US8413018B2 - Separate memories and address busses to store data and signature - Google Patents
Separate memories and address busses to store data and signature Download PDFInfo
- Publication number
- US8413018B2 US8413018B2 US12/542,583 US54258309A US8413018B2 US 8413018 B2 US8413018 B2 US 8413018B2 US 54258309 A US54258309 A US 54258309A US 8413018 B2 US8413018 B2 US 8413018B2
- Authority
- US
- United States
- Prior art keywords
- memory
- signature
- data
- logic
- address
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Expired - Fee Related, expires
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F11/00—Error detection; Error correction; Monitoring
- G06F11/07—Responding to the occurrence of a fault, e.g. fault tolerance
- G06F11/08—Error detection or correction by redundancy in data representation, e.g. by using checking codes
- G06F11/10—Adding special bits or symbols to the coded information, e.g. parity check, casting out 9's or 11's
- G06F11/1008—Adding special bits or symbols to the coded information, e.g. parity check, casting out 9's or 11's in individual solid state devices
- G06F11/1012—Adding special bits or symbols to the coded information, e.g. parity check, casting out 9's or 11's in individual solid state devices using codes or arrangements adapted for a specific type of error
- G06F11/1016—Error in accessing a memory location, i.e. addressing error
-
- H—ELECTRICITY
- H03—ELECTRONIC CIRCUITRY
- H03M—CODING; DECODING; CODE CONVERSION IN GENERAL
- H03M13/00—Coding, decoding or code conversion, for error detection or error correction; Coding theory basic assumptions; Coding bounds; Error probability evaluation methods; Channel models; Simulation or testing of codes
- H03M13/03—Error detection or forward error correction by redundancy in data representation, i.e. code words containing more digits than the source words
- H03M13/05—Error detection or forward error correction by redundancy in data representation, i.e. code words containing more digits than the source words using block codes, i.e. a predetermined number of check bits joined to a predetermined number of information bits
- H03M13/09—Error detection only, e.g. using cyclic redundancy check [CRC] codes or single parity bit
Definitions
- the present invention relates to the field of computer and networking hardware, and in particular to a technique for detecting address corruption during memory transfer operations.
- ECC Error Correction Code
- a device comprises a first memory, a second memory, a core logic unit, coupled to the first memory via a first address line and coupled to the second memory via a second address line, wherein the core logic unit is programmed to read from and write to the first and second memories, a first signature generator logic, configured to compute a first signature from data written to the first memory, coupled to the second memory to store the first signature in the first memory, a second signature generator logic, configured to compute a second signature from data read from the first memory, and a comparator logic, coupled to the second memory and the second signature generator logic, indicating an error condition to the core logic unit if the first signature does not match the second signature.
- a method comprises comparing a first signature computed from data written to a first memory using a first address line with a second signature computed from data read from the first memory, and storing the first signature in a second memory using a second address line.
- a device comprises a first memory and a field programmable gate array (FPGA), coupled to the first memory using a first address line, the FPGA comprising a second memory, internal to the FPGA, addressed using a second address line, and logic to perform the acts of comparing a first signature computed from data written to the first memory with a second signature computed from data read from the first memory and storing the first signature in the second memory.
- FPGA field programmable gate array
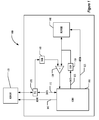
- FIG. 1 is a block diagram illustrating a circuit according to one embodiment
- FIG. 2 is a block diagram illustrating two memories according to one embodiment
- FIG. 3 is a pair of flowcharts illustrating writing and reading memory according to the embodiment of FIG. 2 ;
- FIG. 4 is a block diagram illustrating a circuit according to one embodiment
- FIG. 5 is a block diagram illustrating a memory according to another embodiment.
- FIG. 6 is a pair of flowcharts illustrating writing and reading memory according to the embodiment of FIG. 4 .
- FIG. 1 is a block diagram illustrating a programmable device 100 according to one embodiment, which reads and writes to memory 120 .
- a core logic 110 provides processing capability for the programmable device 100 .
- the memory 120 is external to the programmable device 100 and the memory 140 is internal, either or both of the memories 120 , 140 may be either external or internal to the programmable device 100 .
