext Markup Language, English abbreviation: HTML);
(7) documents (full english: Documents functions, programming guides, API references, video education, and many simple test examples that teach a user how to use them.
In practical applications, the open source framework of Cocos, as an engine development tool for interactive applications, may also include or enhance more functions, which is not necessarily exhaustive here.
It should be understood that the application program to be detected in the embodiment of the present invention may be a game application, but is not limited to a game application, and may also be other types of applications, such as a social application, a media playing application, or a service application, and the like, which is not limited herein.
The detection device can be a detection tool adopted for a Cocos open source framework, the detection tool can be called Cocos check, the Cocos check is displayed as a client on a terminal, and relevant files contained in the application program to be detected are added, detected and output through the client of the Cocos check, so that a user developer can quickly position a code position of an API vulnerability in the application program to be detected and repair the code position in time to restore normal operation of the application program to be detected.
In addition, the invention can be applied to a Windows operating System (Windows OS) developed by Microsoft corporation, and the Windows OS adopts a Graphical User Interface (GUI). With the continuous upgrade of computer hardware and software, microsoft Windows is also continuously upgraded, and it should be noted that the scheme can be applied to Windows operation Experience (Windows Experience, abbreviated as Windows XP) OS, Windows 7OS, Windows 8OS, or Windows10OS, and can also be applied to other types of Windows OS, which is not limited herein.
Referring to fig. 2, an embodiment of a method for detecting an engine vulnerability in the embodiment of the present invention includes:
201. acquiring an application program to be detected;
in this embodiment, the detection device obtains an application to be detected, where the application to be detected is developed by a first application development engine, the first application development engine may be an open-source framework of the Cocos, and the detection device may be a tool designed for the open-source framework of the Cocos and used for detecting an API vulnerability.
202. Acquiring an API experience library of a first application development engine, wherein the first application development engine is used for developing an application program to be detected, and the API experience library comprises at least one item of API information with security vulnerabilities;
in this embodiment, the detection device further calls and obtains the API experience library corresponding to the first application development engine. The API experience library comprises at least one item of API information with security vulnerabilities, the API information with the security vulnerabilities is the API information with high dangerousness, and the extraction rule of the type of the API with high dangerousness can be determined through the API information.
Specifically, for example, the API information includes an API name where the security vulnerability occurs and a location where the security vulnerability occurs in the whole source code, and the refinement rule of the high-risk API type is that the API can be located to the location where the API occurs in the whole source code according to the API name. Therefore, the detection device can find out the code position of the API vulnerability in the application program to be detected by using the extraction rule.
203. Extracting an Application Programming Interface (API) of an application to be detected;
in this embodiment, the detection apparatus may extract the API of the application to be detected by using the keyword.
An API is a predefined function that aims to provide applications and developers the ability to access a set of routines based on certain software or hardware without having to access source code or understand the details of the internal working mechanisms.
204. And judging whether the API of the application program to be detected has a security vulnerability or not according to the API experience library, and if so, determining a target API with the security vulnerability from the API of the application program to be detected.
In this embodiment, after acquiring the API experience library corresponding to the first application development engine, the detection device determines whether the API of the application program to be detected has information that is consistent with the API information of the security vulnerability in the API experience library, for example, whether the API has the same API name, and if so, determines that the target API of the security vulnerability exists in the API of the application program to be detected.
For easy understanding, please refer to fig. 3, where fig. 3 is a schematic flowchart illustrating a process of detecting an API vulnerability in an application according to an embodiment of the present invention, and as shown in the figure, the process specifically includes:
in step 301, the source code of the application development engine is analyzed by means of static scan analysis, wherein multiple versions are usually present for the application development engine, and the current latest version is the first application development engine. Specifically, source codes of Cocos open source frameworks of various versions are mined, and then high-risk APIs with risks at the inner ends are found out;
in step 302, a high-risk API experience library of the Cocos is established according to the version through the static scanning analysis result in step 301, and optionally, a high-risk API corresponding to an updated version may be added to the API experience library each time, that is, the API experience library is continuously updated without establishing a respective API experience library for each version of the Cocos, thereby saving computer storage resources;
in step 303, the CocosChec tool implements the check item of the CocosCheck tool according to the high-risk API type refinement rule in the API experience library;
in step 304, scanning a source code of the application program to be detected by using a CocosCheck tool;
in step 305, the CocosCheck tool scans the code line that has been located to call the high risk API, and the developer can directly modify the code line.
In the embodiment of the invention, the test case does not need to be written for each application development engine, the API experience library of the application development engine is established according to the API information of the security loophole, and the API loophole existing in the application program to be detected is scanned through the API experience library, so that the detection cost of the API loophole is reduced.
Optionally, on the basis of the embodiment corresponding to fig. 2, in a first optional embodiment of the method for detecting an engine vulnerability, before acquiring the API experience library of the first application development engine, the method may further include:
acquiring a source code of a first application development engine;
searching an API with a security vulnerability in a source code of a first application development engine;
and establishing an API experience library according to the API with the security vulnerability.
In this embodiment, the API experience library of the first application development kit is already established in advance before the detection device acquires the API experience library.
Specifically, referring to fig. 4, fig. 4 is a schematic flowchart illustrating a process of creating an API experience library according to an embodiment of the present invention, and as shown in the following process, the API experience library of the first application development engine may be created through the following steps.
In step 401, first, a first application development engine, that is, source codes of each version of the Cocos, is obtained, and if there is only one version, the source code of the version is obtained.
In step 402, the source code of each version of the first application development engine is traversed, and the traversing refers to sequentially performing one-time and only one-time access on each node along a certain search route.
