EP2874074B1 - Method for implementing cross-domain jump, browser, and domain name server - Google Patents
Method for implementing cross-domain jump, browser, and domain name server Download PDFInfo
- Publication number
- EP2874074B1 EP2874074B1 EP13817388.5A EP13817388A EP2874074B1 EP 2874074 B1 EP2874074 B1 EP 2874074B1 EP 13817388 A EP13817388 A EP 13817388A EP 2874074 B1 EP2874074 B1 EP 2874074B1
- Authority
- EP
- European Patent Office
- Prior art keywords
- domain
- domain name
- identifier
- cross
- user
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
- 238000000034 method Methods 0.000 title claims description 26
- 230000009191 jumping Effects 0.000 claims description 42
- 238000010586 diagram Methods 0.000 description 11
- 239000000284 extract Substances 0.000 description 3
- 238000007796 conventional method Methods 0.000 description 2
- 230000001960 triggered effect Effects 0.000 description 2
- 238000012795 verification Methods 0.000 description 2
- 238000004590 computer program Methods 0.000 description 1
- 230000001419 dependent effect Effects 0.000 description 1
- 238000005516 engineering process Methods 0.000 description 1
- 230000003287 optical effect Effects 0.000 description 1
- 238000004904 shortening Methods 0.000 description 1
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L67/00—Network arrangements or protocols for supporting network services or applications
- H04L67/01—Protocols
- H04L67/02—Protocols based on web technology, e.g. hypertext transfer protocol [HTTP]
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/08—Network architectures or network communication protocols for network security for authentication of entities
- H04L63/0815—Network architectures or network communication protocols for network security for authentication of entities providing single-sign-on or federations
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F16/00—Information retrieval; Database structures therefor; File system structures therefor
- G06F16/90—Details of database functions independent of the retrieved data types
- G06F16/95—Retrieval from the web
- G06F16/957—Browsing optimisation, e.g. caching or content distillation
- G06F16/9574—Browsing optimisation, e.g. caching or content distillation of access to content, e.g. by caching
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/04—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks
- H04L63/0428—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks wherein the data content is protected, e.g. by encrypting or encapsulating the payload
Definitions
- the present invention relates to network techniques, more particularly, to a method for implementing a cross-domain jump, a browser, a first domain name server and a second domain name server.
- the features of the preamble of the independent claims are known from WO 02/39237 A2 .
- Related technologies are known from US 2011/302631 A1 , GB 2 452 283 A and EP 1 081 914 A2 .
- Domain name is a computer name or a computer group name that consists of a series of names separated by dots on internet and is used for showing an electronic location (sometimes a physical location) of a computer when transmitting data.
- Each website corresponds to only one domain name. Switching visits between different websites is called a cross-domain jump, such as clicking a link of other website in one website is the cross-domain jump.
- a method for implementing a cross-domain jump includes the following steps:
- a browser as defined in the independent browser claim, includes:
- the browser After receiving the request of jumping from the first domain name to the second domain name, the browser generates the cross-domain user identifier according to the second domain name and the first identifier, and sends the cross-domain jump request including the cross-domain user identifier to the second domain name server.
- the cross-domain user identifier corresponds to the second identifier of the user in the second domain name. Therefore, the user does not need to log in, while still maintaining the login state of the user. This reduces operation time of the user in a terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- a first domain name server includes:
- the first domain name server After receiving the second domain name and the first identifier of the user in the first domain name sent by the browser, the first domain name server generates the cross-domain user identifier according to the second domain name and the first identifier. The generated cross-domain user identifier corresponds to the second identifier of the user in the second domain name.
- the first domain name server sends the cross-domain user identifier to the browser, which makes that when requesting web page sources from the second domain name, the browser can send the cross-domain user identifier indicative of the second identifier of the user in the second domain name to the second domain name server, so that the user does not need to log in the second domain name, while still maintaining the login state of the user.
- a second domain name server as defined in the independent server claim, includes:
- the second domain name server receives the cross-domain jump request including the cross-domain user identifier sent by the browser, and generates the second identifier of the user in the second domain name according to the cross-domain user identifier, and recognizes the identity of the user according to the second identifier, so that the user does not need to log in the second domain name while still maintaining the login state of the user.
- the cross-domain jump request of jumping from the first domain name and the second domain name includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name.
- the second domain name server can generate the second identifier of the user in the second domain name according to the cross-domain user identifier and recognize the identity of the user according to the second identifier, so that the user does not need to log in again while still maintaining the user login state when jumping from the first domain name to the second domain name. This reduces operation time of the user in a terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- a method for implementing a cross-domain jump includes the following steps: Step S102, a second domain name server obtains a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser, the cross-domain jump request includes a cross-domain user identifier corresponding to a first identifier of a user in the first domain name.
- a request of jumping from the first domain name to the second domain name is triggered.
- the cross-domain user identifier corresponding to the first identifier of the user in the first domain name can be obtained, and the cross-domain jump request including the cross-domain user identifier is generated.
- the cross-domain jump request is sent to the second domain name server.
- the first identifier of the user in the first domain name is a username or a user account or an assigned identification number for the user after the user logs in the first domain name.
- Step S104 the second domain name server obtains a second identifier of the user in the second domain name corresponding to the cross-domain user identifier, and generates a user login state of the user in the second domain name according to the second identifier.
- the second domain name server can analyze the cross-domain jump request according to a pre-set way, extract the cross-domain user identifier from the cross-domain jump request, decrypt the cross-domain user identifier to obtain a decrypted cross-domain user identifier, check legality of the decrypted cross-domain user identifier and find the second identifier of the user in the second domain name corresponding to the decrypted cross-domain user identifier.
- legal cross-domain user identifiers are pre-stored.
- the second domain name server can find the decrypted cross-domain user identifier in the pre-stored legal cross-domain user identifiers. If successfully found, then the decrypted cross-domain user identifier is legal. If unsuccessfully found, then the decrypted cross-domain user identifier is illegal.
- the user login state of the second identifier can be labeled as an already-logged-in state in a user login state database of the second domain name.
- a method for implementing a cross-domain jump includes the following steps: Step S202, a first domain name server obtains a request of jumping from a first domain name to a second domain name sent by a browser, the request includes the second domain name and a first identifier of a user in the first domain name.
- the method for implementing the cross-domain jump further includes the steps of: the browser obtaining a login request of the user to the first domain name, the login request including the first identifier (a username or a user account) and a user password of the user in the first domain name; the browser sending the login request to the first domain name server; the first domain name server verifying the login request and sending a verification result to the browser; the browser generating a file that stores already-logged-in user information of the first domain name if the browser receiving a verification-pass result and writing the first identifier into the file and further storing the file in a pre-set path.
- the already-logged-in user information can be used for identifying a user that operates on a web page of the first domain name.
- the browser reads the first identifier of the user in the first domain name from the file that stores the already-logged-in user information of the first domain name in the pre-set path, and further generates the request of jumping from the first domain name to the second domain name and including the second domain name and the first identifier, and sends the request to the first domain name server.
- Step S204 the first domain server generates a cross-domain user identifier according to the second domain name and the first identifier and returns the cross-domain user identifier to the browser.
- the first domain name server generating the cross-domain user identifier according to the second domain name and the first identifier includes: the first domain name server finding a registered identifier and a second domain name key corresponding to the second domain name, combining the registered identifier with the first identifier, further, the first domain name server encrypting the combined identifier according to the second domain name key and generating the cross-domain user identifier.
- the second domain name can be pre-registered in the first domain name.
- the first domain name server can pre-store the registered identifier of the second domain name (referred as appid) and the second domain name key of the second domain name (referred as appkey).
- the first domain name server can send the cross-domain user identifier to the browser.
- the browser generates a cross-domain jump request including the cross-domain user identifier and the second domain name. Further, the browser sends the cross-domain jump request to the second domain name server.
- the second domain name server can generate the cross-domain jump request including the cross-domain user identifier and the second domain name and send the cross-domain jump request to the browser. Further, the browser transmits the cross-domain jump request to the second domain name server.
- Step S206 the second domain name server obtains the cross-domain jump request of jumping from the first domain name to the second domain name sent by the browser, the cross-domain jump request includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name.
- Step S208 the second domain name server obtains a second identifier of the user in the second domain name corresponding to the cross-domain user identifier, and generates a user login state of the user in the second domain name according to the second identifier.