- the illustrated circuits of the programmable device 100 can be implemented as a single chip or multiple chips. Additional elements, such as buffers or other conventional elements of memory-related circuits, may be present in implementations according to this embodiment, but are omitted from FIG. 1 for clarity.
- Core logic 110 is connected via first address lines 105 to external memory 120 .
- Second address lines 125 connect the core logic 110 to internal memory 140 .
- the core logic 110 is connected via data lines 115 to Error Correction Code (ECC) generation and checking logic 170 and thence to memory 120 .
- Core logic 110 is further connected via data lines 135 to a signature generation logic 150 and thence to memory 140 .
- ECC Error Correction Code
- Data read from memory 120 based on address lines 105 are transferred via the ECC logic 170 back to the core logic 110 over data lines 105 , but are also transferred to signature generation logic 160 and thence to comparator 130 .
- Memory 140 is also read based on address lines 125 , reading the stored signature to the comparator 130 .
- the comparator 130 compares the signature of the data read from memory 120 and the signature of the data written to memory 120 that was stored in memory 140 , passing the result on to the core logic 110 . If the signatures do not match, the comparator 130 indicates an error condition to the core logic 110 , which may take any desired error action in response to the error indication. In one embodiment, the same address is used on both address lines 105 , 125 for reading and writing memories 120 , 140 .
- first and second address lines 105 and 125 increase the likelihood of detection of an addressing error as the chance of identically corrupting both address lines 105 and 125 is very small as the address lines 105 and 125 have different paths or layouts for a large amount of their lengths. This is of course true where the memory 120 is a separate module and the memory 140 is onboard the programmable device but also will be true for cases where both memories 120 and 140 are onboard or external.
- This different path or layout differs from the address bus arrangement used with DIMMs and other memory modules with ECC capabilities, where the address bus is identical until only the last very short portion contained on the DIMM or the like.
- the address bus portions used to reach the DIMM are the portions most likely to be the locations of any corruption, not the portion on the DIMM itself.
- Memories 120 , 140 may be any desired type of addressable memory, including volatile storage devices, such as RLDRAM® memories (RLDRAM is a registered trademark of Infineon Technologies AG), and non-volatile storage devices, and the memories 120 , 140 do not need to be identical or of the same type or capacity.
- volatile storage devices such as RLDRAM® memories (RLDRAM is a registered trademark of Infineon Technologies AG)
- non-volatile storage devices and the memories 120 , 140 do not need to be identical or of the same type or capacity.
- the programmable device 100 may be implemented as part of a secure logic, packaged in a tamper-resistant packaging, for an encryption device such as an encryption switch for a Storage Area Network (SAN). But the programmable device 100 may be any programmable device that reads or writes to an addressable memory.
- a secure logic packaged in a tamper-resistant packaging, for an encryption device such as an encryption switch for a Storage Area Network (SAN).
- SAN Storage Area Network
- the programmable device 100 may be any programmable device that reads or writes to an addressable memory.
- FIG. 1 illustrates the use of ECC logic 170 to detect and/or correct data errors. Nevertheless, the use of ECC logic 170 would not detect corruption of the address information when addressing either memory 120 or 140 . ECC 170 may be omitted.
- FIG. 2 is a block diagram illustrating a technique for writing to memories 120 and 140 according the embodiment of FIG. 1 .
- the core logic 110 writes data to memory 120 at address addr 1 using address and data lines 105 , 115 .
- the signature generation logic 150 also computes a signature of the data written to address addr 1 and writes the signature to memory 140 at the same address, addr 1 , using address and data lines 125 , 135 .
- a new signature is computed signature logic 160 for the data read from memory 120 , and compared with the signature read from memory 140 by the comparator 130 . If the signatures match, then the data was successfully written and read; otherwise, the comparator 130 indicates an error indication to the core logic 110 , which may take an error action. The nature of the error action is outside the scope of the present invention, and will not be discussed further herein.
- the described technique can detect not just data corruption, but address corruption. Such corruption may arise either during the time the data is stored in the memory 120 , or because of corruption on the address lines 105 or data lines 115 while writing or reading the data to the memory 120 .