In step 403, in step 402, the source codes of the versions of the first application development engine have been traversed, from which the source code corresponding to the latest version can be found, and the API with null pointer risk in the source code of the current version is analyzed through the static code.
The static code analysis is adopted, the code does not need to be operated, the program is analyzed only by static scanning of the code, and the execution speed and the efficiency are high. The existing mature code static analysis tool can scan tens of thousands of lines of codes per second, and has the characteristics of high detection speed and high efficiency compared with dynamic analysis.
It should be noted that the static code analysis technique adopted in the present solution may be lexical analysis, or syntactic analysis, or abstract syntax tree analysis, or semantic analysis, control flow analysis, or data flow analysis, and in practical applications, other types of static code analysis techniques may also be adopted, which is not limited herein.
In step 404, after the static code analysis in step 403, the API name and the corresponding parameter position of the high risk API risk in the source code corresponding to the latest version are obtained, and the information of the high risk API is recorded.
In step 405, an API experience library corresponding to the latest version is established according to the API information recorded in step 404. Since the version of the first application development engine Cocos is updated continuously, step 402 is executed again after step 405 is completed, so as to ensure that the API experience library covers all the versions of the first application development engine and the corresponding API information.
Optionally, the static code analysis may further detect the validity of different scripting languages when the parameters are called through code scanning, and if parameters do not match when the scripting languages are called mutually, or when the called API does not exist, a risk may exist.
Secondly, in the embodiment of the invention, the API with security holes can be searched for the source code of the first application development engine, so that the API experience library is established, the API information in the API experience library is more complete, and the feasibility and the practicability of the scheme are improved.
Optionally, on the basis of the first embodiment corresponding to fig. 2, in a second optional embodiment of the method for detecting an engine vulnerability provided in the embodiment of the present invention, the searching for an API that has a security vulnerability in a source code of a first application development engine may include:
detecting an API with a null pointer in source code of a first application development engine;
and acquiring the API name and the parameter position corresponding to the API with the null pointer.
In this embodiment, the detection apparatus searches whether a source code in the first application development engine Cocos open source framework has an API with a security vulnerability, and one feasible manner is to detect whether an API with a null pointer exists in the source code, and if so, obtain an API name and a parameter position of the API with the null pointer.
Where NULL pointers are generally intended to be represented by NULL in documents, return NULL and return 0 are equivalent for pointer types, since NULL and 0 both represent "NULL pointer".
Regarding the way of automatically locating null pointer exception, specifically, firstly, combining with a static analysis technology of a program, guiding a program slice by using stack information during program operation, then performing null pointer analysis and alias analysis on the obtained slice to obtain a suspicious statement set causing null pointer exception, and finally giving an error location report. In practical applications, there may be other ways to locate the null pointer, which is not limited herein.
Thirdly, in the embodiment of the present invention, a basis for specifically defining the detection of the API vulnerability may be to detect whether a null pointer exists in the API in the source code, and since the occurrence of the null pointer is a key factor causing downtime, it is more favorable to improve the practicability of the scheme by using the null pointer as a standard for API vulnerability detection, and meanwhile, the way of detecting the null pointer is also simpler and more convenient, thereby improving the detection efficiency of the scheme.
Optionally, on the basis of the second embodiment corresponding to fig. 2, in a third optional embodiment of the method for detecting an engine vulnerability, which is provided by the embodiment of the present invention, establishing an API experience library according to an API with a security vulnerability may include:
and establishing an API experience library of the first application development engine according to the API name and the parameter position corresponding to the API with the null pointer.
In this embodiment, for an API with a security vulnerability, the detection apparatus establishes a corresponding API experience library, where the API experience library includes related information of the high-risk API, such as an API name and a parameter location corresponding to the API with a null pointer.
The following is an example of a high risk API empirical library for Cocos, as shown in table 1 below:
TABLE 1
Further, in the embodiment of the present invention, a basis for establishing an API experience library is illustrated, where an API with a null pointer is considered as a high-risk API, and then relevant information of the high-risk APIs is recorded in the API experience library, so as to perform subsequent vulnerability detection, thereby improving feasibility of the scheme.
Optionally, on the basis of the first, second, or third embodiment corresponding to fig. 2, in a fourth optional embodiment of the method for detecting an engine vulnerability, after acquiring the API experience library of the first application development engine, the method may further include:
when the first application development engine is updated to a second application development engine, acquiring a source code of the second application development engine;
searching an API with security vulnerabilities in source codes of a second application development engine;
and updating the API experience library of the first application development engine into the API experience library of the second application development engine according to the API with the security vulnerability.
In this embodiment, it is assumed that the first application development engine performs version update to obtain the updated second application development engine, in other words, the second application development engine and the first application development engine are the same software, but have different versions, and the version of the second application development engine is updated compared with that of the first application development engine.
Specifically, the detecting device will continuously traverse the version of the first application development engine, and when the version of the information is found to exist, it can be determined that the first application development engine is updated to the second application development engine, and then the detecting device calls the source code of the second application development engine from the official website of the application development engine. Next, the detecting device will find out the API with security vulnerability in the source code of the second application development engine, i.e. find out whether there is API with null pointer, if so, consider that the API has security vulnerability.
And finally, the detection device updates the API experience library of the first application development engine into the API experience library of the second application development engine according to the API with the security vulnerability, namely, the high-risk API information of the second application development engine is added to the API experience library corresponding to the previous version.