- a method for implementing a cross-domain jump includes the following steps: Step S302, a browser obtains a request of jumping from a first domain name to a second domain name, and generates a cross-domain user identifier according to the second domain name and a first identifier.
- the browser generating the cross-domain user identifier according to the second domain name and the first identifier includes: the browser finding a registered identifier and a second domain name key corresponding to the second domain name, and combining the registered identifier and the first identifier; the browser encrypting the combined identifier according to the second domain name key to generate the cross-domain user identifier.
- the first domain name server when the browser requests web page sources from the first domain name server, can embed the registered identifier and the second domain name key of the second domain name included in the web page sources into the web page sources, and embed a program of the cross-domain user identifier generated according to the second domain name and the first identifier into the web page sources, and distribute the web page sources to the browser.
- the browser can execute the program of the cross-domain user identifier generated according to the second domain name and the first identifier and pre-embedded into the web page sources to obtain the cross-domain user identifier.
- Step S304 the browser generates a cross-domain jump request according to the cross-domain user identifier and the second domain name and sends the cross-domain jump request to the second domain name server.
- the browser can generate the cross-domain jump request of jumping from the first domain name to the second domain name and including the cross-domain user identifier and the second domain name, and send the cross-domain name request to the second domain name server.
- Step S306 the second domain name server obtains the cross-domain jump request of jumping from the first domain name to the second domain name sent by the browser.
- the cross-domain jump request includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name.
- Step S308 the second domain name server obtains a second identifier of the user corresponding to the cross-domain user identifier in the second domain name, and generates a user login state of the user in the second domain name according to the second identifier.
- the method for implementing the cross-domain jump further includes the steps of: the second domain name server returning the web page sources corresponding to the cross-domain jump request and the user identity information corresponding to the second identifier to the browser; the browser displaying a web page corresponding to the web page sources, and displaying the user identity information corresponding to the second identifier in the web page.
- the browser can display the user identity information, such as a username or a user nickname, etc. corresponding to the second identifier on a corresponding position of the web page to indicate that the user has logged in the second domain name.
- the user identity information such as a username or a user nickname, etc. corresponding to the second identifier on a corresponding position of the web page to indicate that the user has logged in the second domain name.
- the method for implementing the cross-domain jump further includes a step of: the browser storing the second identifier in the file used for storing already-logged-in user information of the second domain name in the pre-set path.
- the browser can encrypt the second identifier according to a pre-set format, further, can store the encrypted second identifier in the file used for storing already-logged-in user information of the second domain name in the pre-set path.
- a browser 10 includes a request obtaining module 102, a browser sending module 104 and a browser receiving module 106.
- the request obtaining module 102 is configured to obtain a request of jumping from a first domain name to a second domain name.
- the request of jumping from the first domain name to the second domain name is triggered.
- the browser sending module 104 is configured to send the second domain name and a first identifier of a user in the first domain name to a first domain name server.
- the first identifier of the user in the first domain name is a username or a user account inputted when the user logs in the first domain name or an identification number assigned to the user after the user logs in the first domain name.
- the browser 10 obtains a login request of the user to the first domain name.
- the login request includes the first identifier (a username or a user account) and a user password of the user in the first domain name.
- the browser 10 sends the login request to the first domain name server.
- the first domain name server verifies the login request, and sends a verification result to the browser 10.
- the browser 10 generates a file that stores already-logged-in user information of the first domain name if the browser 10 receives a verification-pass result, and writes the first identifier into the file, and further stores the file in a pre-set path.
- the browser 10 reads the first identifier of the user from the file that stores the already-logged-in user information of the first domain name in the pre-set path, and further sends the second domain name and the read first identifier to the first domain name server.
- the browser receiving module 106 is configured to receive a cross-domain user identifier generated according to the second domain name and the first identifier and sent by the first domain name server.
- the cross-domain user identifier corresponds to a second identifier of the user in the second domain name.
- the second domain name server generates the cross-domain user identifier according to the second domain name and the first identifier, and sends the generated cross-domain user information to the browser 10.
- the browser sending module 104 is further configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server.
- the cross-domain jump request includes the cross-domain user identifier.
- the browser 10 further includes a cross-domain request generating module (not shown in the figures) configured to generate the cross-domain jump request according to the cross-domain user identifier and the second domain name.
- the cross-domain request generating module can generate the cross-domain jump request of jumping from the first domain name and the second domain name and including the cross-domain user identifier and the second domain name.
- the browser receiving module 106 is further configured to receive web page sources corresponding to the cross-domain jump request and the user identity information corresponding to the second identifier sent by the second domain name server.
- the browser 10 further includes a display module (not shown in the figures) configured to display a web page corresponding to the web page sources and display the user identity information corresponding to the second identifier in the web page.
- a display module (not shown in the figures) configured to display a web page corresponding to the web page sources and display the user identity information corresponding to the second identifier in the web page.
- the display module can display the user identity information, such as a username or a user account, corresponding to the second identifier in a corresponding position of the web page to indicate that the user has logged in the second domain name.
- the user identity information such as a username or a user account
- the browser 10 further includes an identifier storing module (not shown in the figures) configured to store the second identifier in the file that stores already-logged-in user information of the second domain name in the pre-set path.
- the identifier storing module can encrypt the second identifier according to a pre-set format, furthermore, stores the encrypted second identifier in the file that stores already-logged-in user information of the second domain name in the pre-set path.
- the already-logged-in user information of the second domain name can be used for identifying a user that operates on the web page of the second domain name.
- the browser 10 obtains the request of jumping from the first domain name to the second domain name, receives the cross-domain user identifier sent by the first domain name server and generated according to the second domain name and the first identifier, and sends the cross-domain jump request including the cross-domain user identifier to the second domain name server.
- the cross-domain user identifier corresponds to the second identifier of the user in the second domain name. Therefore, it is unnecessary to log in again, and the login state of the user can be maintained. This reduces operation time of the user in the terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- a first domain name server 20 includes a first receiving module 202, a cross-domain identifier generating module 204 and a first sending module 206.
- the first receiving module 202 is configured to receive a second domain name and a first identifier of a user in a first domain name sent by a browser.
- the cross-domain identifier generating module 204 is configured to generate a cross-domain user identifier according to the second domain name and the first identifier.
- the cross-domain user identifier corresponds to a second identifier of the user in the second domain name.
- the cross-domain identifier generating module 204 is configured to find a registered identifier and a second domain name key corresponding to the second domain name, combine the registered identifier with the first identifier, encrypt the combined identifier according to the second domain name key and generate the cross-domain user identifier.
- the second domain name can be pre-registered in the first domain name.
- the first domain name server 20 can pre-store the registered identifier of the second domain name (referred as appid) and the second domain name key of the second domain name (referred as appkey).
- the first sending module 206 is configured to send the cross-domain user identifier to the browser.
- the first domain name 20 further includes a cross-domain request generating module (not shown in the figures) configured to generate a cross-domain jump request including the cross-domain user identifier and the second domain name.
- the first sending module 206 is configured to send the cross-domain jump request to the browser.
- the first domain name server 20 After receiving the second domain name and the first identifier of the user in the first domain name sent by the browser, the first domain name server 20 generates the cross-domain user identifier according to the second domain name and the first identifier. The generated cross-domain user identifier corresponds to the second identifier of the user in the second domain name.
- the first domain name server 20 sends the cross-domain user identifier to the browser, which makes that when requesting web page sources from the second domain name, the browser can send the cross-domain user identifier indicative of the second identifier of the user in the second domain name to the second domain name server, so that the user does not need to log in the second domain name, while still maintaining the login state of the user.
- a second domain name server 30 includes a second receiving module 302, a second identifier obtaining module 304 and a login state generating module 306.
- the second receiving module 302 is configured to receive a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser.
- the cross-domain jump request includes a cross-domain user identifier corresponding to a first identifier of a user in the first domain name.
- the second identifier obtaining module 304 is configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier.
- the second identifier obtaining module 304 is configured to analyze the cross-domain jump request according to a pre-set way, extract the cross-domain user identifier from the cross-domain jump request, decrypt the cross-domain user identifier to obtain a decrypted cross-domain user identifier, check legality of the decrypted cross-domain user identifier and find the second identifier of the user in the second domain name corresponding to the decrypted cross-domain user identifier.
- the second domain name server can pre-store legal cross-domain user identifiers.