- FIG. 3 is a pair of flowcharts illustrating reading and writing data according to the embodiment of FIG. 1 .
- a signature is computed by signature logic 150 from the data.
- CRC Cyclic Redundancy Code
- the data are stored at the designated address in memory 120 , and in block 310 , the memory 140 also stores the signature at the same address.
- the acts of blocks 310 and 320 may be performed in either order or concurrently as desired.
- additional logic may compute a different address to read and write memory 140 using address line 125 , based on the address transmitted on address line 105 to memory 120 .
- the core logic 110 in block 330 reads the signature from memory 140 , and in block 340 reads the data from memory 120 .
- blocks 330 and 340 may be performed in either order or concurrently as desired.
- the signature logic 160 then in block 350 recomputes the signature from the data received from memory 120 .
- the signature computed by signature logic 160 is compared with the signature read from memory 140 in block 330 . If the signatures match, then the data have been written and read successfully. If the signatures do not match, then an error condition exists, and the core logic 110 may indicate an error indication, including taking any desired error action.
- FIG. 4 illustrates another embodiment of a programmable device 400 , which uses only one of the memories 120 , 140 , illustrated here as memory 120 .
- the signature instead of being written to a different memory 140 , is written to the memory 120 .
- the signature may be written either before or after the data as desired, with the combined data and signature written in this example beginning at address addr 1 .
- the signature in the embodiment of FIG. 4 is computed on a combination of the data and the address.
- additional conventional elements such as buffers have been omitted from the drawing for clarity.
- the memory 120 is illustrated as external to the programmable device 400 , the memory 120 may be internal to the programmable device 400 and implemented on-chip as desired.
- core logic 110 When core logic 110 writes data to memory 120 , the address is placed on address lines 105 and the data on data lines 115 , as it is in the embodiment illustrated in FIG. 1 . But in this embodiment, the signature generation logic 410 computes a signature based on both the address and data. An ECC generation logic 430 then generates an ECC from the data and the signature, passing the data and signature on to the memory 120 , where both data and signature are written to the memory 120 at the address specified on the address line 105 .
- core logic 110 When core logic 110 reads data from memory 120 , the address is once again placed on the address lines 105 . The data and signature at that address are returned to ECC logic checking logic 435 , which checks the ECC and performs any ECC-based data correction as needed. The data are then transmitted to the core logic 110 as well as signature logic 420 , which computes a signature based on the data returned from memory 120 and the address on the address lines 105 . The signature read from the memory is compared with the signature generated by the signature generation logic 420 by comparator 130 , which passes the result on to the core logic 110 . If the signatures do not match, then core logic may take any desired error action responsive to the error indication returned by the comparator 130 . If either the data or address are corrupted when the data are written or read from memory 120 , then this embodiment will detect the corruption.
- ECC logics 430 and 435 are employed in FIG. 4 for conventional ECC purposes, ECC logics 430 and 435 may be omitted if desired.
- FIG. 5 is a block diagram illustrating the data and signature written according to the embodiment of FIG. 4 , where the address is indicated as addr 1 .
- FIG. 6 is a pair of flowcharts illustrating writing and reading the memory 120 according to the embodiment of FIG. 4 .
- the signature logic 410 computes the signature of a combination of the data and the address to which the data are to be written. Any desired technique for combining the data and address for purposes of computing the signature may be used. As with the embodiment of FIGS. 1-3 , any desired signature computation technique can be used, including CRC-10. Then the data and the signature are written in block 510 to memory 120 at the address specified on the address lines 105 .
- the signature portion of the information stored in block 610 is read from the memory 120 .
- the data portion is read. Blocks 620 and 630 may be performed in either order or concurrently.
- the signature logic 420 computes a signature from the received data and the address from which it was read, such as the address addr 1 of FIG. 5 .
- the signature portion read in block 620 is compared by the comparator 130 with the signature computed in block 640 . If the signatures match, then the data was written and read successfully; otherwise, the data was incorrectly written or read, perhaps because of an address corruption, and the comparator indicates an error condition to core logic 110 , which may take any desired error action as a result.