Furthermore, in the embodiment of the present invention, when the version of the application development engine is updated, the detection device may find out the API with the security vulnerability in the updated application development engine, and directly update the API experience library, without re-establishing the API experience library corresponding to the updated application development engine, but add new information to the API experience library of the previous version, which not only can improve the efficiency of establishing the API experience library, but also saves the storage resource of the detection device.
Optionally, on the basis of the third embodiment corresponding to fig. 2, in a fifth optional embodiment of the method for detecting an engine vulnerability, according to the API experience library, determining whether a security vulnerability exists in an API of an application to be detected may include:
traversing the API name of the application program to be detected;
judging whether the API name of the application program to be detected is consistent with the API name contained in the API experience library, if so, acquiring a parameter position corresponding to the API name in the application program to be detected according to the API experience library;
and if the corresponding parameter at the parameter position is a null pointer, determining that the API of the application program to be detected has a security vulnerability.
In this embodiment, the specific implementation manner of the detection device determining whether the API of the application program to be detected has the security vulnerability according to the high-risk API information in the API experience library is introduced as follows:
referring to fig. 5, fig. 5 is a schematic flow chart illustrating implementation of the application development engine detection item in the embodiment of the present invention, in step 501, the detection device first obtains a first application development engine version number used by an application program to be scanned, and may specifically be extracted from a cos2dVersion function of cocos2d.cpp, where the extracted code is as follows:
#include“cocos2d.h”
NS_CC_BEGIN
Const char*cocos2dversion()
{
{return“2.2.1”;
}
}
the version number can be extracted through the codes, and optionally, the version number corresponding to the latest version can also be directly extracted.
In step 502, checking whether an API experience library of a corresponding version exists, wherein the API experience library contains information of high-risk APIs, if so, continuing to step 503, otherwise, skipping to step 510;
in step 503, finding a corresponding API experience library according to the version number of the first application development engine, and extracting the API experience library;
in step 504, each file in the application program to be detected is scanned, the files are the source code of the application program to be detected, and the function call at each position in the source code is traversed.
In step 505, the detection apparatus obtains the function name of each API after traversing each call in the application to be detected in step 504.
In step 506, next, the detection device compares the function name of the API obtained in step 505 with the function name in the API experience library, so as to determine whether the API is a high-risk API, if the function names are consistent, the API is considered to be a high-risk API, and then step 507 is entered, otherwise, the detection device jumps to step 504, i.e., the function call at each position in the source code is continuously traversed.
In step 507, the detection device may search the parameter information corresponding to the API function name, such as the location where the API function appears and the code content, according to the high-risk API information stored in the API experience library.
In step 508, it is determined whether the parameter of the calling API is NULL, if so, step 509 is entered, otherwise, step 504 is skipped, i.e., the traversal of each function call in the source code is continued.
In step 509, the risk information of the application to be detected, including the filename of the bug, the code line number, the called API name, the error information, and the like, is output.
In step 510, the API vulnerability detection is ended.
Still further, in the embodiment of the present invention, a mode of performing API vulnerability detection on an application to be detected by using an API experience library is provided, and a high risk API that may appear in the application to be detected is determined by high risk API information included in the API experience library.
Optionally, on the basis of the embodiment corresponding to fig. 2, in six optional embodiments of the method for detecting an engine vulnerability provided in the embodiment of the present invention, after determining a target API with a security vulnerability from APIs of an application to be detected, the method may further include:
and outputting risk information in the application program to be detected, wherein the risk information comprises at least one of the file name, the code position, the called API name and the error reporting information of the application program to be detected with the target API.
In this embodiment, after determining that the target API with the security vulnerability exists in the application program to be detected, the detection device may further display risk information of the target API on the front-end interface for a developer to view and repair in time.
It should be noted that the risk information of the target API includes at least one of a file name, a code location, a called API name, and error reporting information of the application to be detected, but in practical applications, the risk information includes, but is not limited to, the above information.
The file name of the application program to be detected in the risk information indicates which file of the high-risk API appears in the application program to be detected; the code position in the risk information represents the code position of the high-risk API in the source code of the application program to be detected; the called API name in the risk information represents the name of the high-risk API; the wrong reporting information in the risk information is a message prompt for prompting that the current application program to be detected of the developer has an API bug.
Secondly, in the embodiment of the invention, the detection device can display a series of risk information about the application program to be detected, so that a developer can acquire the information of the occurrence of the API vulnerability in time, thereby improving the efficiency of repairing the application program to be detected.
For convenience of understanding, a detailed description is given below of a method for detecting engine vulnerabilities in the present invention with a specific application scenario, specifically:
the first developer develops a game by adopting a Cocos open source framework, and in order to ensure that the game is successfully online, the first developer detects whether the game has API loopholes by adopting a Cocos check tool. The detection steps are as follows:
first, a developer double-clicks a "CocosCheck. exe" tool on a computer, and then enters a use interface of the CocosCheck tool, please refer to fig. 6, where fig. 6 is an interface display image before detection of the CocosCheck tool in an application scene, a "Check" in a menu bar is a detection function, a "File" is a File selection function, an "Edit" is an editing function, a "View" is a View function, and a "Help" is a Help function.
Next, the developer A selects the detection function in the menu bar, i.e., clicks "Check" and then selects the "Directory" option in "Check". After selection, a game source code directory to be detected appears on the interface of the CocosCheck tool, specifically referring to FIG. 7, FIG. 7 is an interface display image when the CocosCheck tool is detected in an application scene, and a developer A selects all source code files in the game to scan.
After the scanning of the CocosCheck tool is completed, a display interface is shown in FIG. 8, FIG. 8 is an interface display image after the detection of the CocosCheck tool in an application scene, a developer A can see a result after the scanning is completed, a code file name for calling a high-risk API is shown in the result as "QGAuto. cpp", the number of corresponding code lines is 247, and the name of the high-risk API is "initWithMaskSprite".