- the second identifier obtaining module 304 can find the decrypted cross-domain user identifier in the pre-stored legal cross-domain user identifiers. If successfully found, then the decrypted cross-domain user identifier is legal. If unsuccessfully found, then the decrypted cross-domain user identifier is illegal.
- the login state generating module 306 is configured to generate a user login state of the user in the second domain name according to the second identifier.
- the login state generating module 306 is further configured to label the user login state of the second identifier as an already-logged-in state in a user login state database of the second domain name.
- the second domain name server 30 further includes an information returning module 308 configured to return web page sources corresponding to the cross-domain jump request and a user identity information corresponding to the second identifier to the browser.
- the second domain name server 30 receives the cross-domain jump request including the cross-domain user identifier sent by the browser, and generates the second identifier of the user in the second domain name according to the cross-domain user identifier, and recognizes the identity of the user according to the second identifier, so that the user does not need to log in the second domain name while still maintaining the login state of the user.
- a system for implementing a cross-domain jump includes the browser 10, the first domain name server 20 and the second domain name server 30 of any one of the above embodiments.
- the browser 10 includes the request obtaining module 102, the browser sending module 104 and the browser receiving module 106 shown in FIG. 5 .
- the first domain name server 20 includes the first receiving module 202, the cross-domain identifier generating module 204 and the first sending module 206 shown in FIG. 6 .
- the second domain name server 30 includes the second receiving module 302, the second identifier obtaining module 304 and the login state generating module 306 shown in FIG. 7 .
- the request obtaining module 102 is configured to obtain a request of jumping from a first domain name to a second domain name.
- the browser sending module 104 is configured to send the second domain name and a first identifier of a user in the first domain name to the first domain name server 20.
- the first receiving module 202 is configured to receive the second domain name and the first identifier of the user in the first domain name sent by the browser 10.
- the cross-domain identifier generating module 204 is configured to generate a cross-domain user identifier according to the second domain name and the first identifier.
- the first sending module 206 is configured to send the cross-domain user identifier to the browser 10.
- the browser receiving module 106 is configured to receive the cross-domain user identifier sent by the first domain name server 20.
- the browser sending module 104 is further configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server 30.
- the cross-domain jump request includes the cross-domain user identifier.
- the second receiving module 302 is configured to receive the cross-domain jump request of jumping from the first domain name to the second domain name sent by the browser 10.
- the second identifier obtaining module 304 is configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier.
- the login state generating module 306 is configured to generate a user login state of the user in the second domain name according to the second identifier.
- a browser 40 includes a request obtaining unit 402, a cross-domain identifier generating unit 404 and a browser sending unit 406.
- the request obtaining unit 402 is configured to obtain a request of jumping from a first domain name to a second domain name.
- the cross-domain identifier generating unit 404 is configured to generate a cross-domain user identifier according to the second domain name and a first identifier of a user in the first domain name.
- the cross-domain user identifier corresponds to a second identifier of the user in the second domain name.
- the cross-domain identifier generating unit 404 is configured to find a registered identifier and a second domain name key corresponding to the second domain name, combine the registered identifier with the first identifier, encrypt the combined identifier according to the second domain name key and generate the cross-domain user identifier.
- the first domain name server when the browser requests web page sources from the first domain name server, can embed the registered identifier and the second domain name key of the second domain name included in the web page sources into the web page sources, and embed a program of the cross-domain user identifier generated according to the second domain name and the first identifier, and distribute the web page sources to the browser.
- the cross-domain identifier generating unit 404 can execute the program of the cross-domain user identifier generated according to the second domain name and the first identifier and pre-embedded into the web page sources to generate the cross-domain user identifier.
- the browser sending unit 406 is configured to send the cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server.
- the cross-domain jump request includes the cross-domain user identifier.
- the browser 40 further includes a browser receiving unit 408 configured to receive the web page sources corresponding to the cross-domain jump request and a user identity information corresponding to the second identifier sent by the second domain name server.
- the browser 40 further includes a display module (not shown in the figures) configured to display a web page corresponding to the web page sources and display the user identity information corresponding to the second identifier in the web page.
- a display module (not shown in the figures) configured to display a web page corresponding to the web page sources and display the user identity information corresponding to the second identifier in the web page.
- the browser 40 After receiving the request of jumping from the first domain name to the second domain name, the browser 40 generates the cross-domain user identifier according to the second domain name and the first identifier, and sends the cross-domain jump request including the cross-domain user identifier to the second domain name server.
- the cross-domain user identifier corresponds to the second identifier of the user in the second domain name. Therefore, the user does not need to log in, while still maintaining the login state of the user. This reduces operation time of the user in the terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- a system for implementing a cross-domain jump includes the browser 40 and the second domain name server 30 of any one of the above embodiments.
- the browser 40 includes the request obtaining unit 402, the cross-domain identifier generating unit 404 and the browser sending unit 406 shown in FIG. 10 .
- the second domain name server 30 includes the second receiving module 302, the second identifier obtaining module 304 and the login state generating module 306 shown in FIG. 7 .
- the request obtaining unit 402 is configured to obtain a request of jumping from a first domain name to a second domain name.
- the cross-domain identifier generating unit 404 is configured to generate a cross-domain user identifier according to the second domain name and a first identifier of a user in the first domain name.
- the cross-domain user identifier corresponds to a second identifier of the user in the second domain name.
- the browser sending unit 406 is configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server.
- the cross-domain jump request includes the cross-domain user identifier.
- the second receiving module 302 is configured to receive the cross-domain jump request of jumping from the first domain name to the second domain name sent by the browser 40.
- the second identifier obtaining module 304 is configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier.
- the login state generating module 306 is configured to generate a user login state of the user in the second domain name according to the second identifier.
- the cross-domain jump request of jumping from the first domain name and the second domain name includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name.
- the second domain name server can generate the second identifier of the user in the second domain name according to the cross-domain user identifier and recognize the identity of the user according to the second identifier, so that the user does not need to log in again while still maintaining the user login state when jumping from the first domain name to the second domain name. This reduces operation time of the user in a terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
Landscapes
- Engineering & Computer Science (AREA)
- General Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Databases & Information Systems (AREA)
- Theoretical Computer Science (AREA)
- Computing Systems (AREA)
- Computer Hardware Design (AREA)
- Data Mining & Analysis (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Information Transfer Between Computers (AREA)
Description
- The present invention relates to network techniques, more particularly, to a method for implementing a cross-domain jump, a browser, a first domain name server and a second domain name server. The features of the preamble of the independent claims are known from
WO 02/39237 A2 US 2011/302631 A1 ,GB 2 452 283 AEP 1 081 914 A2 - Domain name is a computer name or a computer group name that consists of a series of names separated by dots on internet and is used for showing an electronic location (sometimes a physical location) of a computer when transmitting data. Each website corresponds to only one domain name. Switching visits between different websites is called a cross-domain jump, such as clicking a link of other website in one website is the cross-domain jump.
- After a user logs in a website with one domain name, the user clicks the link of the website to jump to a website with another domain name. In a conventional method for implementing the cross-domain jump, the website with another domain name cannot recognize login information of the user. Therefore, jumping to the website with another domain name cannot maintain a login state of the user. The user can only log in the website with another domain name by inputting login information (such as inputting an account and a password) again. Therefore, in the conventional method for implementing the cross-domain jump, websites of different domain names cannot maintain the login state of the user, which brings inconvenience to the user. The user has to operate a lot of times in a terminal to maintain state of the user after implementing the cross-domain jump. This will increase operation time of the user in the terminal, thereby causing high consumption of electrical power of the terminal, especially for a mobile terminal with limited power, shortening a battery life.
- Accordingly, it is necessary to provide a method for implementing a cross-domain jump capable of maintaining a user login state when implementing the cross-domain jump between different websites.
- A method for implementing a cross-domain jump, as defined in the independent method claim, includes the following steps:
- a second domain name server obtaining a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser, the cross-domain jump request including a cross-domain user identifier corresponding to a first identifier of a user in the first domain name;
- the second domain name server obtaining a second identifier of the user in the second domain name corresponding to the cross-domain user identifier, and generating a user login state of the user in the second domain name according to the second identifier.
- Accordingly, it is necessary provide a browser capable of maintaining a user login state when implementing a cross-domain jump between different websites.