- the programmable device 400 may be implemented as part of a secure logic, packaged in a tamper-resistant packaging, for an encryption device such as an encryption switch for a Storage Area Network (SAN). But the programmable device 400 may be any programmable device that reads or writes to an addressable memory.
- a secure logic packaged in a tamper-resistant packaging, for an encryption device such as an encryption switch for a Storage Area Network (SAN).
- SAN Storage Area Network
- the programmable device 400 may be any programmable device that reads or writes to an addressable memory.
- the programmable devices 100 and 400 may detect and protect against both address and data corruption events when accessing a memory, instead of only data corruption events as in a conventional device that uses only ECC or other similar techniques. Such corruption may arise either during the time the data are stored in the memory 120 , or because of corruption on the address lines 105 or data lines 115 while writing or reading the data to the memory 120 .
- FIGS. 3 and 6 may perform the identified steps in an order different from that disclosed here.
- some embodiments may combine the activities described herein as being separate steps.
- one or more of the described steps may be omitted, depending upon the specific operational environment in which the method is being implemented.
- any or all of the logic of FIGS. 1 and 4 may be implemented with discrete logic elements or combined in a single chip, for example in an application specific integrated circuit (“ASIC”) or a field programmable gate array (“FPGA”).
- ASIC application specific integrated circuit
- FPGA field programmable gate array
- FIGS. 1 and 4 are illustrative and by way of example only, and other circuit and logic elements, and arrangements thereof may be used as desired, including combining elements illustrated as separate, or separating individual elements into multiple elements.
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- Quality & Reliability (AREA)
- Physics & Mathematics (AREA)
- General Engineering & Computer Science (AREA)
- General Physics & Mathematics (AREA)
- Techniques For Improving Reliability Of Storages (AREA)
Abstract
Description
Claims (19)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US12/542,583 US8413018B2 (en) | 2009-08-17 | 2009-08-17 | Separate memories and address busses to store data and signature |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US12/542,583 US8413018B2 (en) | 2009-08-17 | 2009-08-17 | Separate memories and address busses to store data and signature |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| US20110041031A1 US20110041031A1 (en) | 2011-02-17 |
| US8413018B2 true US8413018B2 (en) | 2013-04-02 |
Family
ID=43589313
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US12/542,583 Expired - Fee Related US8413018B2 (en) | 2009-08-17 | 2009-08-17 | Separate memories and address busses to store data and signature |
Country Status (1)
| Country | Link |
|---|---|
| US (1) | US8413018B2 (en) |
Cited By (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20170177428A1 (en) * | 2015-12-20 | 2017-06-22 | Freescale Semiconductor, Inc. | Memory error detection system |
| US20230085149A1 (en) * | 2021-09-16 | 2023-03-16 | Xilinx, Inc. | Intra-chip and inter-chip data protection |
Families Citing this family (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US8566689B2 (en) * | 2009-10-22 | 2013-10-22 | Microsoft Corporation | Data integrity units in nonvolatile memory |
| FR3100346B1 (en) | 2019-09-04 | 2022-07-15 | St Microelectronics Rousset | Error detection |
| FR3100347B1 (en) | 2019-09-04 | 2022-07-22 | St Microelectronics Rousset | Error detection |
| US11735285B1 (en) * | 2021-03-12 | 2023-08-22 | Kioxia Corporation | Detection of address bus corruption for data storage devices |
| US12298846B2 (en) | 2023-07-10 | 2025-05-13 | SanDisk Technologies, Inc. | Enhanced end to end system failure recovery |