Therefore, developers can quickly find the files with the high-risk API, find the error places according to the code positions and repair the files in time, and therefore the game is guaranteed to be on line smoothly.
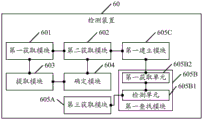
Referring to fig. 9, the detecting apparatus of the present invention is described in detail below, and in an embodiment of the present invention, the detecting apparatus includes:
a first obtaining module 601, configured to obtain an application to be detected;
a second obtaining module 602, configured to obtain an API experience library of a first application development engine, where the first application development engine is configured to develop the to-be-detected application program obtained by the first obtaining module 601, and the API experience library includes at least one item of API information with a security vulnerability;
an extracting module 603, configured to extract an application programming interface API of the application to be detected, acquired by the first acquiring module 601;
a determining module 604, configured to determine, according to the API experience library acquired by the second acquiring module 602, whether the API of the application to be detected extracted by the extracting module 603 has a security vulnerability, and if so, determine a target API having a security vulnerability from the API of the application to be detected.
In this embodiment, a first obtaining module 601 obtains an application to be detected, a second obtaining module 602 obtains an API experience library of a first application development engine, where the first application development engine is configured to develop the application to be detected obtained by the first obtaining module 601, the API experience library includes at least one item of API information with a security vulnerability, an extracting module 603 extracts an application programming interface API of the application to be detected, which is obtained by the first obtaining module 601, a determining module 604 determines whether the API of the application to be detected, which is extracted by the extracting module 603, has a security vulnerability according to the API experience library obtained by the second obtaining module 602, and if so, a target API with a security vulnerability is determined from the APIs of the application to be detected.
In the embodiment of the invention, the test case does not need to be written for each application development engine, the API experience library of the application development engine is established according to the API information of the security loophole, and the API loophole existing in the application program to be detected is scanned through the API experience library, so that the detection cost of the API loophole is reduced.
Optionally, on the basis of the embodiment corresponding to fig. 9, referring to fig. 10, in another embodiment of the detection apparatus provided in the embodiment of the present invention, the detection apparatus further includes:
a third obtaining module 605A, configured to obtain a source code of the first application development engine before the second obtaining module 602 obtains the API experience library of the first application development engine;
a first searching module 605B, configured to search for an API that has a security vulnerability in the source code of the first application development engine acquired by the third acquiring module 605A;
a first establishing module 605C, configured to establish the API experience library according to the API with the security vulnerability searched by the first searching module 605B.
Secondly, in the embodiment of the invention, the API with security holes can be searched for the source code of the first application development engine, so that the API experience library is established, the API information in the API experience library is more complete, and the feasibility and the practicability of the scheme are improved.
Alternatively, on the basis of the embodiment corresponding to fig. 10, referring to fig. 11, in another embodiment of the detection apparatus provided in the embodiment of the present invention,
the first lookup module 605B includes:
a detecting unit 605B1, configured to detect that there is an API with a null pointer in the source code of the first application development engine;
a first obtaining unit 605B2, configured to obtain an API name and a parameter location corresponding to the API where the null pointer exists, detected by the detecting unit 605B 1.
Thirdly, in the embodiment of the present invention, a basis for specifically defining the detection of the API vulnerability may be to detect whether a null pointer exists in the API in the source code, and since the occurrence of the null pointer is a key factor causing downtime, it is more favorable to improve the practicability of the scheme by using the null pointer as a standard for API vulnerability detection, and meanwhile, the way of detecting the null pointer is also simpler and more convenient, thereby improving the detection efficiency of the scheme.
Alternatively, referring to fig. 12 on the basis of the embodiment corresponding to fig. 11, in another embodiment of the detection apparatus provided in the embodiment of the present invention,
the first establishing module 605C comprises:
the establishing unit 605C1 is configured to establish an API experience library of the first application development engine according to the API name and the parameter location corresponding to the API with null pointer acquired by the first acquiring unit 605B 2.
Further, in the embodiment of the present invention, a basis for establishing an API experience library is illustrated, where an API with a null pointer is considered as a high-risk API, and then relevant information of the high-risk APIs is recorded in the API experience library, so as to perform subsequent vulnerability detection, thereby improving feasibility of the scheme.
Alternatively, on the basis of the embodiments corresponding to fig. 10, fig. 11 or fig. 12, referring to fig. 13, in another embodiment of the detection apparatus provided in the embodiment of the present invention,
the detection device 60 further includes:
a fourth obtaining module 606A, configured to, after the second obtaining module 602 obtains the API experience library of the first application development engine, obtain a source code of the second application development engine when the first application development engine is updated to the second application development engine;
a second searching module 606B, configured to search for an API that has a security vulnerability in the source code of the second application development engine acquired by the fourth acquiring module 606A;
an updating module 606C, configured to update the API experience library of the first application development engine to the API experience library of the second application development engine according to the API with the security vulnerability searched by the second searching module 606B.
Furthermore, in the embodiment of the present invention, when the version of the application development engine is updated, the detection device may find out the API with the security vulnerability in the updated application development engine, and directly update the API experience library, without re-establishing the API experience library corresponding to the updated application development engine, but add new information to the API experience library of the previous version, which not only can improve the efficiency of establishing the API experience library, but also saves the storage resource of the detection device.