- A browser, as defined in the independent browser claim, includes:
- a request obtaining module configured to obtain a request of jumping from a first domain name to a second domain name;
- a browser sending module configured to send the second domain name and a first identifier of a user in the first domain name to a first domain name server;
- a browser receiving module configured to receive a cross-domain user identifier sent by the first domain name server and generated according to the second domain name and the first identifier, the cross-domain user identifier corresponding to a second identifier of the user in the second domain name;
- the browser sending module further configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server, the cross-domain jump request including the cross-domain user identifier.
- After receiving the request of jumping from the first domain name to the second domain name, the browser generates the cross-domain user identifier according to the second domain name and the first identifier, and sends the cross-domain jump request including the cross-domain user identifier to the second domain name server. The cross-domain user identifier corresponds to the second identifier of the user in the second domain name. Therefore, the user does not need to log in, while still maintaining the login state of the user. This reduces operation time of the user in a terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- Accordingly, it is necessary to provide a first domain name server capable of maintaining a user login state when jumping from a first domain name to a second domain name.
- A first domain name server includes:
- a first receiving module configured to receive a second domain name and a first identifier of a user in a first domain name sent by a browser.
- a cross-domain identifier generating module configured to generate a cross-domain user identifier according to the second domain name and the first identifier, the cross-domain user identifier corresponding to a second identifier of the user in the second domain name; and
- a first sending module configured to send the cross-domain user identifier to the browser.
- After receiving the second domain name and the first identifier of the user in the first domain name sent by the browser, the first domain name server generates the cross-domain user identifier according to the second domain name and the first identifier. The generated cross-domain user identifier corresponds to the second identifier of the user in the second domain name. The first domain name server sends the cross-domain user identifier to the browser, which makes that when requesting web page sources from the second domain name, the browser can send the cross-domain user identifier indicative of the second identifier of the user in the second domain name to the second domain name server, so that the user does not need to log in the second domain name, while still maintaining the login state of the user.
- Accordingly, it is necessary to provide a second domain name server capable of maintaining a user login state when jumping from a first domain name to a second domain name.
- A second domain name server, as defined in the independent server claim, includes:
- a second receiving module configured to receive a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser, the cross-domain jump request including a cross-domain user identifier corresponding to a first identifier of a user in the first domain name;
- a second identifier obtaining module configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier; and
- a login state generating module configured to generate a user login state of the user in the second domain name according to the second identifier.
- The second domain name server receives the cross-domain jump request including the cross-domain user identifier sent by the browser, and generates the second identifier of the user in the second domain name according to the cross-domain user identifier, and recognizes the identity of the user according to the second identifier, so that the user does not need to log in the second domain name while still maintaining the login state of the user.
- In the method for implementing cross-domain jump, the cross-domain jump request of jumping from the first domain name and the second domain name includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name. The second domain name server can generate the second identifier of the user in the second domain name according to the cross-domain user identifier and recognize the identity of the user according to the second identifier, so that the user does not need to log in again while still maintaining the user login state when jumping from the first domain name to the second domain name. This reduces operation time of the user in a terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- The invention is defined in the independent claims. Preferred embodiments are set out in the dependent claims.
-
-
FIG. 1 is a flow diagram of a method of implementing a cross-domain jump according to an embodiment. -
FIG. 2 is a flow diagram of a method of implementing a cross-domain jump according to another embodiment. -
FIG. 3 is a flow diagram of a method for implementing a cross-domain jump according to yet another embodiment. -
FIG. 4 is a work flowchart of a method for implementing a cross-domain jump according to an embodiment. -
FIG. 5 is a block diagram of a browser according to an embodiment. -
FIG. 6 is a block diagram of a first domain name server according to an embodiment. -
FIG. 7 is a block diagram of a second domain name server according to an embodiment. -
FIG. 8 is a block diagram of a second domain name server according to another embodiment. -
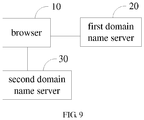
FIG. 9 is a block diagram of a system for implementing a cross-domain jump according to an embodiment. -
FIG. 10 is a block diagram of a browser according to another embodiment. -
FIG. 11 is a block diagram of a browser according to yet another embodiment. -
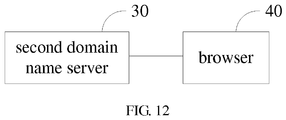
FIG. 12 is a block diagram of a system for implementing a cross-domain jump according to another embodiment. - As shown in
FIG. 1 , in an embodiment, a method for implementing a cross-domain jump includes the following steps:
Step S102, a second domain name server obtains a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser, the cross-domain jump request includes a cross-domain user identifier corresponding to a first identifier of a user in the first domain name. - In an embodiment, after a link of the second domain name in a web page of the first domain name is clicked, a request of jumping from the first domain name to the second domain name is triggered. After the request is obtained, the cross-domain user identifier corresponding to the first identifier of the user in the first domain name can be obtained, and the cross-domain jump request including the cross-domain user identifier is generated. The cross-domain jump request is sent to the second domain name server.
- In an embodiment, the first identifier of the user in the first domain name is a username or a user account or an assigned identification number for the user after the user logs in the first domain name.
- Step S104, the second domain name server obtains a second identifier of the user in the second domain name corresponding to the cross-domain user identifier, and generates a user login state of the user in the second domain name according to the second identifier.
- Specifically, in an embodiment, the second domain name server can analyze the cross-domain jump request according to a pre-set way, extract the cross-domain user identifier from the cross-domain jump request, decrypt the cross-domain user identifier to obtain a decrypted cross-domain user identifier, check legality of the decrypted cross-domain user identifier and find the second identifier of the user in the second domain name corresponding to the decrypted cross-domain user identifier.
- In an embodiment, legal cross-domain user identifiers are pre-stored. The second domain name server can find the decrypted cross-domain user identifier in the pre-stored legal cross-domain user identifiers. If successfully found, then the decrypted cross-domain user identifier is legal. If unsuccessfully found, then the decrypted cross-domain user identifier is illegal. Moreover, in an embodiment, the user login state of the second identifier can be labeled as an already-logged-in state in a user login state database of the second domain name.
- As shown in
FIG. 2 , in an embodiment, a method for implementing a cross-domain jump includes the following steps:
Step S202, a first domain name server obtains a request of jumping from a first domain name to a second domain name sent by a browser, the request includes the second domain name and a first identifier of a user in the first domain name. - In an embodiment, prior to the step S202, the method for implementing the cross-domain jump further includes the steps of: the browser obtaining a login request of the user to the first domain name, the login request including the first identifier (a username or a user account) and a user password of the user in the first domain name; the browser sending the login request to the first domain name server; the first domain name server verifying the login request and sending a verification result to the browser; the browser generating a file that stores already-logged-in user information of the first domain name if the browser receiving a verification-pass result and writing the first identifier into the file and further storing the file in a pre-set path. The already-logged-in user information can be used for identifying a user that operates on a web page of the first domain name.
- Moreover, after a link of the second domain name in the web page of the first domain name is clicked, the browser reads the first identifier of the user in the first domain name from the file that stores the already-logged-in user information of the first domain name in the pre-set path, and further generates the request of jumping from the first domain name to the second domain name and including the second domain name and the first identifier, and sends the request to the first domain name server.
- Step S204, the first domain server generates a cross-domain user identifier according to the second domain name and the first identifier and returns the cross-domain user identifier to the browser.
- In an embodiment, the first domain name server generating the cross-domain user identifier according to the second domain name and the first identifier includes: the first domain name server finding a registered identifier and a second domain name key corresponding to the second domain name, combining the registered identifier with the first identifier, further, the first domain name server encrypting the combined identifier according to the second domain name key and generating the cross-domain user identifier.
- Specifically, the second domain name can be pre-registered in the first domain name. The first domain name server can pre-store the registered identifier of the second domain name (referred as appid) and the second domain name key of the second domain name (referred as appkey).
- Moreover, the first domain name server can send the cross-domain user identifier to the browser. The browser generates a cross-domain jump request including the cross-domain user identifier and the second domain name. Further, the browser sends the cross-domain jump request to the second domain name server. In another embodiment, the second domain name server can generate the cross-domain jump request including the cross-domain user identifier and the second domain name and send the cross-domain jump request to the browser. Further, the browser transmits the cross-domain jump request to the second domain name server.
- Step S206, the second domain name server obtains the cross-domain jump request of jumping from the first domain name to the second domain name sent by the browser, the cross-domain jump request includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name.