Citations (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6101624A (en) * | 1998-01-21 | 2000-08-08 | International Business Machines Corporation | Method and apparatus for detecting and correcting anomalies in field-programmable gate arrays using CRCs for anomaly detection and parity for anomaly correction |
| US6560743B2 (en) * | 1998-03-16 | 2003-05-06 | Actel Corporation | Cyclic redundancy checking of a field programmable gate array having a SRAM memory architecture |
| US6581173B2 (en) * | 1998-06-30 | 2003-06-17 | Intel Corporation | Method and apparatus for verifying that data stored in a memory has not been corrupted |
| US6968478B1 (en) * | 2003-12-18 | 2005-11-22 | Xilinx, Inc. | Method and apparatus for data transfer validation |
| US20070198892A1 (en) * | 2006-02-01 | 2007-08-23 | U.S.A. As Represented By The Administrator Of National Aeronautics And Space Administration | Systems And Methods For Detecting A Failure Event In A Field Programmable Gate Array |
| US7325178B2 (en) * | 2003-12-05 | 2008-01-29 | Texas Instruments Incorporated | Programmable built in self test of memory |
| US20080250297A1 (en) | 2007-04-03 | 2008-10-09 | Industrial Technology Research Institute | Method and system for calculating crc |
| US7865784B1 (en) * | 2006-09-11 | 2011-01-04 | Marvell International Ltd. | Write validation |
| US20110041030A1 (en) | 2009-08-17 | 2011-02-17 | Kung-Ling Ko | Storage of data and signature formed from data and address in a memory |
-
2009
- 2009-08-17 US US12/542,583 patent/US8413018B2/en not_active Expired - Fee Related
Patent Citations (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6101624A (en) * | 1998-01-21 | 2000-08-08 | International Business Machines Corporation | Method and apparatus for detecting and correcting anomalies in field-programmable gate arrays using CRCs for anomaly detection and parity for anomaly correction |
| US6560743B2 (en) * | 1998-03-16 | 2003-05-06 | Actel Corporation | Cyclic redundancy checking of a field programmable gate array having a SRAM memory architecture |
| US7543216B1 (en) * | 1998-03-16 | 2009-06-02 | Actel Corporation | Cyclic redundancy checking of a field programmable gate array having an SRAM memory architecture |
| US6581173B2 (en) * | 1998-06-30 | 2003-06-17 | Intel Corporation | Method and apparatus for verifying that data stored in a memory has not been corrupted |
| US7325178B2 (en) * | 2003-12-05 | 2008-01-29 | Texas Instruments Incorporated | Programmable built in self test of memory |
| US6968478B1 (en) * | 2003-12-18 | 2005-11-22 | Xilinx, Inc. | Method and apparatus for data transfer validation |
| US20070198892A1 (en) * | 2006-02-01 | 2007-08-23 | U.S.A. As Represented By The Administrator Of National Aeronautics And Space Administration | Systems And Methods For Detecting A Failure Event In A Field Programmable Gate Array |
| US7865784B1 (en) * | 2006-09-11 | 2011-01-04 | Marvell International Ltd. | Write validation |
| US20080250297A1 (en) | 2007-04-03 | 2008-10-09 | Industrial Technology Research Institute | Method and system for calculating crc |
| US20110041030A1 (en) | 2009-08-17 | 2011-02-17 | Kung-Ling Ko | Storage of data and signature formed from data and address in a memory |
Non-Patent Citations (1)
| Title |
|---|
| Office Action Summary from U.S. Appl. No. 12/542,575 dated Jan. 12, 2012. |
Cited By (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20170177428A1 (en) * | 2015-12-20 | 2017-06-22 | Freescale Semiconductor, Inc. | Memory error detection system |
| US9727408B2 (en) * | 2015-12-20 | 2017-08-08 | Nxp Usa, Inc. | Memory error detection system |
| US20230085149A1 (en) * | 2021-09-16 | 2023-03-16 | Xilinx, Inc. | Intra-chip and inter-chip data protection |
| US12105658B2 (en) * | 2021-09-16 | 2024-10-01 | Xilinx, Inc. | Intra-chip and inter-chip data protection |
Also Published As
| Publication number | Publication date |
|---|---|
| US20110041031A1 (en) | 2011-02-17 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US11734106B2 (en) | Memory repair method and apparatus based on error code tracking | |