Alternatively, referring to fig. 14 on the basis of the embodiment corresponding to fig. 12, in another embodiment of the detection apparatus provided in the embodiment of the present invention,
the determining module 604 includes:
a traversal unit 6041 configured to traverse the API name of the application to be detected;
a second obtaining unit 6042, configured to determine whether the API name of the application to be detected obtained by traversal by the traversal unit 6041 is consistent with the API name included in the API experience library, and if so, obtain, according to the API experience library, a parameter position corresponding to the API name in the application to be detected;
a determining unit 6043, configured to determine that the API of the application to be detected has a security vulnerability if the parameter corresponding to the parameter position acquired by the second acquiring unit 6042 is a null pointer.
Still further, in the embodiment of the present invention, a mode of performing API vulnerability detection on an application to be detected by using an API experience library is provided, and a high risk API that may appear in the application to be detected is determined by high risk API information included in the API experience library.
Alternatively, on the basis of the embodiment corresponding to fig. 9, referring to fig. 15, in another embodiment of the detection apparatus provided in the embodiment of the present invention,
the detection device 60 further includes:
an output module 607, configured to, after the determining module 604 determines, from the APIs of the to-be-detected application program, a target API with a security vulnerability, output risk information in the to-be-detected application program, where the risk information includes at least one of a file name, a code position, a called API name, and error information of the to-be-detected application program with the target API.
Secondly, in the embodiment of the invention, the detection device can display a series of risk information about the application program to be detected, so that a developer can acquire the information of the occurrence of the API vulnerability in time, thereby improving the efficiency of repairing the application program to be detected.
As shown in fig. 16, for convenience of description, only the parts related to the embodiment of the present invention are shown, and details of the specific technology are not disclosed, please refer to the method part of the embodiment of the present invention. The terminal may be any terminal device including a Personal Computer (PC), a mobile phone, a tablet PC, a Personal Digital Assistant (PDA), a Point of sale terminal (POS), a vehicle-mounted Computer, and the like, taking the terminal as the PC:
fig. 16 is a block diagram showing a partial structure of a PC related to a terminal provided by an embodiment of the present invention. Referring to fig. 16, the PC includes: radio Frequency (RF) circuit 710, memory 720, input unit 730, display unit 740, sensor 750, audio circuit 760, wireless fidelity (WiFi) module 770, processor 780, and power supply 790. Those skilled in the art will appreciate that the PC configuration shown in fig. 16 does not constitute a limitation of a PC, and may include more or fewer components than those shown, or some components may be combined, or a different arrangement of components.
The respective constituent components of the PC will be described specifically with reference to fig. 16:
the RF circuit 710 may be used for receiving and transmitting signals during information transmission and reception or during a call, and in particular, receives downlink information of a base station and then processes the received downlink information to the processor 780; in addition, the data for designing uplink is transmitted to the base station. In general, RF circuit 710 includes, but is not limited to, an antenna, at least one Amplifier, a transceiver, a coupler, a low noise Amplifier (Lownoise Amplifier; LNA), a duplexer, and the like. In addition, the RF circuit 710 may also communicate with networks and other devices via wireless communication. The wireless communication may use any communication standard or protocol, including but not limited to Global System for Mobile communications (GSM), General Packet Radio Service (GPRS), Code Division Multiple Access (CDMA), Wideband Code Division Multiple Access (WCDMA), Long Term Evolution (LTE), e-mail, Short Message Service (SMS), and so on.
The memory 720 may be used to store software programs and modules, and the processor 780 performs various functional applications of the PC and data processing by operating the software programs and modules stored in the memory 720. The memory 720 may mainly include a program storage area and a data storage area, wherein the program storage area may store an operating system, an application program required by at least one function (such as a sound playing function, an image playing function, etc.), and the like; the storage data area may store data (such as audio data, a phonebook, etc.) created according to the use of the PC, and the like. Further, the memory 720 may include high speed random access memory, and may also include non-volatile memory, such as at least one magnetic disk storage device, flash memory device, or other volatile solid state storage device.
The input unit 730 may be used to receive input numeric or character information and generate key signal inputs related to user settings and function control of the PC. Specifically, the input unit 730 may include a touch panel 731 and other input devices 732. The touch panel 731, also referred to as a touch screen, can collect touch operations of a user (e.g. operations of the user on or near the touch panel 731 by using any suitable object or accessory such as a finger, a stylus, etc.) and drive the corresponding connection device according to a preset program. Alternatively, the touch panel 731 may include two portions of a touch detection device and a touch controller. The touch detection device detects the touch direction of a user, detects a signal brought by touch operation and transmits the signal to the touch controller; the touch controller receives touch information from the touch sensing device, converts it to touch point coordinates, and sends the touch point coordinates to the processor 780, and can receive and execute commands from the processor 780. In addition, the touch panel 731 may be implemented by various types, such as a resistive type, a capacitive type, an infrared ray, and a surface acoustic wave. The input unit 730 may include other input devices 732 in addition to the touch panel 731. In particular, other input devices 732 may include, but are not limited to, one or more of a physical keyboard, function keys (such as volume control keys, switch keys, etc.), a trackball, a mouse, a joystick, and the like.
The display unit 740 may be used to display information input by the user or information provided to the user and various menus of the PC. The Display unit 740 may include a Display panel 741, and optionally, the Display panel 741 may be configured in the form of a Liquid Crystal Display (LCD), an Organic Light-emitting diode (OLED), or the like. Further, the touch panel 731 can cover the display panel 741, and when the touch panel 731 detects a touch operation on or near the touch panel 731, the touch operation is transmitted to the processor 780 to determine the type of the touch event, and then the processor 780 provides a corresponding visual output on the display panel 741 according to the type of the touch event. Although in fig. 16, the touch panel 731 and the display panel 741 are two separate components to implement the input and output functions of the PC, in some embodiments, the touch panel 731 and the display panel 741 may be integrated to implement the input and output functions of the PC.