- Step S208, the second domain name server obtains a second identifier of the user in the second domain name corresponding to the cross-domain user identifier, and generates a user login state of the user in the second domain name according to the second identifier.
- As shown in
FIG. 3 , in an embodiment, a method for implementing a cross-domain jump includes the following steps:
Step S302, a browser obtains a request of jumping from a first domain name to a second domain name, and generates a cross-domain user identifier according to the second domain name and a first identifier. - In an embodiment, the browser generating the cross-domain user identifier according to the second domain name and the first identifier includes: the browser finding a registered identifier and a second domain name key corresponding to the second domain name, and combining the registered identifier and the first identifier; the browser encrypting the combined identifier according to the second domain name key to generate the cross-domain user identifier.
- Specifically, in an embodiment, when the browser requests web page sources from the first domain name server, the first domain name server can embed the registered identifier and the second domain name key of the second domain name included in the web page sources into the web page sources, and embed a program of the cross-domain user identifier generated according to the second domain name and the first identifier into the web page sources, and distribute the web page sources to the browser.
- Further, after the link of the second domain name in a first domain name web page is clicked, the browser can execute the program of the cross-domain user identifier generated according to the second domain name and the first identifier and pre-embedded into the web page sources to obtain the cross-domain user identifier.
- Step S304, the browser generates a cross-domain jump request according to the cross-domain user identifier and the second domain name and sends the cross-domain jump request to the second domain name server.
- Specifically, the browser can generate the cross-domain jump request of jumping from the first domain name to the second domain name and including the cross-domain user identifier and the second domain name, and send the cross-domain name request to the second domain name server.
- Step S306, the second domain name server obtains the cross-domain jump request of jumping from the first domain name to the second domain name sent by the browser. The cross-domain jump request includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name.
- Step S308, the second domain name server obtains a second identifier of the user corresponding to the cross-domain user identifier in the second domain name, and generates a user login state of the user in the second domain name according to the second identifier.
- In an embodiment, the method for implementing the cross-domain jump further includes the steps of: the second domain name server returning the web page sources corresponding to the cross-domain jump request and the user identity information corresponding to the second identifier to the browser; the browser displaying a web page corresponding to the web page sources, and displaying the user identity information corresponding to the second identifier in the web page.
- Specifically, the browser can display the user identity information, such as a username or a user nickname, etc. corresponding to the second identifier on a corresponding position of the web page to indicate that the user has logged in the second domain name.
- In an embodiment, the method for implementing the cross-domain jump further includes a step of: the browser storing the second identifier in the file used for storing already-logged-in user information of the second domain name in the pre-set path.
- Specifically, the browser can encrypt the second identifier according to a pre-set format, further, can store the encrypted second identifier in the file used for storing already-logged-in user information of the second domain name in the pre-set path.
- Following is a specific example to explain the method for implementing the cross-domain jump, as shown in
FIG. 4 : - (1) The browser sends a login request of logging in the first domain name to the first domain name server.
- (2) The first domain name server verifies the login request and returns information indicative of the login request of a user being passed and the web page sources of the first domain name to the user browser.
- (3) The browser obtains a request of the user of jumping from the first domain name to the second domain name, obtains a first identifier of the user in the first domain name, and sends a processing request including a second domain name and the first identifier to the first domain name server.
- (4) The first domain name server receives the processing request, generates a cross-domain user identifier according to the second domain name and the first identifier, and generates a cross-domain jump request of jumping from the first domain name to the second domain name and including the cross-domain user identifier, and sends the cross-domain jump request to the browser.
- (5) The browser sends the cross-domain jump request to the second domain name server.
- (6) The second domain name server analyzes the cross-domain jump request, extracts the cross-domain user identifier, generates a second identifier of the user in the second domain name according to the cross-domain user identifier, and generates a user login state of the user in the second domain name according to the second identifier, and further obtains the web page sources corresponding to the second domain name.
- (7) The second domain name server sends the web page sources and the second identifier corresponding to the cross-domain jump request to the browser.
- As shown in
FIG. 5 , in an embodiment, abrowser 10 includes arequest obtaining module 102, abrowser sending module 104 and abrowser receiving module 106. - The
request obtaining module 102 is configured to obtain a request of jumping from a first domain name to a second domain name. - In an embodiment, after a link of the second domain name in a web page of the first domain name is clicked, the request of jumping from the first domain name to the second domain name is triggered.
- The
browser sending module 104 is configured to send the second domain name and a first identifier of a user in the first domain name to a first domain name server. - In an embodiment, the first identifier of the user in the first domain name is a username or a user account inputted when the user logs in the first domain name or an identification number assigned to the user after the user logs in the first domain name.
- In an embodiment, the
browser 10 obtains a login request of the user to the first domain name. The login request includes the first identifier (a username or a user account) and a user password of the user in the first domain name. Thebrowser 10 sends the login request to the first domain name server. The first domain name server verifies the login request, and sends a verification result to thebrowser 10. Thebrowser 10 generates a file that stores already-logged-in user information of the first domain name if thebrowser 10 receives a verification-pass result, and writes the first identifier into the file, and further stores the file in a pre-set path. - Moreover, after the link of the second domain name in the web page of the first domain name is clicked, the
browser 10 reads the first identifier of the user from the file that stores the already-logged-in user information of the first domain name in the pre-set path, and further sends the second domain name and the read first identifier to the first domain name server. - The
browser receiving module 106 is configured to receive a cross-domain user identifier generated according to the second domain name and the first identifier and sent by the first domain name server. The cross-domain user identifier corresponds to a second identifier of the user in the second domain name. - Specifically, the second domain name server generates the cross-domain user identifier according to the second domain name and the first identifier, and sends the generated cross-domain user information to the
browser 10. - The
browser sending module 104 is further configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server. The cross-domain jump request includes the cross-domain user identifier. - In an embodiment, the
browser 10 further includes a cross-domain request generating module (not shown in the figures) configured to generate the cross-domain jump request according to the cross-domain user identifier and the second domain name. Specifically, the cross-domain request generating module can generate the cross-domain jump request of jumping from the first domain name and the second domain name and including the cross-domain user identifier and the second domain name. - In an embodiment, the
browser receiving module 106 is further configured to receive web page sources corresponding to the cross-domain jump request and the user identity information corresponding to the second identifier sent by the second domain name server. - In an embodiment, the
browser 10 further includes a display module (not shown in the figures) configured to display a web page corresponding to the web page sources and display the user identity information corresponding to the second identifier in the web page. - Specifically, the display module can display the user identity information, such as a username or a user account, corresponding to the second identifier in a corresponding position of the web page to indicate that the user has logged in the second domain name.
- In an embodiment, the
browser 10 further includes an identifier storing module (not shown in the figures) configured to store the second identifier in the file that stores already-logged-in user information of the second domain name in the pre-set path. - Specifically, the identifier storing module can encrypt the second identifier according to a pre-set format, furthermore, stores the encrypted second identifier in the file that stores already-logged-in user information of the second domain name in the pre-set path. The already-logged-in user information of the second domain name can be used for identifying a user that operates on the web page of the second domain name.