| US7599235B2 (en) | Memory correction system and method | |
| US9015558B2 (en) | Systems and methods for error detection and correction in a memory module which includes a memory buffer | |
| US8756486B2 (en) | Method and apparatus for repairing high capacity/high bandwidth memory devices | |
| US8413018B2 (en) | Separate memories and address busses to store data and signature | |
| US8245109B2 (en) | Error checking and correction (ECC) system and method | |
| US6052818A (en) | Method and apparatus for ECC bus protection in a computer system with non-parity memory | |
| KR20100082710A (en) | Data memory device and controller with interface error detection and handling logic | |
| CN109785893B (en) | Redundant storage of error-correcting code check bits used to verify proper memory operation | |
| CN111475327B (en) | Memory system and method of operating the same | |
| US20110041030A1 (en) | Storage of data and signature formed from data and address in a memory | |
| US12222829B2 (en) | Memory module with dedicated repair devices | |
| US10481973B2 (en) | Memory module with dedicated repair devices | |
| US12505014B1 (en) | DRAM ECC circuit error detection integrity |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| AS | Assignment |
Owner name: BROCADE COMMUNICATIONS SYSTEMS, INC., CALIFORNIA Free format text: ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNORS:KO, KUNG-LING;VARANASI, SURYA PRAKASH;PALACHARLA, SUBBARAO;SIGNING DATES FROM 20090918 TO 20090921;REEL/FRAME:023280/0654 |
|
| AS | Assignment |
Owner name: WELLS FARGO BANK, NATIONAL ASSOCIATION, AS COLLATE Free format text: SECURITY AGREEMENT;ASSIGNORS:BROCADE COMMUNICATIONS SYSTEMS, INC.;FOUNDRY NETWORKS, LLC;INRANGE TECHNOLOGIES CORPORATION;AND OTHERS;REEL/FRAME:023814/0587 Effective date: 20100120 |
|
| STCF | Information on status: patent grant |
Free format text: PATENTED CASE |
|
| AS | Assignment |
Owner name: BROCADE COMMUNICATIONS SYSTEMS, INC., CALIFORNIA Free format text: RELEASE BY SECURED PARTY;ASSIGNOR:WELLS FARGO BANK, NATIONAL ASSOCIATION, AS COLLATERAL AGENT;REEL/FRAME:034804/0793 Effective date: 20150114 Owner name: FOUNDRY NETWORKS, LLC, CALIFORNIA Free format text: RELEASE BY SECURED PARTY;ASSIGNOR:WELLS FARGO BANK, NATIONAL ASSOCIATION, AS COLLATERAL AGENT;REEL/FRAME:034804/0793 Effective date: 20150114 |
|
| REMI | Maintenance fee reminder mailed | ||
| FPAY | Fee payment |
Year of fee payment: 4 |
|
| SULP | Surcharge for late payment | ||
| AS | Assignment |
Owner name: BROCADE COMMUNICATIONS SYSTEMS LLC, CALIFORNIA Free format text: CHANGE OF NAME;ASSIGNOR:BROCADE COMMUNICATIONS SYSTEMS, INC.;REEL/FRAME:044891/0536 Effective date: 20171128 |
|
| AS | Assignment |
Owner name: AVAGO TECHNOLOGIES INTERNATIONAL SALES PTE. LIMITED, SINGAPORE Free format text: ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:BROCADE COMMUNICATIONS SYSTEMS LLC;REEL/FRAME:047270/0247 Effective date: 20180905 Owner name: AVAGO TECHNOLOGIES INTERNATIONAL SALES PTE. LIMITE Free format text: ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:BROCADE COMMUNICATIONS SYSTEMS LLC;REEL/FRAME:047270/0247 Effective date: 20180905 |
|
| MAFP | Maintenance fee payment |
Free format text: PAYMENT OF MAINTENANCE FEE, 8TH YEAR, LARGE ENTITY (ORIGINAL EVENT CODE: M1552); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY Year of fee payment: 8 |
|
| FEPP | Fee payment procedure |
Free format text: MAINTENANCE FEE REMINDER MAILED (ORIGINAL EVENT CODE: REM.); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY |
|
| LAPS | Lapse for failure to pay maintenance fees |
Free format text: PATENT EXPIRED FOR FAILURE TO PAY MAINTENANCE FEES (ORIGINAL EVENT CODE: EXP.); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY |
|
| STCH | Information on status: patent discontinuation |
Free format text: PATENT EXPIRED DUE TO NONPAYMENT OF MAINTENANCE FEES UNDER 37 CFR 1.362 |
|
| FP | Lapsed due to failure to pay maintenance fee |
Effective date: 20250402 |