The PC may also include at least one sensor 750, such as a light sensor, motion sensor, and other sensors. Specifically, the light sensor may include an ambient light sensor that may adjust the brightness of the display panel 741 according to the brightness of ambient light, and a proximity sensor that may turn off the display panel 741 and/or a backlight when the PC is moved to the ear. As one of the motion sensors, the accelerometer sensor can detect the magnitude of acceleration in each direction (generally, three axes), detect the magnitude and direction of gravity when stationary, and can be used for applications of identifying PC gestures (such as horizontal and vertical screen switching, related games, magnetometer gesture calibration), vibration identification related functions (such as pedometer, tapping), and the like; as for other sensors such as a gyroscope, a barometer, a hygrometer, a thermometer, and an infrared sensor, which can be configured by the PC, the description thereof is omitted.
WiFi belongs to short-distance wireless transmission technology, and the PC can help a user to send and receive e-mails, browse webpages, access streaming media and the like through the WiFi module 770, and provides wireless broadband Internet access for the user. Although fig. 16 shows the WiFi module 770, it is understood that it does not belong to the essential constitution of the PC, and may be omitted entirely as needed within the scope not changing the essence of the invention.
The processor 780 is a control center of the PC, connects various parts of the entire PC using various interfaces and lines, and performs various functions of the PC and processes data by operating or executing software programs and/or modules stored in the memory 720 and calling data stored in the memory 720, thereby monitoring the PC as a whole. Optionally, processor 780 may include one or more processing units; preferably, the processor 780 may integrate an application processor, which primarily handles operating systems, user interfaces, applications, etc., and a modem processor, which primarily handles wireless communications. It will be appreciated that the modem processor described above may not be integrated into processor 780.
The PC also includes a power supply 790 (e.g., a battery) for powering the various components, which may preferably be logically coupled to the processor 780 via a power management system to manage charging, discharging, and power consumption management functions via the power management system.
Although not shown, the PC may further include a camera, a bluetooth module, etc., which will not be described herein.
In this embodiment of the present invention, the processor 780 included in the terminal further has the following functions:
acquiring an application program to be detected;
acquiring an API experience library of a first application development engine, wherein the first application development engine is used for developing the application program to be detected, and the API experience library comprises at least one item of API information with security vulnerabilities;
extracting an Application Programming Interface (API) of the application program to be detected;
and judging whether the API of the application program to be detected has a security vulnerability or not according to the API experience library, and if so, determining a target API with the security vulnerability from the API of the application program to be detected.
It is clear to those skilled in the art that, for convenience and brevity of description, the specific working processes of the above-described systems, apparatuses and units may refer to the corresponding processes in the foregoing method embodiments, and are not described herein again.
In the several embodiments provided in the present application, it should be understood that the disclosed system, apparatus and method may be implemented in other manners. For example, the above-described apparatus embodiments are merely illustrative, and for example, the division of the units is only one logical division, and other divisions may be realized in practice, for example, a plurality of units or components may be combined or integrated into another system, or some features may be omitted, or not executed. In addition, the shown or discussed mutual coupling or direct coupling or communication connection may be an indirect coupling or communication connection through some interfaces, devices or units, and may be in an electrical, mechanical or other form.
The units described as separate parts may or may not be physically separate, and parts displayed as units may or may not be physical units, may be located in one place, or may be distributed on a plurality of network units. Some or all of the units can be selected according to actual needs to achieve the purpose of the solution of the embodiment.
In addition, functional units in the embodiments of the present invention may be integrated into one processing unit, or each unit may exist alone physically, or two or more units are integrated into one unit. The integrated unit can be realized in a form of hardware, and can also be realized in a form of a software functional unit.
The integrated unit, if implemented in the form of a software functional unit and sold or used as a stand-alone product, may be stored in a computer readable storage medium. Based on such understanding, the technical solution of the present invention may be embodied in the form of a software product, which is stored in a storage medium and includes instructions for causing a computer device (which may be a personal computer, a server, or a network device) to execute all or part of the steps of the method according to the embodiments of the present invention. And the aforementioned storage medium includes: a U-disk, a removable hard disk, a Read-only Memory (ROM), a Random Access Memory (RAM), a magnetic disk or an optical disk, and other various media capable of storing program codes.
The above-mentioned embodiments are only used for illustrating the technical solutions of the present invention, and not for limiting the same; although the present invention has been described in detail with reference to the foregoing embodiments, it will be understood by those of ordinary skill in the art that: the technical solutions described in the foregoing embodiments may still be modified, or some technical features may be equivalently replaced; and such modifications or substitutions do not depart from the spirit and scope of the corresponding technical solutions of the embodiments of the present invention.
Claims (14)
1. A method for engine vulnerability detection, comprising:
acquiring an application program to be detected;
acquiring an application programming interface experience library of a first application development engine, wherein the first application development engine is used for developing the application to be detected, the application programming interface experience library comprises at least one item of application programming interface information with a security vulnerability, the application programming interface information with the security vulnerability is acquired from source codes of application development engines corresponding to a plurality of versions, the first application development engine belongs to one of the plurality of versions, the first application development engine is a Cocos open source framework, and the application programming interface information comprises an application programming interface name with the security vulnerability and a position appearing in the whole section of source codes;
extracting an application programming interface of the application program to be detected;
judging whether the application programming interface of the application program to be detected has a security vulnerability or not according to the application programming interface experience library, and if so, determining a target application programming interface with the security vulnerability from the application programming interfaces of the application program to be detected;
lines of code to a high-risk application programming interface are located.