- The
browser 10 obtains the request of jumping from the first domain name to the second domain name, receives the cross-domain user identifier sent by the first domain name server and generated according to the second domain name and the first identifier, and sends the cross-domain jump request including the cross-domain user identifier to the second domain name server. The cross-domain user identifier corresponds to the second identifier of the user in the second domain name. Therefore, it is unnecessary to log in again, and the login state of the user can be maintained. This reduces operation time of the user in the terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life. - As shown in
FIG. 6 , in an embodiment, a firstdomain name server 20 includes afirst receiving module 202, a cross-domainidentifier generating module 204 and afirst sending module 206. - The
first receiving module 202 is configured to receive a second domain name and a first identifier of a user in a first domain name sent by a browser. - The cross-domain
identifier generating module 204 is configured to generate a cross-domain user identifier according to the second domain name and the first identifier. The cross-domain user identifier corresponds to a second identifier of the user in the second domain name. - In an embodiment, the cross-domain
identifier generating module 204 is configured to find a registered identifier and a second domain name key corresponding to the second domain name, combine the registered identifier with the first identifier, encrypt the combined identifier according to the second domain name key and generate the cross-domain user identifier. - Specifically, the second domain name can be pre-registered in the first domain name. The first
domain name server 20 can pre-store the registered identifier of the second domain name (referred as appid) and the second domain name key of the second domain name (referred as appkey). - The
first sending module 206 is configured to send the cross-domain user identifier to the browser. - In another embodiment, the
first domain name 20 further includes a cross-domain request generating module (not shown in the figures) configured to generate a cross-domain jump request including the cross-domain user identifier and the second domain name. In this embodiment, thefirst sending module 206 is configured to send the cross-domain jump request to the browser. - After receiving the second domain name and the first identifier of the user in the first domain name sent by the browser, the first
domain name server 20 generates the cross-domain user identifier according to the second domain name and the first identifier. The generated cross-domain user identifier corresponds to the second identifier of the user in the second domain name. The firstdomain name server 20 sends the cross-domain user identifier to the browser, which makes that when requesting web page sources from the second domain name, the browser can send the cross-domain user identifier indicative of the second identifier of the user in the second domain name to the second domain name server, so that the user does not need to log in the second domain name, while still maintaining the login state of the user. - As shown in
FIG. 7 , in an embodiment, a seconddomain name server 30 includes asecond receiving module 302, a secondidentifier obtaining module 304 and a loginstate generating module 306. - The
second receiving module 302 is configured to receive a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser. The cross-domain jump request includes a cross-domain user identifier corresponding to a first identifier of a user in the first domain name. - The second
identifier obtaining module 304 is configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier. - In an embodiment, the second
identifier obtaining module 304 is configured to analyze the cross-domain jump request according to a pre-set way, extract the cross-domain user identifier from the cross-domain jump request, decrypt the cross-domain user identifier to obtain a decrypted cross-domain user identifier, check legality of the decrypted cross-domain user identifier and find the second identifier of the user in the second domain name corresponding to the decrypted cross-domain user identifier. - In an embodiment, the second domain name server can pre-store legal cross-domain user identifiers. The second
identifier obtaining module 304 can find the decrypted cross-domain user identifier in the pre-stored legal cross-domain user identifiers. If successfully found, then the decrypted cross-domain user identifier is legal. If unsuccessfully found, then the decrypted cross-domain user identifier is illegal. - The login
state generating module 306 is configured to generate a user login state of the user in the second domain name according to the second identifier. - In an embodiment, the login
state generating module 306 is further configured to label the user login state of the second identifier as an already-logged-in state in a user login state database of the second domain name. - As shown in
FIG. 8 , in an embodiment, the seconddomain name server 30 further includes aninformation returning module 308 configured to return web page sources corresponding to the cross-domain jump request and a user identity information corresponding to the second identifier to the browser. - The second
domain name server 30 receives the cross-domain jump request including the cross-domain user identifier sent by the browser, and generates the second identifier of the user in the second domain name according to the cross-domain user identifier, and recognizes the identity of the user according to the second identifier, so that the user does not need to log in the second domain name while still maintaining the login state of the user. - As shown in
FIG. 9 , a system for implementing a cross-domain jump includes thebrowser 10, the firstdomain name server 20 and the seconddomain name server 30 of any one of the above embodiments. Thebrowser 10 includes therequest obtaining module 102, thebrowser sending module 104 and thebrowser receiving module 106 shown inFIG. 5 . The firstdomain name server 20 includes thefirst receiving module 202, the cross-domainidentifier generating module 204 and thefirst sending module 206 shown inFIG. 6 . The seconddomain name server 30 includes thesecond receiving module 302, the secondidentifier obtaining module 304 and the loginstate generating module 306 shown inFIG. 7 . - The
request obtaining module 102 is configured to obtain a request of jumping from a first domain name to a second domain name. - The
browser sending module 104 is configured to send the second domain name and a first identifier of a user in the first domain name to the firstdomain name server 20. - The
first receiving module 202 is configured to receive the second domain name and the first identifier of the user in the first domain name sent by thebrowser 10. - The cross-domain
identifier generating module 204 is configured to generate a cross-domain user identifier according to the second domain name and the first identifier. - The
first sending module 206 is configured to send the cross-domain user identifier to thebrowser 10. - The
browser receiving module 106 is configured to receive the cross-domain user identifier sent by the firstdomain name server 20. - The
browser sending module 104 is further configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the seconddomain name server 30. The cross-domain jump request includes the cross-domain user identifier. - The
second receiving module 302 is configured to receive the cross-domain jump request of jumping from the first domain name to the second domain name sent by thebrowser 10. - The second
identifier obtaining module 304 is configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier. - The login
state generating module 306 is configured to generate a user login state of the user in the second domain name according to the second identifier. - As shown in
FIG. 10 , in an embodiment, abrowser 40 includes arequest obtaining unit 402, a cross-domainidentifier generating unit 404 and abrowser sending unit 406. - The
request obtaining unit 402 is configured to obtain a request of jumping from a first domain name to a second domain name. - The cross-domain
identifier generating unit 404 is configured to generate a cross-domain user identifier according to the second domain name and a first identifier of a user in the first domain name. The cross-domain user identifier corresponds to a second identifier of the user in the second domain name. - In an embodiment, the cross-domain
identifier generating unit 404 is configured to find a registered identifier and a second domain name key corresponding to the second domain name, combine the registered identifier with the first identifier, encrypt the combined identifier according to the second domain name key and generate the cross-domain user identifier. - Specifically, in an embodiment, when the browser requests web page sources from the first domain name server, the first domain name server can embed the registered identifier and the second domain name key of the second domain name included in the web page sources into the web page sources, and embed a program of the cross-domain user identifier generated according to the second domain name and the first identifier, and distribute the web page sources to the browser. After a link of the second domain name in a first domain name web page is clicked, the cross-domain
identifier generating unit 404 can execute the program of the cross-domain user identifier generated according to the second domain name and the first identifier and pre-embedded into the web page sources to generate the cross-domain user identifier. - The
browser sending unit 406 is configured to send the cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server. The cross-domain jump request includes the cross-domain user identifier. - As shown in
FIG. 11 , in an embodiment, thebrowser 40 further includes abrowser receiving unit 408 configured to receive the web page sources corresponding to the cross-domain jump request and a user identity information corresponding to the second identifier sent by the second domain name server. - In an embodiment, the
browser 40 further includes a display module (not shown in the figures) configured to display a web page corresponding to the web page sources and display the user identity information corresponding to the second identifier in the web page. - After receiving the request of jumping from the first domain name to the second domain name, the
browser 40 generates the cross-domain user identifier according to the second domain name and the first identifier, and sends the cross-domain jump request including the cross-domain user identifier to the second domain name server. The cross-domain user identifier corresponds to the second identifier of the user in the second domain name. Therefore, the user does not need to log in, while still maintaining the login state of the user. This reduces operation time of the user in the terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life. - As shown in
FIG. 12 , in an embodiment, a system for implementing a cross-domain jump includes thebrowser 40 and the seconddomain name server 30 of any one of the above embodiments. Thebrowser 40 includes therequest obtaining unit 402, the cross-domainidentifier generating unit 404 and thebrowser sending unit 406 shown inFIG. 10 . The seconddomain name server 30 includes thesecond receiving module 302, the secondidentifier obtaining module 304 and the loginstate generating module 306 shown inFIG. 7 . - The
request obtaining unit 402 is configured to obtain a request of jumping from a first domain name to a second domain name. - The cross-domain
identifier generating unit 404 is configured to generate a cross-domain user identifier according to the second domain name and a first identifier of a user in the first domain name. The cross-domain user identifier corresponds to a second identifier of the user in the second domain name. - The
browser sending unit 406 is configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to the second domain name server. The cross-domain jump request includes the cross-domain user identifier. - The
second receiving module 302 is configured to receive the cross-domain jump request of jumping from the first domain name to the second domain name sent by thebrowser 40. - The second
identifier obtaining module 304 is configured to obtain a second identifier of the user in the second domain name corresponding to the cross-domain user identifier. - The login
state generating module 306 is configured to generate a user login state of the user in the second domain name according to the second identifier. - In the method and system for implementing the cross-domain jump, the cross-domain jump request of jumping from the first domain name and the second domain name includes the cross-domain user identifier corresponding to the first identifier of the user in the first domain name. The second domain name server can generate the second identifier of the user in the second domain name according to the cross-domain user identifier and recognize the identity of the user according to the second identifier, so that the user does not need to log in again while still maintaining the user login state when jumping from the first domain name to the second domain name. This reduces operation time of the user in a terminal after the cross-domain jump, and saves electric power, especially for a mobile terminal with limited electric power, increases a battery life.
- Those skilled in the art should understand that whole or part of the methods in the embodiments could be carried by corresponding hardware instructed by computer programs. Such programs could be stored in a computer-readable storage medium. When such programs are executed, the process of the methods in the embodiments is included. The storage medium can be magnetic disk, optical disk, read-only memory (ROM), or random access memory (RAM), etc.
- The above described embodiments explain only several exemplary embodiments of the present invention; the descriptions are specified and detailed, while shall not be understood as to limit the invention to the precise forms disclosed. It shall be mentioned that for those skilled in the art, alternative embodiments could be made to which the present invention pertains without departing from its scope defined by the appended claims rather than the foregoing description and the exemplary embodiments described therein.
Claims (5)
- A method for implementing a cross-domain jump, comprising the following steps:a second domain name server (30) obtaining (S102) a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser (10), the cross-domain jump request comprising a cross-domain user identifier corresponding to a first identifier of a user in the first domain name;the second domain name server (30) obtaining (SI04) a second identifier of the user in the second domain name corresponding to the cross-domain user identifier, and generating a user login state of the user in the second domain name according to the second identifier,characterized in thatwherein before the step of a second domain name server (30) obtaining (S102) a cross-domain jump request of jumping from a first domain name to a second domain name sent by a browser (10), the method further comprises:the browser (10) obtaining (S302) a request of jumping from the first domain name to the second domain name, and generating (S302) the cross-domain user identifier according to the second domain name and the first identifier;the browser generating (S304) the cross-domain jump request according to the cross-domain user identifier and the second domain name and sending (S304) the cross-domain jump request to the second domain name server (30),wherein the step of the browser generating (S304) the cross-domain user identifier according to the second domain name and the first identifier comprises:the browser (10) finding a registered identifier and a second domain name key corresponding to the second domain name, and combining the registered identifier and the first identifier;the browser (10) encrypting the combined identifier according to the second domain name key to generate the cross-domain user identifier.
- The method for implementing the cross-domain jump of claim 1, the second domain name server (30) returning web page sources corresponding to the cross-domain jump request and a user identity information corresponding to the second identifier to the browser (10);
the browser (10) displaying a web page corresponding to the web page sources, and displaying the user identity information corresponding to the second identifier in the web page; and
the browser (10) storing the second identifier in a file used for storing already-logged-in user information of the second domain name in a pre-set path. - The method for implementing cross-domain jump of claim 1, wherein the step of the second domain name server (30) obtaining (S104) a second identifier of the user in the second domain name corresponding to the cross-domain user identifier comprises:
extracting the cross-domain user identifier from the cross-domain jump request, decrypting the cross-domain user identifier to obtain a decrypted cross-domain user identifier, checking legality of the decrypted cross-domain user identifier and finding the second identifier of the user in the second domain name corresponding to the decrypted cross-domain user identifier. - A browser (10), comprising:a request obtaining module (102) configured to obtain a request of jumping from a first domain name to a second domain name; anda browser sending module (104) configured to send a cross-domain jump request of jumping from the first domain name to the second domain name to a second domain name server (30), the cross-domain jump request comprising a cross-domain user identifier corresponding to a first identifier of a user in the first domain name;characterized in thatthe browser (10) further comprises a cross-domain request generating module, configured to find a registered identifier and a second domain name key corresponding to the second domain name, combine the registered identifier and the first identifier, encrypt the combined identifier according to the second domain name key to generate the cross-domain user identifier, and generate the cross-domain jump request according to the cross-domain user identifier and the second domain name.
- The browser (10) of claim 4, wherein the browser receiving module (106) is further configured to receive web page sources corresponding to the cross-domain jump request and a user identity information corresponding to the second identifier to the browser sent by the second domain name server (30);
wherein the browser (10) further comprises
a display module configured to display a web page corresponding to the web page sources and display the user identity information in the web page; and
an identifier storing module configured to store the second identifier in a file that stores already-logged-in user information of the second domain name in a pre-set path.
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201210241298.6A CN103546432B (en) | 2012-07-12 | 2012-07-12 | Realize method and system and browser, the name server of cross-domain redirect |
| PCT/CN2013/079124 WO2014008858A1 (en) | 2012-07-12 | 2013-07-10 | Method for implementing cross-domain jump, browser, and domain name server |
Publications (3)
| Publication Number | Publication Date |
|---|---|
| EP2874074A1 EP2874074A1 (en) | 2015-05-20 |
| EP2874074A4 EP2874074A4 (en) | 2016-03-09 |
| EP2874074B1 true EP2874074B1 (en) | 2019-02-27 |
Family
ID=49915417
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| EP13817388.5A Active EP2874074B1 (en) | 2012-07-12 | 2013-07-10 | Method for implementing cross-domain jump, browser, and domain name server |
Country Status (5)
| Country | Link |
|---|---|
| US (1) | US9686344B2 (en) |
| EP (1) | EP2874074B1 (en) |
| CN (1) | CN103546432B (en) |
| RU (1) | RU2595931C1 (en) |
| WO (1) | WO2014008858A1 (en) |
Families Citing this family (15)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9503501B2 (en) * | 2012-09-17 | 2016-11-22 | Salesforce.Com, Inc. | Cross domain in-browser proxy |
| CN105472052B (en) * | 2014-09-03 | 2019-12-31 | 阿里巴巴集团控股有限公司 | Cross-domain server login method and system |
| CN105610855A (en) * | 2016-01-21 | 2016-05-25 | 北京京东尚科信息技术有限公司 | Method and device for login verification of cross-domain system |
| CN107196892B (en) * | 2016-03-15 | 2020-03-06 | 阿里巴巴集团控股有限公司 | Website login method and device |
| CN107306296A (en) * | 2016-04-17 | 2017-10-31 | 王正伟 | Domain name substitutes application method |
| CN105897746A (en) * | 2016-05-26 | 2016-08-24 | 深圳市金立通信设备有限公司 | Cross-website login method, terminal and website server |
| CN106060189B (en) * | 2016-07-08 | 2019-03-29 | 厦门纳网科技股份有限公司 | A kind of distribution domain name registration system |
| CN106973037B (en) * | 2017-02-16 | 2018-09-04 | 咪咕视讯科技有限公司 | A kind of method and system of control data transmission |
| CN108574709B (en) * | 2017-03-10 | 2021-09-07 | 北京京东尚科信息技术有限公司 | Method and device for realizing cross-domain operation |
| CN108632209A (en) * | 2017-03-20 | 2018-10-09 | 北京京东尚科信息技术有限公司 | System, method and apparatus for handling information |
| CN107909330B (en) * | 2017-08-31 | 2020-10-09 | 平安科技(深圳)有限公司 | Workflow data processing method and device, storage medium and computer equipment |
| US10992612B2 (en) * | 2018-11-12 | 2021-04-27 | Salesforce.Com, Inc. | Contact information extraction and identification |
| CN109918146A (en) * | 2019-02-02 | 2019-06-21 | 北京字节跳动网络技术有限公司 | Page generation method and device |
| CN111931088B (en) * | 2020-10-13 | 2021-01-26 | 北京拓课网络科技有限公司 | Webpage link processing method and device and electronic equipment |
| CN112511491B (en) * | 2020-10-30 | 2022-12-06 | 福建福诺移动通信技术有限公司 | Single point login method combining message queue under front-end and back-end separation mode |
Family Cites Families (15)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6119234A (en) * | 1997-06-27 | 2000-09-12 | Sun Microsystems, Inc. | Method and apparatus for client-host communication over a computer network |
| US6629246B1 (en) * | 1999-04-28 | 2003-09-30 | Sun Microsystems, Inc. | Single sign-on for a network system that includes multiple separately-controlled restricted access resources |
| CA2346231A1 (en) * | 2000-05-08 | 2001-11-08 | Internet Number Corporation | Method and system for accessing information on a network using message aliasing functions having shadow callback functions |
| WO2002039237A2 (en) * | 2000-11-09 | 2002-05-16 | International Business Machines Corporation | Method and system for web-based cross-domain single-sign-on authentication |
| US20030126136A1 (en) * | 2001-06-22 | 2003-07-03 | Nosa Omoigui | System and method for knowledge retrieval, management, delivery and presentation |
| US6993596B2 (en) * | 2001-12-19 | 2006-01-31 | International Business Machines Corporation | System and method for user enrollment in an e-community |
| JP2003296277A (en) * | 2002-03-29 | 2003-10-17 | Fuji Xerox Co Ltd | Network device, authentication server, network system, and authentication method |
| CN1855814A (en) * | 2005-04-29 | 2006-11-01 | 中国科学院计算机网络信息中心 | Safety uniform certificate verification design |
| CN1835438B (en) * | 2006-03-22 | 2011-07-27 | 阿里巴巴集团控股有限公司 | Method of realizing single time accession between websites and website thereof |
| CN100586066C (en) * | 2006-06-26 | 2010-01-27 | 北京金山软件有限公司 | System and method for realizing single-point login |