2. The method of claim 1, wherein prior to obtaining the api experience library of the first application development engine, the method further comprises:
acquiring a source code of the first application development engine;
searching an application programming interface with a security vulnerability in the source code of the first application development engine;
and establishing the application programming interface experience library according to the application programming interface with the security vulnerability.
3. The method of claim 2, wherein the finding of the application programming interface with the security vulnerability in the source code of the first application development engine comprises:
detecting an application programming interface of a null pointer in source code of the first application development engine;
and acquiring the name and the parameter position of the application programming interface corresponding to the application programming interface with the null pointer.
4. The method according to claim 3, wherein the creating the api experience base according to the api with the security hole comprises:
and establishing an application programming interface experience library of the first application development engine according to the application programming interface name and the parameter position corresponding to the application programming interface with the null pointer.
5. The method of any of claims 2 to 4, wherein after obtaining the application programming interface experience base of the first application development engine, the method further comprises:
when the first application development engine is updated to be a second application development engine, acquiring a source code of the second application development engine;
searching an application programming interface with a security vulnerability in the source code of the second application development engine;
and updating the application programming interface experience base of the first application development engine into the application programming interface experience base of the second application development engine according to the application programming interface with the security vulnerability.
6. The method according to claim 4, wherein the determining whether the api of the application to be detected has a security hole according to the api experience base includes:
traversing the application programming interface name of the application program to be detected;
judging whether the application programming interface name of the application program to be detected is consistent with the application programming interface name contained in the application programming interface experience library, if so, acquiring a parameter position corresponding to the application programming interface name in the application program to be detected according to the application programming interface experience library;
and if the corresponding parameter at the parameter position is a null pointer, determining that the application programming interface of the application program to be detected has a security vulnerability.
7. The method according to claim 1, wherein after determining a target application programming interface with a security vulnerability from the application programming interfaces of the application to be detected, the method further comprises:
and outputting risk information in the application program to be detected, wherein the risk information comprises at least one of the file name, the code position, the called application program programming interface name and error reporting information of the application program to be detected with the target application program programming interface.
8. A detection device, comprising:
the first acquisition module is used for acquiring the application program to be detected;
the second acquisition module is used for acquiring an application programming interface experience library of a first application development engine, the first application development engine is used for developing the application to be detected acquired by the first acquisition module, the application programming interface experience library comprises at least one item of application programming interface information with a security vulnerability, the application programming interface information with the security vulnerability is acquired from source codes of application development engines corresponding to multiple versions, the first application development engine belongs to one of the multiple versions, the first application development engine is a Cocos open source framework, and the application programming interface information comprises an application programming interface name with the security vulnerability and a position appearing in the whole section of source codes;
the extraction module is used for extracting the application programming interface of the application program to be detected, which is acquired by the first acquisition module;
the determining module is used for judging whether the application programming interface of the application program to be detected extracted by the extracting module has a security vulnerability according to the application programming interface experience library acquired by the second acquiring module, and if so, determining a target application programming interface with the security vulnerability from the application programming interfaces of the application program to be detected;
lines of code to a high-risk application programming interface are located.
9. The detection device according to claim 8, further comprising:
the third acquisition module is used for acquiring the source code of the first application development engine before the second acquisition module acquires the application programming interface experience library of the first application development engine;
the first searching module is used for searching an application programming interface with a security vulnerability in the source code of the first application development engine acquired by the third acquiring module;
and the first establishing module is used for establishing the application programming interface experience library according to the application programming interface with the security vulnerability searched by the first searching module.
10. The detection apparatus according to claim 9, wherein the first lookup module comprises:
the detection unit is used for detecting an application programming interface of a null pointer in source codes of the first application development engine;
and the first acquisition unit is used for acquiring the application programming interface name and the parameter position corresponding to the application programming interface with the null pointer detected by the detection unit.
11. The detection apparatus according to claim 10, wherein the first establishing module comprises:
and the establishing unit is used for establishing an application programming interface experience library of the first application development engine according to the application programming interface name and the parameter position corresponding to the application programming interface with the null pointer acquired by the first acquiring unit.
12. The detection device according to any one of claims 9 to 11, further comprising:
a fourth obtaining module, configured to, after the second obtaining module obtains the application programming interface experience library of the first application development engine, obtain a source code of the second application development engine when the first application development engine is updated to the second application development engine;
the second searching module is used for searching an application programming interface with a security vulnerability in the source code of the second application development engine acquired by the fourth acquiring module;
and the updating module is used for updating the application programming interface experience base of the first application development engine into the application programming interface experience base of the second application development engine according to the application programming interface with the security vulnerability searched by the second searching module.
13. The detection apparatus according to claim 11, wherein the determination module comprises:
the traversal unit is used for traversing the application programming interface name of the application program to be detected;
a second obtaining unit, configured to determine whether the application programming interface name of the application to be detected obtained by traversal of the traversal unit is consistent with the application programming interface name included in the application programming interface experience library, and if so, obtain, according to the application programming interface experience library, a parameter position corresponding to the application programming interface name in the application to be detected;
and the determining unit is used for determining that the application programming interface of the application program to be detected has a security vulnerability if the corresponding parameter on the parameter position acquired by the second acquiring unit is a null pointer.
14. The detection device according to claim 8, further comprising:
and the output module is used for outputting risk information in the application program to be detected after the determining module determines a target application program programming interface with a security vulnerability from the application program programming interfaces of the application program to be detected, wherein the risk information comprises at least one of a file name, a code position, a called application program programming interface name and error reporting information of the application program to be detected with the target application program programming interface.