| CN101075875B (en) * | 2007-06-14 | 2011-08-31 | 中国电信股份有限公司 | Method and system for realizing monopoint login between gate and system |
| GB2452283A (en) * | 2007-08-30 | 2009-03-04 | Clickstream Technologies Plc | Establishing a common ID in first and second domain |
| CN101540734A (en) * | 2008-03-21 | 2009-09-23 | 阿里巴巴集团控股有限公司 | Method, system and device for accessing Cookie by crossing domain names |
| RU2413278C1 (en) * | 2009-05-27 | 2011-02-27 | Общество с ограниченной ответственностью "МэйлАдмин" | Method of selecting information on internet and using said information on separate website and server computer for realising said method |
| US9426142B2 (en) * | 2010-06-07 | 2016-08-23 | Salesforce.Com, Inc. | Systems and methods for logging into an application on a second domain from a first domain in a multi-tenant database system environment |
-
2012
- 2012-07-12 CN CN201210241298.6A patent/CN103546432B/en active Active
-
2013
- 2013-07-10 WO PCT/CN2013/079124 patent/WO2014008858A1/en active Application Filing
- 2013-07-10 RU RU2015104540/08A patent/RU2595931C1/en active
- 2013-07-10 EP EP13817388.5A patent/EP2874074B1/en active Active
-
2015
- 2015-01-12 US US14/594,705 patent/US9686344B2/en active Active
Non-Patent Citations (1)
| Title |
|---|
| None * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN103546432A (en) | 2014-01-29 |
| RU2595931C1 (en) | 2016-08-27 |
| US20150127943A1 (en) | 2015-05-07 |
| EP2874074A1 (en) | 2015-05-20 |
| US9686344B2 (en) | 2017-06-20 |
| EP2874074A4 (en) | 2016-03-09 |
| WO2014008858A1 (en) | 2014-01-16 |
| CN103546432B (en) | 2015-12-16 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| EP2874074B1 (en) | Method for implementing cross-domain jump, browser, and domain name server | |
| CN104144419B (en) | Identity authentication method, device and system | |
| US11082422B2 (en) | Authentication manager | |
| CN106330850B (en) | Security verification method based on biological characteristics, client and server | |
| US9887999B2 (en) | Login method and apparatus | |
| CN106878265B (en) | Data processing method and device | |
| CN101860540B (en) | Method and device for identifying legality of website service | |
| EP2890172B1 (en) | Flexible data authentication for an NFC data exchange format NDEF message | |
| CN108965222B (en) | Identity authentication method, system and computer readable storage medium | |
| US20140373125A1 (en) | Web security protection method, device and system | |
| CN104320377A (en) | An anti-stealing-link method and device for stream media file | |
| CN102682009A (en) | Method and system for logging in webpage | |
| CN104284213A (en) | Hotlink protection method, client side and system | |
| CN103607284A (en) | Identity authentication method and equipment and server | |
| CN108075888B (en) | Dynamic URL generation method and device, storage medium and electronic equipment | |
| CN103888255A (en) | Identity authentication method, device and system | |
| CN103475484B (en) | USB key authentication methods and system | |
| CN105577619B (en) | Client login method, client and system | |
| US20180205714A1 (en) | System and Method for Authenticating Electronic Tags | |
| CN109818906B (en) | Equipment fingerprint information processing method and device and server | |
| CN113645226B (en) | Data processing method, device, equipment and storage medium based on gateway layer | |
| CN109495458A (en) | A kind of method, system and the associated component of data transmission | |
| CN108234126B (en) | System and method for remote account opening | |
| CN115567271A (en) | Authentication method and device, page skip method and device, electronic equipment and medium | |
| CN104301285B (en) | Login method for web system |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PUAI | Public reference made under article 153(3) epc to a published international application that has entered the european phase |
Free format text: ORIGINAL CODE: 0009012 |
|
| 17P | Request for examination filed |
Effective date: 20150130 |
|
| AK | Designated contracting states |
Kind code of ref document: A1 Designated state(s): AL AT BE BG CH CY CZ DE DK EE ES FI FR GB GR HR HU IE IS IT LI LT LU LV MC MK MT NL NO PL PT RO RS SE SI SK SM TR |
|
| AX | Request for extension of the european patent |
Extension state: BA ME |
|
| DAX | Request for extension of the european patent (deleted) | ||
| RA4 | Supplementary search report drawn up and despatched (corrected) |
Effective date: 20160210 |
|
| RIC1 | Information provided on ipc code assigned before grant |
Ipc: H04L 29/06 20060101ALI20160204BHEP Ipc: G06F 17/30 20060101AFI20160204BHEP Ipc: H04L 29/08 20060101ALI20160204BHEP |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: EXAMINATION IS IN PROGRESS |
|
| 17Q | First examination report despatched |
Effective date: 20170807 |
|
| GRAP | Despatch of communication of intention to grant a patent |
Free format text: ORIGINAL CODE: EPIDOSNIGR1 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: GRANT OF PATENT IS INTENDED |
|
| INTG | Intention to grant announced |
Effective date: 20180918 |
|
| GRAS | Grant fee paid |
Free format text: ORIGINAL CODE: EPIDOSNIGR3 |
|
| GRAA | (expected) grant |
Free format text: ORIGINAL CODE: 0009210 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: THE PATENT HAS BEEN GRANTED |
|
| AK | Designated contracting states |
Kind code of ref document: B1 Designated state(s): AL AT BE BG CH CY CZ DE DK EE ES FI FR GB GR HR HU IE IS IT LI LT LU LV MC MK MT NL NO PL PT RO RS SE SI SK SM TR |
|
| REG | Reference to a national code |
Ref country code: GB Ref legal event code: FG4D |
|
| REG | Reference to a national code |
Ref country code: CH Ref legal event code: EP |
|
| REG | Reference to a national code |
Ref country code: AT Ref legal event code: REF Ref document number: 1102397 Country of ref document: AT Kind code of ref document: T Effective date: 20190315 |
|
| REG | Reference to a national code |
Ref country code: IE Ref legal event code: FG4D |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R096 Ref document number: 602013051544 Country of ref document: DE |
|
| REG | Reference to a national code |
Ref country code: NL Ref legal event code: MP Effective date: 20190227 |
|
| REG | Reference to a national code |
Ref country code: LT Ref legal event code: MG4D |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: PT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190627 Ref country code: NO Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190527 Ref country code: FI Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: SE Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: LT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: NL Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: RS Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: LV Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: HR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: IS Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190627 Ref country code: GR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190528 Ref country code: BG Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190527 |
|
| REG | Reference to a national code |
Ref country code: AT Ref legal event code: MK05 Ref document number: 1102397 Country of ref document: AT Kind code of ref document: T Effective date: 20190227 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: DK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: IT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: EE Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: AL Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: RO Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: CZ Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: ES Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: SK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R097 Ref document number: 602013051544 Country of ref document: DE |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: PL Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: SM Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: AT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| PLBE | No opposition filed within time limit |
Free format text: ORIGINAL CODE: 0009261 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: NO OPPOSITION FILED WITHIN TIME LIMIT |
|
| 26N | No opposition filed |
Effective date: 20191128 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: SI Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 Ref country code: MC Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| REG | Reference to a national code |
Ref country code: CH Ref legal event code: PL |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: TR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| REG | Reference to a national code |
Ref country code: BE Ref legal event code: MM Effective date: 20190731 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: LU Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20190710 Ref country code: CH Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20190731 Ref country code: LI Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20190731 Ref country code: BE Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20190731 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: IE Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20190710 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: CY Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: HU Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT; INVALID AB INITIO Effective date: 20130710 Ref country code: MT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: MK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20190227 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: FR Payment date: 20230510 Year of fee payment: 11 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: GB Payment date: 20230518 Year of fee payment: 11 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: DE Payment date: 20230516 Year of fee payment: 11 |