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201610643329.9A CN106295353B (en) | 2016-08-08 | 2016-08-08 | Engine vulnerability detection method and detection device |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201610643329.9A CN106295353B (en) | 2016-08-08 | 2016-08-08 | Engine vulnerability detection method and detection device |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN106295353A CN106295353A (en) | 2017-01-04 |
| CN106295353B true CN106295353B (en) | 2020-04-07 |
Family
ID=57666471
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201610643329.9A Active CN106295353B (en) | 2016-08-08 | 2016-08-08 | Engine vulnerability detection method and detection device |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN106295353B (en) |
Families Citing this family (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN108920943A (en) * | 2018-05-08 | 2018-11-30 | 国家计算机网络与信息安全管理中心 | The method and device of installation binding behavior is detected for application software |
| CN109933989B (en) * | 2019-02-25 | 2021-09-07 | 腾讯科技(深圳)有限公司 | Method and device for detecting vulnerability |
| CN112084104A (en) * | 2019-06-12 | 2020-12-15 | 财付通支付科技有限公司 | A kind of abnormal testing method and device |
| CN110572399B (en) * | 2019-09-10 | 2022-05-20 | 阿波罗智联(北京)科技有限公司 | Vulnerability detection processing method, device, equipment and storage medium |
| CN110855642B (en) * | 2019-10-30 | 2021-08-03 | 腾讯科技(深圳)有限公司 | Application vulnerability detection method and device, electronic equipment and storage medium |
| CN111240719B (en) * | 2020-01-23 | 2021-08-20 | 复旦大学 | Recommended method for defect-driven third-party library version upgrade |
| CN113688358B (en) * | 2020-05-18 | 2024-06-07 | 奇安信网神信息技术(北京)股份有限公司 | System safety detection methods, devices, electronic equipment, media and products |
| CN112580060B (en) * | 2021-01-21 | 2024-06-21 | 国网新疆电力有限公司信息通信公司 | Application system data interface vulnerability detection system |
| CN113535559B (en) * | 2021-07-14 | 2024-07-12 | 杭州默安科技有限公司 | Statistical method and system for coverage rate of application interface |
| CN115185854B (en) * | 2022-07-28 | 2025-08-22 | 中国工商银行股份有限公司 | Application programming interface detection method, device and electronic device |
Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103473509A (en) * | 2013-09-30 | 2013-12-25 | 清华大学 | Android platform malware automatic detecting method |
| CN104537309A (en) * | 2015-01-23 | 2015-04-22 | 北京奇虎科技有限公司 | Application program bug detection method, application program bug detection device and server |
| CN105827664A (en) * | 2016-06-06 | 2016-08-03 | 江苏通付盾科技有限公司 | Vulnerability detection method and device |
Family Cites Families (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US8495748B2 (en) * | 2011-02-24 | 2013-07-23 | Red Hat, Inc. | Mechanism for generating vulnerability reports based on application binary interface/application programming interface usage |
-
2016
- 2016-08-08 CN CN201610643329.9A patent/CN106295353B/en active Active
Patent Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103473509A (en) * | 2013-09-30 | 2013-12-25 | 清华大学 | Android platform malware automatic detecting method |
| CN104537309A (en) * | 2015-01-23 | 2015-04-22 | 北京奇虎科技有限公司 | Application program bug detection method, application program bug detection device and server |
| CN105827664A (en) * | 2016-06-06 | 2016-08-03 | 江苏通付盾科技有限公司 | Vulnerability detection method and device |
Also Published As
| Publication number | Publication date |
|---|---|
| CN106295353A (en) | 2017-01-04 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN106295353B (en) | Engine vulnerability detection method and detection device | |
| CN106970790B (en) | Application program creating method, related equipment and system | |
| CN108345543B (en) | Data processing method, device, equipment and storage medium | |
| CN107329985B (en) | Page collection method and device and mobile terminal | |
| CN108156508B (en) | Barrage information processing method and device, mobile terminal, server and system | |
| CN107562864A (en) | A kind of advertisement screen method, mobile terminal and computer-readable recording medium | |
| CN107766358B (en) | Page sharing method and related device | |
| CN105630685A (en) | Method and device for testing program interface | |
| CN106502703B (en) | Function calling method and device | |
| CN104281394A (en) | Method and device for intelligently selecting words | |
| CN106202422B (en) | The treating method and apparatus of Web page icon | |
| US20150169874A1 (en) | Method, device, and system for identifying script virus | |
| CN108984374B (en) | Method and system for testing database performance | |
| CN107943683A (en) | A kind of test script generation method, device, electronic equipment and storage medium | |
| CN110879709A (en) | Detection method and device of useless codes, terminal equipment and storage medium | |
| CN114422274B (en) | Multi-scene vulnerability detection method and device based on cloud protogenesis and storage medium | |
| CN110378107B (en) | Method and related device for detecting installation package | |
| CN109977013B (en) | Debugging information acquisition method, system and device | |
| CN106230919B (en) | File uploading method and device | |
| CN114064447A (en) | Interface test method and device, storage medium and terminal | |
| CN104424324B (en) | The method and device of locating list item in list element | |
| CN114595449B (en) | A security scanning method and device | |
| CN110166815A (en) | A kind of display methods of video content, device, equipment and medium | |
| CN115145910A (en) | Protocol data management method and related device | |
| CN117519666A (en) | Information processing method, device, equipment and storage medium |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| C06 | Publication | ||
| PB01 | Publication | ||
| C10 | Entry into substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |